Quantum Safe Cryptography: A Buzzword Or Something More Serious?

Show transcript [en]
hello hello hello hi everyone I am siku meta um I am a data and application security consultant working in the cryptography space so uh Quantum safe cryptography I'm not going to be biased at all if it's a buzzword or not um so the motivation of this talk is well there's been a lot of buzzwords in the industry lately uh robotics process automation blockchain uh ever seen that video of sun Pai where he's going ai ai ai ai ai um actually I did ai's been great I did ask AI to to write me a cryptography joke but it was so egregious that I'm not even going to repeat that um unless anyone actually wants to hear it
yes okay uh why did the cryptographer who turned into a security guard not get access to his building couldn't keep track of his keys that's so bad feels so B I actually wrote that one not AI so let me give a very brief history um about computers in general so computers have been around for thousands of years um they've been uh used we've been using computers as stone tablets we've done them as we've we've used clay tablets um in recent history we've uh been using them uh we've been creating mechanical computers with switches uh then we've moved moved on to uh vacuum tube uh computers that can create logic gates then we moved on to uh electrical
circuits now we moved into electrical circuits in someone else's data center um and now uh against all other warning we are now moving into the light uh moving in that direction so uh well why are we moving towards the light we see even though modern computers are quite powerful um in fact I know you all know this but you know the phone that you're holding in your hands in your pockets you know they're more stronger than what they're more powerful than what NASA used to send spaceships to the Moon um and yet what we have is still not enough it's still not enough because there are hard computation computational problems out there that we need more power for
ones found in chemistry found in Material Science in medicine machine learning and and the most important problems of all that are found in Banks I'm already joking anyway so chose this diagram um to to kind of represent uh what why we're moving towards it is because it reminds me of the P NP NP hard NP complete um diagram if any of you remember that from computer science at University um so I'm not saying that quantum computers are going to solve all our difficult problems um but they are going to solve up certain uh uh mathematical difficult problems that we rely on today for for cryptography especially for factorization um so I'm not actually going to go into how a quantum computer
works in this talk though if you do want to hear me do that talk you'll have to sub subscribe to my video series on only fans I'm only joking I'm only joking I'm only joking no no I'm not qualified to talking that subject I don't have a PhD o o sorry didn't have a choice really um so public key cryptography relies on hard mathematical problems on uh prime factorization but just very quickly before I go into prime factorization let me give you a very quick background into cryptography itself so there's two types of cryptography that we use um we use symmetric key cryptography and we use asymmetric key cryptography with symmetric key cryptography rely on one
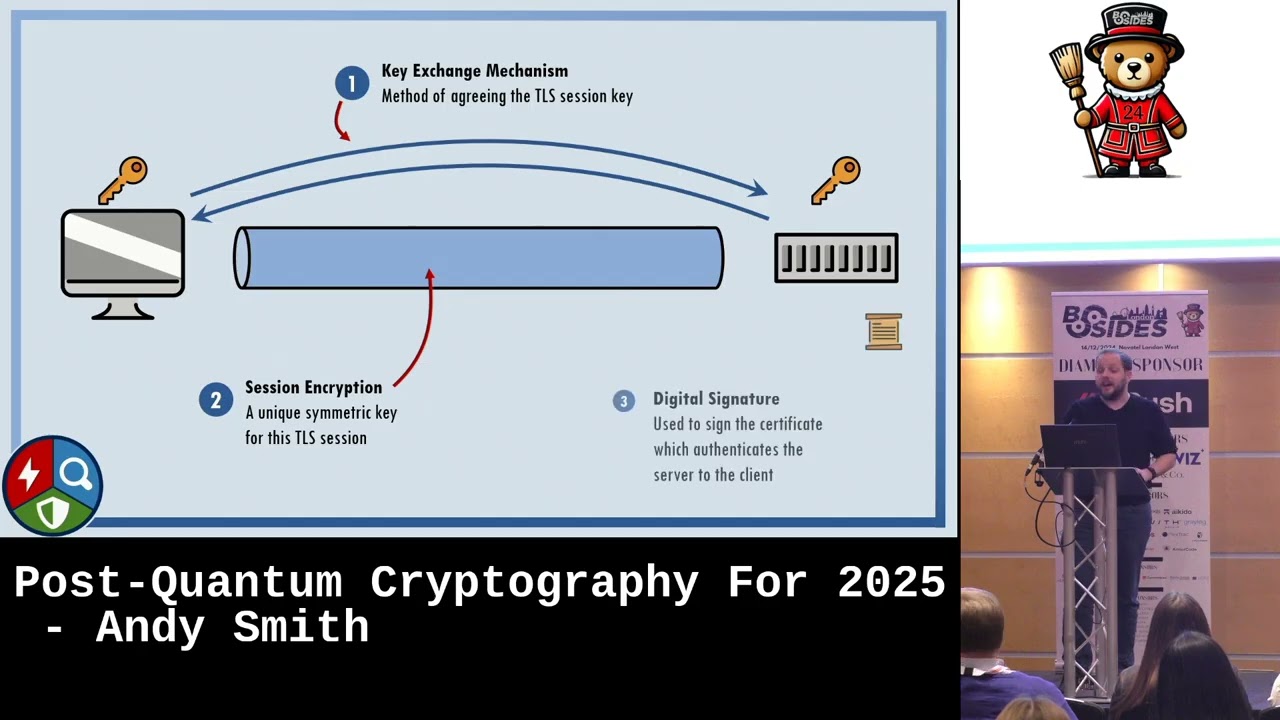
