Purple Teaming 301 – Free Attack Simulation and Control Validation via Atomic Red Team
Show original YouTube description
Show transcript [en]
[Music]
[Music] now I know uh on the last thing between you guys the closing ceremony and getting your way home uh I have long drive back to the Eastern Shore myself so definitely trying to get out of here too so we're try to we're try to make it kind of quick um my name is Jason Wright and I'd like to premise the beginning of my talks with kind of why I make some of these presentations so uh I made purple teaming 301 free attack simulation control alarm and control validation I know it's really long uh not not the most catchy title but um being on the Eastern Shore uh there's a severe Talent shortage over there uh among other
things and uh I tried to find a way for uh to kind of bring something free to secure Delaware every year and that's where this talk kind of came from uh secure Delaware is a small security conference that's uh hosted by uh the Delaware Department of technology and essentially what they do is uh they bring in about 500 people you know from cyber security there on the Del Marva uh bring them in and we all just kind of like hodge podge and kind of have something kind of like here at bsides you know it's great um so my goal is always to try to bring something free because a lot of the attendees or small
towns and municipalities and things like that that don't have a dedicated cyber budget typically or have super small cyber teams and they just don't have the budget to go out and buy something like an attack IQ or something like that so that's where uh that's where this talk came from so a couple kind of quick disclaimers uh you know even though I'm using Chesapeake's uh you know pretty uh PowerPoint template just because I'm I'm not a big fan of the circuits and PowerPoint um so I use their stuff this is not necessarily a reflection of Chesapeake this is not a reflection of my primary employer cona uh or anything like that okay so first thing I want to
start off is with the why why are we here today so out of show of hands out there um anybody you know currently leveraging a mssp as like a sock as a service or anything kind of like that yeah kind of okay so everybody else has like in an in-house sock in-house sock or doing their own detection response inhouse okay okay uh I we try I try to offboard as much as that as I can um but you know sometimes you definitely want to see whether or not an mssp that you're leveraging is properly monitoring your environment U I don't think I'd be the only one in the room that might say hey uh you know had a pen test done for
an audit purpose or something like that and your EDR or something or or your sim never goes off once right so sometimes it's just about gaining that extra visibility um you know it's also a more cost effective way of validating security tools and controls outside of you know your traditional yearly pent test right uh and then you know have you ever had a pentest you know we already talked about kind of just like running commands but never actually send you like any type of escalations or anything like that you know you know what if they're running like Bas 64 and code to commands and you're just not even getting an alarm at all um and then of
course you know have you ever just wanted to mature your detection and response program internally right through exercises without needing to hire a dedicated red team um for a lot of the you know companies on the Eastern Shore you know they can't afford a dedicated red teamer um so it's better to invest into the current blue team that we are have in house that's running some of this versus maybe going out and uh finding more Talent so a little bit about me uh my name is Jason Wright um you know grew up in Glenn Bernie so I'm familiar with the area and stuff like that but moved to the Eastern Shore um got my bachelor's and masters from umgc
I'm also a graduate of chesap Community College I went back there to teach after I got my masters you try to put a dent in some of this Talent deficit that we have over there um Got 5 years of technical security experience just in the financial sector been in security a little bit longer than that I'm currently a senior security engineer for cona uh know basically a fintech company and then um uh over a decade of experience in inform in information technology I do you know I've worked my way up from the help desk I started out taking mice and keyboards to people um took over exchange I think anybody that's been an exchange admin over the
