Descifrando los Infostealers en Latinoamérica: Una mirada a su evolución
Show transcript [en]
Today we are going to talk about InfoStealers. This threat that according to our monitoring of C-Labs, we represent CITUM, has been a fairly growing threat in recent months and in general in recent years, resulting in fairly complex attacks such as giving access to to attacks of ransomware and in general to the exfiltration of information from different organizations. The truth is that this is not a threat that simply affects some organizations, but it also affects many users. My first question here would be: Who of you has been a victim of InfoStealers? Raise your hand please. Nobody? Well, that's very interesting, because according to a recent investigation we did, there are more than 10 million active credentials
that have been sold in forums on the dark web, and many of them are associated with common users, not necessarily organizations. So, there you can find different things, which we will address later. To begin, sorry to start by myself, but I am Daniel Soriano, I am a computer engineer at the National Polytechnic Institute. I have a specialization in national security and intelligence. I am currently the leader of the Cyberthreat Intelligence team at Citum. And well, I have given different conferences. With me is also Julia Viña. He is a professor of computer science, sorry, an engineer of computer science at the National Polytechnic Institute, a professor of computer security, and he is also a member of the CITUM team, C-Labs. He has also been a speaker at different
conferences and he has found some exploits which you can find in those links.
And we also have Josic Espinosa, who is a computer engineer. He also has a master's degree in computer security from the National Polytechnic Institute. He is also a member of the team, of the team of Trade Intelligence. He has been a speaker at several conferences. And he also has some registered CVs, which are very interesting, because they have to do with DLL SciLoading. So, specifically talking about the agenda, we are going to talk about what are the InfoStealers, what is their objective, their evolution, how do they acquire attackers, in fact we are going to show some screenshots from some of the dark web forums where cybercriminals are acquiring this information, what do the adversaries use it for, the general overview of the InfoStealers in the camp, What are
the most relevant families of InfoStealers in Latin America? The most used techniques and procedures by InfoStealers? How does the victim see it? This is quite interesting, but what we are going to observe here is a real-time recording of how an InfoStealer compromises a device and how the information of that device is stolen. So
Hello, good afternoon everyone. My name is Dani. And what we are going to see next is what InfoStealers are and what their objective is. Most of us, because of the name, imagine what they do. Generally, there is no information. Here I am going to ask you something. Have you ever downloaded a pickaxe? to activate their windows, I say here to analyze the malware, but I have heard that some use it to activate windows or who knows for example Ares or Linewire that were like applications to download Trojan music or photoshop, those who are designers or have an approach with that type of environment, photoshop pro, pro plus 3000 full + crack so many times we
are not aware of what we are downloading and most of the time In these scenarios, what happens is that malware is installed. And many of these times are the InfoStealers. The InfoStealers, as I mentioned, have the main function of stealing information from the infected teams. So here, to not take too long, I'm going to... We put a list, but mainly this: Banking data, user and password. Information stored in browsers, all the navigation history, the session cookies, the auto-filled form, in general all the information that we store in the browsers, for example, our favorites, and the pages' histories. Electronic email accounts, the contacts that we have in our clients, for example Outlook. Information about the operating
system in general, what is the operating system, what architecture, the security tools that we have installed, the software that we have installed. personal files, images, photos, documents and crypto wallet. Many of these infos have the ability to kidnap the wallet. So if you have the habit of copying and pasting your crypto wallets in the portals, some of these have the ability to replace the wallet with cyber criminal wallet. So later we will see why all these things are relevant. Later, all this information is sold in web forums, in illegal channels, in Telegram and in different media.
