Cracking The Perimeter: How Red Teams Penetrate

Show transcript [en]
okay well thanks for sticking around a stalker today everyone probably wants to head off to the after party and but welcome to my talk cracking the perimeter so my talk is it's mostly tool talk to be honest so for the next 4 40 45 minutes I'm going to give you a quick overview of some of the problems that we encountered during Red Team engagements getting that initial access and then I'll kind of move on to talking about and some tool development that we did internally we release it to the community in March I'll talk about the journey of this tool really some of once we released it there was some kind of active response to it from the defensive
community and then I'll talk about some of the the bypasses and things that we found around this and released in future updates and so who am i warm my name's Dominic Chell and I work for a company called MD sac and I am responsible for MD sex and see best and star services which means I tend to find myself focusing a lot of my time on why I now call rainbow team testing the reason for this is mainly just because I can talk about all these new colors I was just kind of make sure I didn't miss any of them so so I kind of go full spectrum like in CC there and put them all in the
rainbow so background and again foothold on an internal network is what all I find is often one of the most time-consuming aspects of a red team engagement I find myself spending a lot of time you know testing my payloads with various AV solutions on kind of various EDRs and whatnot trying to find gaps and so I wanted to kind of like streamline some of this but I found was actually once we get onto the network things really fly by and I guess the reason for this is there's been quite a lot of research into lateral movement techniques into Active Directory as with development of tools of things like bullet hounds crap my exact Deathstar things which tools which are really
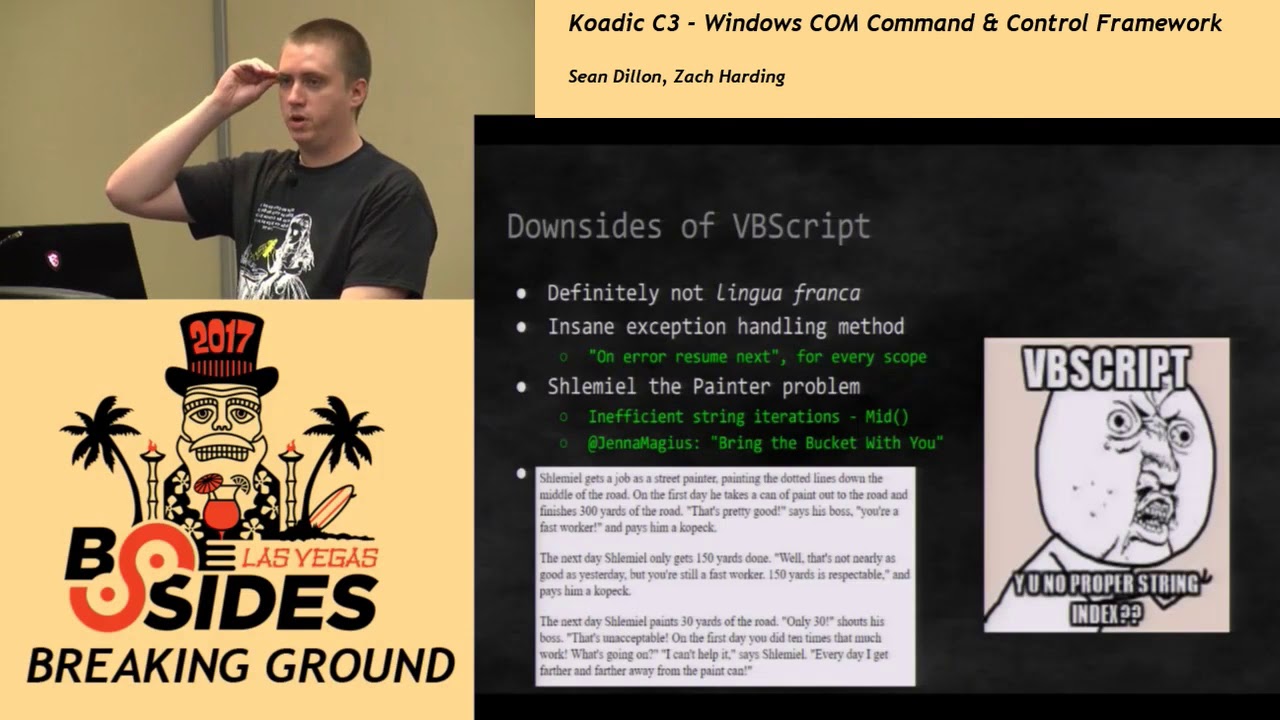
there to my streamline the kind of of lateral movement phase of already maneuvering there I think there's been kind of less focus on the actual initial access in fact there's a lot less kind of tools really for it for these sorts of things in fact the only ones that can really think of other things like unicorn from trusted SEC and as in the tool called star fighters by a guy called scene healers so we used to like PowerShell quite a lot in our engagements um but to be honest I think my general opinion is PowerShell is pretty much dead now and some people may disagree with me but there is a real focus from defenders on
looking for PowerShell attacks so anytime we could create the payload where we'd actually be able to run a command we would try and use PowerShell to actually get into memory and this was a great way to evade things like antivirus and the reason for this was mainly because which you're going to mend me you generally have a free pass but the downside is really pouch elves very easy to signature both statically so looking for people trying to call partial taxi so if you've got command line logging in place or you've got process porn chains if you ever see something like word wearing my PowerShell to exit that's probably a bad thing that with Windows 10 we have the
introduction of anzi which I'll talk a little bit about later but that basically provided AV engines direct access to memory so they could apply the standard signatures for doing fitting memory analysis we've also seen the rise of some boxing technologies and things like fireEye bromium these typically run your payloads inside a micro vm and if they spot behavior then they won't stop the payload kind of getting to the end user we've also got various products like silence power through traps that describe themselves as being kind of next-generation AV and supposedly don't rely on signatures we also occasionally have difficulties actually getting the payloads into the environment so and we used to use things like HD is quite a
lot and but what we found was because they've gained popularity and people starting to block the application HT a mime type they were blocking the HD extension on the perimeter so you can actually get those file types into the network in the first place we spend a bit of time using like exploits for public from abilities so there's quite recent spate of office books but again we found these with very easy signatures traditional AV was often picking these up quite quickly and so for my general opinion was sort of last 12 to 18 months or so we felt like the red team engaging been getting a lot harder so what I wanted to do was focus on developing
some tooling around this basically to streamline the process of testing creating payloads and try and build in some techniques that might help us avoid some of these defensive perceptions I'm sorry at least at all in March this year called sharpshooter and then I've kind of released several kind of iterations of updates and since then we've been using this tool quite a lot on red team engagements have had a lot of success with it we've used it to bypass a number of kind of next-gen security controls things like fire fire I silenced Borromeo parotid traps we as well as kind of like traditional AV and so that Windows Defender and McAfee as well it also got I featured in how because
