Delivering Control Assurance Through Purple Teaming

Show original YouTube description
Show transcript [en]
hey good morning thank you for being here at besides Charlotte uh today Saturday uh and on track three of the conference today we're going to talk about uh attack simulation and purple teaming and how you can use these techniques to deliver control Assurance to your management team my name is Carlos Rodriguez I am the CEO and founder of fractional ciso of ca2 security we are a Consulting cyber security firm I have some products and with me today I have a great partner uh Ben thinker with uh on the fence I will let Ben who by the way I forgot to put here he is the founder of besides Jacksonville uh as well so very experienced in this
uh type of conferences so Ben what you introduce yourself yeah go besides uh so my name is Ben Fink I'm the co-founder of a company called on defend and I uh run development for a tool we call blind spot that doesn't help a lot helps a lot with the purple team Automation and some of the other preaching attack simulation that we'll be talking about today really excited to be here yeah and so man is more of the offensive guys I call him he doesn't like that when I call him that but I'm more yeah is one of the nicest guys I've met but I'm on the on the other side of my in my background I've been more on the on the
sock managing sock delivering uh security uh operation centers and leading those and doing investigations and instant response so here we're coming together to become purple so real quick we'll start with one topic that I run into a lot and uh purple team exercises does run into this as well which is all of these different type of cyber security test that all the organizations have to deal with um and they're all different and as are the organizations so we have vulnerability management which is as you know basically uh running scans to figure out what exploits are available within your environment without taking any action just that understanding what you have then you have the red team
side of the house which is more on the offensive side it's more on the attacking and using the ttp's uh to deliver payloads or or not payloads but deliver simulated attacks and see what they can they can do and you have blue team which is under protection the the instant response uh side of the house they are the first respondent for an incident and then we're going to talk about today's purple teaming is coming together as a team to work together and understand how to get better then we also have Rich and attack simulation which are certain tools that can be used to simulate attacks without really dropping any malware or payload anything you want to add on this then
yeah I you know I'll say one of the great things about purple team is it brings into uh sharp relief the value of a red team which is making the blue team better and that's it right and so by being able to do that we get a chance for both of those teams to work together with the same objective of making the the environment uh a little more resilient a little easier to detect attackers and uh I think what's great about purple team is you can really scale it up or scale it down uh to be what you mean it seems like a really complicated subject and I hope well part of what we're going to do
today is simplify but it really can scale to meet a lot of different needs and uh so I think people get a lot of value at it they weren't expecting yeah and by the way there are many more type of tests that we have to deal with right we have application security testing you know tabletops audits which are some uh kind of tests too a different type of tests but they are and so you know we understand that uh there is a lot going on here um in in that world but I think our goal like Ben said is how can we come together and make each other better right uh by by doing these exercises so
we'll start with a little bit of a definition of what a purple team is and according to um uh there's actually definition was on sites uh purple team exercise framework and it's an open engagement where the tag activities is exposed and explained to the blue team as it occurs Oracle team exercises are Hands-On keyboard exercises where red and blue teams work together with an open discussion about each attack technique and defense expectation to improve people process and technology in real time so all of this to me what it means is collaboration that is that right Ben yeah I mean it's really critical right and and what what really makes it fun is you know and other types of engagements
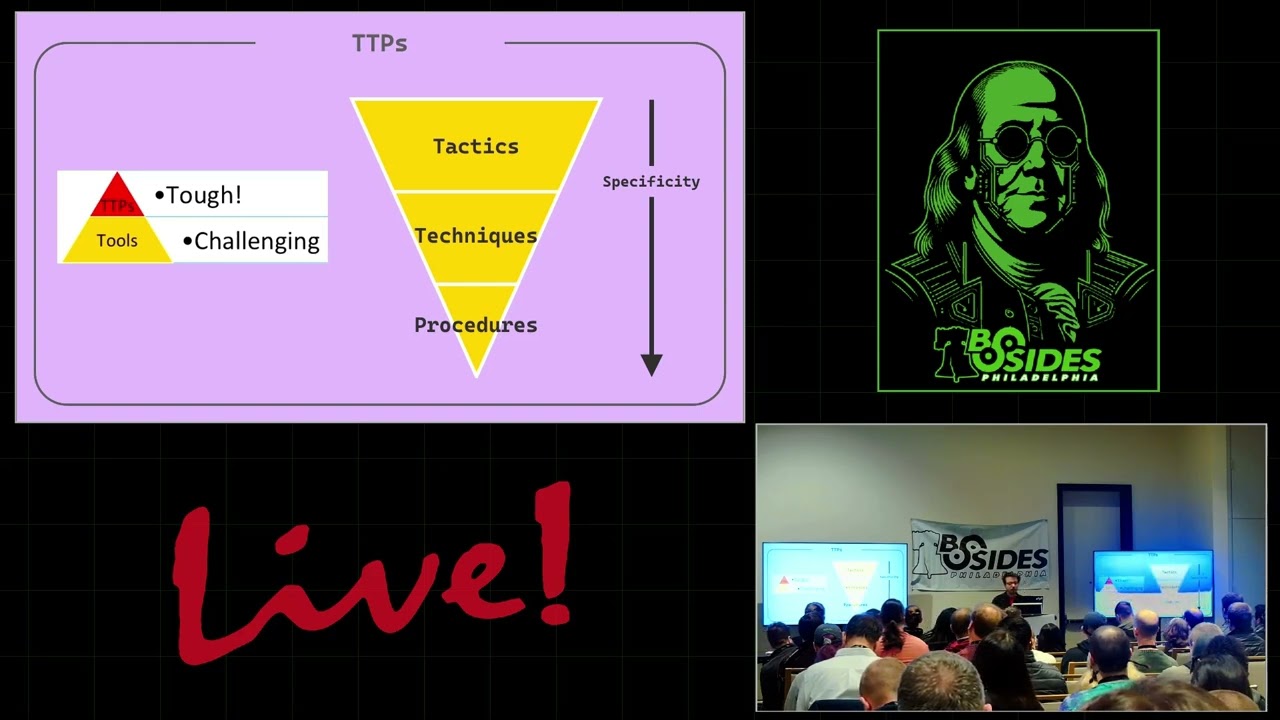
the red team does their work and then it's like the blue team side and they don't really communicate and that is where we lose a lot of the fundamental value that you gain by doing this kind of exercise yeah so the the red team in increment if I'm wrong Ben but the rip team rep team is gonna use ttp's techniques uh uh sorry Ben it escapes my mind the acronym uh tactics techniques and procedure by in for example miter uh attack framework to based on what they know about the environment deliver the the attack right while the blue team is does need to understand those ttps to protect to to hunt to monitor to detect and that's kind of
that collaboration happening so some of the things that uh differentiate from other type of techniques and and testing is it is in red uh purple teaming more strategic than than a pen test for example then and why is that I think that I would say that it what it really helps you do is understand both the capabilities of the security tools that you're using that the blue team is using to defend and the ability of that team to use those tools right so often you show up with a organization they have a lot of really fancy expensive tools and the team spends all day getting pushed around by the tools as opposed to using them uh to to you know
achieve the outcome they're looking for and so I think one of the great outcomes from a purple team is that you can stop letting that happen you can start figuring out like are these things valuable to us or not and like really figuring out like because the reason we have these is to stop attackers in our environment right that's it that's the reason and so now we can see do they actually do the job yeah and and again that collaboration is critical to understand what each other is doing and have a dialogue during the the engagement right I mentioned earlier TDP is the same TDP that you agree upon on during the planning phase which we're
