Unparalleled Remote Desktop Monitoring: Revealing Attackers' Tradecraft
Show original YouTube description
Show transcript [en]
all right welcome uh we're going to start our first uh uh presentation in track two uh we are very honored to have it's very difficult name to say Olivier vadu and he is going to speak uh on a presentation from RDP to D and D unparalleled remote desktop monitor monitoring reveal of attacker tradecraft so we are very well honored and welcome to have and I'll turn it over thank you so much for being here thank you you guys hear me all right I'm might all right that sounds good perfect so uh this is um the Standalone or by myself presentation of something we did at black hat USA this year with andrean beron so first before we get into the
content I want to knowledge that this research would have been uh impossible without andrean and so andrean is kind of the gandal of the research she is the knowledgeable like you know the the the most powerful character of this story unfortunately she isn't here and because of my kids I started playing with Snapchat recently and so I wondered how Gandalf would look like as a woman because Adrian's obviously a woman so this is with a Snapchat filter how looks like but so if andrean is gandal who am I then well I'm the gollum of this presentation okay I am uh why Gollum it's because I am just obsessed with RDP okay I've been working four years
intercepting RDP and developing open source tooling around intercepting RDP at first I started it uh for red teing purposes like red teaming and and Pen testing like to attack from an attacker standpoint uh attack the client's side of it uh some use it in scenarios where we would compromise organizations but then as I was playing with it I realized that there was a lot of value in it uh through honeypots so for understanding criminals and I'm going to get to that but this is what this presentation is about but golum it's because I'm so obsessed with the RDP ring to the point that I am broken I can't talk about anything else than RD P the precious RDP
so the the talk is going to be about Dungeons and Dragons nerdiness and puns and stuff like that but but why did I think that it could work that it could be accepted at conferences like here right it's because of Stranger Things Last Summer who really did a well integration of DnD D inside of their their world and it it's from the season one but season 4 there were like literally playing D and D so I thought I we could pull it off and then the movie that came out this year honor among Thieves there are like the character classes are well uh interlaced in the story and stuff but I want to say that
in a true like old school DND fashion the pop culture reference ends here like this is like character classes and weapons and stuff it's it's no no no stranger things uh imagery it's all custom image that we had an artist uh do for us for this presentation so the quest today is going to be um I'm going to introduce you to RDP interception because you might not be familiar with it and what we are able to achieve and show you how it looks like then we uh over three years studied uh people attacking our systems so we're going to go over five broad areas of how they they do their their their craft uh this
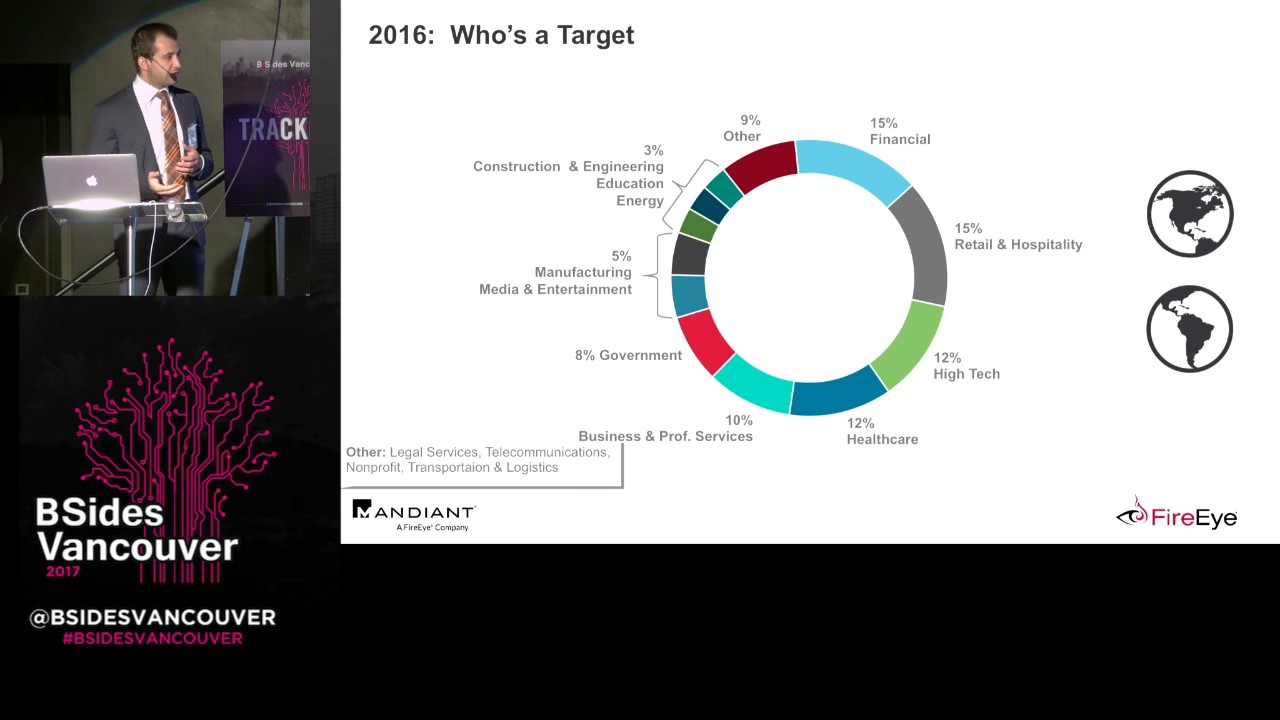
covers over 190 million events uh by the way we're going to look at the tool that they use and then we're going to highlight some specific session that are like interesting uh in on their own so here are the characters that we will look at today uh five of them one of them is well hidden and so uh let's start with the the context so RDP is a targeted protocol very uh attacked it's the second uh ransomware Vector after fishing attacks so it's you know right for for for being studied if you want to understand adversaries uh I I started first you know attract attracting adversaries using tnet and SSH I actually wrote The tnet implementation
of Kye the first draft you know someone else made it better after but uh at that time to track a specific strain of malware and um the what what was is disappointing by running these types of of Honey Poots if if you have done so you you'll you'll agree I'm pretty sure is you it's just a ton of files that you're getting but it's all the same more or less malware and it's all automated there's almost no human behind these things it's all butts running on their own RDP is the total opposite it's like 100% human they move the moue they there there is ways to interact with RDP using automation but I'm telling you
like we watched over a 100 hours and they are moving the mouse they are copy and pasting stuff and you'll see you'll agree um so because of that to understand adversaries it's a a lot more relevant protocol it's it's right for intelligence collection about adversaries now if you've never heard of RDP by now you're like what's what's this talk about so just to be really super clear like ground level uh explanation the RDP is like the left hand side this is the client so you tape in a host uh you type in a host and uh or an IP address and then you click connect and you authenticate and then you manage a computer remotely and so we
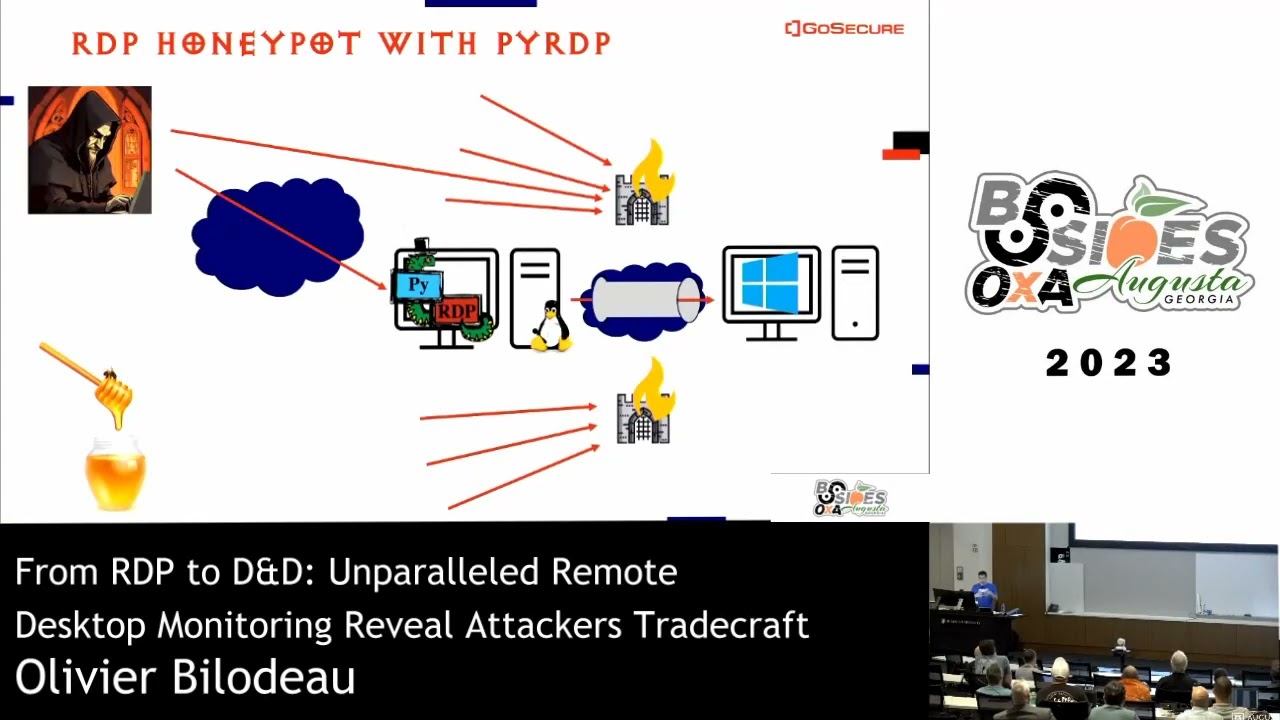