played open if anybody's read this but least this is pretty good and so hackers play book 3 Red Team Edition they they had a couple of pages on on the kind of how the Tool Works and then some of the functionality inside it which I thought was kind of cool sort of the tool do well it basically allows you to create and staged and stages payloads for the majority of the windows-based scripting formats so hasty um applications JavaScript files VB script files windows script files and VBA and so Stage two basically means that you get a small bit of code which will we're on the end point I which is the stager and that will retrieve the main payload which in
this case is actually and some c-sharp source code so there wasn't at all catch the earlier this morning with some similar techniques to what we do with stage and stage low space achill e is the full code is embedded inside the script file want to execute it does everything that you needed to do and that might be you know ruining some shell code like winning your implant whatever and so the tools got some defensive evasion techniques built into it these include things like sandbox detection and another technique called HTML smothering I shall talk a little bit about later so how does it work well at the heart of the Sharpshooter is a tool called Dominic JJ script as written
by a guy called James for Shaw essentially got 9cj script and provides full dotnet interoperability through comments faces and that basically exposes them to windows script host so what that means is you can take an arbitrary compiled dotnet program embed it as a serialized object and then you can access that object and call botnet methods on it through JavaScript or V main script so the way sharpshooter works is it basically takes the dotnet to jscript loader it takes the shops you serialize objects and then encrypts it with a random key using rc4 basics before encodes it and that embeds it inside whatever file format that you want to use and then it's got a small
little harness that will when we're on the end point will and decode and decrypt the payload and execute it so that the kind of flow for that looks a little bit like this so the user gets like a HTML file it decrypts a script which then again decrypt some more content and then that uses dotnet CJ s and in a staged scenario it retrieves the full payload I've of my DNS web delivery or can do both and then it compiles the source code on the on the endpoint using.net code Dom compiler and then uses reflection to actually call the methods on the sterilized object so what you could actually do is I mean you can run anything with this you could use
it to run shell code so kind of retrieve and install your implant you could use it to a memory cuz it's pretty much do anything from you know just from from JavaScript so I've been using this training for actually quite a while and some other tools and I was kind of curious to see whether or not anyone else was using it so I did a few searches on Twitter and I found this tweet from which weren't and he was basically describing some some real live malware in in the wild and that was using code Dom so if we kind of zoom in on this it's actually doing something very similar to what my my code was doing so again I've kind of
thought that was pretty interesting so I'll talk a little bit about how you kind of go the approach to kind of using this tool so before we start any kind of campaign we invest quite a lot of time in constants which really try and kind of understand the target what the environment looks like if you're using sharp shifts as a target and a user there's a few things that you're actually interested in in advance so you you want to know the version of.net that is on the endpoint the reason for this is basically the payload needs to be tailored to match the same version of.net as what the user is using so if these are using like Windows 7 the
probably on version 3.5 of the.net framework whereas Windows 10 is more likely to be version 4 secondly if you're intending to execute and shell code in the existing process on the endpoint then you need to know what the architecture of the endpoint is and the only real exception to this that I've seen is with HDA files which are always 32-bit the reason for this is I believe because an SH Dax C is 32-bit process even on 64-bit systems so to get around that is possible to watch to get around that requirement and I intend to add something a new template which will basically spawn a 32-bit process in Jettas shellcode into it so you only
ever actually need to use 32-bit shell code so how do we kind of go about doing this recon well it's actually really simple so most client-side software will actually leak a lot of this information so we only really need to get the user trick them into opening an email or trick them into Clifton the phishing link so for example we might send in a phishing email that includes a remotely hosted image and when they when they open that email out if they're using outlook for example it will try and render that image and what we actually get is the user agent coming back from Outlook so if we look at a very simple example here we can see