past couple years knows that that's been an absolute dumpster fire for for a while um so but hey you know it's one of those things um and then I did uh some incident response Contracting for a while um I love it when stuff's on fire and being an exchange admin I got used to that for a while uh and then slowly uh started uh an mssp that I was working with at the time saw that I actually had a pretty decent skill set and it was like hey you want to do some IR um Consulting and I was like yeah sure okay yeah sure let's try it uh and it's just kind of spiraled out of control since
then so I just kind of found a way to kind of like when things are on fire uh I got the alphabet soup that everybody else got in terms of certifications and stuff like that too okay um all right so we already covered the wise we covered a little bit about me um going to talk about what I believe in my methodology of blue purple red in terms of like maturing out of security program um I also built this uh presentation to basically serve as a way to uh for students my students down at Chesapeake to be able to kind of spool up their own environment at home um so I have some technical prxs in here it's really
really easy really really straightforward it's not anything super like we're not running containers or anything like that you know I I find some value being able to stand up your own domain controller and stuff like that especially for students that maybe don't have that exposure or never built out that type of infrastructure um so I had the some technical prxs a little bit about the lab architecture uh Jerry I appreciate I appreciate you leaving some of the atomic red stuff out uh we're going to talk about Atomic red uh a little bit there some of their attack simulations and some really dialed down attack Sims um not anything super fancy because if I had to do something super
fancy I probably would had to do a live demo and I've gotten burned by live Demos in the past so Jerry you got a lot more Fai than I do in terms of the live demos I'll give you that okay so we're going to cover uh a couple of the easy ones and then you know just uh kind of wrap up with kind of how to improve and then leave some time for questions at the end I hope all right so blue purple red right this is my methodology so blue teaming I think a lot of us know just being on the defensive side of the house uh kind of what blue teaming means but
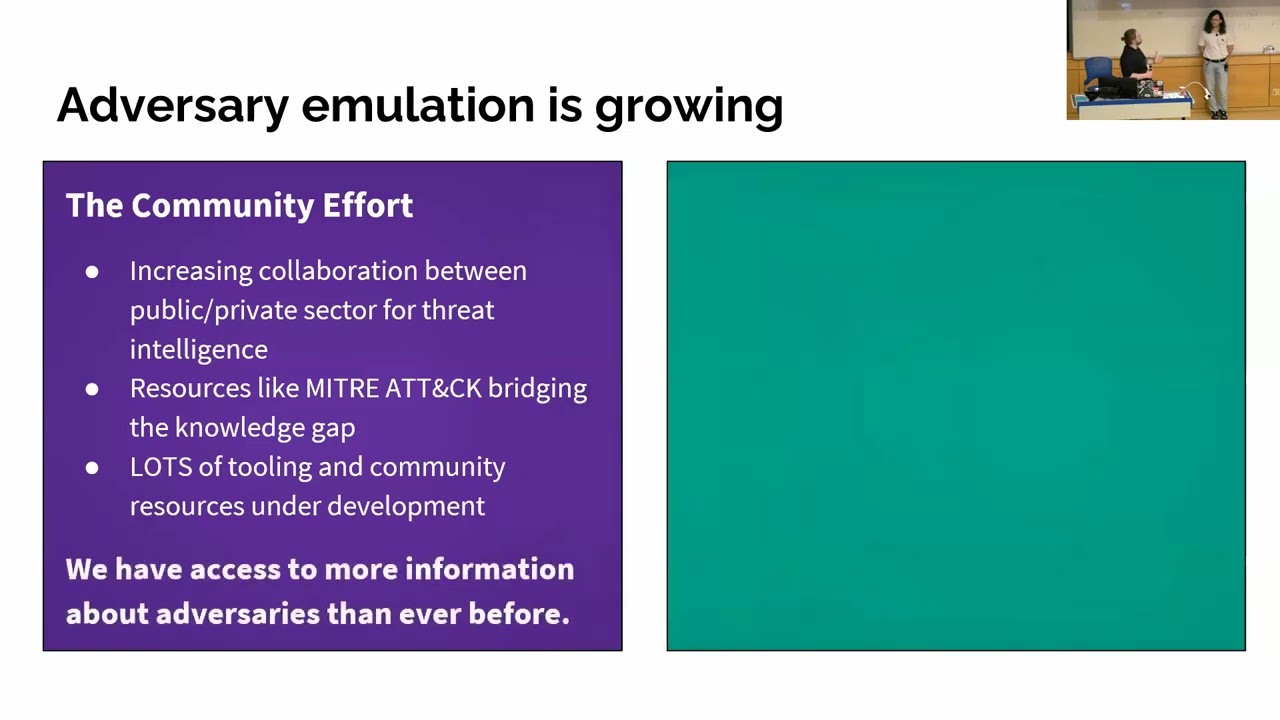
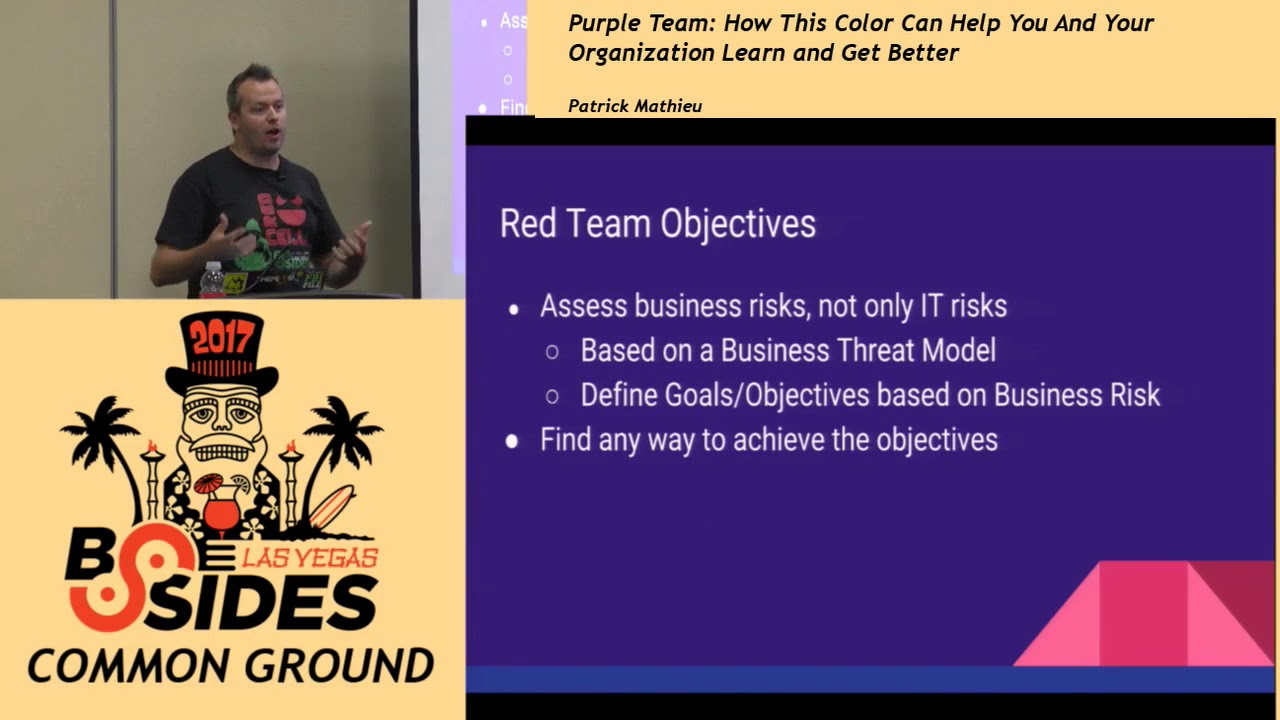
you know this is the group that is going to be responsible for defending our Enterprise you know our information systems being responsible for our security posture and our defensive security stack right so generally you you know maybe they're doing this against red teamers maybe you know you have that or maybe you have adversaries or something like that that's uh kind of coming after you um so you know they serve that defensive uh position uh you know you have your typical red teamers right there a group of individuals authorized to and organized to emulate a potential adversary attack or or just try to actually exploit some vulnerabilities uh within the environment and then we kind of get to
the middle ground right where there's going to be you know a space where you have you know potentially a blue teamer that's looking to kind of take that next step uh in their career and and maybe or maybe they're even stagnating kind of like in their role and they want to take a Next Step but don't really know where that is well you can kind of start bridging that Gap getting into things like attack him and stuff like that and what I like to call Purple team you know you know there's a lot I've actually talked to quite a few people today that were like oh hey you know are you doing the attx thing I was like yeah I like Oh
I'm a purple teamer so you know it seems like there's a lot of people out there that want to um get into this but really purple teaming is where you kind of take both things and kind of mash them together right you know you take your defense you take your offense and you just mash them together so purple team is going to be that group of professionals who simulate malicious taxs uh you know penetration testing and things like that in order to actually identify the security of vulnerabilities and then recommend you know recommend strategies for mitigation whether that is you know some type of control implementation or maybe it's some something as simple as just better
