A VIEW FROM THE FRONT LINES
Show original YouTube description
Show transcript [en]
[Music]
you [Music]
you thanks all for having me good morning everyone my name is Adi our roster this is the still too loud I think right any feedback to the game one two three let's try this
I talk food this is better right okay well thanks all for having me this is my first time at besides I do have to speak a bit low because it just goes crazy I was asking Charles and bran about you know everything about besides the profile of the participants and typical topics that are presented in the conference one thing I forgot to ask was the dress code so I normally don't like ties I don't wear ties I try to avoid them as much as I can so please don't judge me so I just make any quick introduction I'm the director of my den consulting services based in Toronto a vivid Organization for about two years
and a half and I basically respond to breaches helping organizations to be more proactive in becoming more resilient against cyber attacks but also when they're compromised the Collison and performing system responds and try to remove the attackers from the network and then a bit of a quick background mandiant at mandiant we respond to cyber security breaches and you know if there was one thing that we learned over the past decade of responding to most sophisticated and complex security breaches is that there is no such thing as perfect security we are going to continue to see organizations getting breached the reality of the cyber today is is that you know there is no fear of repercussion and processes technologies
people are going to continue to fail to stop the attackers from getting in and unfortunately these realities are going to continue for a number of reasons you know the most important thing is that the exposure is going to continue to grow our networks are going to expand in terms of you know that geology footprint you know the use of cloud in terms of things interconnected business processes channel strategies all of these are going to result in networks that are basically wider bigger exposure and harder to protect we no longer can be only worried about the stuff that are in our network we need to worry about the assets people the personal laptops BYOD and so forth at
the same time attackers are you know not necessarily exploiting systems you know there's a lot of focus on securing systems and networks but almost in every breach that we have responded to we find that that attackers are targeting the users right then you're basically targeting the user pressed and and there is no patch for human so we're going to see them continue to try to to be able to bypass these you know that the controls have implemented our borders other parameters to gain access to our systems leveraging the human factor and then from there on exploiting a feature that is available in a software for an intended unintended purpose thirdly the the attackers are going to evolve in
their capabilities there is a significant opportunity for them both from the intelligence perspective from the financial perspective from the community recognition perspective and as we have been saying over the past decade or so and I'll talk a bit more about the details of some of the improvements and evolve most if they have seen in the wild these innovations are going to continue they are going to evolve enhance their techniques and capabilities and we we are security professionals we are not going to be able to introduce safeguards as this at the same speed that they would be innovating so so the reality is that the cyber risk is an evolving in nature and we need to make sure that the business
understands that you know when making a certain investment is not going to pull it proved you for for your life right there there needs to be continuous monitoring of the cyber risk introducing additional controls and capabilities to minimize that risk and lastly there is a there is no fear of repercussion you know for an attacker that is sitting in China Russia or Eastern Europe there is not much preventive or or you know scaring factors to to target organizations in North America and Asia and so forth and so essentially if you think of you know odds as goalies we are essentially taking the penalty shots one at a time right and it just makes us makes our job
very difficult to to protect our networks we should we should realize that you know our job of the security professionals is not to stop every attack the reality is that if the attacker has the capabilities and resources to target an organization has sufficient sophistication they would be able to bypass our controls our job is to attempt to detect these attackers as early as we can we can while trying to minimize the impact of that on our on our company and our critical assets now with that premier I just I just wanted to quickly walk you through the table of content that I have here we're going to go over some some of the stats that we
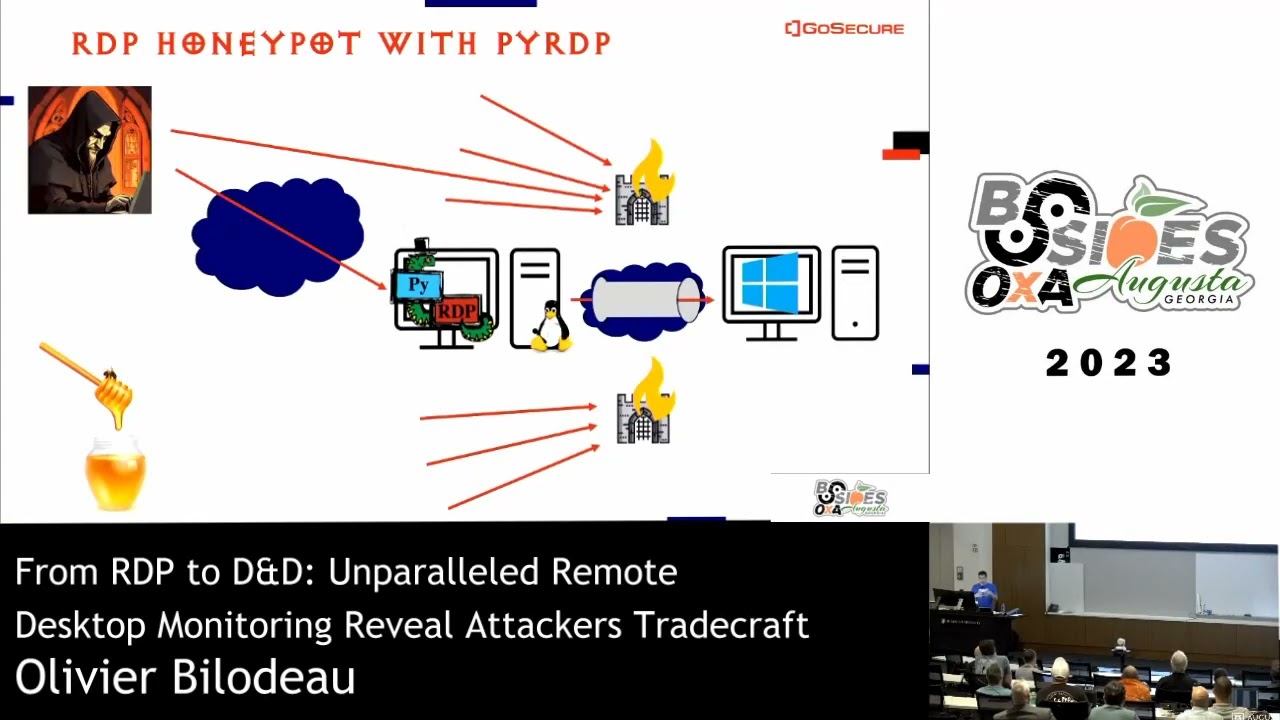
typically publish in our end-to-end report as for those not familiar M trend is essentially a report that we publish as the manual organization every year where we document the findings from our instant response engagements that we've done last year and also a number of other red teaming engagements where we actually act as at the attackers and target environments by the way this report was actually just published this morning so this thought that I'm going to present it's very much of out of the press by all means definitely go ahead and recommend downloading it not one of the key stats that we report on this on this report is basically that in industries and distribution of the
incidents that we respond to now it's very important to understand that this information by nature is flawed because it's based on the incidence that we have responded to and we only respond to most major breaches and incident situations that the clients were able to discover quickly remediate or not impactful opportunistic type of attacks wouldn't be covered here but if you look at the distribution of the incidence if we respond to over the variety of indices then one important fact that you should realize quickly is that all industries are being targeted and there's not you know only few industries that would be the major targets for the cyber attacks essentially every industry depending on the type of data they have the cyber