we've got like the version of the.net CLR so like that using my frequent v we can see their version of office they're using and we can see she says while 64 so if it's well 64 just means it's a 32-bit office on 64-bit host so from one very simple email and the users I'd say the users and actually if we need to click on anything they just need to open email we're actually able to get quite a lot of useful information about the target in advance so now we've got enough information to build one of these payloads how do we actually go about getting into the environment so we'll sharpshooter actually uses a very clever little technique called HTML
smuggling which was again found by rich Warren Buffalo the flow on Twitter and basically the way this works is you can take any arbitrary file and then you can use the JavaScript web crypto API is to encrypt that file and store it inside a HTML file and then and you have made that the rc4 key inside the file and then when the user opens the HTML file it will just use the air crypto API is to decrypt the file and serve it to the user the way it says it to the user is it uses the VMS safe blob web storage method so there are even though the the files getting served to the user the
proxy will actually only ever see HTML file with the content type text HTML plus outlook actually supports opening HTML files as attachments so you could just email the user that HTML file so you could send them whatever you want you can actually send them exes and things if you wanted to let smuggled inside HTML file it's a really cool little technique so there's two templates that I included inside sharpshooter to do this one of them kind of mocks up a fake page making it look like the file have been scanned by McAfee but you can really kind of dress this however you want to based on your fishing and shot shoot has got a few techniques
in there to do some box of Asian these are mostly inspired by air Chris and Brendan's chair please project so the theory is some boxes will do automated analysis on a payload they'll basically looking for some form of behavior if they don't see that behavior will mark the file is safe and then ends up getting served to the user so if we're able to actually only limit our bad behavior to outside of the sandbox then it might be possible to kind of circumvent this perception so sharpshooters got a number of techniques to do this does the main key so if we're able to actually figure out the interactive directory name of the company in advance and then we can say
only everyone on this ad join domain and actually I don't think there's been an occasion where I've not been able to figure out the internal domain from the outside I'll show you a couple of techniques and on the next couple of slides we can we can key the payloads will never run domain gorge systems so things like fire I have like predefined guest images and use though what typically join these to the domain so they're not not typically domain joined so if it's one of these predefined guest images and it's not the main joins you don't the payload won't ever run because it's not on a domain member then it will do things like check for various sandbox
artifacts things like VirtualBox tool VMware tools that kind of thing a lot for pub mac addresses things like typically used by virtualization and then if anybody's doing any analysis on a will check whether it's being debugged but essentially if any of these conditions are met me at the actual payload that main payload won't work so how do we kind of go about the active directory names well there's a lot of different ways you can do this one of the tricks that we've had a lot of good success with is targeting companies you've got sky for business deployments and so if you've got an Skype for business and you've got for an end edge server what you'll find is there's a
default hostname that Skype for business users to locate the front-end edge servers and that for an energy server will leak the internal ad name although the fqdn inside one of the headers so you can see here for example we were looking at fire icon we can see the host name for this fireeyes Skype server is asabi us and I linked zero 1.4 Ida calm so it probably means that their internal ad domain is fire Ida calm we look at another example black calm so this time we can see the fqdn for this server is UK s FB f v1 not bit nine dot local so we could probably speculate that the internal domain name for cob why calm it's bit nine dot local
the reason for that is bitten and obviously originally acquired cob blocker changed the name from benign so with that kind of information we can we can basically try and key our payloads don't we ever run on those specific ad systems I also mentioned a shot shooter can work on the concepts of staging so the stage or in sharp shooter and will basically retrieve some c-sharp source code and that's been zipped base64 encoded and it will do this via HTTP or HTTPS but it can also do it through DNS using another tool that I wrote called power DNS what that does is the power DNS tool basically provide like a fake DNS server it will you can tell any file
