Beyond a Mystery Nation: North Korea Hackers

Show transcript [en]
coming in from there so the way I I like to tell it is like a story anyone likes stories here oh so that's the way I like to tell incidents in general so it's gonna be more of a story me talking about events that happened and kind of together with you trying to examine the evidence and get into some conclusions and so since I'm a threat intelligence engineer I'll look at it from an investigation perspective and show you how the originally the research company companies looked at it so one disclaimer everything I'm showing you here this is usually comes at the end I wanted to put it here in the front nothing is a result of my company's
investigation I'm just a simple intelligence engineer there are much smarter people out there that we're running research for years and just to name few the information you're going to hear today I just gather it together from eyesight very strong investigation from kaspersky BAE and if I missed anyone with the camera I apologize yes all right
you that's a very good question so why my why I call myself threat intelligence engineer just because of that reason the way my position is I'm collecting all the information and we using a threat intelligence platform make it visible and available for analysts so 13 telogen terrorists are almost my customers fuel okay no um you probably hear the little accent it's not a North Korean accent I'm originally from Israel and my career started in the Israeli intelligence Corp so I have a long history with intelligence by profession I'm an electrical engineer so is another reason why I'm proud to call myself an engineer and I moved here 15 years ago and worked for multiple vendors specifically in
user behavior analytics network security and threat intelligence so just to get an idea of who am I speaking with how many of you know okay who knows what IOC stands for which yes which just shout out the answer which number is it 1 2 3 or 4 or yeah oh you were three orth trying to make it easy who knows what's the second phase of the kill chain who remembers is it rotation delivery weaponization or if I if I did anyone remembers so the first one the second one is there were we ponies ation first one is recon reconnaissance last one who knows what's TTP stands for
three that's correct okay so no more tests I just wanted to get an idea of who am i speaking to so this is the terms that thirteen telogen analysts work with so let me just give you a little bit overview of how these investigations are going on in general and then we'll get specifically to the one with the Korean so what are you sees in indicators of compromise our artifact within the network that indicates a some kind of an intrusion now it could be also a host-based hash files file names registry keys those kind of indicators would be network based IP addresses domain names URL now each one of those indicators and be associated to a
different phase within the kill chain so for example a domain name could be related to the email address of a spear phishing attack this is the delivery mechanism right an IP address could be related to the command and control server the the hash file could be related to the specific malware so each one of them will help us resolve this mystery investigate and find how this hack progress now there is a term called a pyramid of pain I don't know if anyone heard about this but this is a term that actually came in one of the post of a guy named David B Andra Bianco sorry who is was trying to describe or categorize the
different type of indicators okay and so one of the ways to do that is to look at which indicators are harder for the adversaries to change so whenever you have adversaries continuously working on an attack they trying to change the indicators now it's relatively easy to change an IP address right nothing too easy to change a malware hash file right you just need to add different couple of bites into the file and then little different it's much harder for the adversaries to change the tools the malware pieces themselves always are mostly reused again and again so when we call it the pyramid of pain the pain for the adversary as you go up the pyramid is higher and higher and
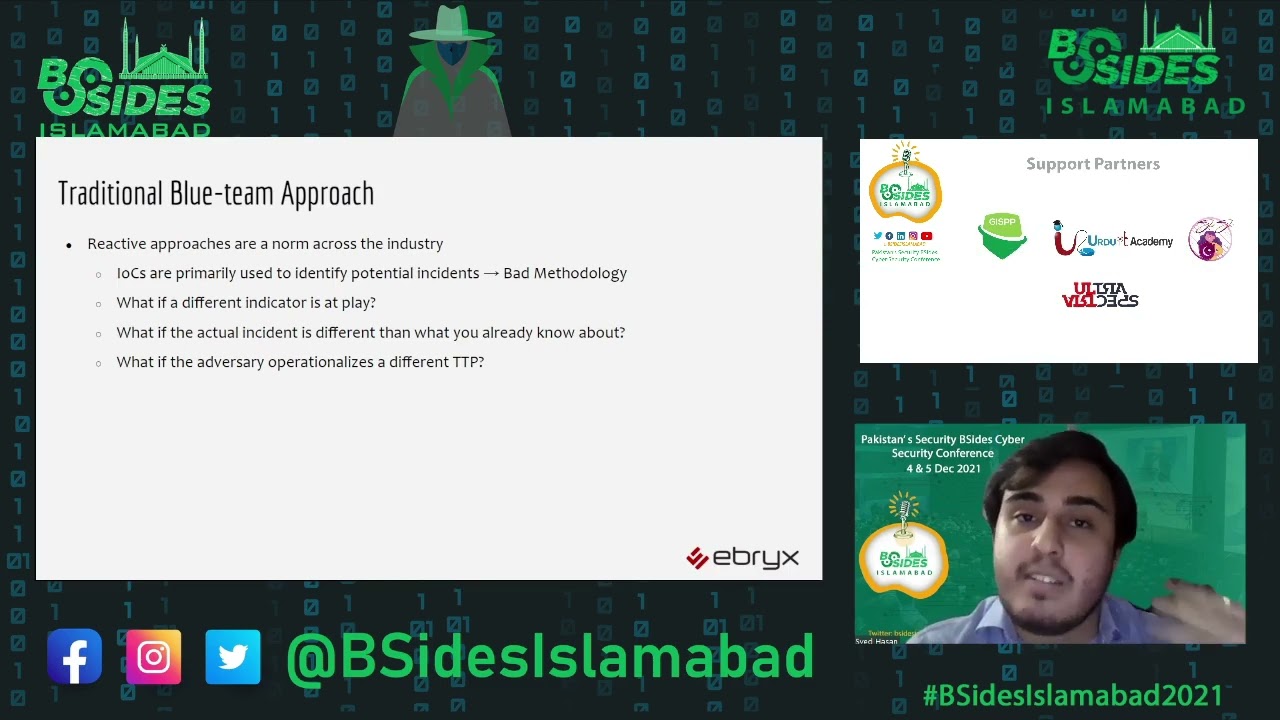