gonna see later you're gonna use both from a different angle right um the attackers or the red team are going to try to exploit while the uh blue team is going to try to um defend and protect but during that conversation you know you are engaged in what are you seeing what's happening in the at this moment in time are you seeing anything right at all so to then like uh mention a few times that the goal is that we all get better and and we it's it's a training opportunity to understand how we can get better in our security depository yeah yep so what are some of the benefits again I'm gonna we're gonna talk about
sharing and dialogue and collaboration throughout the exercise um because that's what we're supposed to be doing is sharing that knowledge sharing the thread Intel so that we can get better uh Ben want to talk through this I do yeah yeah um you know I think one of the the great ideas here is like a lot of organizations receive some type of threat intelligence and I don't mean lists of domains and IPS that are bad I mean behavior-based things like we know for example Conti ransomware likes their initial payload does this activity right it drops the dll and and you know executes it and does a whole bunch of other things like let's see what that
looks like right and um one of the great things about a purple team exercise here is we can take an individual element of like a threat Intel report like say the fact that a threat actor uses a technique called kerberosting which is something that happens all the time on pen tests that organizations are probably not well suited unless they know how to do this themselves to figure out can we detect this and how bad is it for us and that is a great purpose of a purple team exercise because you can see it happening and then all these log events get generated you're like oh all of that because you did this one command over here really valuable to know I also
like the idea of us being able to use that as we develop detection capabilities for more sophisticated attacks when we run a purple team exercise if it's with an organization that's never done this before we almost always end up having to turn on two or three more data sources that we weren't collecting before and the really great news is now they've got a lot of telemetry coming in we can work with and even if it does even if an alert that we build does it specifically it's you know we don't specifically run that same procedure that the real threat actor does there's a good chance that they've got the data available that they can build behavior-based signatures from now
um and so that's that's a really great um benefit of the purple teaming for sure yeah and that's uh the trading tell uh we usually as part of that initial phase correct uh Ben we're going to touch on that later where really starting to tell us specific to your environment correct absolutely you know it doesn't do us any good to practice a whole bunch of Internet of Things Mirai botnet activity if you don't have any Internet of things you know on your network so it's really important to take a look at what is important for the organization that's doing the purple team that's hat that has the blue team what is important to them what systems
do they use uh you know what industry they're in what what are the likely attackers they're going to deal with uh and then let's simulate that or emulate that yeah there is a lot of uh preparation leading into the exercise and what I've seen um I'm going to kind of tell a story also from the receipt from the Cecil point of view when I I did this as a customer one time um but but at the end all this collaboration one of one of the key benefits is that is that healthier environment in that I'm not trying to beat you and show you up all the time right yeah or not only that but another key I think is
you know red team sometimes comes in with a report gives it to The Blue Team hey do you guys have this capsicle fix it talk to you later where that's not what we do here right that's not what we do here yeah in the Consulting world we call that seagull and Carlos yeah yeah exactly so buddy yeah and and that you know from the Cecil point of view from management point of view so I can once we have results and we identify you know those gaps and work together in into remediation I can also provide Assurance to management on the effectiveness of our controls and why we're doing what we're doing and uh you know continue to get better so we we
provide value the value of our investments and that's that's key because many times most of the time you know Senior Management may not understand why you're doing this well again it's a big part of it is delivering that assurance that controls are are working the way they are supposed to and when they are not we're gonna get to it and fix them yeah I I think that you hit on a major major value of this right the outcome of the purple team should be expressed in a way that makes sense to people who are at the stakeholder level where they really are more interested in the money in terms of either cost or risk avoidance
uh if you can do that then you've made a monster Improvement in your ability to get them to react the way you want them to and either sign off on some investment you're recommending whether that's money or time or whatever if you can convert that into this million dollars we spent on this awesome thing we found a black hat really only stops a couple of things and so it's only worth like 150 000 that is a bad Roi and that will help you either get rid of it or figure out how to make the full use of that tool right and that's a that was the message I sent when we decided to do this so I
want to mention also here purple teaming may not be for everybody right uh Ben I mean it may be that you're not mature enough or your red team and blue teams are working just fine and doing great so it's not something that that you always have to do right I I think that's right I think I think if you have a healthy mature blue team it's probably because you have a healthy mature red team who does this kind of activity I think what's more likely is if you don't even do vulnerability scanning on your environment yet and you don't have a good inventory those are some foundational things you probably want to work on first and then
we'll get to this as soon as you got those things lined up right um I think the I think the other side of that uh you know to your point Carlos is that some of these can get really big and be like whole attack chain scenarios which are fun to do having gotten a chance to do a bunch of those uh but those can take a long time to plan and like it requires a lot of people it requires a lot of time you can you can do them in much smaller Snippets but I do agree the there's probably like uh people who try to go to purple team and skip a lot of the foundational things
