Red and Blue Ping Pong: Living Off the Land in Windows Attack and Defense

Show transcript [en]
all right we're just gonna get started here this is red and blue ping pong I'm Anton so in this talk we're gonna go over who we are and then we're gonna just briefly talk about Windows for attacking and windows were defending and then we're gonna get into the meaty part the the demo and then just go over some worthwhile dimensions so uh we didn't really figure out who's who that's true yeah well hi everyone thank you so much for having us here it's a real honor to be able to present to you guys thank you to all the speakers before my name is Lee Kagan I'm from red-black security here in Toronto I go by at invokes rec I
on the Twitter's and I kind of spend my time focusing on adversary systems intrusion SATs that kind of stuff and really focusing in mainly on Windows enterprises Active Directory windows things mainly and introduce yourself man I'm Anton I work at the equitable life insurance in Waterloo my Twitter handles Anton love's DnB if I knew that I would be announcing my Twitter handle like this there's so many people I would have picked a better Twitter handle and I'm just a security general generalist focusing on the defensive end of things so uh what we're gonna do is is kind of walk you guys through something called living off the land in terms of windows attack and defense living off the land
is really a term that was coined I think a few years ago I really hope I'm quoting this right by Matthew graver and Chris Campbell this idea of you know Windows environments tend to provide you all the stuff you could possibly want for attacking and for defending and this idea of the just staying natives you know dropping the kit dropping the big Kali Linux when you don't really need it and just using what's there to your advantage so like I said Microsoft really provides in that space not just for defense but for attackers I mean it gives you everything you could possibly want to weaponize so this idea of living off the land really is is
it's so beneficial from not just trying to emulate anything specific but but for helping to fly under the radar helps you learn a little bit more about Windows if you're in the attack space as well as the defense space and you know you've probably heard of things like PowerShell and and all that kind of stuff and we're just really skimming the surface here but PowerShell on its own which which is you know been sort of the buzz for a while now it's great because it allows you to interact with the dotnet framework win32 API all this kind of fun stuff you have WMI you have sim CI m windows powershell remoting Active Directory as we heard about earlier
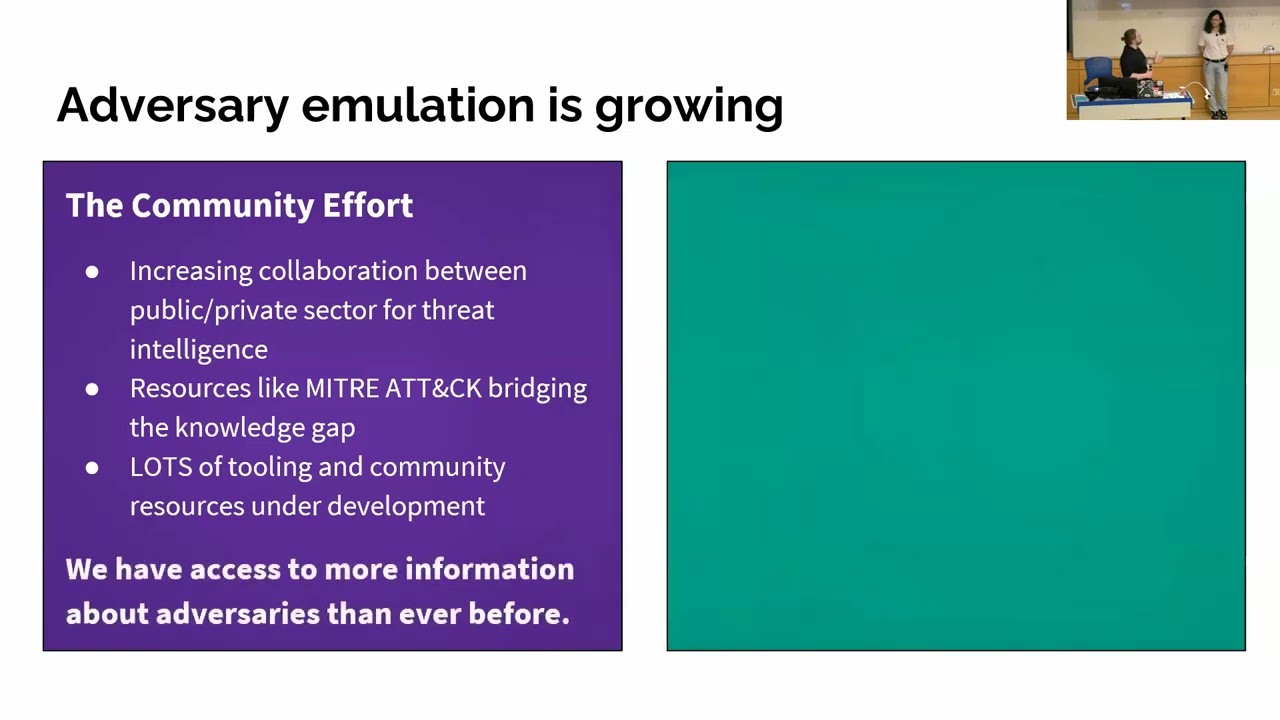
which just loves to tell you all about itself so it's really handy for an attacker and then you also have this the space of the trusted things so if anyone's been following the work of people like sub T Casey Smith or enigma o x3 who was Matt Nelson he's you know mister bypass UAC and all this kind of fun stuff these trusted things is really what's so great to help abused because if the trust is there we get to hijack it and use it for evil stuff and then finally another great thing that really helps with this idea of living off the land is the miter attack framework if you haven't been exposed to it yet I
highly suggest you go out and take a look at it's absolutely fantastic it's early and it's its inception but it's it's so handy especially for the defense people to to really understand this categorical tradecraft perspective of attackers so I'm also we're also gonna try and go really quick to get through this stuff and get over the demo which is like 99% not gonna work but while we're at it what I wanted to show was you know was just some some super basic examples of things you can do with PowerShell and WMI and commandlets doesn't really get any more basic than this so what you're looking at here is everything done inside of a power shell prompt calling WMI via