operations they have and the motivation of the actors that are targeting that industry are going to be targeted and are going to be impacted in terms of some of the observations from last year we see that there is increase in targeting and compromise of financial services retail and hospitality government and healthcare and I'll talk to it a little bit further ease involvement is based on you know some some of evolutions and developments in the cyber criminal market that we saw that here and also made a number of the nation states that have actually not developed cyber capabilities and are using the last part of their stated sponsorship processes now one of the key stats that we report afford to do in our
alternate report is the dwell time so from our perspective to all time is referred to the time from when the attacker gains access to the network so think of it as the initial compromised a spear phishing or exploitation of an external facing vulnerability until they are detected by a by the organization or an external party learns about that informs the organization right and we think this this stat or measure is very important because it essentially determines how much attacker has time in order to accomplish their means right and if you look at last year this number was was 99 days so from the time that they had had to establish the initial access until they were detected one way
or another it was 99 days now the good news is that this number has been dropping over years and last year last year is dropped by almost forty seven days which indicates that companies are are becoming better at detecting these these attacks the other the other aspect is that you will see about more than half of these incidents are being detected by law enforcement versus the actual company which is a concerning because by the time that law enforcement is inform you that is informing you at the other problem it's probably too late attackers that's already breached into your critical infrastructure is stolen data and that's what the law enforcement has probably observed and it's sharing
that with you and the other the other aspect is you know that the old time when an organization would actually detect these activities internally versus when they are informed by law enforcement on average I think it was about eighty eighty eight days for an internal detection versus hundred and seven days for for external detection again that is not very significant last year actually observe that you know when the external notifications are the result of the detection the duration or the dwell time was a lot longer it was around 300 and something days which points to the fact that law enforcement is becoming better at detecting these attacks and as I said this that you all
time has been just dropping over the years which is a really good sign it just means that we are just generally getting better at detecting attacks no detecting attacks it is you know is important but it's also important to understand that which is staging there in the process we have detected the attackers right if the attackers were detected in the earliest stages of the compromised when they established the system or laterally move to a couple of systems the car the impacts of the incident is relatively contained but of the once the attacker has actually compromised your Active Directory has gained access to your critical system it's pretty much too late to to kind of detect and there probably came in
grab your data as left organization and know your you have to deal with the resulting impacts of those now 99 days again is definitely a shorter number of days as compared to last year but what number is is good enough right I mean the drop is significant obviously and it's important it's definitely indicated of better detective capabilities but if you change about this once the attacker gain access to the environment he has 99 days more than three months to stay in the environment and move laterally performing general reconnaissance to accomplish their goal what does that mean I think from our perspective that means essentially it attacker is able to gain access to whatever data thereafter
within 99 days so just give you some ideas when we perform red teaming it typically takes us about three days from the start of the fishing campaign until we actually compromise the Active Directory so three days until we gain access to essential credentials that would enable us to compromise data no matter where they are in your network unless you have some other compensating controls such as segmentation or two-factor authentication and we can really assume that attackers have the same capability right so I think 99 days is really 96 days long too long now some of the attacker trends that the observer I'm going to speak to when I pick these trends some of them are based on what we
have reported in M trend report but also I include this view based on the cases that we observed in Canada obviously I'm try and talk to the trends at the global you know like Ross North America a million AP AP j but I also included a few few things that we observe in Canada which might be interesting to the audience given this conference is being held in Canada but if you think about 2016 you know I I I see - two major trends one was the cyber criminals and number of cyber crime cases and definitely there's an increased sophistication of cybercrime and the second one was Russian as stated sponsored activities I think the year of
2016 can be marked by these two factors the financial actors that are targeting organization to achieve certain goals with the eventual objective of monetizing their access whether this would be you know capturing critical information PCI PII initiating fraudulent transactions or even taking your data and asking for ransom and and the Russian is data sponsored and I'm again going to talk about this data sponsor trade landscape a bit further now talking about cyber criminals specifically you know prior 2013 we taught off to the cyber criminals as a smash-and-grab type of attackers you know they were attacks tended to be very opportunistic they would target organized a they would they would be targeting organizations that would be
vulnerable to their exploitation capabilities it wouldn't necessarily go going after that opposition that all certain data that they know how to monetize they would be leveraging technologies tools techniques procedures command and control infrastructure that very easy to identify and mitigate when we had consultants that were working on you know financial cases we would always wander this is probably going to a straightforward case because once we would identify the attacker techniques we wouldn't see a lot of variations from those in fact very often we had already ran into these attackers in the past and we knew exactly the tools that they were going to use so we could use that that knowledge to quickly scope the incident
