Don't Turn Your Back on Ransomware
Show transcript [en]
the floor is all mine now my friend yep excellent well well hi everyone my name is Eric gaskus um yeah so pity uh so um sorry I couldn't make it to Newcastle Castle would have been great uh but I will know it's just uh just what it is and we have to deal with it and we're going to make the best from it right okay so I'm presenting from lemon shark here which is in Holland um consultant and I've been a subject matter expert for a couple of security topics like for instance same sock probably TV fan testing compliance those kind of things I like many different things as you can see I'm also certified
in a couple of these area and today we're going to talk about ransomware and you probably know what it is seeing that my slide will move and it will okay so what we're going to expect today from this talk I'm going to show some history about the rents we're going to show you some ransomware samples uh obviously I'm going to do a demonstration and after that I'm going to show you how you can prepare for such an attack now ransomware you probably know what it is and I would like to point out it's still here and it's uh bad as ever it's on the attacks are only increasing now but actually what could be the
definition uh if you look to the Spore guy here it's called kept hostage and only being released after Ransom is paid now usually this is uh done in a digital way it's a digital hostage situation and the ransom is usually paid out in Bitcoin okay and how is that hostage situation taking place uh that is being done by using encryption and in this example right here I'm showing a sample about asymmet encryption so the data uh is encrypted with a public key and can be decrypted with a privacy you're going to use two keys in order to to encrypt it now what the attacker does because asymmetric encryption um will slow things down right and somatic
encryption is typically faster to do so the encryption attacker will first encrypt everything with a somatic algorithm and that schematic key will be encrypted with an asymmetic uh algorithm and during that encryption the private key has been used to decrypt everything will stay on the attack server so the victim will not get access to it yeah so looking at some ransomware history um doing um the time there were a lot of friends from their species popped up and they would take too much time to uh to handle them all but before there was uh the ransomware as we all know it now uh with a ransomware note um with a message in order to pay with
with Bitcoins you know all they can go into a tour site and do the negotiation and stuff before that that was a different kind of ransomware it was invented by Joe's pop uh it was I think it was in the 80s he built his own software and in order to make use of the software um the computer actually install the software and reboot it afterwards and then the software was locked and you need to when you want to release it you need to pay the guy with money you put in envelopes and do better man well that was the first type of range wherever the guy got arrested eventually and the encryption was broken and there was also the non-digital
ransomware varieties as we know the screen Locker so you got a nice message popping up for something awful happens like this could be from the local authorities or the police and European um included in some kind of criminal activity some Panic measures like that and in order to pay the fine you can get rid of that um charge something like that will very fake obviously but actually some people fall for it and it's well it was also a lucrative way in order to uh to handle with extortion um then the digital version started to appear we had for instance GP code using RSI encryption and crypto Locker was the first one ever using Bitcoin as a
payment and making also use of the Zeus banking Trojan um and after that uh the the more advanced type uh rental man also started to appear making use also lateral Movement by SMB exportation the things that you have seen probably with uh want to cry and even more advanced type 2 attacks that means that also making use of exfiltration or sensitive software prefer sensitive information and destroying backups um like for instance a Lexus dollar who attacked Microsoft this year in March and they were even able to extract some of the source code and there were also some incidents here in Holland one with media Mark for instance uh done by the hive uh very aggressive ransomware group will
