My Quest for Identity in a Vendor Turmoil
Show original YouTube description
Show transcript [en]
so I'll start a little bit about myself so get to know each other my name is near it's an Israeli name I'm originally from Israel I started my career actually the Israeli intelligence corpse and was part of the Army during Iraq war and I was part of the Cyber Intelligence threat intelligence guys there I worked a couple fields in Israel before I moved here to New York 2002 I've just a little bit after 9/11 which was kind of scary I was working as a security analyst for youth vendors in the user behavior analytics space and in threat intelligence which was relevant to my career and currently I'm working an inside threat that the company named
preempt and I decided to do this stop because you know I've worked for so many vendors that even me started to get confused with all those windows are wrong and each one is kind of giving you a different idea of how they can help you and try to put myself in our side and see what what we can really get out of it so I'll start with a couple of stories just two stories two stat stories to be honest with you this guy Victor Olivia this guy was eventually assassinated by a criminal in in Canada Toronto Canada back in 2015 he used to work in the Canadian Toronto Canadian Police Department and he just went out
of a restaurant and and got chucked which is crazy and so investigation started and the investigation was actually leading to that women erin moran she was a contractor that worked in the toronto police department and the reason they carry Oliver is that they figured out she was running queries in the database about this guy just two weeks before he was murdered so she was working for the Toronto Police Department and she was running searches and those searches eventually led up to his murder but why why would you do that well looks like she had other searches for other people and any person that end up being part of her search was either dead or injured a couple of weeks and
you won't believe what was the reason the guy that murdered this police guy got a traffic ticket and she helped identify who was the police officer that gave him the ticket and that's what that's what they get back so that's kind of a crazy story about internal threat it took 60 months to actually find out this that kind of talks about the time that internal threat just like external threat can reside without being detected and obviously the threat is there anyone knows this guy Alex either live no no Co is a Russian used to work in the KGB and the story of this guy is eventually he accused the KGB of fabricating a story about that in order to support Putin and
it was very vocal about it he wrote some articles and eventually he was immigrating to the UK where he continuously criticized his government one day his former co-workers met him in a restaurant they gave him something to drink and a couple of days after that we started to feel very bad and eventually it was uncovered that he got poisoned by Russia and we know as a threat intelligence engineer we know that Russia was involved and still devoting a lot of cyber activities within the US including involvement in our LED latest election including involvement in Ukraine black energy I don't know if anyone heard about that and so he has a goal you know totally different
individual much much much more power but similarly he has motivation he wants to stay in power and he is a threat externally and what I'm trying to say here with those two stories is there is some commonality when you look at threat when you look at threat eventually it ends up linked to an individual whether this is a hacker and inside employee or a leader there's some kind of a motivation or intent the some kind of capabilities could be a malware it could be their ability to access into a database and there's some kind of an opportunity and although there's a big differences between them they are all threat and some things that we can do
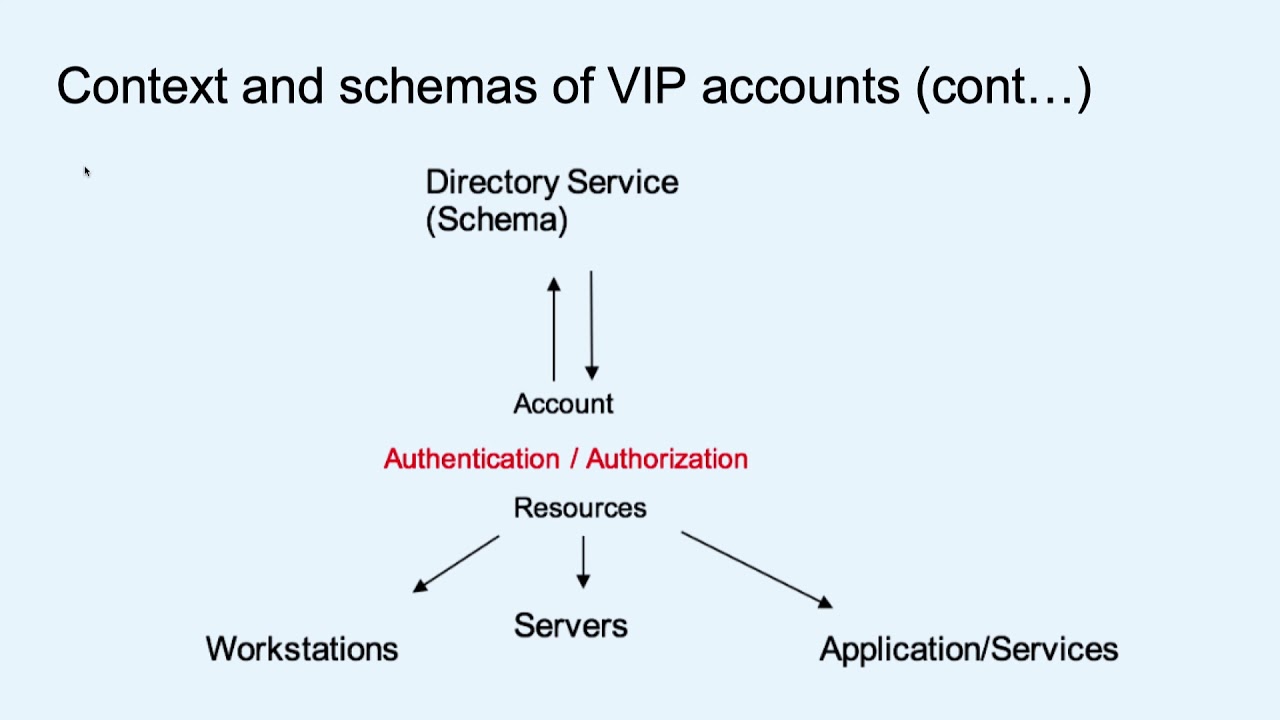
that relates to all of those together so today I'm going to focus around how we can identify those individuals whether those are big groups that are attacking us from nation states or there are individuals that sitting within our organization and in order to that to do that we'll focus in identity we look at the things that can help us track those indicators along the way and indicators that relates to eventually specific individual so this indicators of compromised that relates to endpoints just IP addresses URLs domain files all kind of things but today I'm going to speak more around the indicators that associated with a specific individual and so from an attack perspective going to talk about
the password the privilege escalations and lateral movements all of them really depends eventually on getting in access into specific individual may be impersonating individual may be by accident doing some activities within the organ is and then we look at some of the event or turmoil on all the solutions that people are telling us that can help us and we'll question whether they're really really helpful or not and if they are what's their weaknesses is there any better way we can go around it that make sense sounds good so even I and I am biased and I'm not perfect and I mean so everything said here take it with a grain of salt love to hear your opinion
and this is my Twitter handle so I'm sure everyone is kind of guilty with the way they treat passwords anyone here is using these parts the same password in more than one application I'm raising my hand because even anyone is using their dog name or their college or their date of birth or anything like that within their passwords I'm not but you got a relatively good good quality of audience this is what the real users landscape it's this is where the real problem is password is easy to be forgotten is really easy to be shared and a lot of people don't treat it as it's supposed to be treated so let me show you here
