Netrunning the Grid Safely: For Dummies!
Show transcript [en]
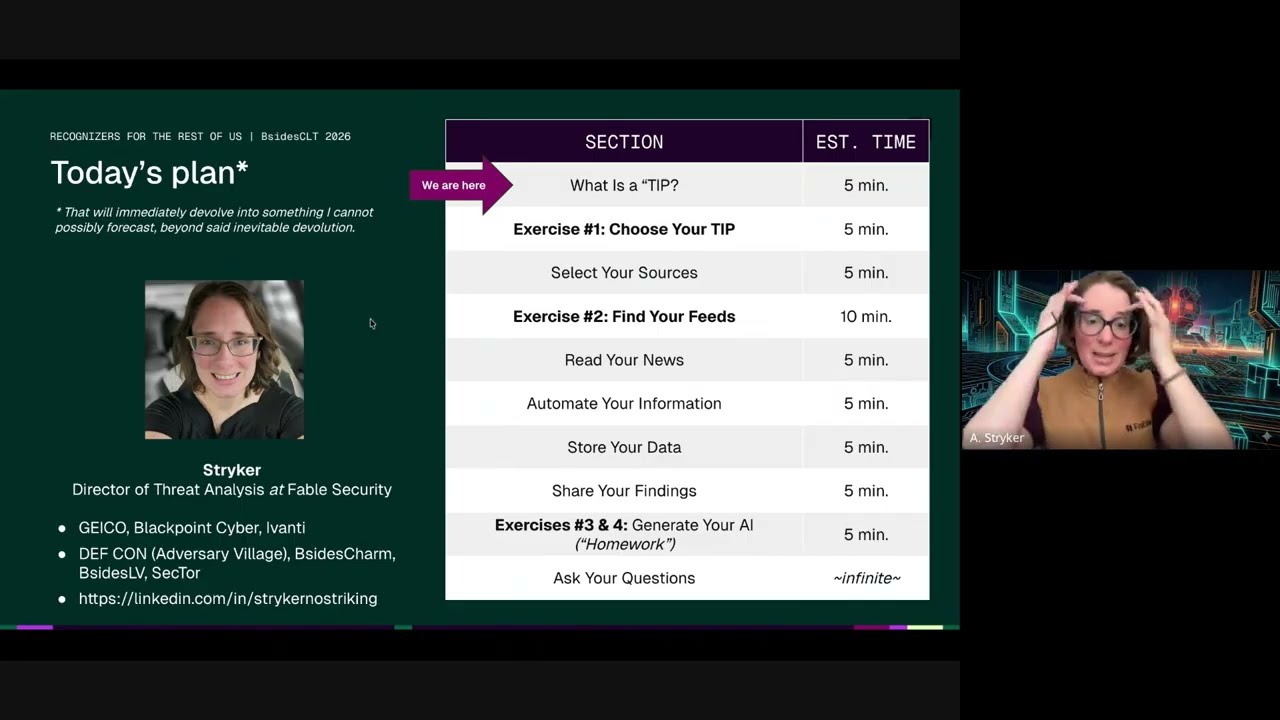
All right. Hello everyone. Uh, this is going to be a very beginner friendly talk about malware analysis titled Malicious Programs for Dummies Don't Get Dresed. Uh, to start off, a little bit about me. If we can please do that. There we go. A little bit about myself. Um, I am known as Skeptic Septic, Alexa, Lev, Destroyer of Reax, whatever you want to call me. Uh I'm currently the forance security division lab manager for UNC Charlotte's security team. Uh we just won competition. Very cool. Very cool stuff. Um I am a big fan of anything keyboard oriented workflow wise. Um I love Linux tiling window managers, Emacs, Vim stuff that kind of stuff. Um I my first ever
talk actually like as a public speaker cyber security speaker uh was a besides Charlotte talk in 2023 about malware no that's this one uh about Wi-Fi hacking with microcontrollers that was very fun and kind of got me to start talking about cyber security stuff with people and so moving on to the talk itself Just kidding. First, we have a disclaimer. Use common sense when following along with this. Don't run any code you don't understand. And don't send any Bitcoin to addresses that you don't recognize. Thank you so much for listening to my talk. That'll be all. Have a good day. Not really. So, to set the scene, as many of you may know, a lot of the time when you're
going around some of the lesser parts of the internet, you can run into some funky stuff. Whether it be in the back alleys of the web and onion sites, peer-to-peer instances, or even something as benign as Pastein. In fact, from my experience, uh, Paste Bin oftentimes has more lucrative stuff for seekers of random interesting information than tour. And it's also a lot faster than tour. So, let me put you in my seat for a minute. I'm uploading something or other in past bin and in the corner of my eye, I pick up the word free. And then not only that, but it's also surrounded by not one but two money face emojis which claims to be a G2A free gift card guide.