powershell commandlets so at the top line there I'm asking for the installed antivirus not a big deal right might be an admin want to do the same thing so we say get W my object the class I want you to ask is uh the or sorry the the namespace in the root security security center to class antivirus product just show me the name alright not a big deal next one down I'm doing the same thing for the operating system right tell me the OS I'd like the build number someone's so forth and then finally show me the CPU information why does this matter how is this an attack it's not these are baked in right they're there
because they wanted people to use them specifically like an admin something I like to say every now and then is what's the difference between an administrator an attacker is intention that's all it is right if the commands are there you might be using because I want to know what the OS version is I might be using it because I'm trying to target a specific OS version so you put these three things together they kind of sing to me as the beginner steps up like a checker script you might have in your malware right that last one is checking for cores it's like a really poor person's version of a ant EVM check you know if the computer has one or two
cores chances are it's not a real computer but this stuff's baked in right it's all there and again just skimming the surface you can ask for so much information from from PowerShell and and and interacting with it to expand that a little bit more here's using PowerShell to interact with the dotnet framework and basically what I'm doing is saying I would like to know about this domain so if you've never seen interaction with the dotnet framework before it really it's the dot system dot directory services dot active directory dot so on and so forth but that simple one-liner gives you a wealth of information we got the forest rim the domain controllers if there's more than one they would be in
that curly brace or if there's child domains the forest function level we get the PDC the primary domain controller the one you probably want to go after as you get this awesome amount of information just off this one baked in command and in order at the bottom there is using something called a DSi what's called a type accelerator and in this it's just a fancy way of saying show me all the organizational units I'm really only interested in the canonical name of them and it spits this all out for you at the end called surface lab I'm on my barely performing surface pro here so we got surface lab desktop surface lost surface lab standard users so on and so
forth and then finally just another basic example is something called PowerShell remoting which is done over win RM which is a soap and it's it's so awesome and not administrative way of doing remote work but also for an attacker and one of the reasons I love it is if you see at the top I'm desktop one I start a new PS session on the domain controller and then I enter that session reminds me a lot of meterpreter which is something I kinda always loved about when I REM like session 1 spawned go into session 1 and do some stuff and in spawn session or and go into that session to do some funky stuff it also has some I don't
want to say anti forensics but it has some some headaches when RM can cause for blue team's so what I just wanted to show here was super basic examples of things that exist on a Windows system that have weaponized give you a lot of leverage right they give you a lot of opportunity to move around and query the local system query remote systems interact with other stuff the domain controller so on and so forth and I think Anton's gonna take over from here and show far more interesting things thank you right so just like Windows provides a lot of things for attacking it also provides a lot of things for defending as well the cats not included