that well you're really going to need to take advantage of these anyways yeah and and in my case when I was a corporate ciso internal C so in an insurance company you know we had the conversation and we'll touch on that in the next slide in that uh one of my security managers told me well why why do we do this why do we need to do this we have other things areas that we need to improve first and I said okay that's cool uh so we got better in other areas when the time came it was still overwhelming because we were not a big team so the message is here you may be in that area where you're not
mature or you have a small team well you don't have to do it all yourself either there are consultant there are teams out there that can help you with this and be effective and that's what we did actually when we saw the the cost and the return that we will get in the the rapid and the speed of the improvements that we will be making it was a no-brainer for us and so we went uh with it we we had a good exercise with one of our partners and uh that was a one-time uh because that's what we budgeted for for that year but then guess what for the next year we budgeted for like less of these more often
because that's one of the things that you want to do right uh Ben is have some frequency in how you do ideally yeah when you do these exercises I think we should definitely talk about some of the best practices for purple TV Carlos do you think that's a good topic we should talk about uh absolutely so what what will be some of those so I really like the first one you have here you definitely want to have somebody who functions as like the organizer of the Activity one of the things that we see a lot of folks get wrong about purple team is not having enough of either red or blue on there right we need enough of the red team
side to simulate or emulate the attacker activity we're interested in we also need the blue team folks who can actually go log into the security tools that potentially can monitor for that stuff right and get that data we also need to make sure that we are falling into a useful scope and practice and like going through some sort of a Cadence of either how often do we repeat it or what exactly we're going to cover in this right what what is what is interesting that we want to make sure we talk about today is it is it making sure that like the process we have for responding to malware Works do we want to make sure that we are set in case
somebody rolls in and decides to use a whole bunch of Powershell techniques do we want to know um you know that that we have a uh working maybe managed security service provider who we pay a lot of money to every month to make sure that if these alarms trip that they let us know super super helpful to know how long would it take for those things to go I think you also something that gets lost a lot is what is the outcome of this need to be right does it need to be tracked as and this gets back to the project manager they need to get tracked as like things to fix is this a report
that's going to a stakeholder what are they going to care about all that stuff is super duper important um in the planning which your third bullet there is super super critical right um I wouldn't get too nuts like everybody again wants to dive into like ttps and and targets and things uh I I would I would say like those uh are important but like unless you have everything else ready you're not really ready to set those up yet right one thing about ttps is like there's so much great threat Intel out there now that you can use to pick things up um and that's something that the red team should really like once they understand the concerns that the
organization have if they're a third party red team that's really a lot of value they can bring us here's the things you should be worried about um and so hopefully that's something if you do engage in third party that that I would expect them to be not just like oh yeah here's things we know how to do really well they should be like here's threats that match your concern that here's what we think you should do right and and uh you hit a good point there and not not getting too waiting into the ttps and whatnot know that there are some Frameworks and excuse me so hopefully some of you do know that that you can use as your
guidance like miter attack I mentioned earlier or uh there's another one that and I remember the name of the the guy that came up with it but it's like the unify cyber kill change where he kind of brought the the miter and the Cyber kill change and other Frameworks together to simplify communication really to me that's what it does for us uh so use those guides to help you and don't go too crazy I mean you can start very basic with things that you have even seen before in your environment and started there I think one of the main things here is that feedback continuous feedback as you are looking into and we'll see an example of that later as
you're looking into uh the results that you're getting you have to have that dialogue right uh to to Norm basically normalize the data if you would then is that correct oh absolutely right and I think what's really important is um we're going to talk about probably some things not to do here in just a second but but I will say that uh that transparency is super clear here like if we're not um being very helpful and actually sharing this information like the attacker showing the red team showing their screen showing their work and the same on The Blue Team side being willing to pull up you know your sim dashboard or your EDR console and be like I mean
this is the data I have then then a lot of this doesn't work yeah let's talk about those bad practices though because well before before before we get there I do have a question for you and that is regarding the would you touch early on on the roles and responsibilities and and having enough blue and red but there is one area gray area I guess or purple maybe where you're working with this small team where they may not even have uh security team to begin with sure so the I.T or or it's just a one team insecurity mostly focus on on Blue that's I see that a lot so how how do you manage that how do you work with