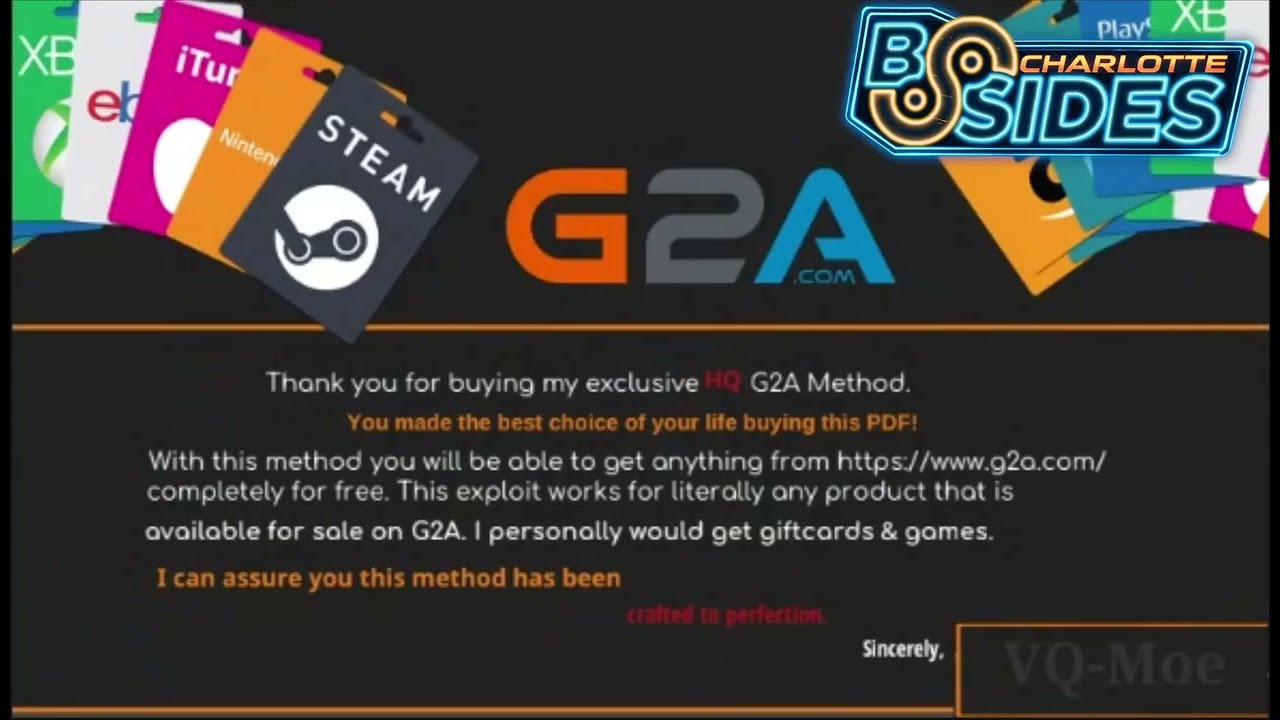
And so if you're unfamiliar with what G2A is, it's this little online video game key reselling platform that is known for uh just a tiny little little tiny small amount of scandals. Um with this one being my personal favorite headline because I mean just look at it. It's I could not have articulated it better myself honestly. But anyways, back to the exploit at hand. Um, it takes me to a PDF um, which looks something like this. Actually, this is it. It's a screenshot of the PDF. Um, and it says, "Thanks for buying my exclusive high quality G2A method." And it says, "You made the best choice of your life buying this PDF." And I'm thinking, "Oh man, this is
awesome. I didn't even buy it. I just stumbled upon it by accident." And it's so great because I mean he says right there, right here, it's been crafted to perfection. Sincerely by VQ Mo. So I look in the instructions all excitedly getting ready to thinking of all the Windows licenses I'm now going to be able to buy. And then I see that it tells me to download a Tamper Monkey script. And which if you don't know what Tamper Monkey is, it's simply a Chrome extension. Um might be available for Firefox, too. I'm not really sure. Um, and it allows you to overlay JavaScript, which is a popular web development language, uh, on top of existing
websites to modify their look center and behavior. The cool part about JavaScript is that it runs locally on your machine. Um, and so keep that in mind. And so this tamper monkey script, according to our wonderful malware author VQ Mo, will allow me to buy products on G2A and then get an automatic refund while keeping said products. And it then notes how you need to transfer at least 0.0021 Bitcoin for the refund to be automatically transferred, which is something like 145 bucks. You know, something about how higher values get prioritized in their automated refund system. stuff like that. Seems legit, right? And so I go get to my cart, add 11 Windows, 11 licenses to my cart, and
then go and check out, get that wonderful QR code, scan it, and send hundreds of dollars through this exploit in Bitcoin to, you know, make sure it really works because, you know, I don't want to be like accidentally send too little and risk not being prioritized by their automated refund system, right? And so I'm waiting for my refund to come through. And so I wait and then I wait. And you know, maybe I'm thinking maybe Bitcoin just takes a while. But I don't get it. So I What happened? Let's let's let's rewind a little bit. Let's let's go to the script at hand. the temper monkey script that I downloaded earlier. Um, to analyze that further, we see that it's a
very long opuscated script, which basically means it's made to be deliberately confusing and unclear to follow for both malware analysis and nerds that desperately want to get into cyber security. I should have audited this speaker notes. Um, and of course, there's legitimate reasons to opiscate code as well. It's not exclusive to malware, but also to people that want to protect their intellectual property, stuff of that sort. Um, but luckily for us, obuscation can be at least partially reversed through plenty of online services like obfuscator.io, etc., etc. I've got some mentioned on the slides. Um, and here's a part of the readme for one of those kind of showcasing what it can do. If you want
to take a look like here we see it's creating arrays of characters and then through some complicated math it puts them together but at the end of the day it's the exact same thing as this little bottom message which just says hello world. And so taking our script through a deopuscator we begin to see some interesting things. Uh we see some references to exploit successfully enabled. We see what else do we see? We see Bitcoin address, etc., etc. qr1.png and ooh we also see i.ibbb.co I'm not reading all that. Uh, right there. There we go. Look at that. Um, and that takes us to none other than a QR code, of course. And the QR code is a Bitcoin
address which very much does not lead to G2A. So in simple terms and to kind of give ourselves a brief overview, what does this mean to the end user? Luckily for us, I've created a very detailed visual through some very complex graphical design software to help the visual learners among us a little. Um, and let me pull it up. There it is. Beautiful. So, what really happens is VueQMO right here, he gives us this little tamper monkey script, which is JavaScript. And what that does is that finds the real QR code and slaps a big old fake QR code on top of it along with doing the same thing for the Bitcoin address. And you're just sitting