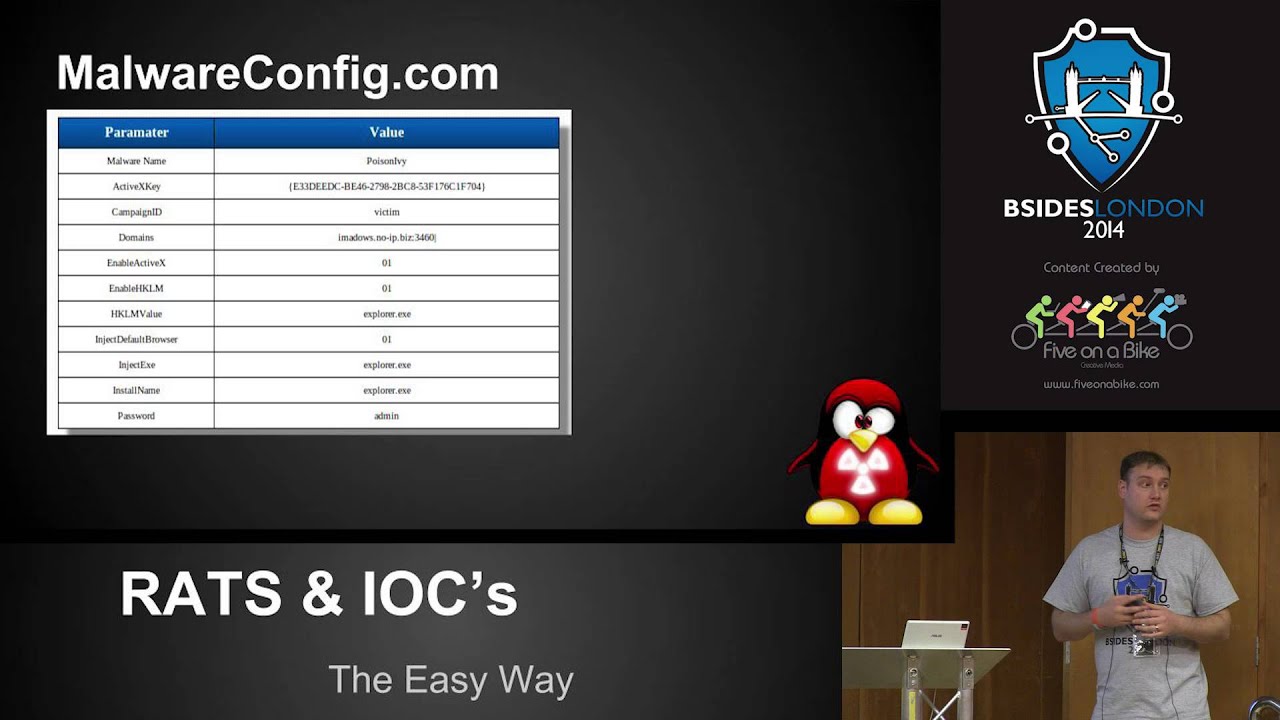
We are going to see a little about how these threats have been evolving. Here, for example, in the 90s, there was a very famous tool called WIFIS. Let's say that at the time it was very famous, it was presented in DEF with 6 in Las Vegas. And it was presented as a legitimate tool of remote writing, of remote administration. However, obviously due to its capabilities, it began to be used by cybercriminals to steal information, take screenshots, monitor the keyboard, etc. Another of the threats in the 90s was, for example, AOL Power Trojan, which is something old, those who are a little older will remember that there were different AOL services, electronic and messaging services. So
it was a Trojan specifically for these credentials and to obtain access.
Sorry. After the 2000s, we started to see other tools. Other tools, like two keyloggers, which basically is a keylogger that captures the keys that the user presses. It is a tool that was often used with legitimate purposes to monitor the activity of employees or to do child monitoring. But for the same of its capabilities, it was also used maliciously. And here we started to see another type of malware that already had more capabilities, like Zeus, Zbot, SpyEye, that already had more specific capacities of a bank bank to steal bank credentials.
- banks where the domain of the pages was modified to steal the credentials or to replace the forms. We were already starting to see, for example, Imhotep.com and here something where it is already starting to get a little more interesting because this type of threats, they already began to have the capacity to be modular and many times they have been used to deploy ransomware, which is here where the thing begins to get dangerous. The distribution in general of Trojans in the infestilers, in general, has been maintained by phishing campaigns, electronic mail with joint files, for example, Word files that contain "CodeMalicioso" in video and run the malware, or download it, through cracks or through patches or
activators. And that is maintained over time. And in the current, here we have some tutorials that we have observed, more recently, and that one of the main characteristics is that they begin to distribute or operate under the malware as a service model. This means that, let's say, anyone no longer needs to have high technical knowledge, as for build a InfoStile or a family of malware, but simply pay for the income of these threats and have access to an administration panel like this. This makes it a little more dangerous because anyone can have access to this type of threats without having to have extensive technical knowledge. Here we put three of the families in need that
we have seen that have been more active in Latin America during the last semester, which is Luma and RicePro. In general, they have the same capabilities, information theft and are also used to deploy ransomware. Later we will go a little deeper about this.
