Adversary Emulation for Everyone!
Show original YouTube description
Show transcript [en]
thanks there you go hey hey folks welcome welcome first thing I want to say thank you so much for being here everybody it's a room full of colleagues mentors mentees students a lot of people that I know a lot of people that I don't new friends super excited to be here um thank you everybody for the uh the invite the attendance all this we're ecstatic to be here so um today we want to talk a little bit about adversary emulation something a little bit Buzz wordy a little bit trendy something you might have heard about recently but maybe you don't know a lot about and how you can get started with it for free I
think there's a big misconception in the realm of security that when you start getting into these deep technical Realms you yourself need to be deeply technical or it's tremendously expensive and the reality is it's not and so today we've got a talk to introduce some of the concepts around what is adversary emulation as well as how you can get started doing this at home for free let's Dive Right In we have two chapters to cover today the first being understanding adversary emulation we want to kind of set the Baseline here make sure everybody's on the same page so let's start with a pretty familiar quote you've probably seen this before right sunu if you know
the enemy and you know yourself you need not fear the result of a 100 Battles really important guys to understand the enemy so that you can inform your defenses your strategy right this is not a New Concept this has gone back as far as history itself so why would we stop now when it comes to cyber let's talk about it so when we talk about adversary emulation what is it really in Industry I'd like to think that this really refers to a broad security discipline where we're replicating adversary behaviors to validate our cyber defenses against Real World threats so we're looking at what kind of threats do we actually face and how good are we at
responding to them right adversary emulation at its core though sounds really really lofty it's kind of difficult to understand it can actually be broken down into a pretty simple process to get you started the first being we're going to start with cyber threat intelligence anybody heard that term before CTI cyber threat Intelligence show a hands so we're familiar we're talking about actionable intelligence things that tell us about things that we can do in this realm we want to understand how threat actors are behaving what kind of activities are they conducting when they're doing their delicious things we want to get intelligence that lets us take action and build defenses around it in the case of adversary emulation we
might want to take that a slightly different route and instead use that to build capabilities so for testing purposes call it detection engineering call it security testing validation whatever you want to call it we're going to take that actionable CTI the stuff that tells us how threat actors are behaving and we're going to translate that into a capability ility that we have that we can run a test with then we're going to test and why are we testing well commonly to identify gaps kind of a high level goal we might want to find out where are we well prepared where are we well equipped to deal with the threats that we might face but we
also might want to know where are we not currently well prepared so that we can patch that up so really adversary emulation at its core comes down to these three steps collect your CTI understand your adversary build your capability out to test according to that CTI replicate your adversary behaviors and then execute your tests in whatever context you need whether it's for the detection engineering the hunting whatever you want to do testing your tools testing your vendors go for it now something you guys might be familiar with anybody here heard of miter attack okay so lots of people familiar with this this is good miter attack is like the Periodic Table of bad guy behaviors okay that's how I like to
describe it I come from a analytical toxicology background so I think it's a good way to sum this up up on the slides here you're going to see there is a sprawling Matrix okay I don't want you to focus on that right now the point is it's really big there's a lot of information here you don't need to memorize this nobody does what you should know is that minor attack is a framework to help you bridge the gap on communicating on and understanding adversary behaviors and we can use this to inform our actionable cyber threat intelligence okay this is a great way to use standardized common language plain language to translate adversary behaviors into something that you or