those type of environments because that's basically most about the environments right yeah yeah so if if the constraint is that we don't have a lot of team members so they can't be on like a meeting all day long to do this and I think the way you plan to do the purple team exercise is let the project manager assign stages and times so for example if it's going to take the red team let's say two hours to work through the checklist of activity whether they're going to actually get it manually or whatever then you schedule them in the morning or whatever to do the activity and schedule the blue team in the afternoon to do the initial
threat hunts and then maybe the next day is the collaboration session so you can block it out and do it different ways you don't want to wait a couple of weeks because then a lot of the useful logs probably will have rolled off you want to do it pretty close to the window if you can um and it is especially important if you're going to bring non-security folks like like one of the things we see a lot when people want to test uh their capabilities to execute their incident response plan frequently there will be a network engineer representative whatever they call it because one of the things they'll have in there is if they are
failing to prevent you know the spread of some kind of malware what one thing you can do is just start turning off network connectivity to other segments to keep those from being impacted while you're dealing with the initial spread so it's important to make sure that you are if you're going to bring that person in that you have a thing for them to do something you're going to simulate and then a way for them to you know action their whatever their part of the checklist is so really important that the project manager lets the red team know here are the participants here are the things we want to make sure we cover all goes back to
those objectives right and how important in terms of targets is it to in your opinion an experience to try to do as much as you can with simulations for example uh on a on life environment like production environments uh with the right image of your uh production uh servers and laptops and whatnot how important is that super great question Carlos that is uh probably one of the most important things is when you pick a Target you pick a representative Target that is actually in your production environment it can be technically speaking a lab system but it needs to be using the same tools you use to do all of the other incident response right I mean you're
essentially doing a CTF in production when you do a purple team right now there's value in learning like the individual folks in this exercise learning if you're doing it like in a cloud range but to actually make the most use of this you have to use your environment with your security tools on your in your constraints right um and I think what we represent what we normally recommend to folks is that um the gold image thing is is interesting to us like if you have a typical like laptop that somebody in the finance team gets that's a great one to start with right the only reason we would say get us a different machine is
let's say that you have a wildly different EDR policy for Developers versus like accountants that that would be interesting and we probably want one of each the other thing would be is if you have like your organization is one that has either acquired others or whatever and you have like well this group still runs this EDR the other group that we acquired last year still on their other EDR well that those are two totally different things let's do probably at some point whether we do it both in the same exercises Up For Debate but both should be tested right yeah so we think of that as like if you're going to have one you need to know that this
is probably a prize applies broadly to your Fleet now eventually you do want to test other systems uh but yeah to get started but that's what I would say yeah very important and we'll talk more about that that how to do that safely later yeah so but there are some bad practices too then walk us through some of those yeah well I did mention this one just do it because yes because it's it's cool it's what everybody's talking about now is definitely a bad reason to basically do anything in life actually um if you don't share information Then I then you're not purple to me I don't know what you're doing but it's not purple teaming
um I think the importance here is that when we execute activity the whole point is you are correlating this activity equals these logs right some of them you may already have alerts for great some of it you may already block great but the whole point is when attackers actually do the things that they try to do how does our environment handle it right how do the tools that we're relying on handle it and so if you're not sharing it then like I said I don't know what you're doing um I do think this is important you definitely like if we're gonna think any team is better it's the blue team which is not how this normally rolls out I
think the other thing that we'll see uh is understanding that the purpose of this exercise is for the organization to get better which is either both of these teams or one team that has been hired by the organization right so flat out either way we're doing it I think if you want to stay on target like there might be other juicy things you see I think you should note those and either and you know put those into another engagement something that is kind of along the same lines of this that we see sometimes is that folks want to treat the miter attack Matrix as a like a bingo or like a checklist and that is not what that is like the mega
attack project is an attempt to categorize things that attackers do it is not a comprehensive list of everything an attacker can do right and even if you open up an individual technique there are dozens of ways to execute that thing so to say that you are like good on one of those uh it's like there's an infinite number of test cases how could you ever accomplish yeah the point is that you test against those and you're understanding that you do collect data that allows your team to hunt those things down but to say that you're good on one of those I mean you could say you're good on a test case but you're not good at a minor attack
technique right I mean that's that's like saying I'm good on science and sharing information starts very early in the process not just as you're doing the exercise like yes once it goes together you gotta Define your targets your take the piece whatever what is it the goals together and share with each other such that you have that collaboration as you navigate through the through the exercise but it starts starts way before uh during that planning session and even the preparation and especially if you are if you have an internal red team they probably know what your security tool set is but if you have an external renting that you're bringing in to help do this purple team and they ask you
