Cyber Cat & Mouse: Law Enforcement Vs The Dark Web - Jordan Powell
Show transcript [en]
[applause] Uh hello everyone. Um I didn't expect so many people to come to this so thank you so much. Um so quick introduction who am I? Um I'm John Powell as we said. Um I'm junior penetration tester at KPMG. Um I'm a freelance researcher. So I primarily focus on vulnerability dislo programs and I also research in niche topics which is hence this talk. Um I'm former president of the lefthquac society and I studied cyber security and digital forensics. My main interest areas are penetration testing you'd hope so for my job. Uh threat intelligence and I like me some malware. Um on the side I like to do gym art gaming and warmer. If anyone fancies a conversation
don't know what to talk to me about just ask me about warmer can go on for hours. Uh so quick disclaimer before I proceed. Uh just want to make absolutely clear that this talk is purely myself any of you shared or thought purely mine my research everything this is all me it does not relate to my um fellow colleagues or KPMG so this is not related to KPMG is entirely my own cool so quick introduction what is the dark web super cool hacker stuff do you have rooms hire a hitman of drug forums do you need elite hacker field to access Let's slow down. Let's let's break it down. So, [snorts] I'm sure a lot of people
have already seen this, but this is a very basic layout. So, you have the surface web, which is just normal. So, like Google, Facebook, Instagram. Deep web, which gets confused a lot with that web is non-indexed information. So, like legal documents, private forms, research, that type of stuff. And then you have the dark web, which is just private communication, that type of stuff. So deep web and dark web gets confused quite often but they classified as different things. Um so the dark web is actually primarily a lot of people are associated with car which is you know the most popular one that's scene but there's actually multiple projects that fall under that. So there's the uh
invisible um invisible internet project freeet and there's loads of different ones. So this talk will primarily just be focused on tar just discuss in that one. So there's a lot of stuff under the umbrella. So quick introduction to top anyone's not aware of it. It's known as art web that's popular one. Uh it was initially developed by the US Navy in the 1990s. Um so it was made by US government. Uh it operates based off nodes and volunteers. So people volunteer their network and the bandwidth then to help run it. So it's grown over the years increased. Um some of sponsors of it include the US government, Zcashes, loads of different ones. again obviously wonderful
