Intrusion Analysis: A Two-Edged Sword Against Persistent Threats
Show original YouTube description
Show transcript [en]
[Music] okay uh after lunch we are back thank you everyone for being with us all day today so this is next talk we have and we have uh ahmed moneem khan with us and said hassan borah both are from ebrix and uh is lead dfir digital foreign and hassan is senior dfir analyst and the topic they are going to discuss today is intriguing analysis to edge sword against persistent threats or advanced persistent press so amanda and hassan hand it over to you all right assalamu alaikum everybody um so the topic of our discussion today is intrusion analysis a two-edged sword against persistent threats i am ahmad munipan and right before we move towards um the meat of the discussion uh let me
introduce ourselves um i have with myself uh who is a senior uh dfir consultant at ebrix and i myself am the lead dfir and uh cti team at ebriggs so collectively we have responded to more than 20 major digital forensics and incident response engagements more than 20 compromise assessments in the financial institutions of pakistan um and we have collectively hunted more than 50 persistent threats with varying sophistication that have been targeting several sectors in pakistan and on a global scale we have responded to um nation state attacks ransomware attacks e-crime groups
foreign
for example you are someone from the retail
infrastructure
when you're not focusing on the right things again a proper threat modeling the process should actually back this up and help you do it the right way next pyramid
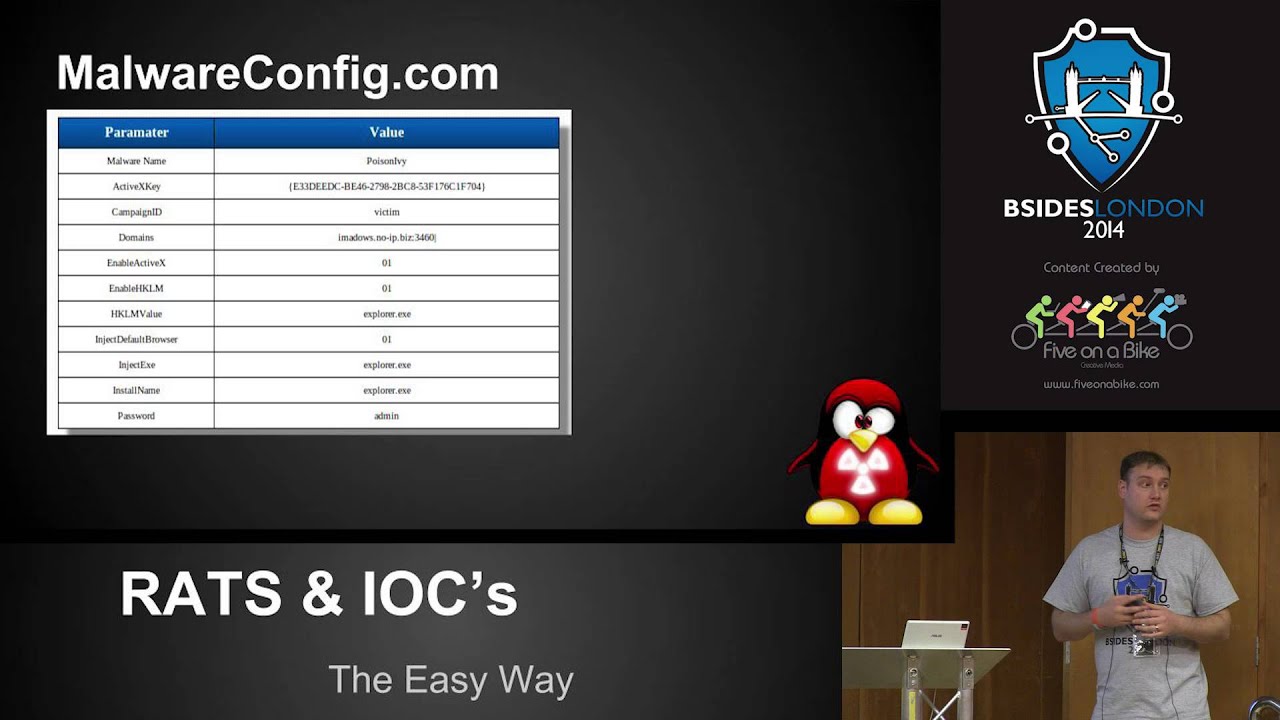
and you sweep them across your organization and you're like okay we are safe and nothing can happen to us because there's no match a problem to change them triple is as in quite easy to change a hash is changed cannot change
actual tactics techniques and procedures ttps which are actually tough to change or tools which are actually hard to write again
and now i'm going to ring bells i'm going to call my vendor help me out they can whatever different indicator does it play what if the hash which you are actually searching is not the one which was used to target your organization it's a very simple concept to use a different tool to maybe use a different differently compiled malware indicator what if a different incident is happening basically going to an organization to uh can
[Music]
is intrusion analysis we need to be analyzing the intrusion the points uh that that were critical during the incident right so
the correct way to move forward is not just responding to the incident but actually learning about the adversary
automatically
so everything is set up uh by humans and humans make errors schematic examples for example um there is a pdp path
similarly
um
or
um
sophisticated
similarly
so moving forward
so these are some of uh the the activity clusters that we have developed over time against several several intrusions that we have um analyzed this may you can uh see very clearly certain intrusions overlap with each other
all right this activity group a is working with this activity group so there is something going in the background so now when we move forward from clustering intrusions we see what the benefits of this intrusion analysis are cyber threat intelligence intelligence generated
right so when you start clustering intrusions when you clock start clustering those activity groups understanding develop infrastructure activity infrastructures
you can even drive your own counter intelligence operations you can drive your own counter offensive operations you can once you have
there was a nation state backed group nation state
[Music]
[Music]
so once you have performed intrusion analysis you can start uh hunting you can start hunting over the internet or inside your organization and
i think he might have connectivity issues did we last time looks like yeah it looks like we lost awesome so maybe uh hassan do you want to continue where he left
so uh i guess we have talked about strengthening our clusters of characteristics
and it goes beyond their operations and then we actually try their movements on the internet on the open internet and the dark web and other sources of intelligence and we'll see how these are uh basically adversaries they operate how many operations go again beyond their technical
okay so um so here we have a case study uh that is related to team pkg uh this this is an activity group that we have been tracking um