identify all of the systems that they've accessed and from there on basically lock a couple of command and control infrastructure they were using remove their tools from the systems and we would be good we never saw attackers you know financial actors 5013 trying to get back in or maintaining long-term persistence typically the duration of components would have been very short until as soon as they got access to the data that they were after or initiate the fraudulent transaction they would just leave the environment starting 2013 erotism 14 we saw that there's a sophistication in some of these cyber criminal you know there is still opportunity cyber criminal activities but we could we could see that some of these cyber
criminals are maturing you're following a more organized approach they're using frameworks and codes that are repeatable but I also expandable they're using command and control infrastructure that are a bit harder to detect or at least they could take with modify those very quickly so as soon as you would detect some of their command and control servers they would switch to something else now in 2016 the line between the level of sophistication of certain financial attackers and the advances today sponsored kinda is not blurred anymore it basically vanished we we run into financial actors that are behind you know the Swift attacks or other type of financial attacks where they emotion is significant capabilities and sophistication they use malware that was
specifically designed for the targeted environment the malware that contained profiling capabilities to minimize the detection rate they use zero days which is kind of rare in a cyber criminal situation but it takes a lot of resources to be able to obtain and weaponize the zero day vulnerabilities they started practicing significant operational security when it comes to targeting the organization's historically they were very noisy they were not worried about being detected or hiding their tracks right we saw that there they are starting to leveraging leveraged anti forensic techniques to make it just more difficult to investigate them or understand the techniques that they're using for the future we saw attacks against you know innovatively attacks in these financial
infrastructure like Swift and other fun processing gear you know applications we saw an ATM malware that was very sophisticated with target ATMs that the upper part of the ATM that is relatively less secure and would basically be used in a campaign that requires a significant coordination with the monomials to be able to take that money and the response that from from the ATM machine so we see that is a you know the financial actors are continuing to evolve the capabilities not mind you stated sponsor attacks especially the Russian based the Chinese ways continue to set the bar for capabilities and resources when it comes to say you know cyber operations but but it's got more
and more we're saying that at that line between these capabilities of learning and and I think it's important to understand this because when you think about this data sponsored there are only a specific objectives that would make them interested in your profile right they typically they are driven either by political intelligence or a commercial espionage right and all those situations are easier to understand it's it's more predictable especially if you monitor the political language landscape you can you can try to figure out who would be targeting you for the process of political intelligence and many organizations are it may not be even relevant to them if you're mining and you know there is a political issue
between let's say Canada and Russia you're not necessarily going to be targeted right but if you think about financial actors from their perspective every company could be a target because a financial actor can monetize one way or another their access to an environment right and so that's it from our perspective is a game changer now we're talking about attackers that have the sophistication level of the status sponsors but have the motivation to target any organization right it's all about you know the level of effort that they have to put in and how much gain they are going to have out of that right less mature you are obviously there's less effort in targeting compromising your environment and more gains from the
attacker perspective
now this is a case of studying that we've heard about the Swift breaches in South Asia or the Bank of Bangladesh were targeted about ageing eight million of funds were transferred you know the potential impact could have been a lot higher but I think this case is was actually in Europe were we investigated similar idea the attacker was able to bypass controls gain access to the Swift environment not a couple of very interesting facts here one was that we observed attack irritating the environment and monitored the business processes and learned those so this was important again very not very typical of a nature of a you know the cyber criminals typically they're you know but
they sure to be as fast as possible focus on getting it data on ensuring transactions but not really learning the internal process of the organization with the observers of the attackers sit in the network for for a long time until they actually figure exactly the process for getting requesting approval getting approvals and so forth the attacker then gained administrative access to the to the core systems and modify accounts to bypass those business processes essentially they had a you know to our approval process they modified the account you will not require any approval but otherwise you know even if they accepted or approve the initial transaction that the owner of the approval account would be would would
learn about the transactions being successful they leverage malware that hide the track of the Swift transactions but there was also one other interesting aspect here and it's something to keep in mind when we responding to breaches off of this nature so typically banks have a grace period during which they would be able to recover a financial transaction if they realize that it was a mistake or it was fraudulent right or the attackers to bypass use this grace period they had to figure out a way to distract the the organization from finding out about this fraudulent transaction right so what they did was that they created a signal again disruption in the infrastructure they literally basically rewrote the