that you want it to serve ID and s it will split that file up into chunks and then every and then the payload will make DNS text lookups to the fake DNS server to download the actual payload and then we construct it on the client side sharpshooter kind of does this iteratively by calling nslookup to EXCI on the command line the reason for this is there is no native library on version 3.5 of the dotnet framework to do tactical clubs so let's look a little example of sharpshooter winning against pal Mazal traps
so I videoed all the demos cuz I've done talks before ok so the first thing we're going to do is basically just create a I went a little bit too faster the first thing we're gonna do is basically just create the new Sharpshooter says once - a Python script targeting version 2 the dotnet framework creating like a CIA file and giving it some shell code we're telling it to use HTML smuggling and use the McAfee template so what it does is actually go here and create HDA which we'd actually need to use and also create like a HTML file and then go new and take that HTML file and just host it on a couple strikes web server
so all I'm doing is literally hosting the HTML file now and then I've got I've got a windows 7 vm with parts or traps and it like fully enabled just browse to the the HTML file so you can see up here it's a HTML and then that serves the download to the user and assuming they open it we get a beacon buck so we're able to like fully pass them we've got rifles full to a c2 so able to kind of fully bypass parts or traps [Music]
um so shortly after at least at all and it starts work get signatures by quite a lot of Vav that well a few of the AV vendors Microsoft actually created a signature for it and um Z signature so anytime you use it in Windows Defender or anytime you actually used dotnet to jscript in Windows Defender it would flag it as being sharp Chappell was probably inconvenient for all the other people who are using botnet to jscript but effectively they were they were detecting on the primitive that donnetta jscript was using for doing the the coins rot so that kind of led to the tool being proclaimed dead by Casey Smith on Twitter this was in April but
kind of again in June of false that's what we look at this again and maybe I can do some updates and so in June I just took the default payload so just took the default HTML file stuck in virustotal just to see what see what the kind of outcome was and even still it was still like 5 out of 58 detections and if I took like their default HDA file its it was still only 14 out of 58 so I wouldn't necessarily said it was dead but I kind of thought well I'll take a look at it again anyway and try and resurrect see if I could bring it back from the dead so the first thing to
do was really look at what defender was doing how it was detecting the payload and what I noticed was that defender didn't actually care about the copy of the payload on disk the alert was tied to an ANSI signature that's when you run it and he was providing defender access to memory and it was basically signature on that and so if you're not familiar with what MZ is it's Microsoft's anti-malware scan interface introduced in Windows 10 so this is basically like a standard interface that allows any kind of security products it's not just Windows Defender to get access to memory so that you can scan for malicious code and the way it works is that anze's
actually implemented as a dll the dll's then load through every powershell or windows script host session one of the most effective things about MZ is that because it wouldn't inside the scripting engine it basically allows the AV engine to actually get access to the plain deal this gated code which obviously makes signature detection a lot more powerful because the AV engine doesn't need to deal with any kind of obfuscation that's going on anymore so it's MZ something we need to worry about as a read T in that well I thought this kind of tweak from we Holmes was pretty interesting basically Lee did a breakdown of all the different AV vendors that are currently using amazeen and you can see there's
not too many of them so we probably only really need to worry about MZ if you're using Windows 10 and if using one of these AV engines that are actually using it so let's let's talk about MZ bypasses and so mid-april and sub T the same guy who kind of proclaimed it dead and basically released details on an attack the second iteration of the squiggly attacks called squiggly tooth I didn't I didn't name the meaning he named them well what the attack basically allowed you to do was execute script works in full trust so and these could be embedded inside an XML stylesheet and he used the the wmic dioxyde command-line tool to do this and so while I was
playing with this technique what I actually noticed was that the same sharpshooter payloads that were getting by MZ previously if I put them inside a scribbler and loaded them through WIC they would they were not the ansi signature was not triggering so this was really interesting to me so I thought this was kind of kind of cool because even though KC originally proclaimed it dead he kind of gave me a technique to actually resurrect some of the the the functionality and so with that in mind I decided to watch the update sharpshooter not not only to incorporate this quickly to attack the tool also incorporate the original squiggly-doo at the squiggly-doo attack uses regice 32 binary with with an SCT file and so