alerting um you know Jerry talked about it with uh with uh Sison right just having better alerting having better context of logs uh the trar guys they have done a great job about just kind of showing what what Microsoft doesn't do great out of the box in terms of logging you know adcs is a you know a treasure TR of logs and just not enabled by default right so things like that so unlike traditional red teams you know purple teams work together closely to share this information and try to tighten up some some of those weaknesses so our blue team people right so they set up our defenses create alarms create those monitors you know
this could be an mssp this could be a sock as a service uh it can be an internal sock this can also be a security engineering or security operations teams typically these things are in-house and affordable this is how a lot of people kind of get their start in the cybercity space is joining on as a blue teamer okay red team right typically attacking defenses finding holes doing uh threat modeling and things like that um typically these are going to be our offensive Engineers or penetration testers and things like that uh but generally that skill set comes with a price tag it can be expensive and generally we use contractors or vendors to perform those tests we have a lot of
great ones here that that do that type type of work right um so we typically offload that versus having somebody dedicated on staff just to do that 24/7 because we need our our team to be able to do other things so this is where purple teaming comes in so generally this is somebody has interest or knowledge between both sides of the field and wants to bring everything together it can be affordable such as promoting somebody on your blue team up you know up a roll and generally you know it might be a blue teamer that wants to explore uh the offensive side of the house improve defenses through you know continuous attack stimulation versus just doing something like a pen
test that is just one of those point in time tests where you have a point in time test you fix everything then you just sit there and you you're kind of stuck in a law until your next pen test where this you can uh perform regularly right you can uh uh work on things and then check for uh things like con you know config drift and stuff like
that all right so some of the tech PRX everything in here is free I assure you it is all free I built this all free all you need is um a workstation virtual box some type of H you know hypervisor software or something like that um we're going to leverage Atomic red so Atomic red team is a library of simple test that every security team can execute to test their controls test our Focus have few dependencies depends on kind of what you want to do um and are defined in a structured format that can be used by automation Frameworks you can eventually automate this once you get to that maturity model okay we're also going to
use Splunk Enterprise Sim free edition right you can get this for free you can usually run it for about 90 days before sales rep is going to reach out to you and start yelling at you for something um but if you tell them what you're doing and why you're using it typically they'll let you go and and and let you go on about your way um the latest version will suffice this is a great experiment it's great for a home lab for students and things like that or if you just want to be able to kind of build out your own your own thing at home um there so four Enterprise right you know if you're actually in a shop or
something like that use your own Sim you know make sure you're you're tuning your stuff um where you where everything already is wherever all of your logs are um and then you're also going to need uh wmi just you know you needs to be configured for spunk Enterprise uh you need to have Windows Active Directory right um You should mirror your current ad force and domain levels please don't do any of this stuff in the pr domain um you know don't want to get those uh emails like hey I tried to do this in prod and something broke like not let's not do all that um but you should miror you know your current 84 and domain
levels and Group Policy should be copied over okay I did this in a groundup build so you know just trying to like get through the presentation and and and try to get through everything so you know it's not like the most robust Group Policy but ideally you're going to be copying over your real Group Policy uh in order to be able to test those things uh Powershell you need to have a general understanding a Powershell you don't need to be a scripting expert or anything like that um but you should be able to understand what you're running and why you're running it okay and then uh Powershell auditing should be turned on if there's anything we've learned