just I don't know if you guys so so that [Music]
in the
[Music]
[Music]
[Music]
[Music]
so yeah yeah [Music] but you don't have to be that stupid in order to lose your password yes yeah just just Google what is your password
yeah but but but even if you're not giving up your your password still easy ways to get a hold of it this just couple of the things that we see out there for example any breach the Olympic in breach has a list of hashes that eventually again distributed to all major security teams and then if you are a hacker you probably also get a hold of it and you can use it against teams so you can basically social engineer understand where the users within LinkedIn is and then use their password within the network and most likely there's another place that they use the same password other things are dictionary attack people tend to write passwords that make
sense so they can remember them and so that's reduced dramatically the specific possible options of you to test a random brute-force again the password you're just using dictionary words other things is is other things that are really involving more tools so if someone is getting involved within Windows Windows has a vulnerability that allows to dump the hash of the password out of memory now that's not the actual that's what it's just a hash of it but still you can crack this hash and figure out so that's a problem and we all we all guilty and we all aware of that problem so there are actually a couple of voices coming out lately that relates to well what do
we have to use passwords let's try to do some in town so the first one is biometrics right we all know the iPhone now that allows to authenticate using your face recognition or your fingerprint it's not perfect and in some cases it's still a vulnerability because somewhere inside the software there is a database that identified so if I steal the database I can still impersonate myself within another operating system other things are just identifying the way you type how fast the type of how slow your targets the keystroke timing the colleague it involves them a i and it's not it yet in a level where it can identify want one individuals so that's another year anyone heard about Windows
hello so so windows realize that that the pass was probably a problem for them I mean Microsoft's or realized that and so they're trying to start with also a password last approach where you can either use some kind of a token some kind of a device either instead or in addition to the password you have there's all kind of idea behind it but none of them is really a fully replacement yet - so if I'm looking at red team's perspective or hackers there's this a nice list of already existing password cracking tools out there our company is using some of those anyone familiar with the rainbow tables so yeah it's just a way to crack it much
easier a lot of the password cracks tracking tools are specializing in specific type of passwords right passwords relating to web answers passwords automated through databases passwords that related to windows passwords that related to minutes each one of them has either a library or a set of tools that helps you crack it so and obviously there's fishing right this is fishing so there's always that the human element where he's just getting an email you link you click on the link and you're voluntarily put your passwords there because you believe this is legitimate but then when you forget the password the next attack vector the next natural attack vector is the privileged user or escalation of privileges because
most of the users especially those users that we saw in the video they're not necessarily having the admin rights so we might watch the battle there and we will get the users potential so we own the user space within the host but what do we do when we want to get into the network to the main what do we do want to do get a hold of the critical assets the finance server or the IP or the executed we need to escalate privileges and statistics telling us this is from 2016 we didn't change much that they next to the password harvesting or password cracking attack vector is the privilege escalation vector and so so a
short video that also amuses me a little bit for me you'll like it [Music] okay so this is a simple example of after a privilege escalation that allows someone to copy files into someone else's desktop and so this is a group of students within a farm a computer farm and this guy is having a list of files copy twist DC now we will remove the machine you removed all the files and see what the other guys doing
[Music]
[Music]
like I swear to God I deleted those file how come they appear all of this data and yet the users just copied all the files back and forth to today Annika because he he was stealing his hat she stole his credentials
[Music]
now at the end of the video they actually the teacher
[Music]
[Music] was the lesson learned there what it was you know just an exercise but the point is this is much much stronger things you can do and remote machines so how do you escalate privilege well we have credentials a lot of times there are older other credentials stored within the machine so it could be well this the simplest and stupid thing would be to have a credentials file and click clear text but even if it's not in clear text this way to prove to dump credentials for memory there's basically way to inject the allel so when Windows you have the user space but you also have the kernel space and the kernel space or what you