finally have TPP's like we said it's technically the procedures those are the actual behavior attributes that we can collect together and what I'll show you today is the TTP's of the Korean hackers what make us believe specific attack is coming from them and how those attributes kind of leading us to one one specific location now by the way from a defenders perspective it's also true it's relatively easy for us to identify the IP addresses for my forensic evidence we know exactly well malware connecting to a C - what was the IP address it's much harder for us to identify what are the tactic techniques of procedures of the adversary
investigation we're going to use cific tools you probably all familiar with right we we're getting a malware sample from a crime scene we find it we put it in a sandbox we're trying to look at its behavior we're analyzing the code we compare it to other samples we have and so on we're looking at network traffic we're trying to identify specific signatures within the traffic back and forth and then we're looking at specific log files but then the infected hosts those are the two
we're getting into what happened or serious of event by the way this is the name of a children book anyone's familiar with that you like it I my daughter loves it she so she read all the books and now there's in Netflix I think they have raised they made it the serious there I love it I see together with her so this is a series of unfortunate event coming in from North Korea and this is only a partial list right we see we see activities starting actually from 2009 a mainly attacking the South Koreans government South Korean broadcasting we have everyone heard 2014 there was this movie that that was about to make fun of
kim jong hoon and mysteriously after they were about to release it we had the Sony hack which is a big deal yeah with so so this is why I'm telling it as a mystery the fact is that there was a lot of activities that nobody connected backwards but in 2009 the there was there were attacks on South Korea as well there was a black sea all and there were some the beginning of what's called the block Pasteur operation though it's all around - South Korea the activities were actually eventually were linked back after we look we're looking at here so that's why I'm telling the story from 2013 because retrospectively later on there were some evidence that it's
related also to activities found in 2009 that makes sense a lot of the stuff it works is it's you find something and then it's starting to conclude to the path
you
well that that's that's good question well it seems to be that since the the rise of kim jeong-hoon there was an increase of cyberattacks I don't know exactly why but but that that's what the trigger by the way you I'll show you later it's it's not only for the cyber attacks it's also for is nucleus weapon arm and is for is the missiles testing and so on so seems to be very ready for war but but but those are by the way there's a very different places that he is hacking right is this is like a Sony hack this is a media type of hack this has to do with with political maybe and now we're looking at
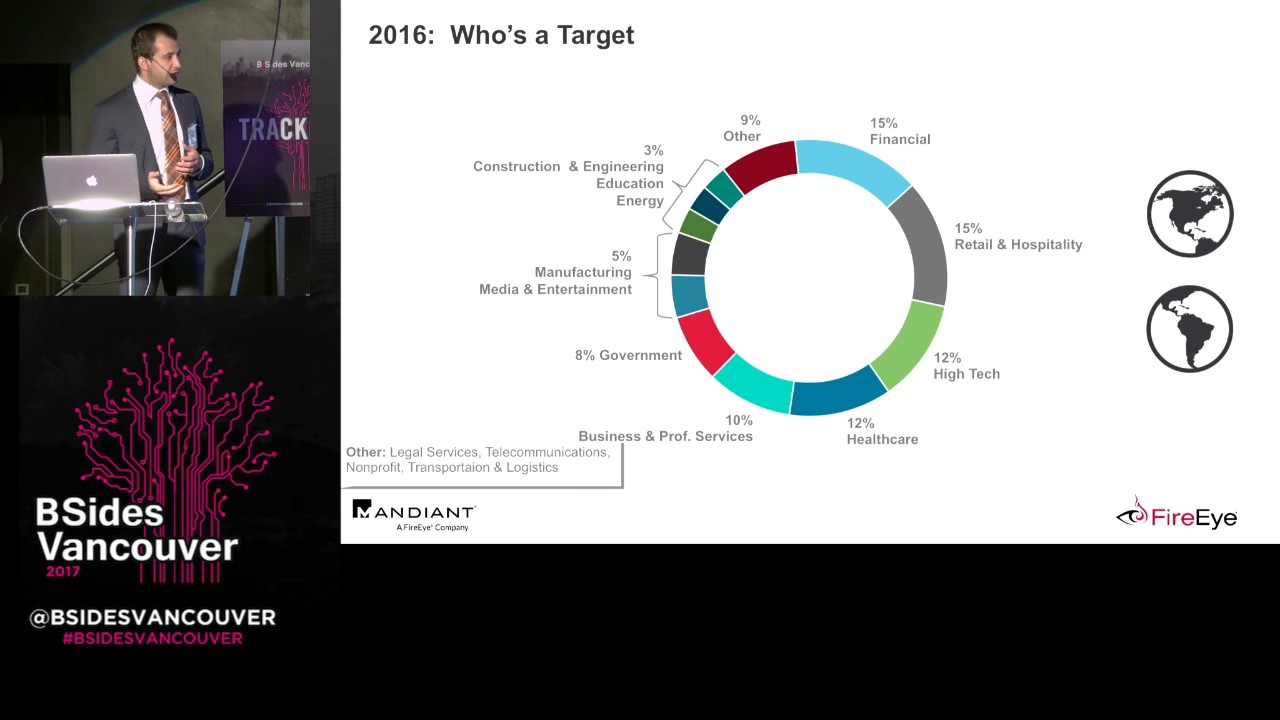
you probably heard that a big central bank of Bangladesh 2016 and there's also some hacks during December 2016 associated with some government official smartphones in South Korea and the latest we hear is some association would want to cry so the question I'm trying to answer first when I'm looking at TTP's is what's the motivation so if it did anyone hear about the most laws hierarchy of needs yeah so so I'm trying to look at it and I'm asking maybe you can help me when when we're looking at for example the the block of the release of the movie where is what do you think it's in here in in then which needs are being basically addressed when I'm trying to
do that
the top self-fulfillment its almost like cyber bullying right yeah who said that yeah that's maybe maybe you know feeling of accomplishment maybe if you feel a little bit good about yourself you know you can you can pani someone who was trying to make fun of you stopping the British television from broadcasting the story about you know the nucleus in yunyoung and in some kidnapping of a science give you something similar but hacking the South Korean Bitcoin exchange that's money
and obviously that the old stuff against South Korea I prefer sounds like kind of almost here or somewhere in the bottom like security safety even though might not be the case sounds like North Korea really feels that they are under some kind of attack continuous attack they need to protect themselves so there's a lot of psychology behind it then your question earlier you can see here that there's an increase in example in the number of North Korean missiles test so we see increased in the cyber activities kind of going in parallel with with with other activities in the physical world and what could be a one of the reason for them looking for American dollars or