like what security tools do you use don't don't not want to give them that information it's very valuable when we come into run purple team exercises we know based on the EDR you're using what what test cases we're going to use that we know will get caught and what test cases we we can use that we think will bypass it that is valuable information for your team to know right and if you don't tell us that then that's just less prep operation we can do to be prepared for the day of the exercise to give you the maximum value so yeah sharing information totally agree both ways blue show that the the right see everything
and the red should absolutely make sure blue sees everything they get all the artifacts they get any scripts you're going to use all of that stuff has to go in they need to see all that stuff yeah so now let's walk through being bringing this together and walk through the uh uh how the process will go from a practical point of view I'm running a purple team exercise so it starts with planning we mentioned that we mentioned all of these but here is also uh to band's last point you know have your uh security stack inventory right well what is it what are the tools that you have have those available um the project coordinator project manager
exercise coordinator should be leading here uh assigning roles responsibilities and then um selecting that what tools are you going to use right that's critical as well Ben correct for actually going at it let's perform the attack quote unquote or or the simulation so Douglas uh we're gonna get more into that in a little bit but talk us through that as well yeah you know so one of the things about picking the the way that the red team is going to operate really like once you've figured out what you want to test and the types of the objective of the of the uh game you know it's really important that that you're bringing the right thing so for
example we see the use of cobalt strike in a lot of data breach reports right where threat actors think Cobalt strike is so great that they use it themselves if the customer's concern is they want to sell could we detect Cobalt strike beacons running our environment and you roll in and you've got like you know other great C2 Frameworks that are not Cobalt strike that's not going to be very very successful the other thing I'll say is that there is Super Value in the ability to run this test over and over again in the exact same way so that as you make changes and improvements you can track it identically so there's all there when
we talk about how we get into some of these later stages there's a phase for manual red teaming and there's also a phase for like highly repeatable very rapidly generated activity so that you can sort of build a Baseline and that you can rerun that Baseline frequently so if you're in the middle of tuning it doesn't take long to reruns like oh yep got the alert now great that tuning that works that's the right config or you know we tuned these three months ago in a purple team workshop that we did let's make sure this still works right because now we want to work on new stuff we don't want to always keep going back to
the same so you can do that if you have an automation platform available uh that will help like really raise the floor of what you can execute in a purple team for sure yeah and and then planning goes almost alongside with preparation and preparation is more of the again what tools we're using what uh trade intelligence what do we know about our industry our environment that that we may be at risk what are our vulnerabilities our security controls and the agreement on what it is that we're gonna try to run and attack anything else in the preparation foreign then you go and you want to again this is a collaborative conversation Ben mentioned some of these do we have
the proper Telemetry for what we want to test right that's critical correct big time and I I really like that third bullet there Carlos the discuss expected results there's a lot of times when you'll work with somebody who's a as a like a red team consultant and they are they're they're like we want to test our EDR implementation to make sure that it picks up things like great well what do you expect it to pick up and that's where like all of a sudden you realize I've never thought about that like I just knew I had to have an EDR I didn't actually think about why like what I expected to do I expect it to log that
or alert or block that I don't I guess I expect it to block that super duper helpful to know that now that's that EDR is kind of a big topic there may be really specific things like if you get into cases where you're talking about data exfiltration and the customer believes they have spent a lot of time and money on some sort of a data loss prevention solution and they're like I believe that if you were to pick any of these documents that are watermarked or whatever they call DLP things these days that you would not be able to exfiltrate them out of this network that is an awesome expectation right now we have a
lot of ground we can figure out okay so any getting these documents out of this network constitutes like that's an edge case they didn't have a chance to look at yet and that is valuable information form or they can validate that yeah that totally works the way we thought it did they tried all these different cloud services that didn't work they tried all these other things that didn't work they couldn't send it directly via mail what whatever the solutions are right and that's where the red team needs to get creative uh and take that tactic or that technique data exfiltration via you know standard services and be like okay let's go get to get to work on that right
yeah and then you get to the day the big day is here so walk us through that day uh and I want to point out that we are like halfway through this chart and we are just now actually at the exercise yeah exactly so there's a lot more stuff we planned before yeah yeah so the executing is actually the fun part I mean that is like literally the CTF in production that is where the red team who has been working on all of the things that we came up with all these objectives all these things we wanted to test and they have built out their test cases they built out their plan they've come in the team who is going to provide the