slide in between and intercept all of that the Tool uh is called PDP it's been four years in development so it's a a monster in the- middle engine uh and does interception record everything we temper so the tempering bit for example we will actively steal clipboard updates from client so the pro the way the protocol works is that the the the client notifies the server that there's a new clipboard available and in the tempering engine we always say I need it right now right and same works for files uh when you share a drive or when you use uh drag and drop to drop files on the the destination and we so we record everything and we also Jon log a lot of
stuff um but there is also a player and the player allows you to rewatch everything so it's very interesting for investigations I'm going to show you what it looks like so here we go that's the the RDP the P RDP player so here is going to be where you'll see the display now this is the mouse pointer it's a little yellow dot we are we have a big screen here that's going to be good on the bottom you have like metadata about the connection this is where the clipboard board shows up in real time uh and here we're going to zoom in you see when you connect you get username password domain host like really RDP metadata now we have someone
connecting so this is the the recording the way it starts we instantly stole his clipboard uh which is the IP address that he connected to this is often the time the case now we see him type interactively he's typing uh to open a tool and then we see he's he's resetting the administrator password and we see the administrator password because we have keyboard access right and so all of this is collected on uh some ones connecting to the the computer he shared the his C drive with the the Honeypot and now he's listing it and we also collect the the the data so we can aggressively steal files but we're not doing it uh right now on purpose because
we fill hard drives with that um we are collecting the file transfer right now but the the the tool allows that right it's it's built in it's just you need to enable it but so now we're we're uh he is drag and dropping a crypto Miner and we are collect uh we are collecting what he is drag and dropping so basically what we saw is a surveillance cameras for Windows system right how can this not change the game regarding uh online adversaries now the unot how we built it uh we we put the Tooling in front of a real window system fairly dangerous you need to monitor it I I have like on my phone I can destroy the honeypots I
built like pipelines to be able to do that so if I get abuse notifications and stuff like that but so and and everything else is firewalled so you cannot get to that system unless you pass through our uh our tool if you want to learn more about PP I've been talking about it for since four years in the offensive context defensive context there's a tons of there are tons of links uh the GitHub repository has links to most of that stuff and the the slides that are going to be available will like these all were all going to be clickable in the PDF so you can uh refer to it um now today the DND the character classes
what are are we going to talk about well first what did we watched what did we collect so this is a timeline so since 2020 up to now the these are the events you know at the bottom you're lucky cuz most places I do this talk they they're not able to see the bottom line um but so the the the the the the map covers like actual sessions where they were able to log in so these are not attacks or credential attempts or like hits on the RDP Port these are people who logged in the system and interacted with it a lot of Panama I I want to study that it's I I'm not sure like it's most
likely proxies uh we have ways to like understand Beyond proxies RDP leaks a lot of stuff and not a lot of adversaries no like for example time zone is part of the RDP protocol it's embedded in the connection and so we could like correlate does the time zone in the connection make sense with Panama and if it if it doesn't then try to you know dig further but so this is 190 million events uh we captured a ton of hashes so every connection attempt will generate a net ntlmv2 hash we captured 21 million of them we cracked 3 million of them uh out of an experiment there's a blog post about that if you're interested we we we
quickly I have time so I'm taking it usually I'm not talking about stuff like that but out of the 20 million hash the the thing I want to say is we found something that is different than other uh security companies said security companies say oh everything they try is part of U of the uh the big breach the com collection one breach or the the the the big one right and our findings are totally opposite like out of 3 million hashes we cracked like 2.6 million of them successfully and it was almost always custom it was like U um iteration around the name of the certificate of the RDP like we we use the it's called
offshore Bank the the certificate that we used and it was all like around like like computer generated but around the offshore Bank uh topic so for us it's a they are really targeting um the the they they're tailoring their Brute Force attempt to the the target which is different than what other publish uh we had out of that 2.6 million Su uh 2.6 2.6 th000 uh successful lugin 500 files transfers more or less and 2.4 th000 uh 2,400 um sessions were captured now out of those 2 uh 2,400 sessions we found um 95 more or less attackers because you know session is one time they disconnect and they reconnect so it's a different sessions but we correlated them based on