with Windows but it's there so some of the things that Windows provides system on device card various gpo's newer operating systems themselves are inherently more secure ata and ATP are also big ones and you you as well because you know your network hopefully better than the attacker and you know where your weak spots are so let's just walk through some of these in action this guy Lee mentioned sub T Casey Smith so he basically took maybe cats and made it into a jscript format so the screenshot here is showing maybe cats being run through C script dot exe so not your standard maybe cats dot exe at all so it's pretty stealthy on the right-hand side DC has a small rural
catching that L SAS was accessed by C script so that should throw up huge red flags for you in a similar vein this is the maquettes same version just run with PowerShell instead and like the same slide system on happily shows you hear that PowerShell accessed the else last process hope that again McGregor fog the granddaddy of defense's device guard device guard is magical for defending window systems the top screenshot there showing all kinds of shenanigans going on you have calc being injected into the running putty process you have unsigned code putty that exe running happily and at the bottom this is a system with the vise guard so PowerShell is not running and constraint
language mode so no more putty tat exe it's not signed but allowed to run you can't you can't call the API is required to do that anymore and on the little screenshot there with Twitter I don't know if you can read that but that's basically Matt great we're dropping expert knowledge as usual saying that you can either keep writing so spawn rules to detect this kind of stuff or you can just implement device guard and yeah one last thing before we get into the actual demo this is a GPO that jessyca pain always tweets about and this is doing two things one it's preventing local accounts for from performing a type 3 network login so if
you have a bunch of systems and the admin password the local admin password is the same for all of them this will prevent lateral movement across those systems so the local account can only be used locally it's also preventing domain admins from authenticating to lower trusted systems so domain admin you can't log in to a server that's not a domain controller or a workstation so their credentials their tickets their hashes they don't get stored there and this screenshot there is just showing you crap crack not exact running with just two systems there the username password is the same and you can see the status logon type not on that hook so big nope and yeah we get
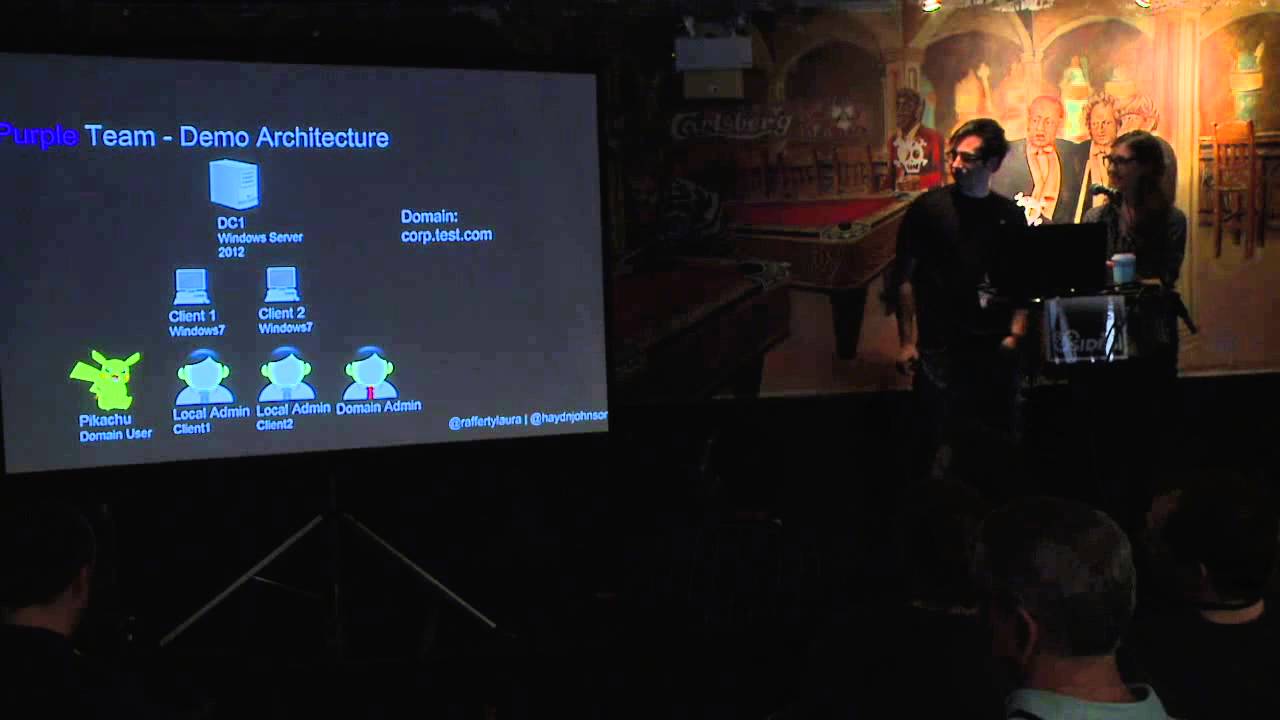
into the demo so we're about to show you guys and again mm-hmm is it's a super basic setup and we really wanted to keep this very simple for you so it's just gonna be a Windows 10 Enterprise desktop we're sort of doing the assumed for each thing somebody dropped something nasty on the on the machine and I'm I'm gonna run through about like seven or eight different attacks I'm gonna execute a payload be a PowerShell in memory will do some process injection drop me me cats actually the application whitelist bypass isn't needed because we don't have enforced persistent a registry persist via WMI some powershell encoded commands malware that has stolen the signature from a trusted binary and
applied it to itself as well as unmanaged powershell in case someone has removed the ability for powershell to run you can put it back on the system and then a little script that anton put together is gonna catch all of this stuff and i think one of the ironies to this is is a you know you just wrote a basic powershell script and i'm gonna be calling all this stuff down through cobalt strike which is you know four thousand dollars and he's catching it with a script and so it's really cool the stuff that you can do with windows it's already there free i think the only additive is sis mon that's it and with