guys if you ever got into task management it's called system right a service that called system if you can inject a code within that user space into a process that is under system you just change your privileges you just get a higher control on the computer now you're not the user you are the system and the system because the system needs to communicate back and forth to Active Directory and to other services you yourself also have the same capabilities that makes sense so injection of DLL something you can do now if there is a specific sharing directory let's say your user someone shared directory to you you potentially can move the path just like you saw in the movie here
those kids were basically copying and pasting a files from their hosts into a desktop of their neighbor in reality you can drop a shell into a remote system and start working remotely on that system if you have any sure network a lot of times there's not enough surface permissions around the users so even though you are a local user you still have permissions that allows you to access other services and when I say services I mean other servers right but you can access for example the exchange server but can you access within the exchange server all your email or can you see some other activities right depending on the rights that you know you've been given you might be able to
do that and then there's token manipulation anyone heard of Kerberos okay so this just talk about Clippers and later on but remember that Kerberos is another vulnerability that can be leveraged there's couple of really strong to mini cuts everyone knows me me cut me because is much more than a criminal privilege escalation too late it's basically a [Music] swiss knife of multiple capability allows you to start with password harvesting through privilege escalation and lateral movement there is a great tool if you are in a Windows environment and you want to explore it look up power up power up is a great tool that allows you to escalate from a local user to a local at me now local admin means that
you have full control on that specific cost you're not necessarily can start moving laterally to the network but it's a great starting point because local administer later on can easily help you to move a domain admin in this is a lot of other tools there but again I'm out of those I really recommend you to look up power up and mimic us
so this is the way it works in order to us starting moving with Internet work we need to start the installation if you are a local domain administrator you have control of that specific cost if you are a domain administrator you have control of the entire enterprise basically on the network okay so that's that's the the kingdom at the keys to the kingdom that's what you need to get now in order to get that you can basically look at a local administrator on all the environments and then start to see if there's other machine that either using the same password or allow you to access a higher level of user within the domain so the whole idea is getting your local
user to become a higher level of inside your local host and then from there moving from high level within your host into other machines so any host within your network within the Active Directory environment for example communicates with a domain controller right domain controller is the server that has all the sleep that's the trusted entity within your environment that eventually can help you communicate with your printers with your finance with your HR apps which would help okay if there's a way for me to communicate with the domain controller the first thing I want to do as a hacker is to query for the environment because I don't know I just know that I mean that specific host I can start enumerate
the users in the environment I can start enumerate the hosts I can start Nurik the services so this is an example of a query that every host can stand into Active Directory which is basically sits within the domain controller and asking simple question show me all the services within the network show me where they are and what's their status and you can see you might not be able to see apologize if you Tom that this is a SQL agent server that I can get as a response you can use also that specific blog ad security that org to to get more details specifically how this is done but at this point I start to map the
network I start to get an understanding of who are the potential targets within the network where are the services that I'm interested in and how can I get it and so from now it's just moving laterally moving within the network anyone is familiar with the kill chain okay so real quick the kitchen actually came up from the Army it used to be a way to describe how an attack by the enemy is going right starts with reconnaissance you get the the enemy looking over your witnesses after the consciousness there is a basically a delivery which is sending the information to you it could be a malware the delivery could be a spear phishing email it could be a spoof
domain then after the delivery there's execution of the the actual attack and then you need to start moving laterally and what happened is as I showed you earlier the escalation process is basically repeating itself so you get a foothold of one most you move laterally to another one you might not have the right permissions to eventually go to your final target target okay but within that you escalate the permissions and then you move to another one it's like hoping until you get into your destination and so those techniques or tactics that I'm talking about can be repeating themselves over and over and over and statistics shows that 90% of the intrusion analysis reports including them 90% of the time you hear someone on