for money what do you think exactly they need to pay for if you know how much it cost to build a nuclear project or to run so many tests on missiles North Korea is a very poor country if you look at the people there on on the street there there's nothing to eat and meanwhile the country needs to finance these cyber activities infrastructure in taking care of the army all of this cost money and they don't have a real way to access your make American dollars and so that can explain that that makes sense right so we're going we're staying on this pyramid here and we're looking at at something that represents most of the
attacks associated with North Korea hackers and looking at four steps first step is compromise a single server so there's a very common way to do it right either you're attacking a harmless site and trying to implant your exploit there or you're having a malicious site and then once you done with exploiting it you're getting the robber The Dropper is starting to move laterally and then second phase with with our case here is to look for the money and so in the example of the Swift everyone heard about this Swift attack just looking for this whip server where the Swift server is how it works how it operates hey they're doing reconnaissance but this is different reconnaissance this is the one
inside not outside reconnaissance this is when you are already have a foot step within the environment and you can start looking or the actual way you eventually create a transaction a forced reduction of money those are the four steps now those four steps were running over multiple banks and financial institutions all over the world so you can see here the targets are definitely financing so you're right on the point there they're trying to finance their activity and they would go anywhere remember Bangladesh is going to be what we're going to talk about but it's all over the world and it's financial institutions casinos right currency very easy to hide it coins and so transfer them to to anything else right so this
is where they after
Oh let's go down in the pyramid of pain now and try to understand how the Swift Network works so you familiar with the Swift right well I had to transfer money from one bank to another one country for another is this the swift code this is the bank code that you have and there is somewhere in between a swift net which is a network that is maintained and supported by Swift organization so they sell those services to the madness so let's see estimates using this using some kind of a software software is going to connect to an alien's connection this is kind of an interface with the Swift Network this is important to remember remember that aliance has to
do with with what the hackers eventually needs to find a way to get into the islands connection and then when they are in their network they need to be able to create a bogus translation transaction that makes sense now it's important to understand here that the kind of very but a the transactions themselves a fulfillment of the transaction is not part of the Swiss protocol the suite protocol is telling the intention eventually the banks themselves between them needs to create a transaction but they rely on the Swift The Cure Network to tell them what to do you see the difference between fulfillment of transaction and just ordering a or requesting the transaction
okay so this is we going down the pyramid of pain now we're getting into tools this is made in North Korea to cold drop you can see here that just like any other software it has version this is version two and he drop is very sophisticated piece of code this is how it works it starts with a 1/4 layer it's downloaded player the player is itself is going to have two files and one of them will show a video of its video player and the other one is going to take over one of the windows processes it's going to inject malicious DLL there that will download a second drop so it's to face kind of execution the first time
you get a proper it down download an additional file that looks like a a regular photo and then this one is going to what's called create a process Halloween take the specific malicious and put it under a valid windows name at this point we installed the malware the malware has the capabilities to communicate it back into command and control this is basically the basic commands that are supported by a drop too so you can start uploading file downloading files modifying C to URL so the hackers could keep on changing their command and control servers and this is related to what we said before pools are usually not completely changed by the hackers they're modifying least