blue team side of this is all logged into the tools they're looking they're ready and off we go right um and I think what's going to happen here is going to be uh some things will go exactly the way we expect them to and a bunch are going to go wrong yeah one way or the other I think that the red team didn't expect to to fail will fail and I think the blue team didn't expect to fail will fail right of course which brings us to the next one right which we keep working our way through the different ttps recording the outcome right right and right and then you continue to monitor throughout the
exercise right yep yep and then the the real thing is we document the things that we learned where there were gaps in our ability to detect or mitigate something really important also uh one thing that that shows up a lot in these these plans is making sure that you document um the exact conditions under which the tests were executed like on what system as what user where their payloads involved um all those other things that you need to know so when you go back like well you know you ran as a local admin all these other things so we now know like that's dangerous but if we go back and we rerun this as a standard
user maybe none of that stuff works and that's not to say that that admin test isn't valuable it's definitely is and now you have additional things you can leverage when you go back later to be like how can we build better alerts on this you'll be like I know if we bring in the data that the user account is an admin that is an alert and this other one isn't right super valuable data yeah yeah and then of course you go and remediate uh or start your remediation activities and then really you start all over the next hopefully in the next quarter or or with some frequency and and one thing there that Ben mentioned a
few minutes ago is do a quick check on one of the of the ones that you just did completed again just to make sure that nothing has changed so yeah yeah this is continues yeah and as a follow-up like once you've do that implementation the next purple team can include a little section of like let's make sure that implementation worked you can also have a section up here stuff we fixed three months ago let's make sure that still works and now let's get to the new fun stuff yeah so now we've talked a lot about uh purple teaming let's talk about you know the one of the tools that can be used for that which is
known as bass bridge and attack simulation which is really um tools that you can use to simulate the attack vectors do it in an automated basis and so it becomes that pane of glass right during the exercise can you talk us through this sure absolutely so the first thing let's talk about there's the idea of simulating an attack and emulating an attack emulation is what you normally get in an automation platform but we've got a list of things that we frequently see attackers do we're going to run through those and that is the that is the part that I was saying like a blue team person uh who does who maybe doesn't know a lot
about creating the threat actor activity like they're not a red teamer but they they work in the sock should be able to kick off a emulated uh campaign that looks like an attacker to validate that that their tools are still working so that should be a definite part of it simulation is really the manual red team side like you the red team comes in they've done their research they know what industry in and the things you're worried about the tools you have and they they bring the same level of inventiveness that a real threat actor would right to to the to the Sim situation a lot of times you'll see in the marketing they'll talk about
continuous security assessments what it really means is you can run it a lot right so it's not like a pen test where we ran it back in April and we're still working off of remediating 700 pounds in April even though it's September we we want this to be more up-to-date and all the time because obviously things are changing and you know just because your EDR worked a week ago does not guarantee that it works today uh so anyways the ability to run this thing in an automated manner is super important um especially if you can like schedule it and if it's a baseline activity where it's going to run stuff and you know that it's going to be doing those things
super helpful and again to the point of the the blue teamer who might not know how to execute a process injection attack but they sure know how to build alerts looking for it that is super duper helpful now they don't have to know how to do it they just know how to go in and run the automated campaign I think it is important um if you're going to use some type of automation one of the values of that is when you expand your scope of what you're sampling that goes from being something and now like a rate you know a red team or doesn't need to take another two hours to figure out how to connect
to this machine in the Pittsburgh office right they can just you can use the any type of automation you've got to do the attack emulation run on that and now you can see like do we get the same outcome there that we do like in the main Center where we've been running a lot of this testing um if it's automated the chances are that you'll get through it a lot faster so as an example if we were to manually run through the activity we do in a campaign would probably take anywhere from 30 minutes to two hours and we could typically do it in about 20 minutes with our automation right and so that gives you all that extra time now
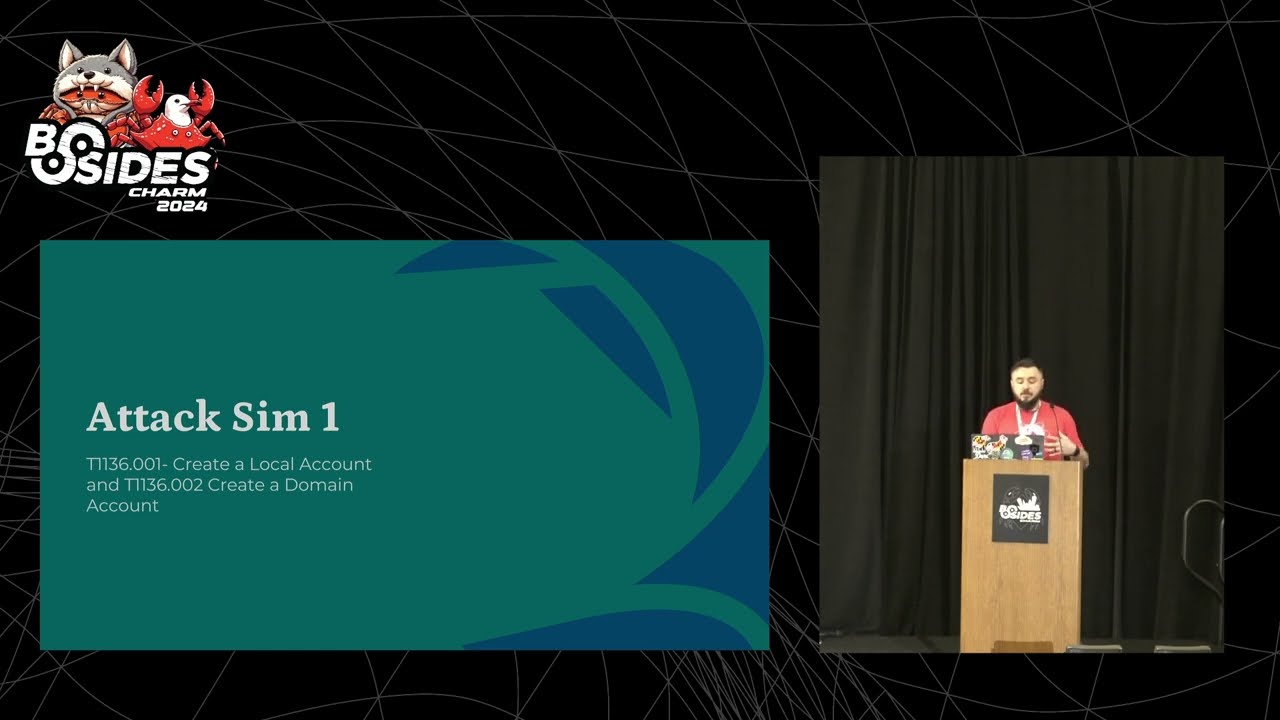
that you've gained back is collaboration time how do we make the defenses better um and I want to be very clear here when we talk about ttps we just mean threat actor activity and so hopefully by being able to test a larger set of that you are really testing like lots of different ways of Express expressing those ttps so like an example I use I use a lot and um there are several different ways to create a local account right a local user account right you can use a regular command line you can do a Powershell command there's other things like apis calls you can do super important if you can script all those up and have them in
your automation platform now you can test all those different ways so if you have an organization that is just monitoring for the like net user ad stuff like that'll text that but it won't detect any of the others right and so it's really valuable to do that so that's a super important differentiator there um I think the you know the the ability to validate that your controls work the way you think they do is really one of the main features of having any kind of automation right that you're going to put together a suite of actions that you expect every one of these to be blocked or every one of these to generate an alert and that way you go sit down you