operating system and restarted the the server's essentially cause a number of servers to go down sinking distance that we had about forty five systems that were impact at twenty nine servers sixteen workstation so think about when you're responding to a breach like this right assuming that you actually learn about some sort of attacking activity in your environment by the time that you actually realize the scope of the bridge know you have to deal with the disruptive attack and you know the just that the level of effort and a strain that's going to put on your you know instant response resources and whether you can actually scale to support both incidents happening at the same time is
an interesting factor now another you know trend that we observed here and it's nothing new but I think it's important to pay attention to is attacks against the emails you know that when we talk about emails it's all about spear phishing campaigns and how the attackers can use emails to to target individuals and compromised systems but 2016 especially the southern sixteen united states a presidential election brought email hacking and theft back to the front front of the cyber security concerns you know during the past year we conducted a number of investigations where we had observed a large amount of emails were targeted specifically by the attackers so they were not going after you know private information is a
storing databases they were just going after emails right and there were a couple of interesting techniques that attackers used in this process one of them was the odd phishing and delegation so if aught is an open standard that is used by applications to authorize access to information without requiring the passwords essentially enables it to share information if you have it or talking and we have seen this technique since 2015 in nothing new in terms of the the sophistication but I think it's the frequency that is concerning where attackers would would basically use the auto can't especially for situations where clients are using cloud services providers for the emails document management and so forth in one instance
that we investigated the attacker basically essentially registered malicious application and send an email a phishing email to a user user would click on that application would install the application and registered under his Google account as part of this process the user would be providing permissions to the applications from their own the application would have unfettered access to users data now what is interesting about this process is that it can bypass two-factor authentication because as long as the application is on the user's device there's no requirement for authentication and also even if you reset the user's password the attacker would still maintain access to the emails now think about detecting this in your environment you know we are founded
it's extremely difficult to detect this on the host environment because there's essentially no artifacts in there on the endpoints right it's also very difficult addicted on the on the network environment because most of the traffic is itself protected and encrypted so you have not much visibility one way of the thing getting it was we would be to monitor your administrative panels and token logs there or token logs that are provided by your service provider but but I mean how many of you have actually taught you the precise or the process of you know obtaining logs from your service providers your cloud service providers and monitoring those for for and you know the suspicious activities your expectation is that your cloud
service provider is providing some level of monitoring and security the reality is that is a shared responsibility if you look at their policies and documentation from security perspective they will probably be able to secure or grantee the security of your infrastructure but when it comes to the application access to your data they are heavily dependent on your ability to govern access and and data protection another techniques that we saw with the Microsoft Exchange web services so EWS or Microsoft Exchange web services essentially provides the ability to access the data that is stored in your exchange server using an API over HTTP when it comes to the the Microsoft exchange environment you know there are different ways that you can access
emails or W or the also web access would support multi-factor authentication so it's generally a best practice to implement two-factor authentication on all the other UA or require users to VPN in before accessing OWA similarly for for the cloud base marks of you know office 365 if you enable the model on the authentication feature you can basically require host to two to two factor authentication able to access the environment now when it comes to EWS or ActiveSync these these would not support two-factor authentication so typically the recommendation is for these services to be to be not exposed to the internet because the attacker as soon as they gain access to a username and password they would be able to programmatically
access the output exchange and exfiltrate emails in a number of instances we saw attackers once gaining access to the environment when it a tws services were not exposed to the internet they would basically laterally move to the exchange servers deploy tunneling tools or deploy web shells that would enable them to basically use EWS as a mechanism to access emails in fact I think apt 29 which is a Russian based actual talked a little bit about it later on use this specifically to harvest emails as one as one part of one of those campaigns against the election and then lastly mailbox delegation in Microsoft you can essentially as an administrator or delegate access to a mailbox again will
have one user be able to access other users emails again we observed this technique in a number of apt attacks where the attacker had basically dedicated access to two users emails to to actually multiple users emails and from there on they were available to steal users emails so so just generally thinking about how you can procure you protect your emails and it's not all about the endpoint there are so many other ways attackers can actually compromise your email in the environment and there's also so much information that the attacker can go after that is really just a story in your emails email is definitely a very interesting you know the source of information for a
number of attackers especially you know stated sponsors where they're after you know commercial espionage many of the business decisions are made and are documented within the emails but also we have seen email compromised they're being used in scenarios where cyber criminals are trying to initiate a fraudulent transaction where they would try to understand the business processes that leverages email for example invoicing is a very good example of that intercept that process modify the emails and as a result of that initiative fund transactions to an illegitimate target and fishing I mean phishing is not going away we obviously do technologies that are more effective at detecting phishing campaigns you know the sandboxing technologies that we detect attachments