also attack North portal even they won't uh move away from that as well and we had a attack on cassia which is a supply chain attack see a software to manage sector directory and via the vulnerability uh on the victim system they moved in Via consider software and were able to uh encrypt the victims the the clients managed by by XC and for some reason also the backstopped because the decision the correction key was disclosed uh to give an other idea about the impacts and the colonial pipeline was attacked in April by Clopper and somewhere and the colonial pipeline is used to fuel the planes and because of the reason and there was no gas anymore able
to fill the planes then they need to keep kept on the ground in Washington um and there are some rumors that a ransomware attack costs human casualty and probably caused by raik in one of these American hospitals so just to get an idea about the impact and if you see here at the diagram on the right you can see here what in that period uh what kind of ransomware species were were active okay let's move on to the next section so if you combine all the elements in the ransomware attack like the wondering encryption I don't want to assuming the extortion and one who is looking uh to get in touch with a victim when you
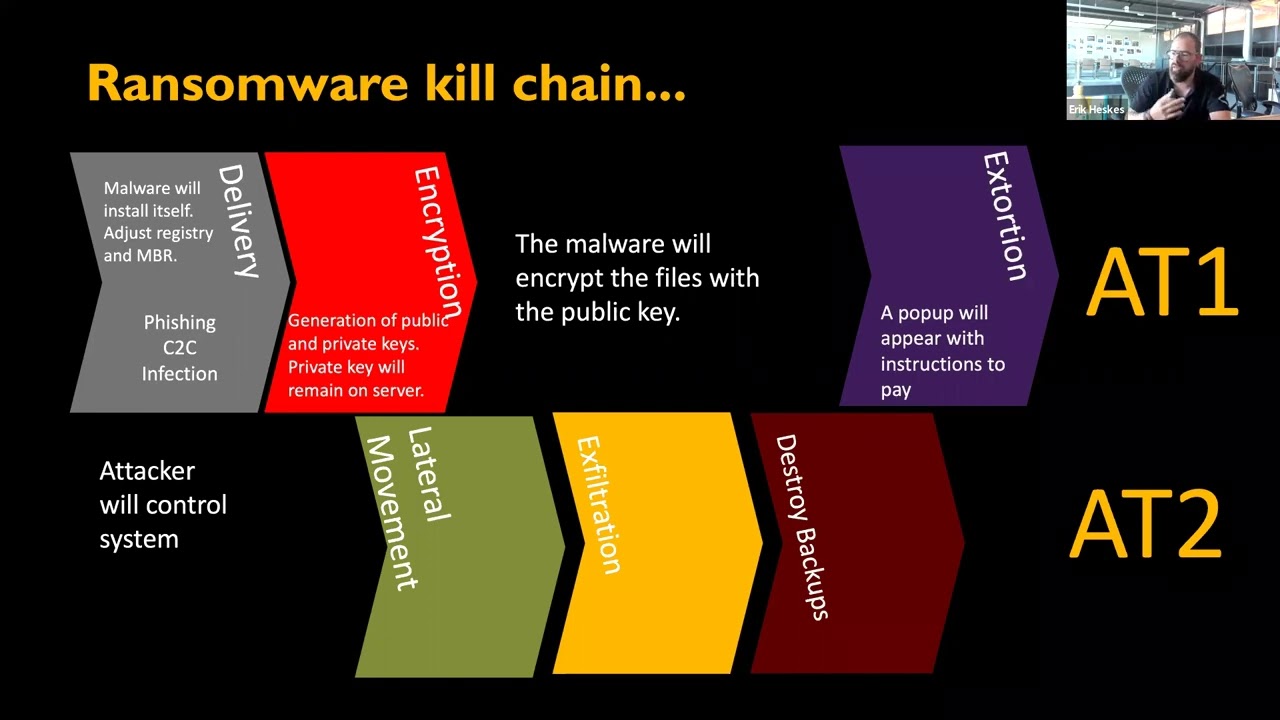
combine all these elements put it in a big bowl and stir it you have a ransomware as a service and that is a very lucrative way of doing business and there is no single actor it is a combination it is an ecosystem of services and what they also do is exchange information with other resume groups they combine and they learn from each other they buy things from each other they grow also in terms of knowledge and making even more money okay now we're looking at a ransomware kill chain and it is quite similar as a cyber kill chain so usually it starts with a delivery it could be a phishing email from ability or a Driveline
download then the malware will install itself if the attacker has a foothold on that system um the data will be encrypted and eventually the ransomware node is Left Behind with instructions to pay now if this happens on a single workstation server or network that storage device we call that an attack type one next to that your attacker is also capable of moving to other targets the lateral movement doing exfiltration of sensitive information in order to put some extra effort to make the victim pay the ransom and destroy the backups to prevent the victim from going back to a previous uh known good State now we call this an attack type 2. okay so what we're going to do today is we're
going to um perform one of these ransomware demonstration where we're going to send victim we're going to send him a phishing email in that way providing footholds we dropped the malware and then when we have foothole we're going to look for other systems on the network we're going to look for credentials and see if there is a way for us to move lateral to the main controller and then encrypt the domain controller to infected with rent somewhere so I would rather relax and watch the show as we're going to start the demonstration by sending the fishing email execute payload and establish foothold so first we're going to send the phishing email and done in a simple script
[Music]
notice are also going to include some social engineering like um if the victim could expect an email from someone who is sending a presentation something that way Dooms are extra knowledge in order to uh to entice that victim to click on a link sonar email is has entered the mailbox and the victim is going to click on the attachment so obviously it's a PowerPoint presentation and the PowerPoint rotation holds a macro fires which will do the rest of the infection foreign
trusted sender so he's going to enable the content very smart thing to do and how the microfires and the payload has started and in the background already a listener was started and now the uh attacker as a foothold on that system all the victim so I'm not using any obfuscation anything like this here to make this as transparent as possible so you can really see what's what's happening okay um well in the previous example macro files was being used doesn't need uh to be per se you can also there was also a vulnerability lately with um Microsoft diagnostic tools the for linear attack and there's also a way to provide foothold to make use of zero day vulnerability