other people at your workplace or for your student projects or whatever your use case is can use to again build your capabilities and do your testing right in the miter attack framework adversaries are broken down uh their behavior specifically into kind of three levels of categorization you have tactics techniques and proced procedures and you'll see that acronym commonly written as a TTP a TTP is used kind of interchangeably to describe one of those behaviors the highest level of this framework you have kind of the objectives the goals the very high order thinking of how an adversary is behaving so you'll see things like initial access or reconnaissance they're very summi of and they're meant to be kind of that top
level bucket where everything falls into one level lower you're going to have techniques right there's lots of different ways to crack an egg so if we're talking about you know dumping passwords there's a ton of different ways to do it we want to be able to differentiate though how are we actually doing it so you know while you might have uh password dumping as a technique there are probably multiple ways to do it that's where procedures come into play and where you're talking about really the lowest level of the framework you're talking about the implementation how people are actually doing the thing if you understand a TTP you can probably build a pretty good capability to
replicate it in a Clos test environment which if you're using it for detection engineering or if you're using it for any of your internal use cases it's a pretty good starting point miter attack fantastic resource most importantly in the spirit of this talk this stuff is all super free I'll say it again it is completely free you can go online you can pull out the miter attack Navigator you can investigate dig deep I encourage you to take a look at this after the talk this could be a talk all in and of itself so spend some time here folks super cool as a related call out you might have seen the defend framework it is a related and
sort of corresponding library of countermeasures I'm not going to spend as much time on defend but as it's a I guess a relatively newer thing and not a lot of people are as familiar with it I encourage you take a look it's a great introduction to sort of the realm of the Cyber countermeasures and you know associating with the commonly understood miter attack let's talk a little bit about a case study um something that we had come in so I'm a manager of cyber defense at KPMG I see a lot of security testing come through onto my desk uh one of these things we had a client who came to us and a bit of a tizzy around the time
that Cony leaks happened anybody remember Cony leaks so Cony leaks there was a pretty big leak involving a lot of the information about how the cony ransomware group was operating at the time and uh notably a lot of information about how their sort of business worked uh was leaked also about how they conducted their operations so there was a ton of security advisories there was lots of sort of public Source or open source leaks um some of the documents were even translated anyway so we had a client who came to us and they said hey we're you know we know kti isn't operating more but we're really concerned about kind of the next generation of ransomware affiliate
groups and we want to understand how do our defenses really stack up to this are we prepared for if one of these guys comes after us and so we built a purple team exercise kind of on short notice so the goal was simply test and validate the client's defenses against ransomware operator ttps so we understand how ransomware groups work we want to figure out how well prepared are they to deal with them if one comes knocking in the end we actually had a pretty interesting test right so we found yeah a lot of it was uh detected or prevented but actually two key things kind of came up and it wouldn't have come up if we didn't actually do the
adversary behavior and simulate for one data exfiltration so we were able to highlight a pretty big gap in the client's infrastructure in terms of their DLP their data loss protection or data leakage protection um tooling didn't have any coverage as far as sensitive data goes so we were able to exfiltrate sensitive data out of the environment to like a mega uh folder which was kind of cool the other thing that we were able to highlight was actually a major misconfiguration with their EDR tool right so this is a client who they had a pretty decent security spend they had a good security stack in fact you know a leading EDR tool but it wasn't configured properly and so it was