volunteers. So to our browser looks like something like this. So it's just bog standard browser you access it and you can go to this site and it'll basically say you are configured. So in this example this is a tall site. So if you look at the top the URL it has onion. So an onion link it's um there loads of different sites used by normal companies. So, Facebook had one, uh, have one. Um, newspapers have one. It's a right mix. And in this case, the FBI have one. Um, so not everything on the dark web uh is bad and evil. A lot of it is, but not all of it. So, if you want to understand how to
work, very basic way, easy way to explain it is onions, always onions. So, this is a very basic explanation. Um, so imagine with a tour client, you want to access a tour site. You pass through these nodes, adding their own layer of a layer of onion encryption, get to the destination, passes it back to relay all the way back. Again, very basic explanation, very poorly explained, but it gives you a rough idea. So on the network, there's obviously a lot of different um cyber going on. So you have breach forums which is cyber crime which has been seized multiple times. Uh ransomware sites like Vice City, Hydra Market. Uh Silk which got seized on the
original dark web drug sites and has had so many spin-offs now. Uh XSS Ice which is a Russian cyber crime forum if anyone's aware of it which I think they actually recently got seized. Um K another ransomware group and Acubus market which I might be incorrect they either got seized or they did an exit scam. Um so you quickly pick up throughout Starlight it changes a lot the uh the like the framework how the environment is there's con sites getting taken down there's constant new groups grow. So obviously due to this there's a lot of seizures. Um so for example in operation talent that took down cracked and nulled um which was cyber crime forums
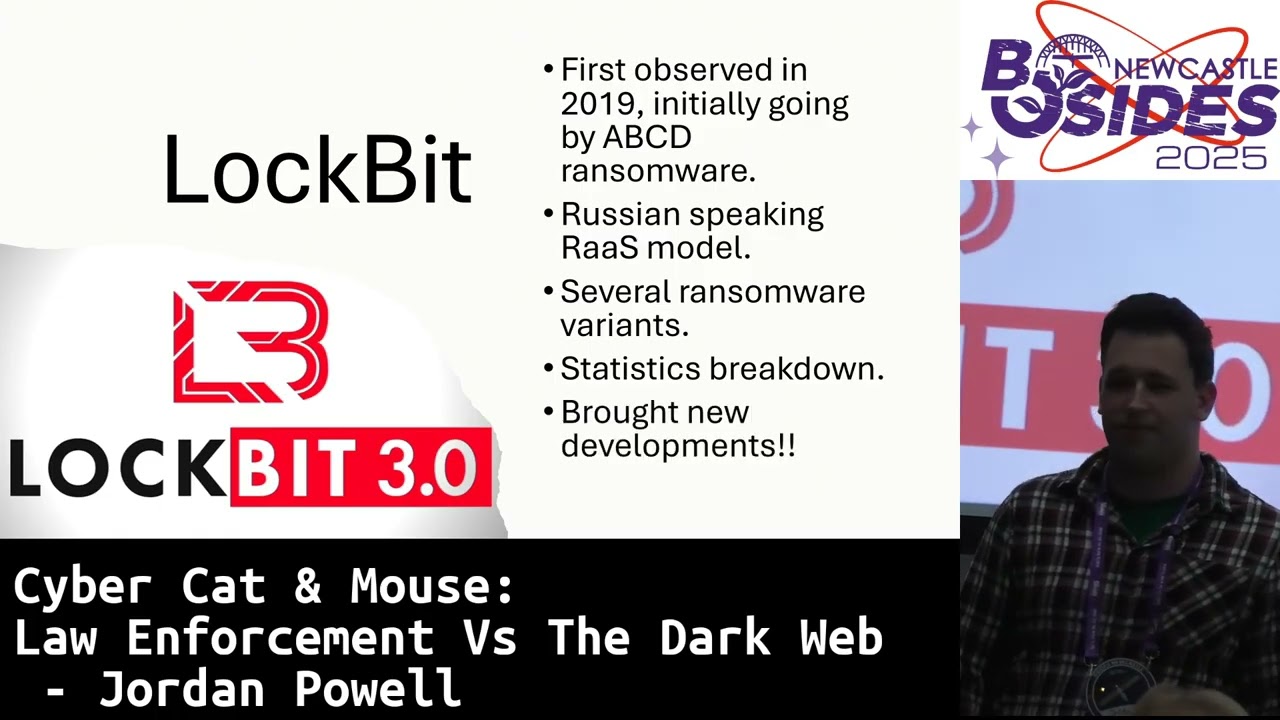
forums which is one of the many seizures. Uh we had this seizure which focused on Hanser and alphabet which are both drug markets I believe and then we have black ransomware. Um so a lot of the times when um law enforcement sees sites what do is they like to display this notice of control. So this is done for various reasons. So it's to demonstrate to you know the the threat actors hey we've took over this site this is a [ __ ] day now. Um and then it show they show all the parties involved. Um so it's really good shows law enforcement are taking actions against you know this massive problem. Um so an introduction to lockbit which
inspired my dissertation project. Um so quick introduction to lockpick. They were first initially observed in 2019 and were initially going as ABCD ransomware. Don't know why they picked that but yeah um they're a Russian speaking ransomware as a service model. So if anyone doesn't know what ransomware service model is, essentially for act operation, they'll make their ransomware and then they'll take on affiliates and they'll say, "Right, you use ransomware, you carry out attacks, we do negotiations, that type of stuff." There's loads of different versions of it. There's loads of different ones. So might say, "Right, you conduct the attack, we take the negotiations, we host the infrastructure, but you get 10% of the cut of profits."