slightly but this is Kaspersky for example they managed to find this piece from 2009 and compare it with the with this one which is the 2016 and find some similarities this is where you're trying to look for attributes and if it's something that was attributed before to North Korea you find it somewhere else most probably it's going to be the same group with IP addresses you wouldn't be able to do that right because it's not easy to identify an adversary by IP address because IP addresses could be using any infrastructure but by a piece of malware such a strong type of an evidence this is the second tool called corny so it's it's it's a rat remote access tool
that is used by North Korea for a long time you can see the history of it I like I like this one because it's really it's like a regular development of a product you have versions you have the the first version then you have a little bit of feature request maybe someone within the hug group sit there with a roadmap and get some priorities and needs to work on timeline so it's actually it's actually started as as just as a stealer just all the information but then you can see here the 2006 it now supports remote administration and you can see that 2017 2016 was the road remote administration 2017 now has screenshot features so they
malla virtually can take screenshot and send them back in into the hacker learn about activities when the users you know that's going to play a big role when they will have the internal reconnaissance trying to figure out how to enter the Swift system and what commands they should run in order to run this action
so another is another system used within the the attack is what they call a proxy malice are you familiar with proximal words what's the proximal where this can help illustrate that the proxy malware is when you have a malicious malicious file installed as a proxy on a victim and used the host as a proxy without the victim knowing about it so the way it works is somehow you get exposed to to that proxy the proxy is being installed the proxy now and poke a hole in the firewall in the case that I'm looking at here it was also a Windows Firewall and so the malware was running a confiscated command in natural firewall in order to
open the Windows Firewall which is also a very important signature this is a very unique way to do that right the way it's constructing the data here and then once it has this it can go over three outside into a proxy server okay so we get this connected to the proxy the proxy is verifying that the connection is there so now we have an outside connection that works now we have the hackers getting it to the proxy and accessing this proxy and from this proxy de conducting a command-and-control this see what I'm saying so they are they're not utilizing any valid IP so what's the problem here for for us for the investigators or for the
engineers we don't have a domain there's no an IP address all the communication back and forth is from and own toast anyway I cannot do anything I don't know it's coming from I cannot even run a sinkhole I cannot get anything with this malware so Koreans are doing this a lot they have a number of owned hosts that are used as proxies and they operate through those proxies and running all their attacks through it one on one with the remote access tools this is very sophisticated
not not necessarily mobile platform mobile times I mean the the the interaction with the user is important here because you need to install it but it's not always a mobile platform as Papa halfa proxy could be installed anywhere but beyond the backup it could eventually end up being on a backup server that nobody's touches
so we're talking about this backup server now that the inside and they have a foothold they moving to a place that is relatively low doesn't have much of of scanning or a much of monitoring on it and they stayed literally eight months before they executed eight months they were sitting in a bank waiting for the right moment learning and learning and developing and moving on without link code now this is from Kaspersky it shows that at some point they had to actually remove evidence so they killed himself when they felt that someone is after them but they still had this little foothold that can bring them back whenever they felt that they're out of trouble