username and password IP address but so if they log in change the admin password to something custom then and they get back in we assume that it's a related attacker in some cases they look it looks like they sold the credentials to other because we had like someone sophisticated and then someone really not sophisticated and you'll see what I mean by that um but so we have we we studied 339 sessions of interest and this is over 100 hours of videos so this is where gandal comes in and like watches all of it and really like no takes a solid note about what's happening in the sessions I watched maybe 15 hours of these 100 hours and and um um of
sessions of Interest I was brought in you know to to give my my expertise what I think about it so inside of these 100 hours we wanted to um to map this to the attack framework and what we we have is mostly Discovery related activities some reconnaissance so uh scanning other systems uh even online line right so we didn't give a fake Corporation we gave like a basically a standalone system and so uh as soon as the adversaries were were realizing that this was not a company and there there was no lateral movement possible they would then scan the rest of the internet and I have like theories about why that I'm going to cover later now if we go about those
character classes okay get back to them the first one I want to talk about is hidden here very well and it's the Rangers so Rangers they explore the system they do reconnaissance they might be evaluating the system for others they might resell systems uh but so here's what uh they're they're not doing anything meaningful like they're really like Rangers they're Scouts if you want like doing the exploration so here is what it looks like here or he drops two files on the desktop he or she I don't know to be honest uh but uh he he uh it drops two files on the desktop and then uh copy and paste Intel that was generated by
one of the tool and then copy and paste in tell that is generated by by another tool what I like about the second tool is that it's a Json payload so the first tool is like text right so okay he copy and paste text and in W right a notepad or whatever how how is that useful but the second tool it it being adjacent payload I feel like there's a tool chain right that we don't see here like the Json payload goes in a file somewhere something interprets it and then you know classifi that compromise system as something that they might get back to or whatever and so a and a as a cleanup step he just deletes the files and then
get get out of the system so these typical Ranger operations uh what we usually see also is like opening the the F Explorer to uh to to look for files and then you know walking around and and and seeing what's on the system next up is the are the thieves so thieves will monetize the RDP access using a lot of stuff more than I expected I expected only like crypto Miners and stuff like that but no we're talking like proxy Weare uh so proxy Weare is a class of gray Weare I would say like uh they are not malware but a lot of Av and um endpoint edrs will classify them as such um but they are
basically using your computer to uh to proxy traffic and you get paid for that so kind of like old school like I don't want to pay for the internet I have banners it's like similar type uh you know grayware um these are the the the tra tra monetizer type stuff but it's like a Trend Micro is doing really good studies around these tools and they labeled it proxy Weare and I like I like the name I think it reflects really well what it's doing and then there's the crypto Miner but there's also like traffic generators is the browsers that have that gets you into pay to serve schemes so these are like uh uh you get
a little bit of crypto as you browse the internet and they there's a revenue sharing model so they they install stuff like that as well so here's how it looks like what's interesting about this video is the first one you notice that is on um portrait mode and we were like why is there portrait mode RDP clients and then we looked at the resolution and and we uh looked at phones and we looked at the how many pixels the RDP client on a phone takes and we had a perfect match so we know like this is a Samsung with the RDP I think it's top and bottom there are some pixels for the the the
RDP software and so basically a lot of the adversaries are using phones when they are attacking our honeypots which is which is really interesting cuz it explains a lot of stuff like why are they doing so much inside the RDP and not doing more outside of it because they reveal so much as you'll see through many videos today but so this is the a tra monetizer so in order to download the software and and have it put money into your account you need a token you need to put a token in so he basically logs in that system and then get the and put in the token in the software that he installed and here we
are highlighting like the the money that is made and it's not a lot it's a currency that is uh is not us and it's not worth uh a lot so there these are basically pennies you know by day and stuff that they are doing but if they do it at scale then they might be uh making some money um next up is the crypto Miner so a lot of them are using XM rig very popular among criminal circles uh because it will do like uh CPU type mining which this doesn't have a GPU so it makes sense and so but they he's putting in his wallet like straight in the honey poot maybe one day I'll retire