Load different ones, but very basic like that. Um, so from their time with lock bit, they've had several variants. Quickly researching before the talk, I found out there's been a new one discovered, which is 5.0. There's also lot black and green. So they've had the development of their ransomware is, you know, massive and massive. Um, and they're one of the most prolific ransomware groups. They're still very active today. Um, and their top targets include the US, UK, France, Germany, and China according to NCA, International Crime in the UK. Um they're very interesting group. Um you got to give them credit because they brought a lot of new developments to the ransomware scene. So they launched their
own bug bounty program which is quite unique. Um so what they offered was if you found bugs in a sites and reported it, they'll give you money. Um if you give them good ideas for ransomware operation and they go, "Shit, it's actually a really good idea. Here's some money." [clears throat] Um, they also offered a bounty for Lockup, who is the owner of Lock Bit. Um, and they basically said, "Look, if you manage to dox him and you get it right, we're going to pay you a million." Um, so it's very interesting. They also did a tattoo competition where if you got a tattoo logo on you, they will pay you, which is mental. Um, so a
lot of people end up doing it. And um lot bit claimed to have spent around 20k on this. Um so previously from other ransomware groups a lot of them just their promotion was very basic. It was like hey we're the best ransomware group in the world. Everyone should fear us. Come work as an affiliate. Whereas lot bit really advanced their techniques and quickly grin gained um come very prolific. And you know stuff like this makes them go wow these guys are you know professionals these guys are cool. Um, which gets on to the lock seizure. So, law enforcement ended up seizing them in February 2024, um, which was a collaboration between NCA, uh, I believe
FBI and a bunch of other agencies. It was massive. So, in my previous, well, I was a threat intelligence analyst. When this dropped, we were all over it. It was crazy. Um, all the cyber crime forums, all the affiliates who are part of the group were terrified. Um, was not good. Um so a lot of affiliates were actually masked and led to arrests. Um I believe a father and son was actually found to have been affiliates and they were arrested which is you know disastrous. Um Lock bits was identified and he was sanctioned. So he turned out to be a Russian national. Um I don't think they paid bounty to the NCA for finding him unfortunately. So um but
they did offer the guy who exploited him um a job um and we'll pay you more than the FBI or whatever. um I don't think took the job. I don't blame them. Um so due to this seizure, it caused major reput reputational damage. So since then their presence on the cyber crime forums, a lot of people end up mocking them. So other people who are affiliates who potentially like going to go, I'm going to start working with lot see this and go, yeah, no [ __ ] way. Just been seized and you know, all their affids have been arrested. It's a mess. The leaders been doxed. It's not very good. Um, so what they ended up doing was
which was quite unique. Uh, law enforcement actually took over the site and you see like these bits here where it says like published and like times. This is where they used to display their victims. So you'd go on the site and it would say ex company. This is the dessert. So law enforcement went yeah we're going to use that in comparison. So they shared a bunch of stuff and gave updates. So lock bit rest UK arrest a major arrest of um affiliate which again when I was muttering cyber crime forms at this time they were getting absolutely abused um which is very interesting to see. Um so from that I really got fascinated um cuz I was coming off placement year
and I was going into China and I was like this is really cool. I really want to know how did this happen? Um, so I really closely monitored like the story and I was like, "How did this work?" So, shout out to VX underground. Love you guys. Um, they managed to do an interview um and talk to the leader cuz they had some communication and they basically said we might have been exploited with CVE. It might have been a zero day. Other groups might have been hit. They were very much up in the air and not really sharing cuz they don't know what the [ __ ] going on. Uh so the the shares uh from VX underground uh the
FBI [ __ ] our servers using PHP backup servers while uh PHP were not touched. Um hearing this and hearing oh you got uh [ __ ] from a CE um there is is pretty embarrassing when you're meant to be this massive cyber group. Um so even more hearing this a lot of people on cyber crime for like the cyber crime scene went yeah no this is embarrassing this is not good. Um so this really inspired uh my dissertation project um which is tada void core um which is completely name I made um I actually used uh their site as like um inspiration for the design um which is really cool um but I really got fascinated with how do
law enforcement how do actors actually compromise these top sites? How many people are here? Pesters, red teamers, anything like that? Few of you. How many of you have been trained on targeting tour sites? Exactly. Like for the camera, no one raised arms. Um, so there's not a lot of training. There's not a lot of education. So I thought, you know what, it'd be really cool if I can make something like that.