and so by the way that means that there was a person beyond the other side situ was not a botnet it was not automatically there was someone there sitting monitoring making sure that it interacts with the malware piece and based on what they see oh you know it's it much more targeted and much more customized than a regular distributed mouth oh let's look a little bit deeper into how they got into the network Oh following the kill chain we're looking at like I said the first thing you need to do is just to have one single mistake the human element talked about it earlier right one Hindu person needs to write on a on a Ron link in this case it
was Hangul I've never heard of it before but apparently this is a application for document that is very popular in Korea and there is a vulnerability there and that vulnerability helped to install or download the first drop oh there was a DK document here and it opened using this specific application and exploiting that specific vulnerability all right so now we got this this dropper we we can get a back door we have something already inside the network that can move to the next step but we we looked at some or companies we worked with looked at some of those back doors and so similarities you can see the similarities again between history back doors current back doors and one
interesting item that I want to point out is that some of them use some Russian words but you'll look at the Russian developers looking at that it was very fake low kind of level of Russian was it looks like there was a an attempt at least try to attribute it to a different country
so now we have it the dip dropper starting to install them our this is this is a relatively unique technique where the malware was actually a two pieces of malware and each one of the pieces was installed in a different host and so again from an investigation perspective it's really hard you find what is the kill chain if you show only part of the puzzle if you saw only one of the files so as an example here is there's a a Trojan dropper sitting on host C and then there is a another backdoor found in host D and in order to execute the Trojan the backdoor remotely run it as a command line in other words
if I'm going to this computer and I'm looking for it I would not find anything after looking for this computer I will not find anything I need to have the to precess in order to being able to see the that's relatively unique and there's another example here where you need to inject a DLL from machine a into an executable in machine B really sophisticated no another and other information we we see here is some cases where the control is directly from the end-user there's no command and control in the middle makes it very hard and you can see that for the detection tools there are in a attempt you disguise as Mozilla but it's misspelled
it's Mozilla and the trying to create a a fake SSL connection outside but it's not really SSL it's it's a fake and by the way all of this code is is also encrypted and so you to decrypt it takes a lot of time so there's a lot of effort cover and make it hard for the forensic evidence
okay so this so the first stage is done we got into the system now we're moving to the second stage the second stage is we need to get it into the Swift we don't know where we were in the backup server we don't know where the sweeties we have time trying to run recurrences we're trying to look for the right place where the swifty but we need higher privileges and so there was a privilege escalation you got into server as user X we moved it as an administrator and then we created some tasks that can remotely execute on different hosts and so at this point I'm trying to figure out where is my target where's the Swift
system it was very clear that they're looking after the money
everyone wake up we're getting into the interesting part the money connecting to the Swift so this is and this is actually really really really interesting because the Swift system something you need to learn each one of the installations is a little bit different so here's the way it works first you look so this software swift Alliant server it's kind of the the link between the bank and the Swift Network so you look at the software and you're trying to identify where is the data the data is stored in a database but in order to find where is it you have to get into the configuration file so do you decrypt the configuration this is all time this is why it has to take six