you can host the SSL or the SCT remotely and then use wmic or better 32 to download and execute the code inside them and so to do this I basically coined a technique why called Archon staging in sharpshooter in short there are several known comm methods that allow you to execute a command on the OS and are accessible from the windows script host and so the ones that I decided to implement were the outlook got great objects which was originally discovered by its installments the Brio script up run shell browser window which was found by Mac Nelson inspector ops and then the standard kind of W my stolen 30 process and so the idea really
is sharpshooter will now generate a little stub that will use these comm objects-- to execute the command and then retrieve the kind of remotely hosted script script look but then like I had a bit of a revelation it kind of struck me I was but I was being a little bit of stupid here even though this kind of technique worked well I know I was getting around and II thought well I've got something running on the machine I've got access to calm but I'm kind of calling a sick man like why do I need to call out to the command line or if I could find something in calm that would actually process a stylesheet internally
so I did a bit of searching on on MSDN I basically found a comment face called XML Dom an XML Dom can be reached and through the windows script host and it's got a method inside it called transform node and that can be used to pass an XML style sheet that's remotely hosted and inside the external style sheet you can include a script which executes in full trust so the main benefit around this was and basically I could I didn't need to execute commands on the OS anymore and I was able to avoid some of the indicators that are associated with the squiggly-doo attack so things like the noone registered a to user-agent and then the Palos actually
becomes very very small and you can remotely host the XSL file the reason and it's also very difficult to signature the reason for this is because it's any kind of code that is using this comm object will have very similar similar method calls so if we look at an example of what the export might look like something like this in JavaScript would actually you could actually use to execute full dotnet from inside the hosted stylesheet and so as you can see like a legitimate tool that might be using this comic jet will will probably have very similar code if it's using a star shape so we can look at like a little a little example of how I'm gonna
do this so I'm on another video
um so I'm doing this time is I'm using sharpshooter and basically creating an additional file which is this XSL file and this time will host it again very similar to the previous one but we need to host actually both file so I'm hosting the HTML file and I also need to actually host the XSL as well so what host it to sell to the Fuhrer and this will basically create the little stub to run on the endpoints so we see you've got Windows Defender went in here Windows 10 no no alerts at the moment and will work will just browse to the two shown it's on again will browse to the HTML file at this
time you can see we serve in a JavaScript file so we open up open the JavaScript file up nothing happens no Evie alerts in independent no pop-ups or anything but what we should see is we've actually got like the standard kind of purple stripe beacon again so this has been able to fully bypass the the defender MZ detection so let's let's look at let's let's assume at some point Microsoft blocks that technique all they care about Anne's esport into scriptlets now what will they kind of lamzy by classes are there will a guy called tal Lieberman and discovered a very cool and very simple a mizue bypass which is basically there is a registry key called
an ziyan able and if it is set to zero it turns it off so with this in mind it is possible to actually sorry that registry key as you can see it's in sitting there current user hive so it just means like loop standard users can actually even turn it off so this in - actually possible to create a scripts which will check if the key set if it's not set it will then set it and then it will just reopen the same file that you've already downloaded and then on the second pass they should actually be disabled so basically means the scripts will get like full court launch so this is an example of how I wrote this
yesterday this is an example of how we kind of exploit this basically we just check whether the registry key exists if it doesn't exist it throws an exception which we catch and we write the registry key and then it uses Matt Nelson's shell browser window come object to basically just call the downloaded JavaScript file so what we do is we open the same file that we already unloaded on the second pass and Z's fully disabled what are the techniques are left James for Shaw he found a second hamza by paths through dll hijacking basically what James found was this was kind of interested in was that it was possible to stop the load library function from loading the OMSI dll by