this weekend is that a lot of things are not turned on Jerry said it probably like 5 10 times um you know turn on script level logging and and script lock logging and things like that you know we need to be able to have those logs especially being on the defensive side of the house so uh Power shell auditing should be turned on for the domain include module and Block Level logging okay uh Microsoft Office can be a dependency depending on what Atomic red exercises you're looking to leverage so it just kind of depends on on what you're trying to do um architecture is going to be really basic uh Windows Server 2016 with adds installed uh 2016
Force and domain uh functional levels default domain policy where I have module and Block Level log game turned on right we need to be able to have that otherwise we're not going to be able to see much uh computer names I originally made this for security uh for secure Delaware so hence some of the names we're going to see seel dc1 and which is going to operate as our domain controller sect Del desktop one is going to be a Windows 10 Enterprise domain member uh going to have uh Windows 10 rsat tools on the desktop machine and then both machines have Splunk Enterprise with forwarding and enabled from sect Del desktop one to sect Del DC
no I I get it we don't put our Sim on our DC but for the case of this particular lab uh it just made sense to put it there instead of standing up another dedicated box uh you know the poor laptop can only run so much okay um so really really simple kind of log forwarding here coming from uh sectel desktop down here on the bottom right over to the DC uh they both have access to the internet because I need to be able to get to Atomic red to be able to get uh the actual tax scripts so what we're going to start with is kind of like a highle view of what it looks like
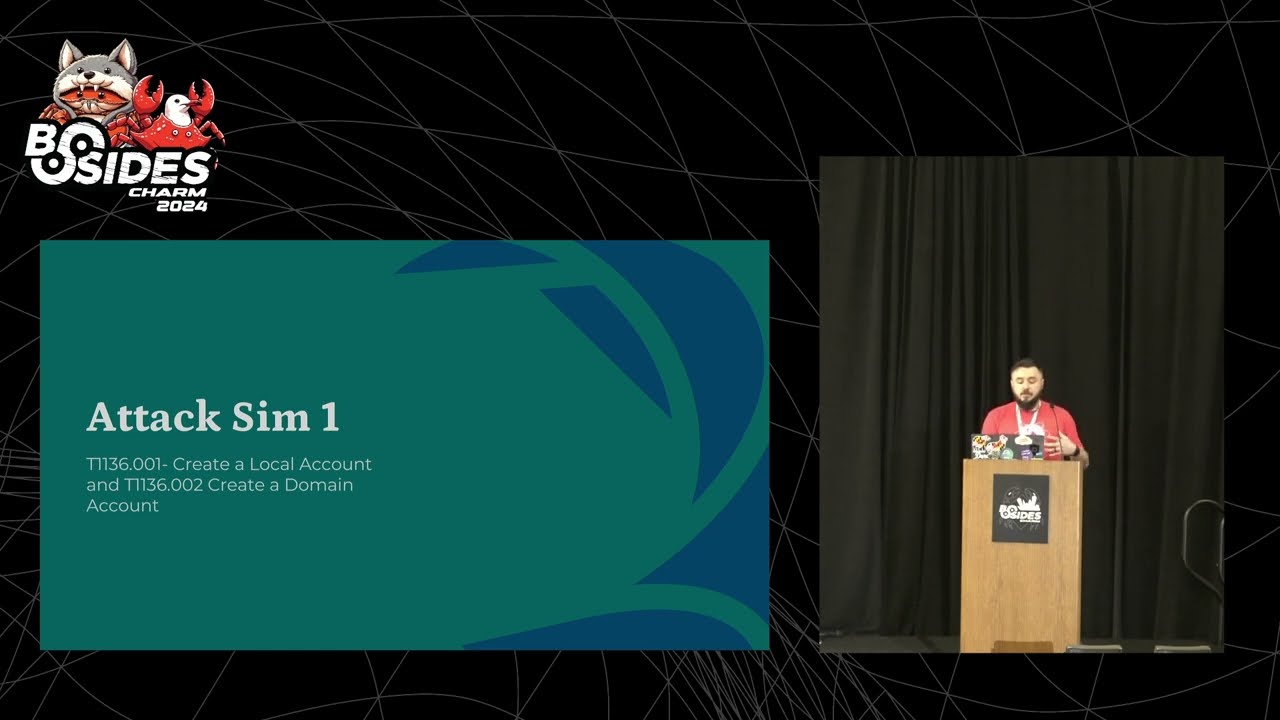
to go to Atomic red and and start pulling some of these things down uh we're going to start with like a local account and then we're going to work on like a domain account and then we're going to see what it looks like on the endpoint and then what it looks like on the Sim so creating a local account when you first go to um Atomic red or explore Atomic red it's going to have a ton of lists you know Red Canary has done a great job of just having a whole bunch of uh simulations already stacked out for you um everything's mapped the miter so you know everything everything's just kind of like lined up and then they
actually detail in each test what you're doing and why you're doing it and then if there are any variables in that test like U you know say like a password string or some string that you need to substitute in they clearly outline that for you so that makes that part really easy um so for the first one we're just going to be creating a user and Powershell so upon execution details of the new account will be displayed in the power s session uh to verify the new account you can run like net user or something like that okay so uh down there on the bottom on the bottom left hand side they have a couple of the
actual inputs uh that are required uh I just kind of showed you know kind of like some Snippets uh for t136 .001 which is you know basically creating like local accounts okay so running the attack all we're doing is creating a new local user with this um the cool thing about Atomic red is that they give you a way to clean up your own stuff right so once you're done this uh they actually give you a clean up scrape so you can go back and clean up everything that you actually did okay um so here uh all we're doing is creating a new local user uh not anything kind of crazy going on there with Powershell but what does that
look like on the endpoint right are we getting those logs on the endpoint level because if somebody's making a new local user on one of our Edge machines in our environment you know do you know can they do that if they can do that should they be doing that probably not uh so it you know if they're doing if they're able to do it and we're not and and it logs but we're not getting any alarms then that's a gap in our process but if we're not getting logs at all that's still that's still on us in order to make sure that we're actually getting the right logging so in this case right we we have the Powershell loging enabled