key to both encrypt and decrypt and it's very fast encryption um because of the way that the computers do um um symmetric key cryptography rely on on bit bitwise exor and and you know substitution and diffusion and so it's very fast we use ciphers such as AES triple des and Blowfish and others and then we have asymmetric cryptography where we use a public and a private key pair to both encrypt and decrypt um so we encrypt decrypt we we uh sign we verify among other things and um asymmetric cryptography is much more computationally expensive because of the way that the chips uh multiply uh bits so we tend not to use it for everything but we do use it to
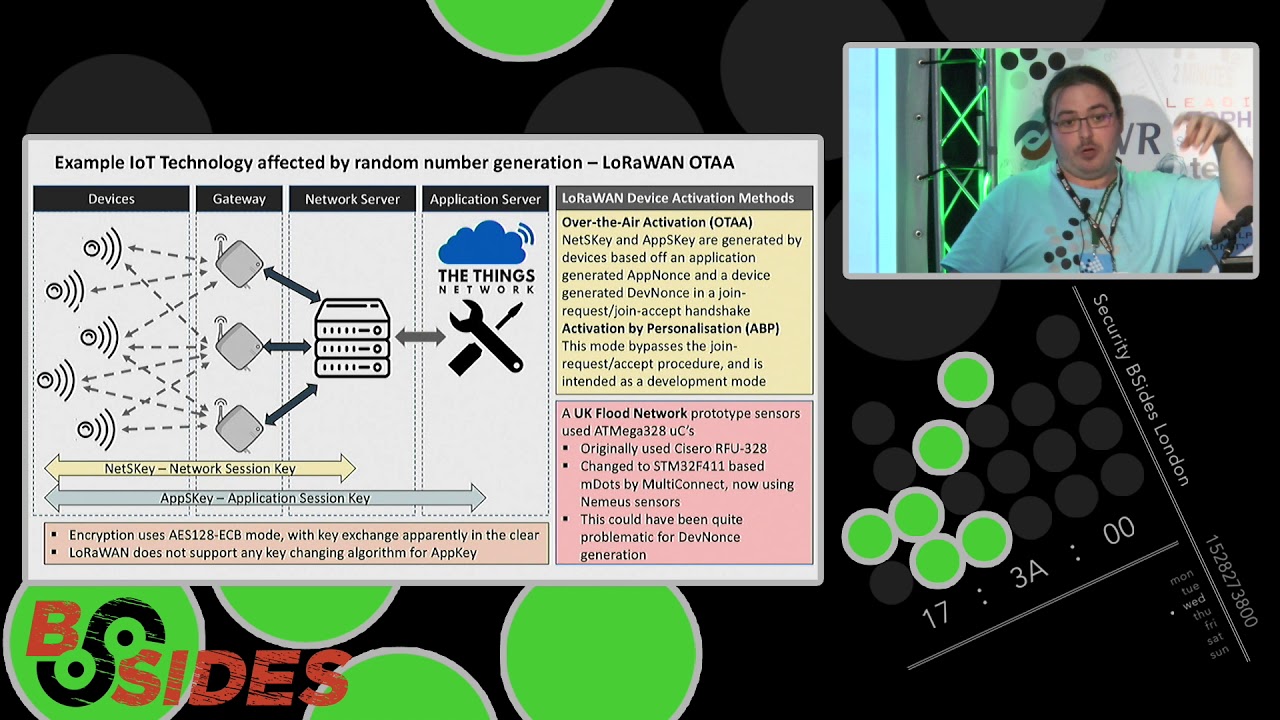
keep our communication secure especially with SSL TLS um we use it for code signing we use it for authentication we use it for SSO we use it for multiple other uses and well back in the 1990s a fellow called Peter Shaw um created a Quantum algorithm uh that makes use of a sufficiently powerful quantum computer to well effectively speed up prime factorization so he so essentially that algorithm will break public key cryptography so if I was denior a top uh Min tith this is the time I'll child flee Flee for your lives y went as down as well as I thought that would but anyway not all hope is lost so remember I said public key cryptography
or asymmetric key cryptography is going to be broken not symmetric key cryptography there is going to be another that there there is another algorithm called Grover's algorithm which does impact symmetric key but not as much it is public key cryptography that we need to worry about actually so um is it a buzzword probably not yet yet or probably not so well what can a quantum computer do um what kind of attacks can we do with a quantum computer um and why should we worry that our public key cryptography is probably going to break we see right now before a quantum computer has actually been created what companies can do or what agencies can do is Harvest
all the data that you're sending in and out of your organization um Harvest enough of it and decrypt it later with a quantum computer uh perfect perfect forward secrecy not going to matter uh especially if you have TLS 1.3 because you've you've you've gathered enough um enough communication to be able to decrypt it to find the key basically and so that's now but what about later right um well think about what could happen if you have a CA compromise in your organization um you and and how would that even work actually so let's say I've got access to an organization I've got access to anyone's laptop doesn't have to be someone privileged it could just be someone that works in an
organization I would have their root certificate stored in my web browser or in my my keychain I could easily find the private key because I've got the public key and that's how a quantum computer would be able to break uh TLS or uh digital certificates basically um and so I can decrypt uh lots of data within the organization I can masquerade around the organization as a legitimate service um I can disrupt business I can perform man- in-the-middle attacks I can manipulate um signatures there's loads that I can do and those are just some of the attacks that I've listed out now um there's always more right um I'm sure you uh red teamers and the blue teamers
all know there's always something more that comes along later and so you're probably wondering well how far away are quantum computers well you see there's advancements happening on a daily weekly and even monthly basis in quantum computers um really there's advancements happening on a daily basis in quantum computers um Google have unveiled a new chip IBM have unveiled a new chip um China are unveiling new chips and so we are we are making Leaps and Bounds in the direction that we're going in and well I'm not saying that we're I don't have a plant here so I can't really tell you the future but I'm not saying that we'll be there by 2030 however nists very