now some of those are getting better at actually analyzing the links that are embedded in the emails software would actually look for username password in the context of a content of email and use that in order to you know get cryptic encrypted content for this purpose of analysis but you know I wanted to point this out because we continue to see innovative ID by approaches by the attackers to to bypass these controls one example that we saw was very interesting where attack is actually called the user to teach them how to enable the macros on onwards right or in other example where the social engineer the user to providing their personal password email account and target them
to the personal email account because they want to bypass Thema controls that are in place one other example was the use of email sorry the use of chat Enterprise chat software for example a Skype enables you to be able to reach to people especially if you have a federated account and register that with Microsoft so you don't even really need to go to the email the route to reach the user just think about the different ways that attackers can get to your users and entice them to click on the link email is definitely not the only way of achieving that now when it comes to multi-factor authentication it's certainly one of the effective controls that we have recommended many years to
to our clients the idea here is that you know you don't want to protect your most critical assets just based on a username password because it's easy for an attacker to obtain access to that username password other to the compromised of let's say your Active Directory or just fishing the user to entice them to provider username password we also always recommend using multi-factor authentication for both you know the state mechanisms that provide remote access to our environment so externally facing services but also your critical infrastructure internally you know your administrative charm box says you know your critical databases and so forth while it's at an effective technology and capability I think it's also important to emphasize the areas where
you know attackers are actually bypassing these capabilities based on gaps in configuration operation of the environments or just generally leveraging the the variety of techniques that are available to the attacker so this is again not a new trend for again as more companies or leveraging these capabilities to go protect your data we see more and more attackers are merging different techniques to bypass them some of those can be prevented some of them may not be as easy to prevent without using other technologies so one way of you have seen attackers bypass multi-factor authentication which is very similar to phishing is the pass through with multi-factor authentication essentially they entice the user to click approve on
their token it was in an email the user would go to a you know a legitimately looking website that asks for the user and Passover at the same time asks were talking token authentication and the user would provide that once the token is approved the attacker would use that for for other activities essentially that would intercept the one-time password another example is the enrollment of the tokens so we have seen in a number of our Red Team engagements where it would compromise the environment and then you know certain targets are protected by two-factor authentication this scenario is the first thing that we're going to do is to look for the token registration emails in users email accounts some of those
actually are so old about you know three to four years old when the user initially joined the organization but with enables we essentially register a new token for us and use them so it's definitely a good practice to make sure that this already moved or expired after they are initially issued one instance we saw attackers exploiting an XSS vulnerability on the portal on the VPN portal that would essentially enable the attacker to capture the tokens so the one-time tokens are passed on to the attacker one other example is when attackers would go after the multi-factor authentication itself right you know sometimes your multi-factor authentication provider is already integrated into your domain admin so as soon as the attacker is able to
compromise your Active Directory they would be able to gain administrate access to your resume RSA server and from there on they can essentially register themselves with new tokens and other you know opportunity we have seen in many clearances where they have you know these groups on Active Directory that are exempted from performing multi-factor authentication so the attacker simply would need to just add a user account to this mode the group on Active Directory and from there on it would be able to bypass two-factor authentication and lastly again nothing new we have seen in situations where the second factor is not it's not secure enough the an attack you are able to exploit that and bypass multi-factor
authentication one example of this certificate based authentication right these are situations where the certificate is is a stored in the register key as non exportable abided by the body configuration but once the attacker is able to compromise the system they are able to export that certificate from the register and use it on their own systems you know the the best factors configuration for two-factor authentication is that the two factors should be independent from each other right so when you have the user and password on the same system as stored in the cache as well as you know the certificate again on the same system it's not really true two-factor authentication so we have seen that's
being exploited in the world for bypassing multi-factor authentication now in terms of malleable trends I mean there's obviously a lot of different malware samples that are produced every day I mean that you hear these crazy numbers of to two million malware's every day or 98% of the matters are only used once and and so forth so so there's going to be continuous innovations there and at the same time we're finding that the technologies are getting better at detecting executable based malware's you know dll's and exas that can be run in a sandbox environment and to take activities that are typically not associated with legitimate software very indicative of you know malicious content we when it comes to a script based