we can see the command being RAM and we can see the user uh being uh put uh in in uh local computer management so going to the Sim side going to the Splunk side right we can if we uh kind of filter out because you know there was a bunch of noise uh just between the two machines um but if we filter out uh with the host uh sectel desktop one and look in the event log and look for event code 800 right just to kind of filter down into this we can see the logs there on the Sim but did we generate an alarm in this particular use case you know the Sim's fresh out of the box it's the free
version so we don't have a bunch of pre-made rules that are already ready for us I got no alarms right so now we actually have to build out the the uh the flags essentially the criteria in order indicate on on those uh Fields or those things being met in this case we have an event ID maybe we're worried about uh uh Powershell being called by users that should not be calling Powershell at all right you know I can't think of a lot of opportunities or a lot of circumstances where somebody um in my operations team you know not security operations but operations for the business should NE you know should necessarily be launching Powershell for
any reason um so maybe that's the criteria we make the alarm somebody outside of it is running poers shell .exe for whatever reason okay so running the cleanup uh in this case so so you know quick summary right we just sat there made a local user fored you know made sure we had those logs locally on the endpoint then made sure we had the logs over on our Sim tool right and then we you know we would sit there and build out an alarm for it then we would take Atomic Red's cleanup script use that to clean up any residual mess that we would have put in our environment so moving on to a domain account so this script is a
little bit more involved um they have a couple more variables here in order to kind of get the command over uh to the domain controller okay but in this case it's still the same deal um username password are going to be the two main strings that we're going to be substituting in and then we have a cleanup command down at the bottom uh in this particular use case um I don't know I don't use really vs that much so I'm more of like an ISC person um so I leverage ISC you know filled in my strings the way I needed them to um and then went ahead and ran the command the command did give me an error about
password policy but I didn't have the password policy set on this domain controller um so I went ahead and it actually created the user you know it did complete successfully looking over you know kind of going over to the DC to confirm that the user was there I can see that the user was there everything completed successfully so it actually made this user uh without a proper password so what did it look like on the endpoint on the right side we could see the Powershell uh uh the Powershell logs on the endpoint indicating kind of what was ran how it was ran and um who ran it all of the good information that we need
to be able to parse out in order to be able to build better alarms for our environment okay going to the Sim again didn't really have any built out of the box rules but we can see the logs there so having the logs there gets us 90% of the way there we just need to start parsing the fields out that are relevant for this particular alarm in order to cause the trigger so that the SE Ops Team can can actually gain that visibility okay so looking back so we just kind of ran through that one pretty fast um so we created a local account we verified we had logs on the endpoint we verified we had logs in the Sim we
created a domain account we verified we had logs on the endpoint we verified we had logs on the Sim were we being alerted in this case no in your production environments I would hope you would be okay um you know but there's caveats what don't we care about we probably don't care if the IM team is spooling up users all the time right that's going to be business as usual activity that's our standard baau they should be able to do that but if somebody in the infrastructure side is trying to spool up users that's outside of their job scope we should get an alarm for that maybe we were curious if somebody uh you know trar was talking
about it yesterday uh people being left stagnant in global admins maybe we're worried about people jumping in and out of domain admins Enterprise admins schema admins right we can create alarms across you know across the environment you know to drop uh if somebody drops anybody into these groups right we can set alarms for that so we have that visibility so really you know do we care about the IM team probably sitting there making users that much n probably not really that's part of their job but what we do care about is if somebody else outside of the IM team is either making a user for any purpose or if they're actually taking that user and dropping