monitoring Powershell for you know command inputs militia stuff that was fine but it wasn't monitoring CMD so we were able to execute the same data exfiltration test uh test case using the same malicious tool on CMD where it was blocked by the EDR in Powershell so if not for thinking like the adversary and understanding they might try this we would never have found that you know weird misconfiguration Gap in the security visibility into their or so to call back to Cony leaks you know one way that we did this we actually looked for some actionable CTI I mentioned there was leaks around the operator manuals and sort of how they did their stuff we kind of took that to
the next level and built an exercise themed around it so you can see looks like a spreadsheet I promise it's not death by spreadsheet it's not one of those presentations but we took those oper manuals and actually built out some full comprehensive capabilities this is one of our sort of internal reference testing sheets we took the operator manual line by line uh found a translated version of it and migrated it into a format where we were able to customize these commands and these tools and build this into a test case that we could run in the client's environment right so this is the real bad guys stuff this is what they're doing in a client
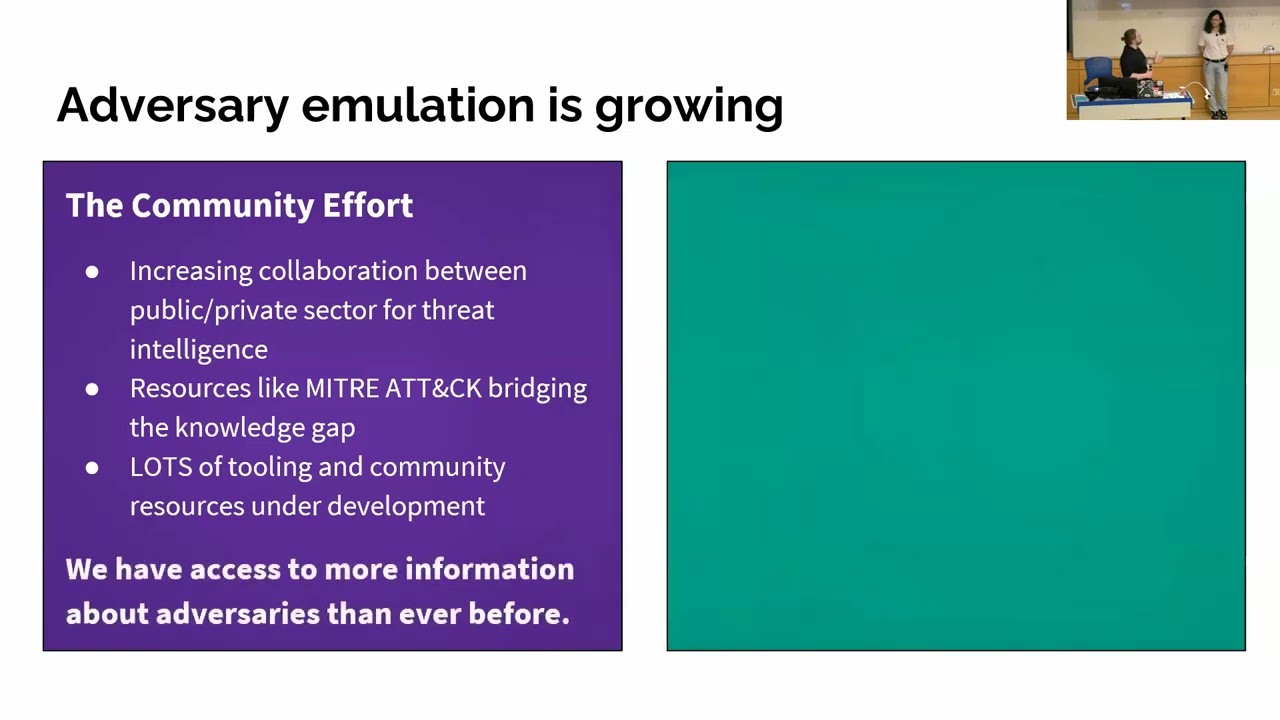
environment when they're in there so we took their literal manual turned turn it into an exercise that's adversary emulation right replicate their behavior in your context so you guys might be wondering now okay that's really cool fun purple team story haha but why should you care well I think the big thing is that adversary emulation is kind of growing right in two areas first being the community effort so there is a lot of Open Source resources a lot of community effort a lot of uh sort of industrywide support for purple teaming highly highly recommend that you dig in here because yeah there's a lot of support here for one we have a couple of things driving
this one being uh collaboration between public and private sector as far as threat intelligence goes you guys ever seen a cisa advisory um or you know an advisory from the csse here in Canada or anything like that these kinds of public sector private sector collaborations are increasingly common and we have lots of vendors here regionally even in Canada that are supporting these kinds of advisories and Publications to prevent the prolifer ation of you know ransomware and cyber crime and the like so that's one kind of driver here another thing is of course the resourcing right so miter attack longstanding I think it's actually it's attack con next week register it looks like it's going to be really cool
they're celebrating 10 years there are a lot of resources like miter attack that are now focused on adversary emulation they're Bridging the Gap the knowledge gap between sort of what you see as the dark arts and what everybody else is doing insecurity right and then beyond that it's not just knowledge it is tooling there is a wealth of Open Source and free tooling that is available to get you started so today you know in the spirit of this talk we're talking about how really we have more access to information about adversaries than ever before and it is entirely free so the other thing that I kind of want to touch on so maybe from a
management consulting lens working big four we work with a lot of financial institutions we work with a lot of small medium businesses we do a whole mad of clients there are some other pushes in the industry like for example regulatory involvement or you know client recognition in this case that are kind of driving adoption of adversary emulation as a practice or as kind of a goal a recent example of this anybody here familiar with the office of the superintendent of financial institutions osie here in Canada okay a lot of people raising their hands we like those guys maybe yeah we like them so osie recently published uh an intelligence Leed cyber resilience testing framework that was pretty heavily informed by CEST
and Tyber EU other existing regulatory Frameworks talking about augmented uh red teaming where you're using cyber threat intelligence to go above and beyond what you'd call conventional red teaming or pen testing and you're adding in a layer of realism right so they want us to be using information about our adversaries and the threats we Face to improve the realism and the efficacy of our testing we're also seeing increasing appetite at least in my client base around sort of the adoption of adverse imulation as a best practice right it's kind of being recognized as is innovative even though it's been around for a while as kind of a leading practice or something that now because they have the security maturity in the