recently have announced that they are deprecating RSA elliptic curve DSA and all these other fun acronyms Dy Helman and stuff by 2030 so and they'll be completely disallowed by 2035 so what does that mean for us what does that mean for you your organization well typically in the UK we get our standards or our cryptography standards from nist um because they're a standardized body we all use AES for encryption somewhere and that's because nist have standardized encrypt AES um however there are four new standardized algorithms that nist also released this year uh crystals crystals kyber crystals dilithium Falcon and sphinx that last one has an odd name um but yeah anyway so so what kind
of problem are we facing when it comes to cryptography you see the thing is cryptography is everywhere and you just don't appreciate how how everywhere where it is until you actually go looking for it um it's it's in every single industry that we uh are Rel uh that we are linked to uh linked to indirectly linked to um it's in every layer of our systems it's in our policies it's in our procedures it's in our uh firewalls it's in our servers it's in our storage systems it's in our ID cards it's everywhere um and so well what seems to O what seems to be what what is out there that can help us right um the thing is I've been talking a bit
bit Doom and Gloom but there is there is hope there is light at the end of this tunnel um Quantum safe Technologies do exist there are companies that are working on uh on upgrading and updating their systems and uh helping others to to do the same um awareness and urgency is growing um there's actually a Quantum Quantum Village on the second floor which I had no idea about but yeah I'm sure those guys will help you uh understand about the awareness and stuff and Regulators are issuing new guidance and advisory and directives so what seems to be one of the main problems that organizations face when they come to this now I'm not I'm not going to try I'm not here to
talk about politics or anything but just like the outside world migration is a huge problem when it comes to Quantum safe cryptography um we need to migrate our public hey cryptography to a more Quantum safe alternative um and this actually takes a lot longer than than what what we may Envision see we've done this with sha 1 and sha 2 and this took about a decade to fully complete and oh look at that we've got just about a decade until RSA is fully dep uh deprecated by uh by nist so we need to start migrating our systems or start thinking about migrating our systems now um and I'm going to leave you with these final things to think about so if we do
want to do a Quantum safe migration what kinds of things do we need to think about well we need to have a cryptography inventory um I have heard someone other people talk about inventories and asset inventories which are very important if you look in the cisp book tells you that asset inventory is one of the most important things you can do I think that might even be one of the top CIS controls um we need to start thinking about crypto agility in our products and our services and in our applications again what does that mean it means that our applications are designed to work with certain algorithms with certain and um ciphers the new nist
ones they have larger keys they have larger size requirements um they're computationally slower so we need to take that all into account when we're developing these new applications or even if we're looking at new Solutions in the play uh in this space we need to update our governance cuz nothing happens without the policy at the top um or the people at the top saying to to we need to do something so we need to update our governance uh application performance just what I was talking about with crypto agility and we need to think about our ecosystem um when I say ecosystem I mean um we need to think about so so in our organizations we have lots of um