- is a state they in for you know this red line you can't even put it with the capacity that is not a game is your not but what i can't understand is it a simple promotion is a rather malicious it's a little bit important that has to be in contrast with the computer is malicious not don't say it's a little post Here we also have another example of how to acquire it. This is an example of a screenshot of a Russian forum where this type of malicious services are constantly being offered, not only from InfoStreamers but also from Ransom, Rasa Service, where for a small amount of dollars or bitcoins of their effect, they can
get this type of tool that has enough capabilities to take action from compromised teams. Also, if someone gets curious and says, "Hey, is there a way to get this type of malware for free?" Now, But why do attackers use it? They already talked a lot about InfoStealers and that I have to worry about them, but why do they use it? Why can it become a dangerous tool for my device? Well, for that kind of thing, right? It is quite common for users to save in their browsers the credentials of Netflix, Disney Plus, Active Directory, the company's administration console, Amazon and any service that they need, because it is obviously easier to access them if I already have the password saved, right?
So, this is taken advantage of by attackers to to steal their credentials, their e-mails in a simple way and with that, obviously, they can make more complex attacks. Because there is also a bad practice that many users use, which is to use the same user, the same e-mail and password in several services. So, with one of these, maybe I'm trying with different services, different social networks, and with one of these, I'm successful and I can also access other types of services. And also, why do they use it? Well, obviously for bank data theft. Surely, you have seen that some services, some online banks, still don't implement or don't do it obligatorily, the part of the
multiple authentication factor. So, in many cases, with just having the user and the password of the web application, it is possible to have access to the account and with it, well, to be able to steal our money, right? And another interesting thing is the theft of documents, not theft of sensitive information. Databases, photographs, documents obviously depending on the victim, because they will be the documents that are stored in the device and that can be of interest to other types of cybercriminals that maybe seek to do specific damage to that victim. And something that also becomes quite interesting for organizations, or rather quite worrying, is that also through this type of tools they can have access
to the VPN accounts of the services of the organizations. Many times we have also observed that there are some users who have bad practices and say: "Why not? I'm going to use my personal computer, where I have many games with cracks and many illegal things, I'm also going to use it for work." And obviously they give way for cybercriminals to access their devices. It is another bad practice that some users usually follow. Now, after I talk about this, this is also a vector of initial access for some more complex attacks, like ransomware attacks, where many of these adversaries go to the dark web, go to these cybercriminals forums, get access in these forums, paying very
low amounts for the damage they manage to do, like 10 dollars for example, they buy accesses with their 10 dollars, especially from organizations, and in the end, after a complex attack process, they end up ciphering the company's files.
And now, all this that we have told you, how does it look in numbers? And we can see in this case the number of publications related to infestation activity in the different Latin American countries. As we can see, Brazil has almost half a million publications on the dark web related to this type of threat, followed by Argentina and Mexico. Very close to Mexico are Colombia and Peru. But all this is relevant. Well, unlike some families of ransomware, of bank trojan, which focus on some specific countries, like in the case, for example, of Mecotio, which sends malware campaigns to Mexico, Argentina, Brazil or Peru, In this case, the InfoStealers are present in all Latin American countries.
In greater or lesser quantity, but we can find active credentials of users from anywhere in Latin America, including countries that at some point are usually a bit irrelevant for threat actors. Especially, for example, for attackers who use ransomware, such as Nicaragua, Haiti or Honduras, for example.