that being so so sorry yeah his he's gonna catch injected threads look at the parent-child relationships that are sort of suspect suspect command-line arguments authentic code mismatches things powershell running anything encoded stuff that's trying to touch l SAS unmanaged powershell basically the the blue equivalent to all the different attacks I'm about to demonstrate for you guys and with that let's dig right into it okay everyone pray for me right now pretty promotion what's up just out of curiosity does anyone actually run this mod in production what about the Vice guard just curious about that too
meanwhile ask questions did everyone hear that question okay yeah the question was would he would he do with all the data that's a great question the good thing about this one is that the configuration is very granular so I'll show you if the demo works you'll see a bunch of stuff and you can see that you can filter out certain noisy things from this mahn config it does go in the sim yep yep any other questions while we're waiting okay we're good okay space we're gonna start with we just launched the PowerShell command on oh yeah that would help cool I don't get rid of that let's close it down Kiel okay sorry guys there we go so we have this infected
machine that's the red and lightning if that wasn't obvious and so he was just PowerShell injected into memory via command line download cradle thank you sir and first couple things we're gonna do is I think we're gonna start with the process injection space what I'm going to do is look at running processes which I'm gonna do like this sorry the font is so small in here l right sleep time yeah so that you guys don't have to wait 60 seconds between every command okay three should be good we're gonna inject another agent into a process that probably would have no business launching a command prompt which is gonna be onedrive just for the hell of
it let's get those guys back how we doing oh cool we can all just hang here for like 35 seconds so first I'm gonna inject in this new process spawn a new agent use that process of being inside of onedrive dot exe to open a command prompt that's going to trigger a rule that we're gonna catch when this thing checks in and then from there I'm just gonna do all that stuff you saw on the on this slide of different attacks isn't dead air awesome Swift on Security's awesome really really good keeps it keeps getting updated to with a nice real it's really really good there's nothing won from a I want to say dfi or
hunter or something like that I can't really remember just make sure you test it because when I ran it it didn't find certain things that were in the config cuz I think she did it for her environment so certain registry keys are not set exactly the way they would be on all system so tested person okay so there we go new shell this is living inside of onedrive so I'm just gonna say you know through a shell prompt run command dot exe that's going to trigger one of our rule Arina catch and then we'll go back to this guy and oh no I didn't start inside of the right directory yep oh no we're gonna okay I'm gonna see de attacks no
nope okay so I don't you gotta try this one it's the best to get little blurry there guys I'm just gonna run through these four things here first say I'm gonna launch this bad Sigma X see this is a piece of malware and it's been signed with the Microsoft signing certificate from TCP view from the SIS internal scope and that'll spawn another shell which is horrible tradecraft and then after that we're going to use C script to launch our Mimi cat's JavaScript version do that jay-z said it's not right Jay yes there we go and then finally this NPS exe from benter is a not powershell basically powershell has been removed scuttled functionality the automation dll to be put back in is