malware refiner technologies are lacking these situations where attackers would use that's a VBS script or PowerShell you know macro enabled the type of content in order to bypass the detection and gain initial compromise and so we do actually saw that expanding in 2016 a lot of user for you know PowerShell in the initial compromise phase and that's just going to continue we also see that for for macro based enabled documents attackers are using unexpected formats that are not very well known or at least are planned by by the security technologies we saw attackers using the the Microsoft Publisher document was or the max of Windows 2007 template files the dot M files and also the PPT the
template files so you know we're going to see we're going to see a continuation of these activities where they find more innovative ways of bypassing sandbox or execution detection capabilities when it comes to around somewhere I'm not going to talk a lot about it obviously there's going to be a significant increase on the ransomware attacks I think the one projection but Beasley was was that they expected expected the number of ransom attacks is going to be doubled by 2017 but we have also seen that law enforcement has made significant progress in in mitigating those we do foresee law enforcement is going to continue to you know catch up here and and target ransomware situations especially when they are relatively
opportunistic and and we have a large audience now when it comes to ransomware a couple of interesting trends that we observe was was that you know historically when somebody's initiating a ransom campaign they wouldn't target an individual or an organization they would distribute as to as many people as they can because they're more people who have an opportunity to click on and get infected the more money the attacker can make right and from the attacker perspective this is a really good return on investment because the level of effort that it takes to prepare a ransom and execute on that is relatively low we don't need to customize that your targets and so forth now in a number of situations we
actually observe targeted attacks using grant summers and that these some were actually initiated by a stated sponsor to cause disruption so once they gain access to the target environment they leverage the Active Directory foot to deploy ransomware across the board all of a sudden all of their servers were actually encrypted and other situations where cyber criminals have the bridge ransomware again targeted situations where they would go and identify most critical systems of the organization that holds the data and deploy ransomware purposely to that specific system and and again lastly the MBRs and VBR base members these are matters that would basically target the layer underneath the operating system it's your Master Boot Record or volume Boot
Record to bypass all of the controls that you have a within the OS in fact in in one of the financial cases that we had the attackers solely relied on VBR based malware to maintain persistent in the environment which just points out the fact that there's just going to be more and more use of this for the persistent purposes it's very hard to detect the technologies of today are not detected - are not designed to detectives and at the same time many of the investigators are not very familiar with these new advanced persistent mechanisms now extortion is not a new trend it's used you don't even find that in the M trend but in Canada we continue
to see extortion cases what we mean by extortion is the attack of gaining access of the environment compromising the data taking the data out of the environment and then reaching back to the company and asking for or for for certain amounts of fund normally in the amended form of bitcoins and threatening that if he does not receive that data why so and so did all that one by so and so data will go ahead and publish that data on the public or they would sell that data in the underground market and you know the typical ransoms would range between fifty K to eight hundred here or even higher and months depending on the value of the data that the attacker has
gained access to nice the ocean campaigns are important and goes back to the to the discussion around advancement of the cyber criminals and and financial actors in the sense that I think again every organization could be subject to this you have data that is important to you maybe the attacker can not sell your data in the undergone forum to to make money from that you know the PII or critical information is not as significant to your environment but there has to be data that is important to you from the you know the competition perspective from the reputation perspective that's what the attacker would go after so it there's a a bit of the shift in my mind said where
you you always think about who would be interesting in my data I think it becomes the question of what data is important to me rather than to the attackers one group that we have a specifically seen significant level of activities in Canada we refer to them as fake Tesla group so they're not the real Tesla group and we have a number of reasons why we think that's the case but the first case that we investigated from this fake Tesla group or FD T was back in 2013 when they had targeted an organization in the morning and resource industry they had compromised the data at the time they actually introduced themselves as angels of truth so they
had not even adapted that take the Tesla team name they saw the data and they basically just published it on the internet and the same time they asked the company to stop their miss practices they were a generic in this process didn't really talk about what miss miss practices they're talking about and and they they also chattin that if they don't basically publicly announce and apologize they are going to basically post more data and cause disruption or in this case the company obviously didn't even learn about this because the email that they receive initially was ignored or was a spam filter and so the Italia actually went ahead and cause disruption on the system and the method
of disruption they use was very very simple they basically overrode the whole see directory with zero and restarted system I think as a result that a specific incident the company was not able to pay their employees because the his ap system was done for about a week or so and think about a mining organization that you know with it's a position that is dysfunctional it it was definitely very significant now over the years we have seen them to to improve their capabilities and also figure out ways to monetize their access in terms of the sophistication of or capabilities that they have all the tools that they use we think they're relatively unsophisticated they're not using very