CU I will catch an adversary so rich that I'm not going to need to work anymore I'm not I I to be honest I'm too ethical to do stuff like that but you know there's a price point um so the for me thieves are really interesting because this is a very good example about what cyber crime is about they're in most cases they're not after a specific organization they're just after making money and you happen to be that organization right that that falls victims I know I know there's a lot of targeted attackers and I mean there's a lot of mil military around here and this is not the same type of adversary you know threat model is threat modeling is
complex but for you know exposed RDP systems online I was not surprised at all to see this this type of behavior next up are the barbarians hard to miss so barbarians they just brute force their way into more computers uh they they uh they scan uh horizontally so you know identify other RDP systems and then they scan vertically uh they try credentials and they just like pound the system until they get in uh using two different tools uh that that we will uh we will see so the the big thing that they use uh is uh Mass scan Robert Graham's Mass scan very powerful and fast scanner uh that we're going to cover also in the Arsenal section of the
talk uh but so they don't use the common line they use a gooey wrapper uh that allows you to choose like it's kind of con convenient allows you to Target a specific country they they like in the tool put in like country and uh will adapt the network ranges I don't know how they extracted it but most likely it's automatable via who is databases or Arin or whatever uh but so and then it launches uh it just prepares the common line for you if you want so you just push a button and then you get your your scan and it's fast and they scan they're scanning tons of systems out there and they are also like they're doing 3389
but they will do like 1 3389 2 3389 and stuff like that so it is um uh something that they do a next up are the Wizards Wizards are interesting and like we labeled them as Wizards because of uh they use the RDP access to access other RDP systems so like portals or like you know uh jumping through host hiding their traces and they they will also in um in most cases not deploy any tool anything that could be linked to malware or like any anything that had has hits on virus total so they use mstc the RDP client which means that from a lug perspective they are hard to detect they are like hard or impossible right so in
this session so this is a captured session so in the captured session they are using RDP to connect to here we saw ghost user mentioned which is something that uh comes back often that we will see later but so inside that system now he he minimizes it and then Focus the window on a credential brute forcing uh attempt that is going on and so doing performing credential brute forcing on one system connecting to another one performing uh credential brute forcing minimizing it so he's basically building a dashboard of his hacking attempts you know looking at it from uh behind another and and this is all about hiding your TR right you're you're you're jumping through
compromised systems uh which makes you a lot harder to go after anyone who uh collaborated uh with law enforcement on takeown attempts you'll you'll know like every hoop on another ISP provider is just harder because you need to collaborate with more people get the logs I hope that they will be kind with you and and U and comply and so uh uh this is the the Wizard scanning via system other systems and the these are all like wizard type activities that we uh cluster together now last of the characters but not least is The Bard so the B is arguing the the the a small contributor this is actually a DND joke it's not true I know I I'll get hat
hatred for that but it's like oh you're a Bard like what do you do really like and even in the movie they they like assume it it's like you make plans that fails right this is what you do and so uh the the B for our story is is is like my favorite character because it does stuff that you would just not expect so Googling about hacking inside the compromise system not outside of it right and watching some porn downloading movie we think that they might have bought the access uh via you know forums Telegram whatever because they needed it to perform other activities uh but let's see what it looks like and so we're back
to a phone format for BS I it's not surprising to me so this person is like Googling in Arabic the strongest virus ever and then hoping that Google will give it the strongest virus ever so that he can compromise that system unfortunately he falls on a page describing computer viruses so this is the where the text is so he's disappointed go back to Google and types virus script like he's like I'm going to get this now and so now we have like how to write DS attempt uh how to write write python code he abandon and then switch straight to porn he tries porn.com first sex.com second uh sex. org third heran porn is fourth
and then he will go on YouTube and search for porn on YouTube like pornh Hub on YouTube like this is the disappointing but you know there there was so so the way uh uh we decided to attack looking at the sessions we started with the largest file size first okay so because we did that we had all the porn so basically RDP is very up optimized and it it it will tile the whole window in some in tiles and will reuse aggressively cash and reuse the content so if you use Explorer a common line you know a browser for regular sites your your capture files will not be large but if you watch movies or porn the capture