and if it's not patched already then there's a risk an attacker could take advantage of that okay this was just as an extra example you're going to move to the next example okay so now we have foothold and the system the system has been affected uh with malware we're going to look for credentials and we're going to look for anything else um valuable Target on the network so uh we're going to start by dropping sharp out the sharp pound is basically mapping out the entire active directory environment by importing the the Json file you get from the from the sharp out software and the the Json file can be important important in the diagram to
to draw the the map actually so there's no administrator access necessary for this kind of attack so it's good to start with this
so now the attacker is able to see the shortest path to uh to the main controller and to the to the service account which is maybe attached to to Administration rights and this is what the attacker wants right okay now we're going to look for credentials on that system and to be able to do that we're going to start responded our responder is just listening for any kind of authentication events on the network
foreign well I could just uh browse for a network share it doesn't need to be the network share is present so even when the victim is going to make a typo the event is being captured being senior authentication as you can see here there is a hash file intercepted and the hash file has been cracked and we have to use spots for it yes I'm going to shut this thing down okay so now we have user accounts we're going to look for maybe some credentials with a higher privileged account and there is a feature on a web station you can for instance enable all the logo it's a very handy feature but it also um if you type in the the password
without encryption it can be read directly from the registry so in this example here uh well we're actually got a auto log on feature enabled and we therefore we got local admin password doesn't have very often I must admit but there are some cases when this happens okay so next phase we're going to look into lateral movements uh we want to do some elevation and create a ticket which we can use the golden ticket we can use to make a remote connection to the domain control and eventually drop the malware and infected with ransomware foreign so first we need to elevate our shell we have still user access in our existing metal exploit shells and we want to
upgrade it to uh to an admin shell
and that's we uh what we're going to do now
okay so now we've got an Administration shell and basically now we can do anything we want here next we need a golden ticket to log on to the domain controller now we already have we found some credentials so we can use those to to dump even more hashes and make combinations with ashes and tickets
so we have ad here we're going to combine this by using minicats and mini cats will create a ticket for us
and that's basically how that goes now the only thing now we do need to do now is make a remote connection to the domain controller um drop them all away and execute
foreign
and as you can see with a Minecraft trailer is now encrypted the ransomware node is right there it's encrypted with grand crap ransomware
all right now we've got an uh renssware incident what are we going to do now well basically when you have an incident like this uh you want to have as much as information you are able to get your hands on to start a new investigation to be able to uh react in time in order to mitigate the rest of the attack okay so how are we going to get the information well in a traditional scene as you can see here uh we gather all the log files from all the parameter devices so for instance the firewall proxy server are all sending their logs to one logging server and a logging server is aggregating all that information
and you can config figure that with correlation rules so you can alert on the information happening in in that log files and we're going to look through the logs for any evidence of ransomware also well known as threat hunting so it's usually a lot of work to configure all these correlation rules and in the end you're going to look like this okay then um for the first type of evidence of ransomware I want to look for the resume notes you can do a simple search on these log files and look for cryptic crypto txt and see we have found a couple of these and it could be interesting for our the rest of our investigation
so next um other kinds of indicators of attack could be that the event lock has been cleared obviously uh very good information to look for in our example we use the PowerPoint file we can also provide that one in the search and all of the malicious tools and attacker will use like for instance mimikatz sharkhound.xc those things are also interesting to include in your threat hunting activities uh other indicators of attack and not mentioned in the slide here uh well uh before an attacker will eventually launch the the infection uh it might be handy if all kinds of defensive mechanisms are being disabled like for instance real-time protection and disabling those capabilities will also cause evidence which you can use uh