And well, this graph that we put here is very interesting because when we are doing or we are analyzing the telemetry about the InfoStealers campaigns that we see in the whole region and that we want to identify patterns, this type of tool serves us. For example, here what we put is the activity that we have observed of these InfoStealers families that are on this side from December 2023 to May 2024. So, for example, if it says that in December it is all green, that means that we have seen the presence of practically all InfoStealers families except Ninja in December. And then we see, for example, in March and April, some red squares, which means that
is where we have identified greater activity. This type of thing, as I said, allows us to identify patterns. Why is this happening? Why in March, in April, in December, or in certain months? Well, it happens for many things. For example, when it's tax season, cybercriminals usually do campaigns, for example, of malvertising, to advertise police, ambushers, and they do campaigns related to tax payments, with refunds, etc. So, this allows us to precisely, more or less, identify patterns, and on those dates, we will also start to disseminate intelligence and information to help organizations to have a better security posture. Very good. Now, talking about the threats that we are most recently observing in this last semester, we have three, the top three that we have observed. The first one is
Luma, the second is Rise Pro, and the third is Red Light. If I forget, it is also present in the region, and Steel is what we are observing that has a significant increase in attacks. In fact, the cousin of a friend recently was a victim of this type of InfoStealer, and we see that it has quite interesting capabilities to be able to make the action of security tools. So, very little here with this type of InfoStealer. And well, as Daniel mentioned a moment ago, the most relevant InfoStealers in Latin America are Loom, in the first place, followed by Redline and Rise. But some of the features that are present not only in these three families,
but in general in all InfoStealers families that we observe in the region, is that they are sold as Malware as a Service, which means that, as well as the Software as a Service, as the Platform as a Service, then the malware is sold with support, with infrastructure, with all the software necessary to deploy it, with all the instructions necessary to deploy it, and in case it is needed, for example, even with the templates of the phishing campaigns necessary to deploy Smallware. It has multiple distribution mechanisms, among the most important are the massive phishing campaigns, advertising advertising of malvertising, which is malicious advertising of browsers, also through ads on social networks, or as we commented a
moment ago, also through the downloads of activator, cracks, or all this kind of malicious software. It has multiple monitoring capabilities, not only the information of the device is stolen, but it also has the ability to monitor the activation of the keyboard, the mouse, the screen, and even the camera. It steals multiple types of information, unlike some of the macs that we analyze day by day, that focus on bank data theft, in this case, attackers could obtain practically any data that interests them from the team, and in a moment we will see a demonstration of it. Also, several of them have the capacity to perform downloads and executions, which makes it a very dangerous threat to
organizations, and to all of us in general, since an InfoStealer attack could also lead to a more dangerous attack, such as ransomware, for example. Many of them also have the ability to filter files, which is a very dangerous threat, just like ransomware, since the only thing it lacks to do it, for example, is this part of the encryption of files. From there on, it has the ability to download, execute and filter. It uses multiple command and control channels, not only the channels created by the attackers, such as domains or own-management servers, but also uses channels that are already used and that in a certain way are serial, such as Telegram channels and groups, and even
in some cases they usually get certain instructions from YouTube comments or comments on Facebook as well. The typical attack flow of a InfoHealer begins with the distribution method, which as I mentioned a moment ago, can be through phishing campaigns, malvertising campaigns, downloading of non-legitimate software, of crack, activators, or through social networks. Later, all these campaigns usually have files or joint URLs. Normally, these URLs or these files are usually compressed in zip format, although we have encountered any type of format of... of... of... of compression, sorry. Like it can be UUV, RAR, 7-zip, etc. But then follows the installation of the malware and its complements, which implies the creation of folders, creation of persistence, among others. And they continue with the information theft, which as I mentioned a moment ago,
can be any type of data, including passwords, encrypted activity, mouse, screenshots, etc. Followed by the command and control phase, which can be channels created by the same attackers or existing channels, in this case represented by the Telegram icon, which is the most common among the infestillers. And finally, the sale of information. The sale of information is usually separate LOCKS packages in different sections according to the type of information sold on the dark web for a relatively cheap price, depending on the information that is being distributed and depending on the user and organization that has been affected.