them into like some type of privilege access groups okay and then are we s in the logs in a format that can be parsed it's not enough to just send logs to some typee of log aggregator or some log bucket or something like that um especially Windows logs Windows logs can like a lot of the time depending on what platform you're using they come over in in a legacy format that's not easily parsable um so for the you know some vendors out there you know there's a lot of no I'm not going to throw out any names but um you can do like Json format and stuff like that in order to be able to try to get better uh uh parsing for
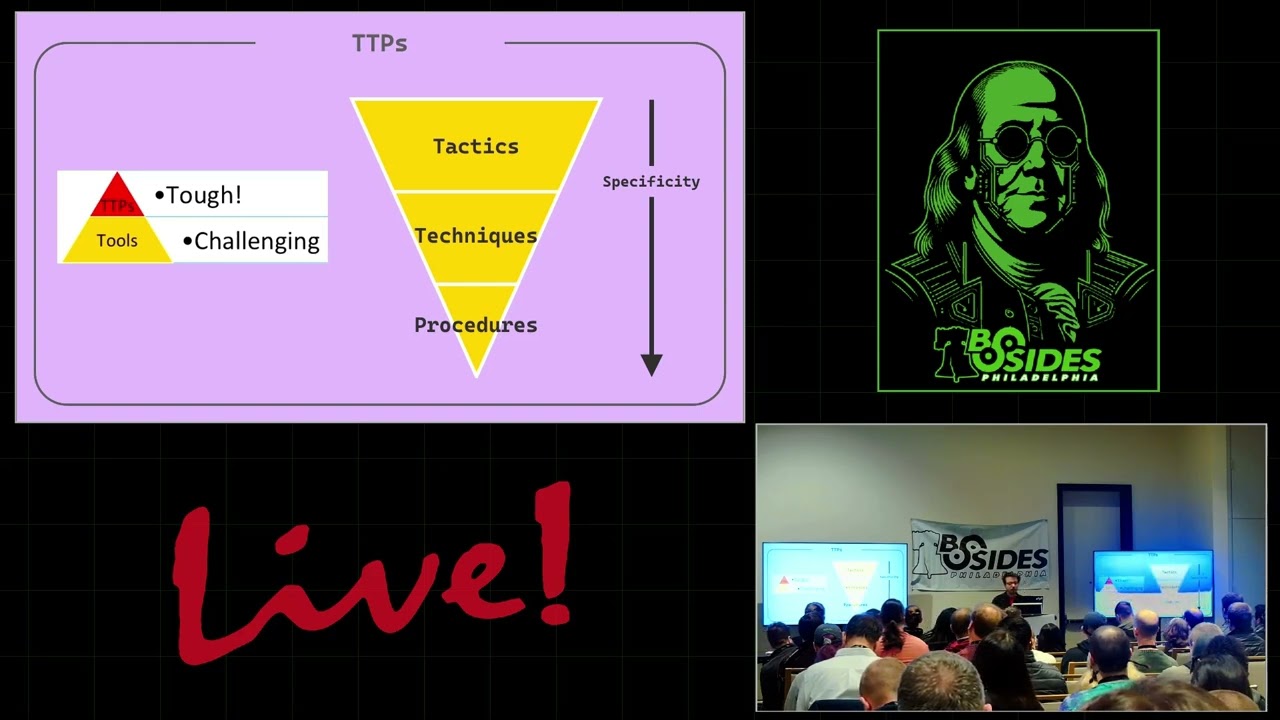
your logs um to be able to uh you know alert on on on on you know more Nuance aspects of the context of the alert versus or or the log uh versus uh something that's kind of generic out of the box okay all right so tax Sim 2 we're going to talk about Atomic uh uh T 1055 do12 it's process hollowing so right when we talk about process injection uh we talk about injecting a code into a running process uh when we talk about process hollowing we're saying that the process Hall is common referred to or performed by creating a process that is in a suspended state unmapping it in memory and then which then can be replaced by you know some
other malicious binary okay or something else or even a law bin if you want to okay so in this particular use case uh Atomic red is going to point you to their GitHub uh they have a GitHub for a lot of this you know especially for like the automation side of atomic um so in this particular use case this particular uh uh Sim is going to uh use Powershell to hollow out notepad.exe so that we can actually run Powershell through that process so that's the goal with the SIM or or or with this uh attack simulation so this test uses Powershell to create a hollow from PE on a dis uh with Explorer as app parent uh in this case I
substituted in notepad.exe instead of Explorer okay u a couple of strings uh set as variables that they want you to use um uh just basically binary paths and stuff like that so you plug them into the script and it does its thing um running the attack here I just did it here in ISC again um so ran the call and ISC filled in the variables and then sure enough I had a hollowed out session that ended up popping up on the right um it's kind of probably hard to see but then you know it's right in the notepad icon up there at the top um and so that's our hollow out session that we can use for U you know any type of
Nefarious actions you know running other commands doing recon stuff like that so we have logging on the endpoint right we can see that on the endpoint you can see me run Parell via ISC but this is not the end all be all at this point right we would have hoped that our EDR MDR xdr all the drrs out there right um we would hope that we have that uh that that this is being blocked by that okay now same question still arises do we have the logging on the endpoint you know does the EDR see it if the EDR sees it are we taking the logging from the EDR and the alerts being generated by the EDR and
are we foring them over to our Sim or or to some type of incident um manager in order to be able to kind of catalog those events and start building out attack trees and things like that uh it's not enough to just kind of have the EDR be like oh hey I blocked it and then and then that's it you know you what did it block why did it block it why is that person even trying to do that thing right um so it leads us kind of down that road of you know do we have the right processes and things in place again maturing this out so this is what it looked like on the Sim so on the Sim
perspective right it's not necessarily going to see the actual event law kind of pulling this out unless we had something like cismon like Jerry was saying uh prior you know cismon to be able to actually correlate those events too um so in this case we don't have that process uh visibility that's what cismon would be for but there's a ton of other EDR products out there just checking time uh there's a lot of other EDR products out there um that to perform that function for us right so we need to make sure we have it there in EDR so again you know do we have proper logging on the endpoint yes no um do we