organization they're well equipped to take on so there's a little bit more sort of client appetite there for sure I think another thing that has really kind of come into Focus recently as well is evaluating your service providers right so it's one thing to be looking at your tooling or your own capabilities as far as your security stack goes but we've had a lot of clients who've come in and said hey we're working with an mssp a managed security services provider of some sort and we want to understand what their capability really are if you run one of these tests in our environment are they going to pick up on it can they see what you're doing and you know what
are they going to catch what's going to slip through what do we need to prepare for so kind of another interesting uh topic area I guess in the age of services and as you know we kind of move in that direction there um another kind of I guess benefit is as far as a lot of these engagements and services are delivered they tend to be a little bit cheaper than what you might call sort of conventional testing conventional approaches because you're focused really only on you know a specific adversary or a specific set of objectives it is much more narrowly defined which means you can kind of keep costs a little bit lower as you're building and scoping
these exercises it does definitely help to uh keep this relatively inexpensive the bottom line is conventional approaches as far as pen testing and red teaming go they're not really cutting it anymore right we have all this information so why wouldn't we use it so again we've talked a little bit of the cost of this stuff you guys are wondering now I'm sure isn't this expensive right well the answer
no not really uh you can get started for free this is true I'm not lying we're actually going to show you how I'm going to hand things over to Christian here in a couple of minutes um I will say commercial tooling for this stuff definitely can be expensive but it's worth its while uh getting started for free today we're going to you know walk you through a little bit of a lab demo and actually we prepared a bit of a write up for you for how to build an adversary emulation home lab so hopefully you guys enjoy that I'll hand things over to Christian here to get started perfect thanks Todd all right so as Todd had mentioned we had gone
through all that and now you know now that we understand the context and the need for adversary emulation now you're asking how do I build one and that's what this part is going to be covering um and one of the things that um uh you know our friend sunzu is here to give us is that he who does not build the home lab shall lose his homeland keep in mind this may not be historically accurate not entirely sure but um so okay home lab requirements so one of the big spooky things with technology as it increases is that there's more demand for resources so sure if you're running it locally and in this case this is the one that we're
going to be running the infrastructure that we have off of which will just be run off of a virtual box VMware host we have two separate areas our corpet infrastructure which is going to have a Splunk and Debian server our Windows Server domain controller and a Windows 10 workstation so kind of like a small little uh corporate environment that we've set up and then on the other hand we've also set up our um deban C2 server and a k linkx virtual host so this seems like a lot especially if you have just maybe an okay laptop at home and you can't maybe use your work laptop so the thing is this is just maybe one of the
things that you're going to worry about as you start getting into it later you don't have to do anything this complex and in fact some people even have even more complex than that you can drop this down to pretty much just a Windows 10 workstation that can run Splunk and you honestly don't even need a a domain controller and then on top of that C2 server you can run all this off of your own Ken host so with that being said with just those two um PCS you can get as low as eight gigabytes of RAM probably just a decent Siz hard drive um and maybe even like a two core processor so kind of is anything you could do off
a random MacBook and even if you don't have a a laptop that still can run that a lot of cloud services are available uh you know never have they seen before before and on top of that is it's probably going to be a lot cheaper than buying yourself a new laptop so um in our case we're going to be running with at least 16 gigs of B of ram 250 SSD the reason why I recommend an SSD is hard drives don't like it when you run five machines at once I learned that the hard way when I was building this lab I think it took maybe like 10 minutes for the like our Debian server is entirely CLI