size will be super big okay so we started an investigation by going by file size big from small and so we were really disappointed at first like to the level that we had to involve HR like I was like I told HR like we are not watching porn n work we're we're like investigating attackers and like if the the employees looking at the captures are disagree I can put them on other task like they're not I'm not forcing them to go through the weird porn that we're seeing fortunately enough the porn was very vanilla it was like really regular porn so uh it it it went well but now we we were like wondering at some point
like why porn and then we thought about it and we figured it out it was coming from Mostly a Middle East countries and we think that to avoid censorship vpss are blocked in these countries uh uh VPS VPN are blocked in these countries and you know VPS like $10 us amount for a VPS it's probably might be too much for a lot of people and so a compromised RDP system is probably useful and where what uh tipped us off is one actor was downloading the the the movies right a PornHub you have a download feature I didn't know I realized when I was watching that so we're thinking like there's also so this is kind of a bar
Thief multiclass character I guess so he would like download the movies and then he could put that on USB key and sell it in his country right like like we used to sell pirated games when we were kids uh on CD you know you get a friend with a burner CD I'm I'm old I'm sorry uh but so we think that this is what's happening here they're not they were not like fapping live they were like downloading or selling or reusing the the porn so how do uh how do we like like it's fun to talk about bars but bars are not that relevant right it just happens to be the way we sorted files we
were inundated by B at first but so most of them are Rangers and barbarians and then you have like the thieves and the the wizards but uh you know a lot of it like if we would deploy our honeypots elsewhere than digital ocean Amazon we would get different results for sure so this is biased towards our experience uh running running them um there is some overlap so so so some multiclass characters as I mentioned earlier so the thieves and the barbarians and the Rangers and the Wizards and the BS they all like all of the classes have shown different behaviors again this is clustered based on Source IP and uh uh password so if the password was changed
someone connected after showed a different Behavior but this also shows the specialization in hacking right one person gets in he does the reconnaissance and then okay that system is L is in this category passes the puck to someone else who gets in and then does his thing um so it's uh it's interesting finding to do and and we are definitely going to dive deeper in in in that area in the future now let's talk about uh some of the Weaponry that uh we found uh these are are interesting because they are things that Defenders can act upon right you can detect the hashes and you can understand now oh if I see this tool it means that it's the
first step in in uh worse activities right and that that you you must not downplay the the the presence of tools like this in in your environments um so we built like little spec sheets for the tooling uh and we aim to uh to do Sigma rules so I I suck at Sigma rules I'm learning to do them but I would like like I I I don't like hashes as a detection methodology you know it's so easy to change a hash so uh I I want my aim is to build Sigma rules for all of the the tooling that we're talking about today uh uh and I mean I I think some of them already trigger some
of the popular open source Sigma rules but I would like to have them more narrow but so here uh this exd Z RDP patch is a strange tool because it's focused it has a graphical interface they almost all have graphical interface by the way which is interesting in itself uh but so it is uh it does like two things it creates an admin user and it um patches RDP to remove the limitation on desktop operating system that uh you can only have one session at a time so this is done via like a popular it's like it's not even B inary dll patching like it's it's it it puts a layer on top in front of the RDP
connection so it survives OS updates and it it doesn't blue screen your system it's kind of well done but and it it relies on an open source like GitHub binary that it drops and then executes uh but so these two function combined is you you really it feels like crime wear right they're combining two under related features in a super easy to use click click click uh uh binary um and the the the group behind the xdz group was taken down a couple years ago uh but still the tool like it's a binary file and it's on windows so it's going to work forever uh until they like you know re architect RDP but until they do that
it's going to work and so uh and and it's well detected I want to add so this is used by Rangers but uh ghost user we saw it earlier connect uh used by Wizards to connect to other systems so it's a very commonly used uh persistent uh tool persistence tool next up is uh NL brute so NL brute is a multi-threaded brute forcing tool dedicated to RDP it's a lot better than what is open source however if you are in pentest I would never run this on my system I tried I tried reverse engineering it and it's like packed like crazy it probably has back doors or or some of them do uh I mean it it's a a reverse