have proper logging on the Sim is it making its way from the endpoint up to the Sim right do we have that visibility can we parse it is it coming over in a format that we can parse um are we being alerted by the EDR for this particular exercise okay what don't we care about well making a generic parser for powershell.exe or any type of like star. PS1 that's probably going to create a ton of noise for the SEC Ops Team okay we probably don't care that someone on the infrastructure team is running some type of Powershell command it's probably part of their day-to-day activities okay but maybe we care if somebody outside of the infrastructure team is running
Powershell like we said before so maybe we scope our bypass out to that group we scope our bypass to the infrastructure team but make sure we still get alerted if somebody else in the environment tries to execute the same thing okay so it's important to kind of understand what you do care about and what you don't care about from an alerting perspective because being a SE Ops member in the field I know what a alert fatigue is I know what it feels like and I know what it feels like to actually drown in alerts es especially when an event's going down okay um again you know already send in the logs in a format that can be parsed
it's not enough to just be able to sit there and say hey the logs are making it over to the SIM for whatever reason we need to make sure that we can actually pull stuff out of the logs and do something with it okay be able to Pivot off of that and then should we be forward forwarding logs from the EDR to the Sim alerts and otherwise typically yes right I I hate to use bud you know buzzwords and the single paint of glass and everything else right um but as a SE Ops member I know what it's like to have to sit there and try to correlate events across five different product lines uh
because we don't have that kind of centralized place to be able to go through in triage events um and and pull everything in whether it's for compatibility issues or you know whatever the case may be all right so this is another one where like uh you know the EDR is going to kind of come in place uh you know there was a good talk yesterday where they talked about kind of like dumping um credentials from Elsas and things like that um in this case right we're just going to keep this super mundane and scope it out to the actual registry uh and and the password stor is there within the registry so there are various
cache locations uh for um credentials in the registry typically in the Sam hiive or there Security account maner manager right so adversaries May search for common password storage locations uh to obtain user credentials passwords are stored in several places on the system depending on the operating system or application holding the credentials there are also specific applications that store passwords to make it easier for users uh to manage and maintain right you know kind of think like password managers and stuff like that you know if you got user storing passwords in Chrome or something like that you can dump that too right so once credentials are obtained they can be used to perform lateral movement and
access restricted information that's what we want to prevent so in this particular use case right super easy all we're trying to do is dump the registry save it off to the side um and we're looking for HK or or H key for local machine right we're looking for the Sam system and security hives okay so there's the three that we're looking to dump um really simple commands in atomic red right you can run these via uh command line and you can see it all all processes are kind of completing successfully over there on the right so I know that I got dumped and and uh in the quick snip down on the bottom in that temp folder uh we can see the
actual exports from running those commands now clean up for this particular use case is just going to go back and delete those files I don't think we need really need to get into that part so what does logging look like on the endpoint command Line's one of those things that Microsoft screwed up again and was like hey it's not that important to log it but you can do a lot of dumb stuff with command line you can call power shell and everything else and it'll run a PS1 stuff like that so it's important to be able to make sure you have some type of command line level auditing also going on because that's something else that they uh that they