run it it does its thing and you go look in your spunk console wherever you got there and you get like alert alert alert alert you just kind of work through the checklist and like yep everything's working today way better finding it out that way that something's not working than having a real breach and be like how come the thing didn't work that stops the bad stuff and you realize it hasn't worked for three weeks yeah I agree and that's that's again from a management point of view that's that's the duel there if I can uh instill confidence in management that we are investing in the right things and working you know effectively then I'll
make a lot of friends as a season Carlos you help a lot of organizations that have had some kind of security incident in the past my guess is that if you had to like put a number on it it is about 75 or maybe more of those organizations that had like a technical security event thought they had a thing that would detect an alert or block the thing that happened and they were super surprised when it didn't right would you say that number is about right yeah I would say so it is incredibly uh is inside we see it all the time and and we will talk about some of the use cases soon but even when you do a like a
tabletop exercise and start seeing yeah like you know the combination of the tabletop with a tool like this and start seeing what could really happen then it doesn't eye opening for many yeah absolutely so here are some use cases right uh so using of course these tools for your exercise we've talked extensively about that uh we talk about making sure that you're running in production environments because of what Ben just mentioned because it's the rate of failure is high and that's why also you you have a you know defensive depth or call it whatever you want to call it uh but that's why you have different layers of controls and then you know you you
have that real time uh conversation right man I think that's one of the most important things here yep the real time like the delay between I just ran this attack thing and then the alert doesn't show up for 20 minutes right I think a lot of people without doing this type of testing assume that that is instantaneous right but there's like there's delivery of the log events to wherever the alerts get generated and then a lot of the places where the alerts get generated there's not real time they like batch them up and like every 10 minutes this search runs and if something shows up in the search there it goes but it's important to know how much lead time
does an attacker have once that alert pops so you know like oh man they've already been doing this for 15 minutes I got to get after it um yeah yeah and or even you know when we get alert uh fatigue we do get the Lord but we don't take action on it because oh my God it's another one constantly so now you can see that the which ones are the ones that you need to pay closer attention to right yeah go ahead oh yeah go ahead Carlos yeah this is an important one no well I just mentioned that when you when you do that uh with the tabletop exercises and depending on the level of
the table top but you couldn't even have some Senior Management around and see what happens and that's a big one I think it's really valuable to use some automation to do this in the middle of a tabletop exercise because most of the time in my experience especially if you have like a senior uh executive management team who's there they if they have ever observed any kind of like I.T outage it's almost always been like an accidental like they pushed a new patch and it brought things down very rarely do they get to observe the way that like threat hunting works and it is a little bit different um and when you go to those if you don't
have like something for the threat team representative who's there to actually go do they just make Grand statements like oh yeah we would identify all of the command and control channels and use isolate all those computers and stop the spread of you know whatever the ransomware is and you're looking on your on your script you're like well I know that's not the case because the next step is it's about to get worse so you would you have not done that so rather than be the jerk and be like okay I get that that's what you think you would do but it doesn't really work that way be like fantastic there are currently three or more
executing action activities here are the iocs for it but see if you don't see you find it right it's and I find that they actually enjoy that too and even though they want to look good in front of their bosses and their bosses bosses uh by maybe like struggling and showing the lack of ability for them to like very quickly get to the answer it kind of reinforces probably a message they've been sending before anyways about needing better teams or something um I do want to go back to the first item there the running purple team exercise is using baz I will say this uh they can be a like accelerator but I don't think that you can get the
advantage of a red team exclusively using a breach and attack simulation tool I think it allows you to again Elevate the floor you're going to run a lot of activity that you've either the red team has already gone through and validated is important and that you've tuned to uh but I don't think if you're planning on just using like buying an expensive basketball and that being your red team you're probably not planning on having a very good red team component in your purple team exercise so what we like to focus on is the ability of like automation so we can get through a lot of like the stuff we know we want to get through and then being able to augment
with some manual activity and some new activity uh that we kind of like keep you know keep moving uh a little more to like expanding the capabilities of what the team is is able to detect and block but I do think it really raises the floor of what you can get out of a purple team exercise by having some kind of Automation in there yeah and on to close these on the other side of that tabletop exercise when I run them without a tool like this then I 80 of the time 70 of the time at least I get that it or security team telling me that's not going to happen here because we have cross strike or