. Right now we are going to describe the main techniques that we have observed when we analyzed the InfoStealers according to the MITRE. Surely many of you already know what the MITRE is, but it is a framework that groups, classifies and describes the tactics and techniques that cybercriminals use to carry out their attacks and in their malware. One of these is Gather Victim Cough Information, which basically consists of collecting information from the infected team. And well, this is done to make a recognition of the environment and it serves them because they get information, for example, of the security solutions that are installed, the version of the operating system, and based on that information that they collect,
they usually send tools to disable security solutions or other types of tools that are compatible or optimal in the environment that they recognized and that facilitates their attacks.
Then we have the process injection technique, which is interesting because, well, who hasn't been in their computer and says, it got very slow, and we always blame Google Chrome, right? The classic, the ball eating the RAM memory. And well, many times this is caused because, just behind it, some malicious process is running, related to, in this case, InfoStealers. And what this process injection technique is about is that basically the malware is injected into some legitimate process through various techniques, like process hollowing or process uh And this is obviously one of the main techniques of the InfoStilers, because it is precisely the technique that is used to steal information. But not only for this, commonly, communication is always bidirectional, where through some protocol, HTTP, HTTPS, SMB, the infected team receives
instructions and also the exfiltration is carried out to a server. And not only protocols, we have also observed how exfiltration is carried out through HTTP or even through the Telegram app. There are different methods that we have observed. Now, another interesting technique that adversaries use is to omit the artifacts, to somehow make them incontrovertible for security solutions, because obviously, some people have antivirus tools, they have tools like EDRs that protect their devices, and that surely if they didn't have any kind of protection, they would be easily detectable. Especially with this issue of signatures, which is how some antivirus are based to detect types of malware. So, in order to somehow skip this kind of protection,
what the adversaries do is use different tools, even make different modifications in their source code to break these signatures and be able to go unnoticed by the security solutions. Then we have the part of the evasion of virtualization and the sandbox tools. Because, let me tell you that we are not necessarily the best friends of the cybercriminals. Constantly we are looking for what they are doing, how they are doing to help the security tools to protect them better. And they know it. They know that we use certain tools to identify how they are doing all that process of infection in the devices. And they somehow try to put protections to their malware so that we
do not know or do not find it so easy. So, that's another common technique they use. And now, a while ago I was asking you who has been a victim of a "infestilor" and no one raised their hand. Maybe this can help us change the perspective a little bit because we're going to see how a victim sees it. The victim can see it like this. As we can see, it's a completely identical phishing template of this company called FactoraTech. It's a Colombian company and it has a compressed file in TAR format that simulates an invoice. In this case, this campaign of the invoice we're looking at was directed exclusively to Colombia. But how many of
us have not received emails that have to do with, for example, the payment of electricity, with some bank transfer or something like that? Also, at this moment, we are here, we have certain knowledge of IT security, but for example, when we were in high school or perhaps in high school, how many of us were not looking for Office, for example, or Word, or things like that. And currently, how many of us are not looking for Steam or things like that. In this case, the user is looking for Adobe Reader, and as we can observe, none of the first pages is the original Adobe Reader. All the pages are paid ads that could bring some malware.