advanced customized malware they typically leverage open-source malware PowerShell the scripts that are available to anyone and they are very consistent in terms of their methods of operation across different targets but we see that they are you know depending on the type of the data they gain access to the amount of ransom could range I think the initial case where they asked for around some day it was around 40k US dollars and then the last one they asked for ransom about 500k so you can see this natural evolution of these these attackers and if you think about a you know in general extortion attack that we think they're they're going to be very very profitable to the attackers and
also going to be very interesting to the attackers for for the main reason that the level of for that it takes to execute on one of these it's significantly less than the liver before that would require two let's say for example initiative fraudulent transaction all the attacker needs to do is to compromise system escalate villages laterally move copy as many files as they can from your shell and then from there on they can basically ask for a ransom so that's why I think this changes is definitely going to get to be continued and there's going to be more and more cases that we'll hear about in Canada specifically interesting flag about Tesla team was that all of the targeting that they've
done that you're aware of is in Canada and it's just by nature of targeting it's very interesting they're just focusing on the Canadian organizations some of the lessons learned from these are you know the disruptive attacks and consideration is that before taking any actions you want to confirm that the breach is actually real and the attacker is has access to what they're climbing to do claiming to have now typically they would they would basically share with you samples of the data that they have right now from your perspective you need to have two immediate objectives you need to understand that your data is gone and when the data is gone it's gone you don't have any control over that
right you should immediately focus on understanding how they're maintaining access your environment and how you can remove them and the second question that you need to answer is what kind of data was taken so make sure that you don't get distracted with other aspects of negotiation with the attacker or payment versus not payments those are important but do not distract your you know the information security capabilities and resources on those factors now when it comes to paying the ransom you know a quick oh really different ways the reality is that that data is the stolen you could potentially save your data from being published at this publicly but paying the ransom but there's also chance that the attacker with that
should ask for more ransom after you pay them or they would just go ahead and simply obvious your data even claiming that they got around some and other things which is which which could have potential reputational concerns and maybe lastly on on the attacker trends around the status sponsored activities the what you know initiative we observe in the daily sponsor you know that landscape china was obviously significantly active in this area for a number of years I think since the early 2000s they target many organizations for a number of reasons mainly around the commercial espionage where they would go after the data that would be important to a state-owned company from the competitiveness perspective or you know
intelligence based data aware or political intelligence data over they would use that as part of their political objectives or to insure the you know stability of their environment and promote their objectives since 2014 mid 2014 and especially September 2015 when US and China agreed on a treaty that neither government would conduct or knowingly support cyber-enabled theft of intellectual property we have certainly seen it the decrease in in a number of targeting and intrusions by China against North American companies that is not necessarily the case for you know the activities of the Chinese cyber cyber operations in the region so we associate target against Australia the Japan South Korea and so forth but definitely in North America we are
seeing less and less of China activities but then on the other hand we have seen as significant aggression on the Russia side in a Russian cyber criminals are very effective they also exercise significant security in their operation so hard to detect and we see we have seen basically a significant aggression being exercised by the Russian actors against the North American and European East European specifically companies two of the groups that we have heavily seen especially in in US and some activities in Canada apt 28 and apt 29 both groups are very sophisticated we have seen them leveraging you know the zero day vulnerabilities all vulnerabilities that were just published but were not realized so their time to the
organization of these vulnerabilities are very short and and are very innovative in the different ways that they would target organization since that they have access to significant development capabilities that will enable to address and cosmology tools when they are targeting an environment for example apt 28 we have seen you know since 2007 they have been just developing code based on a very flexible and modular framework they are heavily incorporating the content analysis capabilities to make sure that you know there are on runtime checks in place and and essentially making it more difficult for intrusion detection systems to detect those activities or analyze them you know the use of odd the vulnerability or issue that I talked
about earlier as tragic web compromises and and you know in one case for a Canadian company I actually remember they they basically compromised the user credential using net basis proofing on a Wi-Fi network that the the user you know was connected to so the user was travelling to a conference the attacker was able to converse credentials for acquiring that over the Wi-Fi and and within hours they use that to access the organization so that's definitely they're finding different ways and and very innovative less repetitive in terms of the techniques that they use definitely very consistent in terms of the you know the content that objectives that they have and and the relevance of that to the to the Russian government