convincing load library into thinking the DLL was already loaded see my thing well how did kind of go about that well actually it's really simple and so the way he did this was basically you could copy the name of the the scripting engine so like W script I'd see you just cook it to a name location rename it to MZ DLL and then when your scripts and then what would happen is um because they they were basically full load library into thinking that the DLL that was loaded was an Z dot DLL but really it was your copy of W scripts and because it couldn't because it wasn't the real an ZD allow it couldn't find
any of the exported functions so it would just fail safe and then it would basically mean there was no MZ detection so again a pretty simple technique so I've got another another quick demo of this technique as I say I only wrote this this this one yesterday and soon we just we just create this the same kind of payload host it up on the cobalt straight web server and then if we look at the Windows 10 VM so I've got the I'm showing that the registry keys not actually there at the moment but we are then we browse to the file download the JavaScript file if we open up you'll see it pops up twice for even a
click open it clicks again and you still got the same open and then now we can see that the actual the MC flag is there the JavaScript file that we downloaded is there there's no alerts inside defender we should we should have there the full purple strobe beacon again so let's talk a little bit about kind of detection prevention these types of payloads so if the payload is using the kind of code dom reflection trick you might think that the payload is is fully compiled generated in memory and that's originally what I thought so there is actually in the source code of code Dom there is a compiler parameter called generating memory is set to true but it
doesn't do what you think it does basically what it does is it takes a copy of this easter shop source code it drops it in windows 10 folder and then it uses an CFC 2x e which is bundled with a dotnet framework to to actually compile it get the loaded dll and then downloaded dll and put it into memory and then use reflection on it so one possible detection technique might be looking for random calls to CSC to exit if you're using something like like the dns delivery I mentioned before that it uses an S lock a backseater to retrieve the sense records so you could look for kind of very a lot of calls it received
calls to and it's lookup direct seed or if you're looking something that's trying to bypass on Z you you could just monitor for any changes to the UM Z enable registry key in terms of prevention if we're talking about a Windows 10 in point one of the probably one of the most effective approaches is using device barcode integrity policy which will basically allow you to limit scripts to execution of only sign scripts you could use application whitelisting for example so you can block things like MSHDA w script XC or CFC 2x e because in most cases most normally uses probably why wouldn't these quite a quite an effective technique which I see from time to time
is people creating group policy to basically change the default handlers for some of these file extensions so rather than associating a s with debris scripts or dot HDA with MSHDA you just change it to notepad so anytime one of these files hit to the end point if the user opens of it just opens up a notepad or maybe even like a combination of all these from a network perspective I guess like if the DNS technique is quite easier to block just stop low there kind of outbound DNS filtering right potentially for looking for HTML smuggling you could look for HTML files are using the web crypto API you'll probably get a few false positives but
it is possible it's a future work I've already started development on some of these bloodlines what a few templates more than just shellcode executions so you could do things like what Mimi Cutts quite easily I'd like to have more up the station particularly it's like this see short code that's which is disk it should be possible to obfuscate this and then probably additional the file type so Matt Nelson found and some interesting files that effect Windows 10 over like the same content a mess file which is it will be quite interesting to add you can download the tool from an besets github page and also like to just thank guys that I borrowed ideas from I
would recommend following all these guys on Twitter because they're regularly kicking out interesting stuff and then our that's it for questions [Music]
also stop thanks Dom has anyone got any questions just a quick run on the.net 2j ass doesn't work with the very latest version of.net cuz i would just mess around done that yes come on weeks ago I tried to compile it I'm like 4.6 or yeah and for some reason it just phoned and said now it's only for like vision too cuz they thanked you removed vision too so because I've also they tried it on light up to 4.5 but if they remove v2 doesn't mean if they were completely remove it yeah Buhler no okay so we're just going to wait third track to to to finish before we