engineering challenge in itself um but uh the it it is very efficient compared to to the open source offerings that uh I know about um the there are many variants of it so it is uh it it was copy protected it got cracked and so there are some cracked versions online that you can find we uh in we collected like I think 12 different samples and uh or around this like 10 10 area and we uploaded the ones that were not on virus totals two virus total and they were uh uh so three of them were previously unseen I would say samples because they were not on virus total and the um these ones like the lowest detection ratio
it's all like the the garbage false positive uh AI stuff like the ones that were the less detected were not detected by um crowd strike EET F secure Casper ski so so some of these tools are not are like under the radar you know the way they were repacked fortunately for us Defenders uh the Russian author was arrested he was selling attack tool chains and he was arrested and extradited this year so the tool will exist because it's efficient and and its function doesn't need change but it will not see a dates next up is the masang GOI we've seen it before so and I talked about it during the video so not much to add uh
there is an advanced mode variant that uh is described on hacking forums but it's behind uh pay wall so uh I don't know what it what it does that is more advanced it's probably like has a back door or whatever but so the advanced mode variant I I haven't studied it much more than that but it's uh you know basically exposing a lot of attacker Focus options in a GUI for for the Robert Grahams original masam this uh this tool here is interesting Silver Bullet is uh it's kind of a burp but but for black hat and what I I I like about it is that it's uh it they're try like like it's on GitHub
they're trying to be legit or to look like it's legit but but there's nothing legit about it so it comes with like pre-made configuration kits so you don't even need to do your own like uh web you know scraping or like like scripting language like okay I'm trying this and then if this is the response I'm going to do that and whatever so the the configuration kits are shared on telegram they're like PayPal brute force uh uh or not Brute Force but credential stuffing uh Spotify credential stuffing YouTube credential stuffing and um why when I say like uh clearly little uh legitimate uh use is they're they have a banner so open bullet and Silver Bullet it's like a fork of of one
another but so they have a banner saying like oh it's a scraping and automated pentesting but when you look at the guy like the tabs the top level concept are proxies not a proxy hundreds of proxies like it's meant to spider through hundreds of IP address in order to reach the victim in order to prevent being blocked when you do credential stuffing attempt word lists like these are not concept that you see in burp that are top level uh Concepts right word list so usernames and password that you want to try and then if uh the screenshot like at the bottom I this is the configs page at the bottom you see like proxies are
we going to use proxy yes no captures are we going to solve captures yes no and then there's even OCR and and CF for cloud flare so there is like is the config built to bypass Cloud flare is the config built to do OCR to uh uh solve captures um so it it is uh like really like a black hat stuff and then in their disclaimer what I like is that they they took they they took a lot of care not to reveal that it's a blackout tool and but in the disclaimer bam they forgot that they're trying to look legit it just says credential stuffing on sites you don't know own is illegal don't use this
right they basically like this is what it's for it's credential stuffing of websites and so we are again another classic case of we put the label for research purposes only and we're we're stopping everything it can stay on GitHub you know it's not deleted from GitHub because it's written for research purpose only thank you now next up is uh I'm going to cover uh or end the the tools section by two tools uh that are or maybe no I have another one I have three three more um but two of them is uh def Defender disa disabling disabling Defender uh which is which are interesting uh tools this one here leverages um so whim on Windows is
like the how it's the operating system is packaged if you want to do a POS or an ATM using Windows you go at this level of the the windows packaging uh like Auto on aend stuff and you remove the components that you don't need that you don't want and so this leverages that functionality to unhide the defender features remove them and then reapply the the the filter so that AV doesn't uh Panic um and but this requires a reboot for Defender to be disabled cuz it's like removed at the OS level and I have to be honest with you it it doesn't work on Windows 11 I tried it like latest image from Microsoft and