and they are actually working in the indian interests and they are targeting pakistan since at least 2019. inclusion analysis performed gonna start here during the incident response so we figured out some phone numbers some ip addresses and we figured out that in fact they were using birth suit during uh the intrusion command information this is very helpful in understanding how we can actually uh start exploiting uh the these artifacts that we collect collected from the incident response once we start exploiting uh these we we can actually find remarkable findings against
um
state sponsored group just sold motorists to conduct espionage campaigns nk operations they've been running since at least 2012 zinco harmony actively start can basically track in a start current in 2019 and we've continued uh our intrusion analysis efforts against them campaigns intent as in the motive of their campaigns in order to steal information exfiltrate
again
fields or indicators like the e-tag values yeah domain registrars yeah here
foreign [Music]
future defenses okay proactively detect gonna start getting it then you can actually uh get you could say live updates on on how this campaign is being carried out the campaign
you can take a look at uh some work you've done in the past for example left hammer infrastructure tracks this is basically on showdown pakistan myself found out a few uh of their infrastructure domains our domains are hardcave or we basically indicated that just now for example the date there's a infrastructure last update was on 30th first december and second december right but you can see our efforts on uh basically exposing their intel for exposing intel against
and we use that to again re-exploit that data again correlate information
using that you can basically retro
maybe even fully undetectable
using that
we want to generate intelligence we want to um be proactive and have an edge over uh the the threat activity groups expertise
uh certain hardening techniques yeah uh having
[Music]
so what is actually uh causing this to happen your financial security
um
a different job institutions here which are related to cyber security maybe they can have internship programs
[Music]
[Music]
[Music]
actually first question is what is the difference between static and dynamic analysis
dynamic analysis and then advanced dynamic and static analysis thank you
dynamic analysis
thank you our next question is social engineering helpful for intrusion analysis and identifying group of hackers or attackers okay
engineering
you know you you talked about the infrastructure to understand the first sector the tdp is most important than ioc you know your iocs are basically short-lived ioc is url domain they will take down maybe after one day today that is gone you know they will not use that linking more focus on ttp is like what do you think about that like now we know the ransomware detectors they are using the ransomware service like a rest service you know that is available someone is hosting that platform or malware and you know you hire that service you know attack someone you know get the ransom share your royalty with them and you know you go away with that
one thing okay this sentence was like we talked about continuing somewhere we talked about ryuk and
you know hosted infrastructure or shared infrastructure okay so past name we have seen uh a couple of attacks
uh the flow logs over the internet right um internet may there are certain uh vendors that provide this visibility they give you flow logs they can even tell you uh that this certain instruction infrastructure was being um run by or being operated by a certain eyepiece or usually observed adversities either they come with
that is using this infrastructure which which does not actually belong to this adversity thank you so much uh we have couple of questions actually still coming through discord if you can just hop over and discard you know respond to these questions especially i think just i would say like the professionals are students they want to ask more they want to understand more about malware lessons what are the tools what are the techniques you know they can use and i would say like maybe guide them about the journey as well you know how you can start with the basics as as you know on the cfv panel and discuss your basic should be right if you are talking about the static
analysis and then you are moving to the next to the dynamic analysis you know and that going in the deeper deeper level as well so what are the core skills you should be you know developing as well so thank you so much for your time today and uh yep if you can just respond back thank you for having us [Music]