use that having a bridge it's because someone was successfully stealing credentials escalated the privileges and started to move within their environment that's the common denominator that's what hackers are doing they're changing them hours they might check the tactics of the way they they weaponized and deliver their their hours that once it's there that's really a repeatable process and a principle problem and so what I up lateral movement that's what I got by the way I'm from Israel I was like okay I learned something that's also a lateral movement I guess right so the lateral movements techniques could be relating to what you got right where you are so depending on protocols you might be able to
i chat an interest rate session which is basically command-line interface to another lino sometimes with those machines you can use windows type of services such as remote services or distributed comm you can create a golden ticket which is basically a ticket that allows you to access anything within the network anytime that's that's basically the end end game right that's that's why you would be able to to own anything so since not everyone's familiar with with givers and ends and this is really a in a Windows environment the authentication method let me just go over real quick the wait works okay so this is your home towards a client joined the network client means they they host right your PC joining the
network and now the PC wants to guest access to a printer for example well the first thing you need to do is you need to identify the stuff and so the first step is client log on the client log on what you do is you don't expose your password but you said your password hashing with a specific ticket that specific ticket is called TGT digiti is standing for ticket granting ticket and that is basically your pass that allows the Active Directory portion called authentication server to say okay this is John this is Sarah now I know whenever John is telling me this ticket that ticket is almost like their ID right this is this is representing that
speak up so far so good it doesn't allow you to do anything yet right it just allows you to say I am who I claim I make sense all right now let's say I want to go to the printer what I do is I take my ticket okay and I send it together with a request to the ticket granting server and I say I want to go to the printer the ticket granting server looks at my ticket and see okay near is allowed to go to that server to that printer I'm going to create another ticket that's going to be a service ticket and it's going to be very specific it was going to work to work
only on the printer and it's good to help also by the way have an expiration time of 10 hours so next time in 10 hours or if you restart your machine you will have to ask it again and so now it goes back to you today a client and it goes also today Twitter and say listen if Muir is coming to you and it shows you to stick it he's fine you can trust you so that's what happens and every time you need to get a new server or a new service you need to go through this process and this is where this is your trusted nd that makes sense so what you can see here is what hackers can do in
order to determine if specific so the attacker basically got a foothold in the system and now there's an infected system but you still don't have those tickets that I mentioned earlier right and so in order to do that you need to dump this specific password so remember the ticket granting ticket the first picot it kept in a memory so if I get all of it I can basically try to ask for access to other things that the user itself didn't ask basically I'm impersonating that makes sense so I get a lot of this ticket and from now on I can try to ask services now there is a way to have kind of include all services which means that
from now on my server will be able to access any resources within the network and that's why it's worth it so getting back getting back into the red stuff one of the things we didn't take into account when I told you to think about is that people make mistakes so that's why I'm saying well you might not necessarily have a bad intent you might just be stupid sorry just made a mistake that's kind of break a little bit this this model of threat right so when we're looking at insect rate an external threat we need to take this intercom people makes mistakes they can make mistakes because they're rushing because they frayed they can make
mistakes for a lot of reasons but we have to take this into account we need to save people from themselves the other thing about people is that they don't like to change there's a lot of things within the stuff that we're doing on a daily basis that we do just because of a habit and so people are kind of predictable they're making mistakes but with their real intention they're predictable if I have a bad actor I'll probably be another bad tomorrow as well right if I might have met my good responsible employee I probably be a good responsible employee tomorrow as well basically I'm starting my day I'm getting into my PC I'm logging into my PC then there's a server
that I need to access that my boss is asking me to do some kind of a report so I'm going into report and if you look at it for the long run it's pretty boring it's pretty repeatable and the idea is because it's repeatable what I want we try to track it and model it that's the idea people don't like to change and I kind of look at it it's almost like the weather they are going to be places and times where the people will have a different unique behavior but on the long run it's pretty pretty predictable you agree so the only question is now how are we going to model it very similar to what we do on the network
what we're looking at the network when we have a network traffic monitoring we're trying to see a pattern this is a very obvious pattern right you know we have big times we have you know load time of activity and this is something we can predict with endpoints but we can also predict it when we look at it identities but for that we need to get some data so how do we capture the identity we need to take all the activities that we're doing whether it's from our Mobile's whether it's on the cloud whether it's on our desktop and try to somehow unify it so from a monitoring perspective it looks like it's basically the same person and so we