and it took like five 10 minutes to boot up then which I you know I never knew that it could go that but all right so moving on to the demo and we're going to pray that it does not break um one of the things that I want you guys to maybe take an opportunity to is take a picture or scan it we'll have this available later on our social media uh LinkedIn whatever when we show it at the end but this QR code will actually take you to Todd's um uh medium article where we talk about building the adversary emulation lab why are we not building it right now well Kelly Linux takes about
30 minutes alone to install so I don't think you guys want to sit here through lunch just waiting for you know a popup every five minutes so what we'll do is we'll just quickly um share our screen there and get all that ready let me just uh change our
display all right perfect and you guys are able to see that just fine right all right awesome so um pretty much this is going to be um Caldera one of the tools that we personally like to get us started with entirely free so for some context Caldera is an adversary emulation framework that is developed by miter the same organization that Todd had mentioned earlier and the great thing is with Caldera is it pretty much runs off of a client server model you'll have your agents which you're able to deploy deploy to host and then Caldera itself will act as the C2 framework except that it's very interactive and it has a lot of features that you guys are
probably going to be excited to see about especially for something that's free and in fact actually for who here um came to Defcon this year so okay nice so a decent bit of people if you stop by the IC Village one of the things that miter did is that they showed up and they had actually introduced that they also have OT capabilities in calir as well so maybe if you for some reason have like a windmill that you can test some ttps on you also have that that ability to test it on as well so starting off with the agents this is going to be what you're going to be deploying onto the host and this is
what'll be allowing you to pretty much have a connection with it so deploying a Caldera agent is honestly extremely easy so if we just go here and we choose for example rag doll host is you'll have the opportunity to do maybe Linux and Mac if you want to try some of the other ones you also have Windows opportunity as well and it's as simple as honestly just copying a couple of commands and just pasting it onto your host I'll even show you guys right now a demonstration of how fast this can work so we'll grab our our little machine here paste in one of the commands from earlier and just like that we will have
an agent deployed and there we go just that simple so now that we have an agent what do we do with it on its own it's not going to do anything but that's where you come in so abilities one of the words that Todd had mentioned earlier was ttps ttps are going to be uh important to Caldera and in fact if you take a look at these is we have a collection of what's called Atomic red team uh tools so these are something that's created by Red Canary as an organization a separate tool that's also open source and integrated into Caldera so you have a collection of over 1,000 ttps that are already pre-built to you
that are aligned with miter attack so in case if to translate that is pretty much that saves you a lot of development time and on top of that you also have the opportunity where you're able to pretty much start building adversary uh Frameworks in a bit so just to show you and examples we have one thread actor group here called wicked Panda this is also available on miter where they have these kind types of spreadsheets available and you can pretty much just take a look at the techniques that each adversary group uses and the ones that they're most likely to execute so now that you know that is maybe you're thinking okay but what if they have one
that isn't aligned on uh Atomic red team or maybe if calar doesn't have it aldera allows you to build your own agents or your own abilities as well so you can kind of just take it through it it's very simp Le you just kind of put the name the tactic and whatever to it and then you'll run it um using command shell so you could do Linux shell you could do python you can do um all the way over here with Windows is um Powershell native and a couple of other things as well um so individual ttps maybe it might not seem that great to run on its own Caldera has a solution for that as well and that's with the