And finally, the victim can also see it like this. It's also Adobe Reader in a Facebook advertising campaign. But, how many of us, when Facebook was in its apogee, we didn't see any link, we clicked and didn't know what it was leading to. We simply noticed that it didn't do anything, or we noticed that it downloaded a lot of files and we didn't know what they were for. And now, the interesting part. Can you give me a play, please? We can see an email that the user receives. In this case, it is the confirmation of the limitation of the besides. With the text as it uses the besides when we get the confirmation of the
talk. With a PDF adjunct called ConfirmationBesides2024.pdf When the victim downloads it, what it will see is that it is a common PDF, like any other file, so far everything is normal and we don't have anything weird. But what happens when we open it? When we open it, despite the fact that it has the appearance of the invitation of the confirmation of the besides, we can notice that the whole image is an hyperlink. So when the user clicks on that hyperlink, the download of invitation.zip begins. So far there is something weird, why are so many confirmations coming to us? for us, but maybe our parents, grandparents, siblings, or cousins who don't do this could do something
completely normal. As we can see, we have a PDF called ConfirmationBesidesMX.pdf with the PDF icon. So, up to here, we could say that there's nothing weird. As we can see, it's the Adobe icon. So, we execute it. But here is where it's not good. But, then, it takes us to the Visites page. What would happen if instead of the Visites page, it was the SAT page, the CPE page, for example? Well, for us, apparently, everything is normal and we continue with our normal life, precisely. In this case, our victim is going to enter her online bank, like any of us could do, because the only thing we have or know is that the PDF did
not open correctly, that it redirected us to a page, and we probably complained to Visites the next day because their file was not working. But for us, everything is exactly normal. As we can see, the domains are those of the online bank, And what follows is that the user, as he would normally do, enters his username and password, waiting to enter his online bank. Due to the demonstration, obviously, these are false data and what will happen is that he will send us an error, which indicates that the credentials are not valid. But what would happen if it were? And not only in this online bank, what would happen if we go to Facebook, Instagram, our
email, and what would happen even further if this was not a personal computer, but our institutional computer? Now, from the attacker's perspective, what can we observe? From the attacker's perspective, we can observe a command and control site that we currently build in localhost, but let's imagine it's in any other part of the world, and this is a URL with domain, maybe .top, .shop, or something like that, of these free domains. And we can see 5 categories. In the first one, the device data. And in this case we can see all kinds of data. Because of the simple fact that the user wants to read his/her PDF and the invitation of Luis Sáenz, we already obtained his/her IP address. The
country where the operating system is located. The architecture it uses. The user name. We also know if it's a laptop or a desktop PC, for example. We know the installed applications that the device has and the ones it has allowed for all users. And we also know the applications that only that user has allowed. And all because of just wanting to read a PDF. Here in this case we can see that it has installed the entire Office suite and the current user. It has OneDrive, it has Opera GX, it has Telegram. In addition to a list of processes, which are the list of active processes in the device. With this we could start doing a
more complete profiling of the victim. Why? Because we know at this moment that it uses Telegram and that it has Opera GX. Opera GX is a browser more directed to gamers, for example. So here we can start doing a different profiling. In addition to all that, we brought the cookies. of different sessions. How can they be Bing, Mega, Opera, Android, Android developer. In this case, then the profiling is more directed to what? Maybe it's a gamer, a developer, something like that, because it has this type of information. As Dani was saying, we usually use the same email and password for everything. And the easiest thing is to save the information in the browser. Why? Because
it gives us the flexibility to write user and password again every time. What a flexibility that when I'm on Facebook, then on my bank, then on Outlook, I write the same thing again. So, the easiest thing is to self-complete it. But in this case, we can observe credentials from Chrome, credentials extracted from Edge, with login, which in this case is muchluchademovisex2024@gmail, and the text password, of course, which is muchlucha2024. and from different browsers, from different accounts, and accounts that could be a little more critical, as we will see next, there is an account there in a Samsung portal. But also our InfoStealer also left a keyword, an active keyword, where, as we can see, we
have "Bancanet", which is what our user searched for, pressed enter to search for it, entered an account number, pressed enter twice for some reason, and entered his password, which is "mypassword123", and pressed enter again. So, at this moment, the attacker, or we as attackers, we would already have all the possibility to start making unauthorized transactions, and simply empty the victim's account. Finally, our InfoStealer also has the ability to filter, and in this case we brought all the PDFs that were stored in the victim's desktop. We can observe the task of master 1.pdf, passwords, which can probably be an archive where the user stored the wrong passwords, tax form and demand. In this case, the point is to exemplify that the user can bring any type of archive that we