it didn't work but on Windows Server 2016 which is what our honeypots are it worked wonderfully uh and it has a zero detection ratio on virus total so completely undetected uh but I I uploaded it so hope hopefully this is going to be eventually the predicted or it's probably right now um but so uh I didn't expect in my uh previous open source stuff that I did I was trying to build a malware reverse engineering environments and I was trying to automate it and removing the fender was always the hard step because of temper protection and stuff and so I was surprised by how elegant this solution W was and the fact that since it relies on leg legitimate
operating system functionality it's going to be hard to prevent or to block next up is a def DEC control Defender control so this is a tool that is distributed legitly on a on a website and uh it it's just a gooey one click you can disable the fender uh it's packed and it's Shady like I wouldn't recommend people using it uh but the the the the software vendor offering it has a lot of other tools so it could be you know clean I guess but so it was very well documented by the dfri report so I I when I realized that I stopped there and I refer to their uh their blog instead um but it is an interesting tool
and this works on Windows 11 so it works everywhere still and we've saw this tool used by the luus uh ransomware group so we know that it is it's is seeing crime Weare related activity um the last uh tool we're going to talk about today is uh fishing uh tool graphical fishing tool kit has a lot of functionality around fishing including testing the SMTP end point so it does the email sending on its own but also like for uh like uh variable uh replacement and stuff uh templates uh so it's called gamine mailer and it again another tool that is clearly has like it's not for marketing purposes let me tell you like it's too weird to be used
for that and um the but but it could be spamming Not Just Fishing spear fishing it could be spamming probably comes from spam um it's interesting because it was not detected by crowd strike EET FSE secure Casper ski and Microsoft when we uh we um uh uploaded it and um the the you know the the fact that it's not detected by by like these big Brands AV I think is a hint that it could it should be like as part of an early alarm system like if you have stuff like that that has very little legitimate use then you know that something's uh that something's off there's a lot more tooling that we saw but a lot are
variations of stuff that we uh we covered today um uh so we we might dive into to some of the other things uh later but but but at the same time again you know Keyport scan is clearly just a variant of mascan GUI and so uh so yeah so a lot of stuff to further study now if we want to do some classification so uh the tools like most of them is uh scanning and attack uh there's some monetization some some enable uh enablement uh communication here is like 100% telegram they would install telegram on their their machine um so now I promised you some interesting sessions let's go over them here we have a case of someone
downloading an El brute okay but he copy and paste on his clipboard a message and we're like okay what's the message so he says in Arabic why did you delete all applications so and with a broken heart so for us this leads us to um thank you um to the fact that they work in team right they they they this is an example of Puck passing right there I'm Canadian so all my analogies are true hockey uh but so we we we were like oh okay wow they work in team and they have feelings too you know so another one interesting so this is a Google ads he's trying like to uh use uh compromise the uh credit card
information to uh register an account but then he gets an error message and he doesn't know what to do and so he goes on Google translate on his phone in the the environment and translate the eror message to Arabic so now we know that you cannot beat this level of attribution like even if you use a proxy I mean you're clearly from Arabic region uh so so for us this was interesting and and it happens more than once and so more so that out of uh uh 45 sessions uh we we found these languages so not all sessions revealed the language because most people are uh speak or read English but so some that did these were the the
languages and I say languages but we realize it's not a it's not language it's alphabet because it's uh you know the Arabic has many different languages and uh seric you know we saw seric but we cannot say for sure it's Russian there are many uh seric languages uh but so these is this is the distribution of the alphabets that we found in the sessions now another thing we we we found is like it's great for intelligence collection so this is something we share because we're not an intelligence company but we would like people to use it for for intelligence purposes to scare to give give a good scare to the adversaries and so the person is here is um putting in a you
know country code phone number signing into telegram we're going to collect the credentials of the the person but then what's interesting is what's revealed after is like all the chat rooms that he is uh participating into the private chats are there and we see them interact they use they use telegram a lot to download and upload stuff like the the porn I was meant talking about earlier he would upload porn to himself via t so that he can retrieve it on another system later so he did lug into the the telegram system so we we think that someone who really has the means that the analyst cap capacity to to go after the the these types of threat actors uh