in a search through your log files for your investigation okay so what we've been doing so far we have started a ransomware simulation attack you can see that as a red team exercise uh red team exercise is doing an offensive game and try to stay undetected so usually you also use some kind of confiscation I didn't do it because I wanted to be as transparent as possible so you are able to see what's really happening and the blue team will try to detect it all the um uh attacks and be able to mitigate and what else you can do is for instance you can also um do a tabletop exercise which is basically uh more or less the same but
then in theory by drawing uh scenarios and see what can go wrong in those scenarios okay so basically entails everything I've showed you in the demonstration so uh obviously uh you can have your EDR you can have all kinds of uh written down procedures uh you can be very cyber resilient but they're also always our chances uh that uh backup has been overwritten with malware could be a logic bomb that has been activated after a certain time it will then still destroy all of your backups uh well people make mistakes obviously as you can see here in this meme from cyber security app you have the best defense mechanism ever but a user clicks on an email and then you
have an incident so these risks still can happen obviously so awareness is always very important to uh to include that in your strategy um usually doing a substipan of attack there is usually there's Panic maybe you don't have access to the data center you need to to call someone and the phone number changed all these mistakes in written procedures can lead to even more problems uh so we just have to deal uh with these and then malware will eventually run on workstations well if we know it we can prepare for it right and the vulnerabilities will exploit it just as the zero day with Felina of course there is this Silver Bullet uh everyone uses which is multi-factor
authentication and I must admit uh in the most of advisors I've given after a ransomware exercise this was one of the outcomes uh but then I need to point out that okay um very good advice but you what if um you have an on-premise environment and the advice is to synchronize all your high privileges accounts to the cloud and make use of for instance Azure MFA would that then be a very good idea to do not sure about that so MFA sure but when applicable I would say um that brings us now to my key takeaways um about backups make sure these are right protected make sure the when you have access to active directory
environments the backups are separated from active directory I will obviously practice cyber resilience uh patching make sure the systems are up to date uh perform your exercises in order to see where the weak points are uh what about Cloud I haven't talked much about Cloud yet but Cloud can be much as they occurs as a gift would say a gift because Cloud provides all kind of security tools you can use uh to benefit from um extra evidence you can use in an investigation for instance when dealing with ransomware but make sure when using a public Cloud uh what you're going to to store over there and how you're going to do that with going to face multiple challenges
um about traditional scene I I showed you what you can do using certain kind of searches in your uh threat hunting but there's also something is just endpoint detection and response um it hasn't been uh here for a long time already so first it was just nice to have and now it's even Unthinkable to to don't to don't have it includes also um machine learning kind of activities to be able to see where the threats are obviously uh proper Network segmentation preventing from lateral movement from happening um when you experience an attack make sure you document everything so you have the plan ready for next attack and just like I showed you like the meme
from cyber security Hub um one single Arrow or one user clicked on email we will sufficient to foreign series incidents I would really not just bet on MFA or any other Silver Bullet but just combine all these strategies and apply defense in depth so and that was it and thank you very much for having me and if there are any questions I'm happy to answer them thank you very much