really you guys are far sharper than me by the way don't have like four beers before talk just just FYI you know and finally not powershell and it's gonna allow me to use basic powershell commandlets with it so I'm just gonna say get process and I'm also not waiting for the output from all of this stuff just to breeze through it really quickly because I know we're running short and then finally let's just do in memory me me me cats like that's a little sweet for getting them oh the run kit yeah okay so I'm just gonna drop a couple forms of persistence here besides to you besides do commands there we go let's wait I want to type all this out perfect
okay so this is going to use a PowerShell to add a registry key and then finally WMI persistence using what's called WMI permanent event subscriptions now it's kind of a cool technique shell powershell EP bypass stood up and W my persist dot PS one cool thing that we just did there is that registry key is going to launch notepad whenever the user logs back in and the WMI persistence is going to watch for notepad as a process being created and any time it sees that process at a launch calculator to simulating the bad thing basically and I think that's all of the attacks now let's see if we can catch these suckers
for me to set it up person the Passover to how we you know we don't talk good timing so stranger things to was good sorry it's a little laggy folks I apologize yes we know thank you invoke besides tio
respond yeah so I'll just start walking you guys to the script of what it's actually looking for basically the script is running first it's running a PowerShell script called get injected thread it was written by Jerry doc Benton and it what it does is it searches processes and it goes into those processes and memory and sees which one had something injected to it so when Lee did his inject into one drive that script will hopefully find that the rest of the script basically just combs through sis monologues and finds odd stuff like CMD running from one drive that shouldn't happen you have PowerShell DLL is loaded by something that's not PowerShell that shouldn't happen either you have C
script accessing your else ass again shouldn't happen okay let's run this sucker let's hope this works that's me it's supposed to be windy so that's that's the first step it's delicious crab and they inject the threads that I just talked about and now it's looking for a suspect process relationships and breaking the gods that is super weird yeah let's take a look at the report we might still have an old report that we could show you again
desktop we're almost at the end of the time so that works wow this super let me try this from while I'm just gonna run the script in one more time guys what's that it's always none were hard as none what was the actual winner oh maybe that could be one yeah where modules
get injected thread and then we want to get win event I thought he did but maybe I didn't and then don't be shitty well it does work sometimes and then it catches on the idea is to have this stuff at your sin obviously you're not gonna be doing this for like thousands of systems but totally it'll work this time all right well I'm really sorry about that guys but uh it worked down and downstairs for let's see what did actually spit out well when it does work it does this right so this is kind of the stuff it would have caught but I sorry it didn't work we're gonna wrap this up now basically this is not
production ready if you haven't figured that part out yet but it works when we do it but it's something we're gonna put on github and tweak obviously and get it to get us something we can share the idea really behind us is like this is not something that's supposed to solve your problems it's just showing how with you know get win event data get injected threads you can go look at the windows event logs from system on and pull out all of this stuff WMI activity beaconing all that kind of stuff it does work trust me yeah sorry sorry guys and
well do that actually I think yes yeah cool thanks guys sorry about that thank you [Applause]