to eight months in order for them to eventually develop a specific malware for that specific system it's not a commodity room over here it's very dedicated model for that specific environment you create you you create the malware and now you test it just like a QA in in a regular environment you're starting to look for the transaction you monitor them now here's the problem there were two problems the first problem was that every transaction regarding of the system the bank had the policy that he has to go and print it to the printer so there was a hard copy of the transaction now they didn't want their transaction to go to the printer right so the first
mission was to is able a print of the trend the defect transactions right that's one thing to deal with they can deal the deal is you're being able to construct the fake transaction so it can go as a legal one within the suite with network so nobody will suspect it's it's you know it's not coming out of the bank right so they had two problems to deal with and they knew you have to know for both cases what's the problem with problem is the technical or is it procedural and so they had to prevent this now this is getting into details but the idea is that this is all under a testing phase it were a couple of times where they
were just trying to test it just trying to make sure that they can do it now most likely they had also recreated the similar environment within their systems but they created Swift emulation think about how professional you have to be because you know you have one chance it's not like you will be able to you know you failed that's fine let's write again I have only one chance though have to have patience and you have to go through all the scenarios within your environment before you run them on the real production so to speak and so they did and this is the Swift malware that worked there was executed with different changes depending on the environment on
multiple places we heard about one huge event but this was running over different Philippines in other places where they were trying to do exactly the same thing
but that day arrived probably was a very excited day but then think about it it worked for six eight months like it's like the delivery time that's like like launching iPhone 7 hit everything is supposed to work and you need to do it fast why because I told you this Swift is is sending the request the request is fulfilled and if someone is having any doubt it can cancel it in them and so after it fulfilled do you need to go into the bank take the money and run away so at this point you need to be fast you need to be sweet so they'll be getting into the they're getting into the system and they trying
to few transactions and after that that's it they killing the evidence they don't want anything to stay there removing the DLLs that responsible for the database from the backup and restore off of the swift they're removing some other files and they're running after the money and this is what happened so first of all this is a credit to time on chai so this whole story was very very nicely illustrated here so let's find let's find okay this is Bangladesh Bank this is the bank that was compromised originally they were trying to steal nine hundred and fifty $1,000,000 they were trying to transfer twenty two the Federal Reserve back and then to Sri Lanka this one was
blocked so those 20 were saved however 81 million as a result of four orders that successfully transferred our CBC in the Philippines got the money and they got it 81 million dollars were never recovered out of this attack 81 million dollar can you believe that
you well someone took the money the money moved from to account once they fulfilled it the Swift Network said this should be moved from this account to this account the account was a fake account but it was an account right someone owned and once it was there the bank's just followed the protocol I want to kid up and until today was not recovering I don't know they will never recover no it's just everything is wired but you take the money yours now the banks could have gone to Swift and there was a big you know conference where they were trying to say you know it's not our fault maybe Swift should pay who should pay