policies I only have five more minutes just went very quickly I want to talk about of the defensive strategies you know the reality is that obviously the cyber risk has been identified as one of the major potential impact impacts to the business and many companies have have investments significant in this area in the past year we saw many organizations that acquired capabilities around automation or hunting in automation makes sense because IT professionals we have invested heavily in different technologies and for solutions for security which has resulted in the significant alert fatigue we get to the tour of data and our job as security you know handlers incident handlers we is to monitor these errors and identify
you know the signals in the noise and and something like automation would be helpful because you can basically try to minimize the amount of time that your resources are spending on a day to day mundane security activities and focus on areas that data with bring most value like hunting the hunting is thought to be the process by which you know a human actor would basically sit down and analyze your data it's not very alert based driven rather it's a very human centric process focuses on building hypotheses around if the attacker was going to target my environment or would they come in and and look for the specific data that would represent that hunting is important because in some of
the attacker techniques especially within the lateral movement privilege escalation and persistence is sometimes very difficult to detect by technologies because they essentially you know hiding the day-to-day processes and operational activities within the environment now all that being said we continue to see that companies and organizations are lacking when it comes to fundamental security practices their realities that are our networks are not built with difference ability in mind right and and did you know the getting your technology is important developing advanced capabilities are important but that's not going to realistic the fundamental requirement for the cyber security in fact when these fundamentals are not in place is advantech knowledge 'yes are not going to be as effective at at
performing their job and reducing the risk you know when it comes to some of these fundamental concepts definitely understanding your crown jewels your systems that would would represent your critical data you know what systems are running which applications and which applications are using which data that are most important to your business think about restoring these capabilities in a cyber situation that is disruptive if the attacker you know destroyed your systems your tier one systems how quickly can you actually rebuild them and start from scratch visibility is key especially when it comes to you know endpoint visibility because you know historically we have had a lot of thought given to where we can incorporate network visibility when
it comes to endpoint we don't have the developed depth that would be required from the investigation perspective but also some of these know new areas that we're getting exposed to you know how do you monitor your cloud how do you monitor your BYOD how do you monitor your integrations in into the variety of third-party vendors that you're connected to credential management and multi-factor authentication we talk about those but almost in every incident that you respond to as soon as the attacker gained access the environment they will go after your domain credentials how do you make sure that you minimize the number of domain credentials usually password and ensure that the administrator are exercising you know
some policies in using those admin credentials and network segmentation and de jure segregation you know that the impact of a security incident could be significantly less if we sufficiently protect our most important data that the reality is that we cannot protect everything at the same level it's important to take an intelligence based approach understand your exposure try to reduce your exposure your as much as possible you know resolve as many vulnerabilities as possible understand what is important to you and your business and and what kind of protection do you have around that and then prioritize your investment and services to basically focus on what is most important see or to your environment and an established
escape of virtues hopefully if your briefs you are able to detect the attacks and by just making it more difficult for the attacker to eventually obtain the objective you're essentially increasing your chance of detecting them I almost run out of time if there are any questions I can answer
so the multi-factor authentication you know there are different types of video is the whole hardware based tokens there's a mobile there's a text we definitely don't recommend takes very small two-factor authentication typically recommend the software based or Hardware based most important thing is that you make you make sure those two factors are actually independent from each other right and attacker by compromising one channel is not able to compromise your two factors
thank you so with regards to state-sponsored attacks you know Russia may not really want to cover their tracks they're making political statements by not doing so but with regards to China and other countries that you're saying you're seeing diminishing profiles on them is it not more likely that they're simply going underground and covering their tracks and and as a result of diminishing any political flack that may result I mean do you actually believe that there's diminished attacks coming from those from from China absolutely we think it's not I guess in terms of frequency its diminished in terms of focus and and success it's not and what we have seen in China's activities is that their
activities are a lot more focused I think it has to do with a number of factors one is obviously the US government I you know agreements with the China government it was significant exposure of Chinese activities but there is also significant streamlining and coordination within their military services so we think they are just becoming more effective at directing their their effort in accomplishing various specific goal you know what we observed from China was that there was a you know decrease in targeting of the commercial space but their activities against the government especially for the purpose of political intelligence gathering continues right and so I think the capability is there at some point they will probably use it
but it's going to definitely be more focused and coordinated
all right thank you very much for your time I appreciate [Applause]