have on the device, and they can be confidential archives that can not only compromise information, but at some point they can get us to extortion, perhaps because we are involved in some kind of crime, because we are carrying out a judicial process, and this may not be just, or not end just in the sale of data, but also go to more critical points such as extortion, for example. But what follows? Well, what follows is the sale of all this information that we extracted in the dark web. This is Russian Market, which is one of the most common forums for this type of threats, more popular for the attackers who implement this type of threats. And
we can observe different logs of some of the websites that we have talked about, which are Luma, Redline, from Mexico, Spain, Argentina, compressed into a civic archive at a cost of $10. As I mentioned, it really is not a cost too excessive for the threat actors and that they could really use it for anything. All this, how does a 100% real log look like? Well, a log looks like this, as we can see, it doesn't make much difference from what we showed in the demo. And well, it's just an URL that we would copy and paste, a username and a password that most of the time, or when they can be captured, are in clear
text and the platform to which they enter. In the case below, for example, the username is unknown, but the password is known. So in this case, taking into account what we have been talking about from the beginning of the presentation, we could try with that email and with that password on a lot of platforms and it can be used in all. Very good. Talking about the adversaries, the threat groups that use this type of tools the most, we have APTS36, also known as Vingin Eagle, which is in charge of doing cyber espionage tasks in Latin American countries, especially Colombia and Venezuela. It has been seen out there that it has activity. In fact, it is already expanding. In the last campaigns we have analyzed
of this cybercrime group, we have noticed that it already has some characteristics of the use of the Brazilian jargon, so we also believe that it can be affecting Brazil. So, I repeat, its final objective is to do cyber espionage using different themes in its phishing emails, such as judicial citations and some other legal things, where the victim is threatened that she is being processed penally, and in order for her to proceed, she needs to open the email. foreign is And one of the many things we do here in C-Labs, in situ, is to monitor the threats that affect the Latin American region. We are constantly checking the malware that is affecting organizations or individuals. And in this case we have this emerging malware
family that we identify is affecting the region, specifically Brazil. And one main feature that we saw, that we had not seen before, is that it has some characteristics anti-analysis and anti-evasion quite interesting. Sometimes we are fighting with the assembler and with several things. But basically with this, for example, there is also a restart of the team. If it is in a different directory, supplanting different applications, like Notepad++ or applications that are used in organizations, which makes it quite dangerous because it is focused on masking between all these tools that we use, the people who are dedicated to development or other activities that have to do with technology. And in this way it is hidden in
the infected teams and it is quite critical for organizations.
Well, first we invite you to scan the QR codes that are in the presentation. None is malware, so feel free to do it. And as general recommendations, so that we take them into account in our organizations, in our homes, and we also share them with our family members. First, in the case of phishing email, avoid opening unknown email addresses. When we don't know something, simply ignore it, delete it, or in the case of organizations, share it with the corresponding department. Also avoid opening suspicious links or downloading suspicious files, and avoid using institutional passwords for personal purposes. Please, don't use your company's or your work's email to register in Liverpool, in Steam, and all that kind
of stuff, because it's something we commonly see, and that undoubtedly widens the attack area for a malicious intent. Also avoid downloading illegal software from unselected sites, Better use free software tools and avoid downloading cracks or activators. Make the correct implementation of policies for the creation and use of passwords. Remembering that the most secure passwords are those that start from three characters and are a combination of capital letters, lowercase letters, numbers and symbols. And that you have to change them at least every three months. And finally, avoid the storage of users and passwords in browsers, since as we can observe with a simple click, they obtain most of our information stored in the browser. And to
finish, some other general recommendations for organizations. Well, having blocked the service of gratuitous DNS, which is one of the different... services that attackers use to register their command and control servers, things like NoIP, IPC, and DUCDNS are widely used in this type of malware campaigns. Blocking domains like Paste, like Pastebin and any other of them, because they are also used to be able to download information, additional information in their malware, and with that, bring more configurations. Also enabling multiple authentication factors in most of the portals that can. Also, in case they manage to steal their user and password, having an additional barrier that protects them. Paying attention to suspicious behavior on the device, if suddenly
strange things come out, If something doesn't fit, and I didn't ask for that package, and it's coming to me, then be very careful with that. And finally, for organizations, have an ER solution or an effective antivirus solution that is constantly updated and that passes the necessary security protocols so that it somehow protects the devices in a robust way. From our part, that would be all. Thank you very much. I don't know if anyone has any questions. Yes? No, no one has any questions? Any questions? Hands up, no? Who of you thinks that you have been a victim of an InfoStiller and you don't know? Thank you very much. Before you leave, we invite you to scan the QR code for our blog where you can find different investigations that
we do regularly in a more detailed and technical way. And we also invite you to visit our booth where you can find sweets and different gifts for you. Thank you very much.