So tobased CTF. So it was all hosted on tour was a very interesting dis project. Um so what I did was I decided I'm going to make a tour CTF site and I'm going to implement the most common vulnerability I could find from research and all that type of stuff. So it was to essentially have the goal of providing a plot a platform which pentest law enforcement could use to get training and go right we have this new person on the team who's not targeted top sites before. let's get them to train against this to site and go right let's look for this common stuff. Um so for the project it was only focused on actual issues within the
domains. So stuff like issues of the to network I didn't include that. I know there few and offset failures I didn't include that. There was other CTFs I found on based on to which was like you know tracking cryptocurrency and that type stuff. Um but for this I wanted it purely just focused on the actual technical issues. Um there you go. Um so what I included for researchers was research uh law enforcement announcements researchers finding and some actor activity. So for the threat actor activity cuz I wanted to try and have it as broad as possible the findings. Um if I saw a like a rep for actor or someone who posted that like credible source like a video actually
exploiting a tour site I would include it. So for an example I don't remember the exact details but it was a threat actor managed to get local file inclusion or server side request for on a tour site and I was like that's pretty cool that's getting added it's seems legit. So that type of stuff. So quick disclaimer just before I get into the findings. So this is completely independent researchers degree student. Um there was no collaboration with any law enforcement or other organizations. So it was entirely me just researching myself. Um my findings have not been peer reviewed or verified. Um so might have missed a thing or two. Um I tried the best I could. So again this is all
on me. I tried the best I could. Was a great student. was quite stressed out at the time and I was like, you know what, I really want this over with. I can get my degree. Um, so I tried my best I could. Okay. Right. So, the findings. M drum roll. Any guesses first? Shout them out. >> You what? >> Louder. They won >> Gladia. Any others? Shout them out. injection. Yes, correct. Next. Anyone else? >> Good thinking. One last one. >> Default. >> Good thinking. So, this is the findings. Infrastructure misconfiguration, SQL injection, access to infrastructure, compromised database. So for context, when I'm putting it in speech marks, obviously the law enforcement ain't going to give away all the secrets of
how they do super cool hacking stuff. Um, so a lot of times they just put we access the infrastructure, we compromise the database. So that's why I put in speech marks, uh, crossite scripting and then other which was like default crest uh, LFI all type stuff. So me as a stressed out one year student I was like oh no this isn't enough detail how am I going to do this how I'm going to implement this I was panicking um so for the implementation I really just tried to make it as realistic as I thought like possible and based off the stuff I could find online. So for the implementation it was pretty basic straightforward. So I just use an
AWS EC2 instance. Apache running MySQL PHP to was a very basic setup. Most of the code if you look at my GitHub, yes, it is written with AI. Um I'm pretty [ __ ] developer, I can't lie, but it did the job. It's very basic. It worked. So as you see top so the crossite scripting one, I just invented a very basic one in the search engine. Click search. Tada. fl um obviously in real world cases I'm not saying it's this simple um but it's just a demo so as injection so void soup was like our imaginary leader I made for this so once you access it can access all that information again obviously in real
world cases it'd be a lot more complicated [clears throat] uh and this one which actually I found in quite a few research cases the uh server status page was actually um designed to be exposed So, if one isn't aware, it's built into Apache and essentially, as you can see there in the lovely GIF, uh it exposes the server version, the IP, a lot of information. So, if you was a penetration test and you found the server status page exposed on a pen test, you'd probably rate it asformational, low, nothing major. When you're exposing your IP as a ransomware site, it's not a good idea. Um, so a lot of the times actually the cases I found