Sentinel one or whatever whatever we have and so it's not going to happen I'm like well yeah so do they they have it so it gives you that other piece right but um so we want to play real quick we had a few minutes left um a quick video on one example right a use case uh in this case uh Ben is going to run us through a process injection um example so I'm hoping that it uh does play I'll give a few seconds of quiet time just in case we need to edit
um
hey everybody today we're going to talk about kicking off a simulation in the blind spot platform what we call a campaign and today we're going to do it using a process injection technique something that you've probably heard about and one of our goals is to make it very easy for you to replicate that well no matter what simulation type you want to run inside a blind spot kicking that off via a process injection method so we're going to scroll down here we've picked the maze ransomware simulation that we want to run and we'll find our 64-bit for Windows process injection simulation execution type now a couple of things in previous years we talked about some of the different
execution methods involving us putting part of the payload on disk before we can run it one of the main differences with this one is that this payload this Shell Code payload that we have here is never going to touch disk it's only going to live in memory when we kick this campaign off it's going to happen the blind spot agent will download this Shell Code that we have here that represents the beginning stages of this simulation we'll inject it into the process Target that we're about to select for it and all of that will run in memory we do publish the hash values of the Shell Code but it's hard to say that you'll actually see these in memory
but the C2 domain is the correct domain and is the indicator that your team can use to find out what is going on or at this simulation where the simulation May exists so if you've seen some of our previous campaign videos you'd know that there weren't a lot of questions to answer we have a couple more on this one so let's go ahead and get this one started so we're going to name this something in this case I'm going to name it May's Pi demo for process injection again the payload and execution options already selected for us so we don't have to do anything there we do have to make a couple decisions though about what
method we want to use for process injection hey what Target we want to go for the agent currently has five different methods using the windows apis of creating the process injection execution method essentially requesting access to another processes memory space putting our Shell Code in there and then running it all of these work and I would encourage you to go through them and take equal turns running using different methods just to see if your tools on your endpoints react differently one of the things that we have the ability to do inside of the commit the tool here is to specify the Target that we are going to inject our Shell Code into now because when we built the blind spot
tool we had no idea what systems we may end up running some of our simulations on we always want to keep an eye towards safe and reliable execution of our simulations without impacting the production workloads that that system may be running so whether this is a laptop of one of your colleagues or a domain controller somewhere in your environment we don't want to cause a problem with a process that is in turn used by something that other people are relying on so we're actually going to start a new instance of the security health assist tray app and then we will inject our payload Shell Code into that now the security health Assist tray.exe app if
you're not familiar with it is the little app that Microsoft makes that goes into your system tray and tells you if your Windows Defender is turned on or not which we see that ours definitely is so we've got everything in here that we need now we gave it a name we picked that process injection method we picked that process ejection Target we are going to submit this and now this Pro this campaign is going to sit and wait for our blind spot agent to check in with it and be ready to run it so we'll give that just a second while that is queuing up we're going to pull up our task manager so that we can see as new
uh processes are created so we're going to scroll down here into the S's and we're going to look and we see the security health systrade.exe right here this 8760 that's the one that's actually running that should be on our machine we're going to let this run for just a second and we will wait and see when the new security health assist trade out XC app pops up we'll notice some big differences about it well we're waiting you notice this one which is the real one the one that's the windows started when it started up this has 1.88 megabytes in use in the memory space which is pretty good it uses basically no CPU you're not going to see that
really uh spiky numbers here in the process hacker we're going to give this just a minute and we'll notice oh look there it is another one has already popped up the security health assist Ray app it says 11 584 is the thread you'll notice this is already bigger than the other one let's take a look at our points about Asia can we see sure enough stimulation injected using the creative method running a process ID 11584 so there it is I think Windows Defender turned on we've got our app here and it's already continuing to grow in size if we go back to our blind spot interface and refresh the page we'll see that this is running
and we can open up our campaign status model and we can see as things are beginning to run on the campaign that's it for this video come back for the next one we'll talk about how to score one of these campaigns once it's done thanks all right so can you hear me again yep we can hear you okay so let me go back so we had another video but I think we've uh God now we're running our time so the next video will be a score in that campaign how you will manipulate your result your results so go and take a look at it uh we'll post the the a link to that in Discord
so you can grab it but it's also available in the presentation and and then our last uh item here is some resources that we're adding to the uh for you to to have and continue to learn about purple teaming with that uh thank you Ben this has been a great conversation I hope uh everybody got something good out of this presentation been any closing remarks oh no really appreciate it Carlos and thank you to B-side Charlotte I always love chatting with uh provokes and especially supporting other b-sides so hope everybody's having a great Saturday thank you all have a good weekend