adversary profiles so with the adversary profiles is these allow you to create a collection of ttps that can be run starting off um as I've already got one that's pre-built for you um just kind of one that runs three Discovery commands that are emulated from Wicked Panda which is um a well-known thread actor group um and we have probably just a collection of five ones just to run with you really quickly today and pretty much what you're able to do is you're able to reorganize them you're able to have all these ttps ready and you're able to kind of create an adversary profile so what you see in here you can condense all the way into Caldera and you're able to have
an emulation of a thread actor group so how do you use this this is where operations comes in so really quickly is what we're g to is we're going to create an operation just by clicking that you can put it um adversary test is what we'll call it and here's where I start praying that the profile is going to work I ran this thing like five times here but um so the way it works is pretty simple is you press start and it does all the work for you you pretty much you can think of it almost like hands-free hacking um but of course it's it's more than that it is threat in formed defense and while this runs I
want to show you guys something over here our Splunk instance is shows that this isn't just about attacking this isn't just about emulating a threat actor group it's about threat informed defense and you're able to have this opportunity with your home lab where you're able to go ahead install this for free um sometimes with licenses it depends but main thing is is this is all running on free things and you're able to go ahead and check out and say oh hey clear history that seems a little bit weird um and pretty much all of this stuff that you can use in just is this allows you to create an effective purple team environment where you're able to
truly learn about adversary ulation um so going on here is the way that it runs is you'll see three different states is you'll see collect success and failure collect is going to be that it's currently running the command success means that you didn't get told to try hard harder and if it shows up and failed sometimes it tells you to try harder so I'll get to that one in a moment here but you can go ahead and view your commands to see what's being run and then you can also press view output so that way you can take a look and see what it produces the great thing is with Caldera is what's being produced you can also move some of
this data into variables as well this allows you to create something that's actually very emulated and something that says handsfree pause so that way you don't have to start from scratch um so what we're going to do is we're just going to take a look um view SMB share so and then if we move over to our Splunk instance I believe that you will get uh some of this ready so I know that we're um at 11:55 and it's going to take some time for some of this stuff to run so if you also have any questions feel free to raise them up and we will uh answer them as we go on maybe uh while this runs the
background I can uh F some questions if anybody has any I think this kind of concludes the talk so thank you for listening in folks appreciate everybody being
here any questions before we uh yeah let everybody out of here for some I see in the pink shirt yeah go for
it uh in this case I believe it's deployed on Debian and in the uh medium article you'll see it written up on how to install it on a new bun 22204 system the version of it it's it's running for Debian uh it's running Bookworm so that would be Debian 12 oh of the spunk install I think it's 911 something it actually has it like right at the top here as well yeah uh spunk 911
yeah yeah well hey no silly questions here yeah uh I think it's it might even just be a browser themed thing I'm not really sure yeah I mean we we like dark mode we like having our ex we don't want to flashbang ourselves here so also really quickly as well is um so we finished our SSH Brute Force as well so while it looks like it's telling you to try harder one of the things I want to focus on is you get one of the standard outputs of true which tells us something interesting is happening and we're just going to wait for our output file this is running against the domain controller with some of the IP addresses that we
had collected from earlier and if we give it probably three two one all right uh we have login successful administrator with besides to so uh if you could tell there's probably multiple instances of the same thing it's just because it appends to the file I ran this like six times just making sure it didn't you know tell us to try hard in the middle of the presentation and if you would like to connect with us as well QR codes to LinkedIn and if you're cool and like using Discord you can also reach us there as well thank you guys so much for this presentation that's





