Modern Threats: Preparing For A Dystopian Future

Show transcript [en]
modern threats, dystopian future. My name is Serhiy. I'm from Ukraine. You can see my Twitter. Many of you subscribed already.
Or seen my tweets anyway.
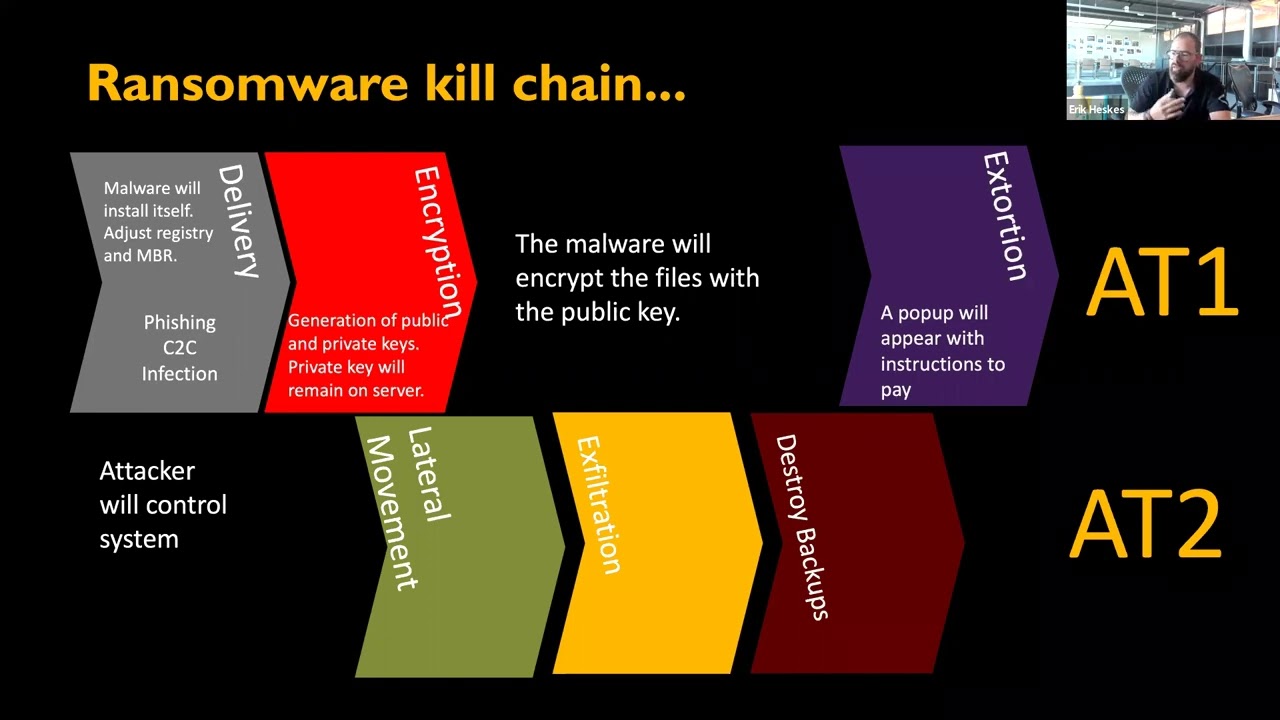
Unimaginable data leaks. Modern threads become sophisticated every day with unimaginable landscape of data leak and information infiltration despite various protections we might have in place such as antiviruses,
updated workstations, EDR or some enterprise solutions that can protect us. And recently I dived into threat hunting and was overwhelmed with potential that adversaries have in the offensive arsenal. They frequently focused on remote code execution and tend to exploit victims infrastructure to retrieve all secrets they are interested in and in a way that every year we have more and more CVE assigned and critical issues that becomes public we can find easily exploit to different kind of vulnerabilities SQL injection, XSS attacks
and yeah for someone it's just a game
they practice like capture the flag events different competitions and become more and more powerful every day and not every exploit be public obviously and hard to say if your updated system vulnerable or not and Companies invest budget into protection and have ROTA of incident responders to monitor the network traffic. But for us, who monitor our traffic or even who enable DNS log on their workstation? by default it's disabled and even when you enable it you need time to investigate if something happening on your system something unusual and with all this overwhelming information it's hard to deselect
what is good and what is suspicious in your system.
Your emails, messenger history, saved files, passwords all may occur in hands of cyber criminals. How can we protect ourselves and minimize exposure of data breach First point would be to cite Sun Tzu Art of War
Know yourself make assessment of everything you are going to protect your mobile phones, tablets, USB drives, whatever you have important in your system you need to have listed because it's hard to protect when you are unsure what needs to be protected or even more if you trying to protect everything it's impossible so you need make some preparation risk analysis and evaluation how much you are going to invest into security
next step would be removing all sensitive data from internet connected devices cloud storages and if you need to save
the data archive it with strong encryption for example your email account may contain a lot of historical data that you never use anymore but when it becomes public you even wouldn't notice because two factor authorization not implemented or it has some faults that allow a thread actor to get data anyway. So if you don't need some emails, all emails deleted and the same with files folders. pictures, screenshots, whatever you have that you don't wish to become public tomorrow. Delete or encrypt.
And last but not least, you need to implement control lifecycle of your data. Have some logging security controls. with restrictions role based or some different security controls that have implemented implementation in enterprises but you can implement for your home workstation and for personal devices also would be have to follow some recommendations from security agencies public security agencies they have guidance and advices how to improve your security controls for small business and for personal use any questions please yes
Companies invest big budgets to protect resources and have
other resources to monitor any anomaly, any unusual activity and track what is going on. And they constantly improve this process. But for us, for personal use, it's only us who is responsible for our data. And you need to be prepared. Whatever controls you put, all your files will be public and indexed by searching engines. Yeah.
Just try to minimize risk exposure and follow best practices. Any other questions?
So to summarize, be prepared that all your private information
be public tomorrow or in the nearest future. because more and more power on red team side. Red team should be successful only once and blue team should monitor life constantly. One mistake and files gone. Practice data sanitization.
lean up after yourself and improve your security portion. Thank you.
Yeah. A few hours ago, I didn't expect I'd be presenting. Thanks. James quickly created this presentation and yeah sure I hope you like it thank you