a lot of the times law enforcement just go right looking on shan oh cool we found the IP great contact the provider seizure done. So in conclusion, um to sites is very much a hydra. You take one down, six more grow back. Some of them end up in fighting. Some of them get compromised. They get a spin-off. They keep going and going and going. [snorts] So it's a neverending issue. It's constantly growing. And the tour network is getting is continuously popular. There have been a lot of transitions to platforms like Telegram with a lot of cyber crime groups. Um but poor still quite popular. Um if for some reason you end up working at NCA and
you're panicking and you know you get put on to find an exploiting at all very basic simple way is don't worry don't panic end of the day these sites are just sites they still got you know escro injection they still got cross- sight scripting you just need to apply a different methodology so instead of right guys let's boot up end mapap and scan it and go oh it's fine port there's no IP can you try identify IP from shan can you try and see if the server status be exposed can you try cross- sight scripting try various different and just see what you can work with um the amount of law enforcement person I managed to speak to while making this
dissertation um they were actually really interested in this project which is great to see and a lot of them don't have this type of resources they don't have a direct training method you know a lot of them like us, you know, they just have hacked the box as Pa pointed out. We don't know what we're doing with all sites. We can have a guess, try crossite scripting, that type of stuff. Um, so yeah, also if anyone wants to nick this idea and improve it, please feel free, but give credit if you don't mind. Thank you. Um but yeah, no on a serious note, something like this developed into a more professional because that was just,
you know, I made very basic CE site on tour. Um something a bit more professional, a bit more challenging, that type stuff having laser difficulty could be brilliant for law enforcement. Um person I spoke to an NCA very interested in that type of stuff. Um so if anyone has a business idea, you feel free to nick mine. Um, so if anyone wants to read a bit more into it, I did write a very basic like um blog like research article covering my disc, it's available on my LinkedIn. Um, feel free to add me on LinkedIn. If you got any questions about my research or you just want to have a chat and catch up, feel
free to add me. Um, other than that, does anyone have any questions? >> Any questions? >> [applause]
>> What would you like to do next? Could you be interested in my other projects? >> I've always got projects on the go. >> Which ones can you share that we don't want to do? Uh um one so I'm trying to do much as I can like I'm busy with work but one of the things I've been doing is recent there's been a new I'm trying not to give away too much information um there was recently a new ransomware group that came into operation so I've managed to make a few sock puppets and I'm trying to appear as an affiliate of interest um so I'm trying to social engineer information and go how does your
ransomware work is it just a ripoff of lockbit or PI or whatever of a group. Um the dark web tour type stuff is always is always going to be interesting to me. So I'll always find my ideas but they always have stuff on go. So yeah, one more. Sorry. >> I've never looked into any of the stuff. Have you looked You mentioned like I can be loud and subtle channels. [snorts] >> Yes. Yeah. So when I in my previous role, I had to do a lot of work with Telegram. So it's really interesting shift. So with my old manager, we actually discussed this cuz he was he's ex law enforcement. Um and he was discussing with me that
essentially a lot of these fract cuz there've been obviously so many seizures nowadays. It's you know your whole site end of the day. You got to keep up with the updates. A lot of bit should have took out. You got to keep up with it. It's very hard. So [snorts] that a lot of these groups are just going no [ __ ] this do most of our communication through telegram which is another kettle of fish which is an issue you know with the um corporation they're having with law enforcement now since the CEO arrest uh but yeah there's a certainly a shift towards telegram and other platforms but again to just run so popular I don't
think personally I don't think it's going anytime soon especially with ransomware groups the group just keep increasing numbers It keeps growing and obviously other drug drug markets and that type of stuff. So >> any other questions? You can ask me anything. It doesn't have to be related to this if it's that boring to you. Cool. No worries. Well, thank you so much for attending and hope you enjoyed it. Thank you. Thank you. [applause]