would really find a lot of intelligence in these systems now it's time uh for the loot the endgame the experience points uh we you survived I have like we're trying to make this presentation actionable like I know that the videos are fun and they they really relate but uh we want people to really like have ideas of of stuff to do so this section is uh is comprehensive um so I wanted to share the the the the the hyet environment that we built I and there's an emphasis here on you you need to be able to destroy everything fast because uh can go south uh so you uh you when they when they are after Sony you know you
you need to make sure it stops quickly um so so the the way to do that without losing evidence is by using a message CU so this is the Rabid mq part here so the lugs are streamed to rabid mq this way I can destroy the the the the kits so the windows and the pp machines together very quickly um the replay files which are binary at first I was using the message queue but then I gave up and we're using object storage instead and so for object storage synchronization we're using AR clone for uh and then for investigation we're using elastic uh querying elastic via Jupiter python stuff like like all of this is is open
source except uh Excel it's not open source uh but Excel has its limit right after a million rows when you're doing graphs it blows up so you need other stuff um and this is uh the the two like decoupled from the operating system we use Docker compose uh and this is orchestrated via terraform and put into git laab cicd this way on my phone I can like log in and run a pipeline uh to destroy some some of the the honeypots if they get compromised so this sounds great I guess the the the takeaway is that it always on fire there's always a problem everything is like broken except if you see Rabbid mq no fire on Rabbid
mq this thing has been running for a thousand days without a reboot okay and never crashed like the first mistake I made is I uh the the cues were persisting to dis without a limit of file size made that mistake and once I fixed that a thousand days of up time without a crash without a reboot and it's obviously you know unpatched right now but I'm I'm I was doing this yesterday like patching it but so it's interesting because it's super reliable the rest of it no um so the the party what I want you to remember is the Rangers are the largest group and they identify systems and open the path to others and we are
clearly going to we're the ones we're after right now we want to increase the um The credibility of our Honeypot you know join it to a domain have other systems behind had a bunch of files and these are the the ones that we expect are going to change the behavior the most or they're just going to do the same but the adversary that comes after is going to have a different behavior um the bars of questionable technical skills and appetite uh the thieves uh which for me represent what cyber crime is about it's opportunity and it's like you were the one unfortunately you were not targeted and they just run whatever they uh they can run now to make money uh the Wizards
which are mysterious and and scary and like I like to tell that they're like living off the land you know like red teamers would do they like use system binaries they don't drop anything else so they're hard to detect and The Barbarians aggressive brute forcing you know they they exist cuz clearly like we were deployed in a Amazon AWS and I believe that a lot of Barbarian activity is because of that because organization probably whitelist Amazon's IP ranges because they have a lot of of you know it's too intricate to allow specific code path it's too complicated the firewall management so they Whit list the whole thing and so this is why when The Barbarians gets in uh they will
rescan something they could have scanned from elsewhere but they will re scan it from an Amazon IP this is our Theory anyway um so the specific takeaways for researchers RDP is right for attacker study everything is open source uh why not right why don't you have your own findings and and do that stuff for Blue teers uh consume the ioc and roll your own out your own traps you could do it internally you could do it exposed on the internet and and gather your your own intelligence and also mess up with the adversaries like one of our goals is I'm I'm I'm trying to do it safely but I want to do it on on IP Rangers I'm from
um um the French speaking part of Canada and we have Partners there and we want to deploy like uh like um some banks or some hydro electricity stuff and we want to see like how are they attacked differently than uh than than uh Cloud stuff right um and for long en forcement uh we we already collaborated with law enforcement for RDP interception but we I want more of them to know that it's possible and see it because the the intelligence that you collect from activity like that is a of of a higher value like for Imagine like fishing or spear fishing or spamming okay instead of knowing oh this machine talks to uh Microsoft and Gmail instead of
having this super like encrypted and and far uh visibility now you see like when they build the fishing campaigns you know the the target you know the victims and I know that for law enforcement having victims in your dur this dition is key right so with this type of uh interception and it was approved in the Netherlands uh to uh a judge accepted the fact that there was RDP interception in place so it can't it's possible