for it but the money is gone and you can see here that this is trick was tried all over and all over now since then obviously the aliens that were with hardening their security at Sur etc but we know for sure there are still attempts to run those type of transactions using other techniques but again over Swift so who is behind all of this so we know it's North Korea right at the motivation everything shows that it's from North Korea but what what would be the researchers call them well you heard about the les Lazarus group Lazarus group is the name of the group that researchers hold responsible but this is another attacks now as in North
Korea everything comes from the government it's not like they're independent so we believe that the government under the reconnaissance Bureau has a specific unit called Bureau one to one Bureau one to one it's in China and employs hackers the government employed occurs to do exactly this financed the nucleus weapon production finance their cyber attacks and and so on run things like against the Sony hack etc so there are all government employees and so all of those operations and this is the 2009 that you asked about this is the Detroit pression yeah
no this is our attic well now obviously they don't it will not admit that they have this Bureau one on one so they have bureaus that are officials and then we call them bureau 101 one-to-one yeah yes and this is a group that sits in China mostly and they're responsible to write those sophisticated tools
No you have ten more minutes so let's try to look at how we can what we can learn from this about North Korean general which obviously North Korea is going to continue with cyberattacks it works for them and it doesn't looks like they're going to reduce if anything from what we see today in the news they might utilize it you go after the US government but also maybe us facilities like manufacturers infrastructure maybe nuclear plants their main enemy is South Korea so we will keep on seeing the South Korea being attacked and financial institutions they will definitely need to keep on financing their operation through
now one of the things we know from intelligence is that north Korea has programs for students it's the way I like to explain it it's like you know the Russians when they prepare their athletes to the Olympics from very very early age this is how they're doing it for hackers in North Korea they have over 200 specific institutions for programming for software programming they designate the students there and then when they're done they're done with their education they're going for hands on hacking hands on and then they sending them to China they're also getting support from Russia so we know a lot of the hacking tools that Russians are using eventually ending up in the hands of North Korea
and those guys are dedicated to work depending on on the agenda of the government so anyone heard about wanna cry No so this is the latest news they hear the latest news with one a Christ we don't know to date who to attribute to wanna crack where I wanna cry is coming from there's no specific group that was sure is associate with however semantics and I want to mention name not sure but I know at least two or three research companies starting to believe that there is a connection between one a cry and the Lazarus crew and the reason is because again forensic evidence their specific our pieces in a dropper of one a cry that originally being used by a
Lazarus group the dropper piece from earlier earlier times associated with Lazarus now one of the things that it could be it could be a false flag right it could be that the guys from wanna cry want to show that it's not you know it's not Korean it's not I don't know Russians but what what interesting is that the latest instances of wanna cry don't have this piece of code in the dropper so you know one should ask why would guys that were trying to discuss themselves as Lazarus group all of the sudden will remove this part maybe that's reserved group trying to pretend they're Russian trying to pretend that there you'll never know it's like it's like
it's very very interesting what people trying to do in order to disguise as someone else so we the prediction with regard to North Korea in in general is that we will keep on seeing those disguise so even though North Korea feels pretty free about doing everything they want on cyberspace it's still not happy to disclose that this is really admit whenever there is a an incident most people believe based on the current activity that we will have wolf or warfare also political we see how political elections and those kind of events are triggering attacks as well damage to infrastructure this is true in general but but also relevant for North Korea espionage goes mobile since a last