don't you know enable by default okay so that was a particular use case here uh also need to audit process creation you know you know there's a lot of docs out there by Microsoft that provide you know kind of guidelines for default logging and stuff like that um so all great resources to kind of uh tug and play on so but in this particular use case right we used command line to call reg.exe in order to be able to dump uh those particular hives so what does the loging look like on the Sim essentially you know the same as what we see uh down there on the endpoint but again this allows us to take that that information out and be
able to parse it so maybe we again we don't care if somebody from infastructure is you know running like Ping and stuff like that from command line right we don't want to be alerted through somebody just trying to check General connectivity but maybe we want to be alerted if somebody outside of the IT team or the infrastructure team whatever the case may be is attempting to do the same activity right they probably shouldn't be running ping for you know whatever reason unless maybe somebody's kind of over the shoulder uh maybe troubleshooting with them or something like that but we can again use the noise that Atomic red creates for us uh to be able to kind of go into our Sim or
whatever our alerting uh tool is and be able to grab that data be able to parse for it and create better alerting for our environment right so again uh this is just kind of showing uh the process running and um dumping the uh the data from the stores okay we're actually doing really good I must be talking kind of fast all right so improvements po shell auditing by default it's turned off be as verbose as possible try to it can get noisy especially depending on you got in certain environments um but but try to be as verbose as possible uh script lock logging right again you know if we learned anything from the triyar guys
and and and and some of their presentations is that all of this logging is turned off by default script loock logging is also turned off by default if if you don't if you don't know you have it on you probably don't have it on so maybe go back and go check um command prompt logging guess what it's also not turned on you know just one of those things um so we got to make sure we have those things on um make sure we're logging all the things right um know what your crown jewels are and and be able to narrow them down but you know make sure you're logging your domain controllers make sure you're
logging the edge of your network and your endpoints um make sure you have some type of central logging utility have somewhere centralized that you're setting all the logs back to so you just have one place to go to be able to find all the things that you need okay and then I you know if if there's any environment I've ever been in um nine times out of 10 they don't have the level of web application loging that they say that they have um so having some of those app level logs or some of those is logs can be um can help reveal a lot more information and give you a lot more context in terms of what's
going on inside some of those applications um you know for those of you that are using ack as a service or some type of manage EDR function or um an mssp right you know their job is to protect you right run simulations regularly and test for their alerting capacity right make sure that they're providing the service to you and organization that they're supposed to be providing okay if they don't alarm work with them to build better parsers to prove not only the alerts for your environment but for their other customers as well I actually worked with a with one mssp at a prior organization um they didn't have this level of detailed alerting going on we just
didn't see it it was kind of upset with them um but worked with them in order to be able to build better parsers and what did they do they actually made that a premium offering and actually started charging their other customers to have a a premium uh a premium parser built out uh so they kind of spread that out um you know I I think it should have been part of their Baseline package but hey I digress okay um automate testing so one of the big things you can do with this like like it's like yeah we can go through Atomic red we can go through the site we can start cherry picking things that takes time right that takes time
it's a little bit it can definitely get tedious you can absolutely automate Atomic red out um so you can mature it out further by automating this and tracking the results to resolutions um there's a couple different ways of doing this
what
e
e
e
e
e
e
e
e e