there. You have no idea. You're just trying to get your free free Windows licenses. It's awful. It truly is just horrible. And so now that we understand what's going on, let's take a look at the very similar uh arguably dumber exploit that is from the same exact author. This one uses pretty much the exact same concept as the previous one, but the only difference is um actually forgot to mention uh that URL earlier that led to the QR code. it has been down for some time. And so this script avoids that by instead of having the payload be a link to a QR code, the payload is the QR code. But let me elaborate a little bit.
Put simply, what the script does differently is again in instead of relying on a link, it uses what's called base 64, which is an encode encoding uh thing uh binary to text encoding scheme, fancy words, that through dark arts and black magic can both encode and decode images into ASKI strings like we see right here. Uh, and we can tell that it's base 64 through a very advanced technique called looking closer where we see data colon image PNG semicolon base 64 and then the actual values of that image. And just like uh earlier, there's a bunch of online tools that can convert your B 64 encoded image into or well your B 64 encoded text into an
image. Um and we see that converting just copying and pasting that into an online converter gives us a QR code of course. And so at this point, I was kind of curious if anyone did actually fall for this scam. So I tossed the address into an open- source blockchain explorer called Mempool. Uh, and I found that this bastard netted themselves almost $5,000 in Bitcoin through that. And you know, for anyone else who had a reconsidering of their career, I asked Chat GPT and it said not to do that and that there's a bunch of boring laws that they're going to get you for if you do that. Uh, but anyways, back to the script at hand. Encoding an image
through text is interesting and all, but also we don't have any concrete evidence that it did actually hook onto the real payment code. So let's go to number one suspect after our deoffiscator. This is the function that takes care of the actual hooking onto the QR code. And it looks very self-explanatory, right? I mean like you can just tell exactly what it does just by looking at it, right? No, absolutely not you can't because it's still obuscated. Uh so let's break it down a little bit more with the help of a familiar friend here by forcing chat GPT to rewrite this in a more human readable way. We can see exactly how this works. And we can see
that it takes the addresses of the actual Bitcoin address as well as the alt text. It uses that to find the QR code. Um and then after that it defines the actual QR code and uh address of the malware author and then while the real ones exist it replaces them with uh the attacker's address and it just keeps doing that every 100 milliseconds in order to win any race conditions in order to persist after a refresh etc. And so there we go. Congratulations to you. Together, we have managed to break down this incredibly complex, super advanced piece of malware consisting of pretty much just fishing and hoping that you're dumb enough to execute JavaScript from some random person on the internet
and then send $150 in currency known for not being the easiest to get back. Well said. JavaScript is running. So, congratulations to you. Give yourself a wonderful round of applause. There we go. But what's the takeaway here? What's our what's our bigger picture? What's the What's the moral of the story? I will answer that with don't blindly run [ __ ] you don't understand. But at the same time, don't be scared to do a little poking because who knows, you might learn something new in the process. So let's say you, the viewer, are out in the wild and you find a sketchy script. What's next for you? As we have seen, running it blindly is not quite the best
idea, although we will get into that as well. So, why not call for some backup? Enter chat GPT and friends. Lots of LLM models are actually pretty okay at analyzing suspicious code for general overview. >> Um, and also great at like providing more guidance as to what to do yourself. Uh although it is a generally good idea to say you're analyzing the malware in a controlled environment or it might yell at you for good reason because you should be analyzing it in a controlled environment. And also AI hallucinate trust them as far as you can throw them. Wh There we go. Uh so back to that though sometimes did I skip a slide here? No I
didn't. Okay cool. Sometimes even with that though static analysis that is analyzing code without actually running it can be a little bit more complex than someone new to the field may want. And you know maybe you're just unfamiliar with the language maybe etc etc. Maybe just the code is really long and you know put it simply sometimes you want to see whatever it is you're analyzing as it actually runs and sometimes you want to run it blindly. Enter sandboxing. When you want to analyze something or other as it actually runs, it's important to be able to keep it on a short leash, which is what virtual machines commonly abbreviated as VMs are ideal for. And by using a VM, you can