software Hardware that are from other companies sometimes we're relying on those companies uh to up provide us with updates and patches and stuff so we need to think about how we manage those Partners as well um and so yeah that's uh about the end of this talk so I hope I've convince you that no it's not a buzz word and that it is something more serious um please give a round of
applause I feel like we might have a few questions for you is that the case you see you see score in the as a serious threat model people sucking up encrypted internet now to decrypt it when yeah so so that's a good question um I I I I do think that is a serious thre I think there are definitely capabilities out there and I'm not saying it's going to be like a commercial um sector that does that but there will definitely be agencies and spy agencies and other kinds of actors potentially potentially actors with even more resources um outside the commercial sector that can can that can do that and there are definitely data centers that
have the ability to store that kind of information so yeah but it also depends on your risk model as well like what are you protecting and how long are you protecting that data for sorry yeah that's all someone over there would like to ask a question um you briefly showed the nist standardization candidates do you think that our Reliance on hard ltis problems is going to be an issue in the future similar to our reliance on factoring and discret log yeah so so again another good question um uh so those like like you said the new candidates they all rely on latis based cryptography right um at the moment it there could be an attack on ltis based cryptography and
and I know that there's definitely academics and other cryptographers out there that are working on trying to break that kind of stuff as there would be um for now I think we're okay um it seems to be like a a tested and tried U model um and so until you know someone comes up with with an attack on that uh yeah I think we should be okay for now we can have one
more thanks um thank you for your talk and I we be signing up to only FS thank you um so what steps like what practical steps do you think organization should be taking today yes uh very good um so what kinds of steps should we start thinking about um the thing is many I I've been asked this question um in terms of do I need to have a mature cryptography capability in my company to start thinking about this now and the answer is no you don't actually you you can mature your cryptography uh capability as you do this at the same time um definitely the the things to think about are do you know where your
cryptography is do you know what uh what vendors uh are you work with and and the cryptography that they provide what kind of cryptography do you use from outside of your company um and other things are probably best to think about is to to to have to start thinking about Quantum have a plan have a strategy um no and have some resources in place as well I think to start that would be good yeah start with the cryptography inventory that will help with the transition and and come uh talk to me in my uh so my company can tell you Services later that was fa but feel free to continue the conversation in the corridor um but yeah we'll have our next
talk in 10 minutes should we give another round of applause I think that deserves it yeah