would be able to attribute it making you accountable of what you're doing whether your home office surfing your you know website whatever you do we want to eventually be able to link it to you to your individual I'll make you a condo so this is what the bend or terminal stops right everyone understand that this is going to be cool thing right the the new parameter is the identity right the spy walls are not relevant anymore or they're relevant but they're not going to stop those breaches we we lost our work on spearfishing the tax you know people will be stupid people will give up their password literally or through some kind of a phishing attack so what
can we do so there's a lot of fingers coming up with this idea of any faith and you want family with their faith pretty cool right you put your password then just to make sure this is will you claim you are you're gonna get a text or you're gonna get this type of verified or decline and only if you verify that you're going to get the answers that's pretty cool right because you have it within you this is part of physical evidence that you are who you claim your but there are a lot of pros related to image faith however this some kind of disadvantages as well now one of the things that people are
pushing back of course is when when you get into your work environment within your environment you know logging into your desktop for example you know the extreme example I don't want to get a text file every time I'm logging in into my PC that makes sense right the other things is that what if the service is really essential for your operation and there's no one there that can approve it you can basically harm some of your business operations basically let's say the users specific user has a probability cell phone they're trying to access this server all of the sudden this is preventing some type of activity so you know from a business perspective you can lose money
or you can potentially even lose uptime due to that so you need to be careful of how you use it but that's not better then there are those vendors that telling you listen we will be able to give you a risk score what is that let's go big number it's going to be a number let's say between 0 and 10 1 0 and 100 that associated to a specific user so John is the risk score of 90 Sarah is 40 don't worry about Sarah watch John how because there is a I write the magic of machine learning we'll look at it with the start what it does now it's an exchange in some way it does
make sense right because if you track all those activities on the network you can start to identify things that historically are risky and then give you know highest risk for to those individuals however this again this prose and code there's a lot of of this which is a snake or a lot of people telling you yeah we we can run in some kind of a magic algorithm in the background which will tell you exactly what's the right risk or what is this algorithm how do you get to that person or how do you really cannot touch a number two to individual based on what right other things are well okay so you recognize that this is a risky user but did you
really prevent the hack or is it a kind of post mortem that type of a thing right did you already pass the logs you had to go into the steam you have to see everything what happened you kind of depending on all the logs that coming in from all the firewalls and and an active directory's in order to figure out what this user really did and by the time you figure out what the user did the user already got exfiltrated all the information out so again not a perfect solution and then this new magics called SSO single sign-on how about just having one username and password I don't need to worry to put it on the internet again I just put it once
and then I have access to the world well what if someone got an access to your username and password then he has access to the world it is making things simple and saml which is a secure drifted way to kind of allow the SSO to work is it good it is a good idea when it comes with it comes to controlling the amount of time you're using your password outside of the enterprise and it does make the users experience much better but it still has this problem where if someone get all of it it gets the key to the kingdom and it's not necessarily always secure so there's all kind of protocols that enabling SSO pad but it
are very easy to crack so in practicality you basically help helping the hackers to get a hold of you passwords even make sense I might just keep that one it well you know what I'll show you
[Music]
[Music]
shopping sprees with your credit card waste measures is trying to stop this
there
[Music]
[Music]
all right so what did we see here well it's a couple of things first of all we saw a gas pump that has a key that matches all the other gas pumps can you believe that when I saw that I was like you crazy that's sharing passwords isn't it that's crazy you making their life much easier but the other thing we saw is that if we're smart enough we can monitor the activity and we can identify who are the guys and what they're doing and how do they be 8 so let's take this story from the gas station scan into the cyber world and we're talking about risk this is obviously going to increase the
risk if we see those type of activities but if you're looking at the cyber world what are the indicators that relevant to cyber as opposed to this you know the gas tap well we're going to look at people who's having the keys for those important assets who has the keys to defiance who has the key to the HR server who are Dean has the executives access who is having the high privilege who is having access to the applications that are really really going to damage the usability or to benefit the adversaries and then what we do is we're looking at the impact ok is that stealing credit card in going to basically bankrupt you yes is it going