basically have another computer inside of your computer. And so you can quarantine whatever malware you're working with specifically to that virtual computer running inside of your actual computer to prevent the malware from actually doing anything to your host machine which is being like the machine computer you're actually using. Um and so this process when properly implemented is called sandboxing. And through that you can analyze all sorts of malware as it runs within that virtual machine without any risk of harming your actual computer until you can't enter sandbox escapes which through dark arts that I'll unfortunately not be discussing today can escape onto your host system or at the very least detect that they're within a virtual machine and stop
whatever it is they're doing to prevent being analyzed. Typ typically this is done by fingerprinting your virtual machine for software and or hardware that's common to virtual machines. But fortunately this is mostly isolated to more complex bits of malware and Fortnite and a lot of games actually. Um but most of the time you probably won't have to worry too much about it. But I never told you that. Luckily for us though, there are patches for virtual machines that protect against exactly that, with this one in particular being shown to be by a certain friend. And how it works is essentially primarily by spoofing hardware serial numbers and UFI settings by us settings. Uh like for example this
one specifically one of the things it does is instead of reporting a generic KU keyboard Kimu being a virtual machine program for Linux um it instead reports says that we have ASUS keyboard along with a ton of similar tweaks and you know that's usually good enough um but even then such patched virtual machines can still be identified through more advanced timing based attacks. uh which is again something that's way out of the scope of this presentation. Um but this means that if you do intend on quite literally looking for trouble, uh it might be a good idea to invest in a cheap ThinkPad or some machine dedicated to this, preferably without a connection to the internet, often called
an air gap system. But again, this is a bit overkill for today's discussion. So instead, it's advisable to focus on being prepared for when things do go wrong because they will go wrong. Like with safe backup solutions, you either love them because you've had to use them or you hate them because you haven't had to use them yet. And backups are actually a bit of a personal staple of mine since moving to Linux. Um, now a solid two years back, my first ever time irrevertably destroying my computer was when I tried to right here we can see uh, essentially I tried to move something that I downloaded into my downloads folder instead of whatever folder it was in.
Um, and I got the syntax slightly wrong. And so the difference here looks, you know, very benign, but the top one right here, it copies or no, not copies, sorry. It moves uh everything from the directory that you're currently in to the downloads folder. Whereas the second one right here, that little slash right there indicates your root drive being like your very initial drive. uh meaning that you're moving absolutely everything in your computer into the downloads folder. Uh needless to say that is not very good for your computer and I had to unfortunately reinstall Arch Linux again because I didn't keep backups at the time and this gift actually is from me. Uh that is the
backup solution I had for a while after that. uh one singular SD card that could fling out of my laptop at any moment. And I mean saved me a couple times actually. Uh because I mean backups, you can revert to a known good point. Very cool stuff. Uh and so personal anecdotes aside, uh the tried and tested rule is the 321 backup rule. And so generally uh you should keep three copies of data on two types of media uh with one of them being stored offsite. Uh it's whole thing to be safe. So backups very important very easy to implement and very tedious. If you're a fellow Linux nerd I highly recommend time shift which
has a great guey and is very easy to schedule backups. And if you're on Mac or Windows, I have no idea. Go find some. And so to kind of go over what we've discussed today, don't run scripts you don't understand. Feel mostly free to let said scripts loose in a sandbox or better yet, an airgap machine if the funds permit. And if you're a curious cat, make sure to keep a backup or five. and courtesy of our very own club's internal vice president, send it. That motto has led to a lot of data loss in the past. And that will be it from me. That's my LinkedIn. And that is an image that I spent way too long photoshopping.