incident shown that South Korea's government officials were hacked on their mobile and naturally mobile is less secure so it makes sense that they will move together with the rest of the industry to mobile and
also the prediction is that those sophisticated mowers that were created in specifically to to hack Swift would eventually become commercialized so they're going to be sold in the dark web and other hackers from other countries will use them and so probably we'll see this coming more and more as far as want to cry I don't think there's any decision yet what wanna cry is coming from when what's the end of France and where in general there's some French creatures now that have ransom where's that instead of taking ransom are actually damaging and distracting environments which doesn't make a lot of sense unless you are in a warfare and so one of the things is that there's
there's a kind of a broken trust today between the hackers of malware's and the victims and so if the hackers dimensionally don't get the money it doesn't make sense for them to create all this ransomware right so the salt maybe maybe they're try to kind of build a trust between them and the victims make sure the victims know that they will get their file back if they pay and Internet of Things like like anything else that will move as well with the North Korea I don't know if if there's any questions when I talk too much so up for a second if there's any what do you think any question any thoughts this kind of or off the usual preach on
how should we protect the stuff right to better with with data protection we should do better with perimeter we should do better with user behaviors education and so on I don't think it's specific to North Korea but um it it should be applied I think what banks owners and financial institution owners needs to know is they need to be aware of the North Korea the service group and its potential because this is one group that can and continue to under estimate if they're on Thurs to made them there will be surprised right there's going to be more and more involvement from from North Korea there yeah you
Bangladesh one it's a hat yeah it's it's agreed upon all that this is coming in from North Korea a lot of the activities there so this example was sweet but there was also an attack on the South Korea Bitcoin exchange and there was an evidence that eventually this was converted into an infrastructure managed by the North Korea caucus it's directly going you know operation directly goes to operations it's about the way a lot of companies actually describe it is a subgroup of the subgroup that deals only with finance so there's the group that deals with the political and and they were fir and then there's a sub group that deals with making sure that they
have enough money yeah I'm not going to get into this we all know what we need to do obviously don't do that and we know what we need and just to summarize is it this is the report again Kurtis to Kaspersky you can look it up look up Kaspersky and the Lazarov group a very interesting story actually detective story so it's very cool report to read I can give you the exact legs if you want me to then to summarize I will use the quorum I'm not a group but a great book reader but there is a book that I read you know anyone read June um by Frank Herbert and there's a saying there by by the u k-- so u n-- is about
a specific planet full of sand and then there's another planet nobody heard about June yes oh I'm sorry dune I knew my Israeli accent will will get me sir how come nobody knows about you doing all right so who knows about dune oh I get scared I mean in Israeli knows about it and you don't No so you know the Duke Leto that the the father of Paul was there on when when their planet was full of water and they would have decided to move to do he said to his son yet I'll miss the sea but a person needs new experience a jar of something inside allowing him to grow without change without change dumping sleeps inside us
and seldom awaken sleeper asked awaken what he's saying is we need change in order for us to fulfill yourself this is I think something generally for us as security professionals you know when if we want to feel ourselves to be better in our profession we want to change we want to maybe a little bit get a little bit more knowledge maybe get another class maybe learn from a college and also as as as analysts or when we're looking at those incidents with time there's a continuous change the adversaries are not stopping you keep on changing and we should do the same so with that I thank you have a great day