to allow you to just get the spam and get rid of it ok that's how you start giving the risk or based on what is the probability and what is the actual impact and then basically you're trying to adjust your response whether it's just alerting but they're just alert the user in television you did something wrong you shouldn't access this server you should copy files this is not the file server you're just wasting our resources or you're going to link up you just was running a query within our database that relates to police guy that was killed a week ago okay you're going to be having to reset your password why because because we don't believe you is you you're going to
be basically blocked or even though you're running within your environment you will have to have an MFA because you never accessing this server this is the first time you're accessing it for the past two years that makes sense so we can put those cameras the disturbance camera that you saw on the path this is it let's put it on our network it's basically going to look at all the activities that I showed you earlier the Kerberos activities the ntlm the LDAP queries the query for those services that I spoke about earlier let's put this and start looking at it over time and if something is come out of the norm either alert or even prevent it by
blocking because while you are in line I can just walk this ticket remember the ticket I showed I talked to you about the ticket that the Kerberos ticket requests if you put something in line you literally can hold the request okay and say all right John please identify yourself John didn't identify himself I'm dropping two ticket and whoever pretends to be John will never access the server so me in the middle me being able to not only steal or do civilians objectively but literally block it is probably part of the solutions to this huge problem of identity how do you do that well each and every tactics that I spoke to you about earlier has some kind of a fingerprint
on the network and if we're smart enough and we reverse engineers those tools the hacker tools we can identify how it looks like this is how a something that's called camera speed and you can look it up I'm not going to go over it now it's one one tactic that that's the way it looks when you are watching the network when you monitoring the traffic so if I know how it looks like I can detect this and I can detect it I can also block now a lot of people are saying well Mimi cache is dead because now Windows 10 and 2006 are coming in with this credential gardening and they have the the ability to put the service
Wow why don't you spike noise so that's not true Windows 10 has some hidden a password allocated into the those specific Kerberos credentials it's make it harder for the hackers but you can still sneak close to themselves when they're coming out of the house into the authentication servers there's a lot of other ways to look at it I recommend to look at the latest versions of mimic ads and how it overcomes the credentials card within windows getting close to our conclusions what should we do we should reduce the attack surface how do we do that we're starting to have those balances check and balances across your environment every time you're trying to move to the
next step within the kill chain if someone is trying to elevate their privileges they need to be double check someone's trying to move to one computer from another popular he needs to be double check all of those suspicious steps are not going to be happening before some kind of an audit detection and potentially prevention Microsoft is starting to move that direction as well Microsoft is doing a hell good a lot of things nowadays to be honest with you I think the whole idea behind hello always it's great and I know how fast this is going to evolve but the idea of Azure being secure moving into a secure area within the cloud again keeping a same identity whether you are
asking your local Active Directory or your actual Active Directory helps to identify who is behind it is an eventually either identified malicious activity or just an innocent user that doing something that shouldn't be done so let them learn they think from a password perspective with we killed that worse or repeated it to death right definitely need to be careful with your passwords and make it complicated don't use it on multiple place at the same password and honestly if you can use password less it's probably the best option from privilege escalation if you are an IT administrator you don't want to have local administrations in most cases local administrator account should be disabled there's no really reason for
local administrator to work for user without your network you can do your work without this privilege enabled at all try to demote the information over time if you monitoring the user's activity you can be see what we call stealth admins at means that we're never using their username and password probably needs to be demoted right this also add means that are not admins there may be just users but they have the right to reset the password of an admin so in practicality there are ministers right so look all those loopholes over time and just by looking at activities you can decide whether it's something you can reduce go into minimum privilege policy and yet the thread things right
don't forget about race so summarizing I don't think there's a stupid bullet I think each one of those mentors kind of give us a little bit of a different way to look at the problem and just end up with one of the course that if anyone knows where is it coming from dude right all right thanks for your time