Post-Quantum Cryptography For 2025
Show transcript [en]
thank you very much uh and thank you all for uh coming to this talk uh said my name is Andy Smith um I guess we'll start off at this point something went wrong with the audio feed we got from the mixer desk it is resolved in about 2
minutes
e
e
e e
headlines really really cool sounding headlines uh from the past year or so uh okay a researcher has cracked RSA 2048 using a quantum computer uh Google has uh just in the past couple of days unveiled this amazing new Quantum uh chip that can perform calculations way way quicker than a traditional machine uh the Chinese have broken RSA okay but when we pick away the buzz the hype behind those headlines it's a little bit less exciting yeah the Chinese did indeed break RSA a 22-bit RSA that's a long way from the 248 the minimum that we tend to be using today uh Google's latest chip you probably saw this in the news recently uh that wonderful statistic is based on
a kind of pointless problem that doesn't have a real world application uh and the guy that claimed to have broken RSA uh 2048 I mean the fact that he claimed to have done it on his mobile phone was maybe a bit of a giveaway that uh maybe this wasn't a solid break and yeah we're still waiting for proof of that so let's demystify some of this let's start off uh with a little bit of a touch into quantum physics not much but just enough here basically when things get small they start to get really really weird they start to operate in ways that we just don't expect them to in our macro world uh you may recognize some of these
phrases if you ever did kind of physics at school this whole kind of wave uh particle duality the fact that small things kind of act as a wave and a particle at the same time uh superpositions that classic Shing as cat analogy the cat is both alive and dead at the same time um at the small scales yes a a Quantum thing can be in two different states at the same time but conceptually makes no sense when we bring it up to the level of cats and also this kind of quantum process of entanglement the fact that one particle can be somehow spookily linked to another particle and if you measure one particle you cause that other particle
to collapse into another predefined state all really really weird stuff and it turns out that we can use those kind of weird factors of small particles uh to do some Computing uh Quantum Computing uses those weirdnesses to perform calculations and operations that our traditional computers cannot do when we talk about a quantum computer it sometimes sound a bit like hand wavy quantum computer the reality is we've got multiple different types of flavor of quantum computer each using different elements of quantum mechanics in order to do those calculations the the actual calculations themselves are performed on what we call cubits again phrase that you've probably heard of these cubits that can be in multiple States at the same time and we
only identify the true state that that particle is in once we take a measurement the fact that those cubits can be entangled together as well again a big driver for some of those really interesting Computing functions that our quantum computers can perform there's two Key properties of a cubit uh the probability amplitude and the phase so there's two parameters that gets manipulated when we're undertaking these Quantum functions these Quantum functions uh that are referred to sometimes as gates gates of Type X or Y or s or h T like really weird named operations these are just different ways that we might manipulate that probability amplitude and uh the um the the the uh the alignment of each of
those cubits and this is really fundamentally different to the classic logical Gates that maybe we've seen before things like the and or the or gate or the exor gates entirely different operations that are we performing on cubits when we see in the news the fact that a computer has been created with X number of cubits H that's a really easily digestible way of getting a feel for the size and complexity of quantum computers but it's actually only very small part of what makes a quantum computer useful crucially we need to have quantum computers with a very very low error rate when things get small they also get affected by noise to a very High degree
so one of the biggest challenges with quantum computers and building quantum computers is being able to control that noise that exists at that teeny tiny level and actually that was one of the biggest things that that most recent Ship by Google uh has done really well they've made quite a big leap in terms of controlling noise the other factors that we might consider that drive the usefulness of a quantum computer include how well each of the gates that we're operating on the cubits actually performs the intended function rather than kind of like 90% of the intended function and also the connectivity between different cubits these are all lots and lots of different factors that drive the usefulness of a
quantum computer so next time you see a news article that's talking lots and lots about cubits bear in mind there's a lot more under the hood there as well okay so bit of a stop tour through Quantum Computing uh why do we care about this from a cyber security perspective uh well it turns out that some of those operations that a quantum computer can perform that are traditional computers struggle with are operations that would otherwise break some of the cryptographic algorithms that we use today crucial to recognize that a quantum computer isn't just some magical box that you you can run uh normal codeon traditional code on and it will just accelerate everything but rather we need to write a specific
function a specific algorithm that takes advantage of some of those Quantum uh Gates some of those Quantum computations two of the key Quantum algorithms that are of most relevance to us in cyber security uh Grover's algorithm and Sha's algorithm a Grover's algorithm is an algorith that allows for almost like brute forcing of um a blackbox function it is an algorithm that provides a quadratic speed up compared to traditional computers uh when it comes to things like breaking our symmetric cryptographic algorithms so things like AES so to put that into context uh normally if you had something protected with AES 128 for someone to be able to Brute for force that they would need to go through
two to the power of 12 operations in order to test all possible combinations and see whether the output matches the target what they're looking for with Grover's algorithm that's dropped down to two to the Paris 64 operations so quite a big um reduction in the time taken to Brute Force AES with Shaw's algorithm Shaw's algorithm uh provides an exponential speed up up on things like factoring primes and calculating discrete logarithms two mathematical problems that provide the foundation for unfortunately all of the symmetric crypto that we tend to use today so RSA uh elliptic curve Diffy Helman um all facing an exponential speed up through the application of Shaw's algorithm running on a sufficiently powerful quantum
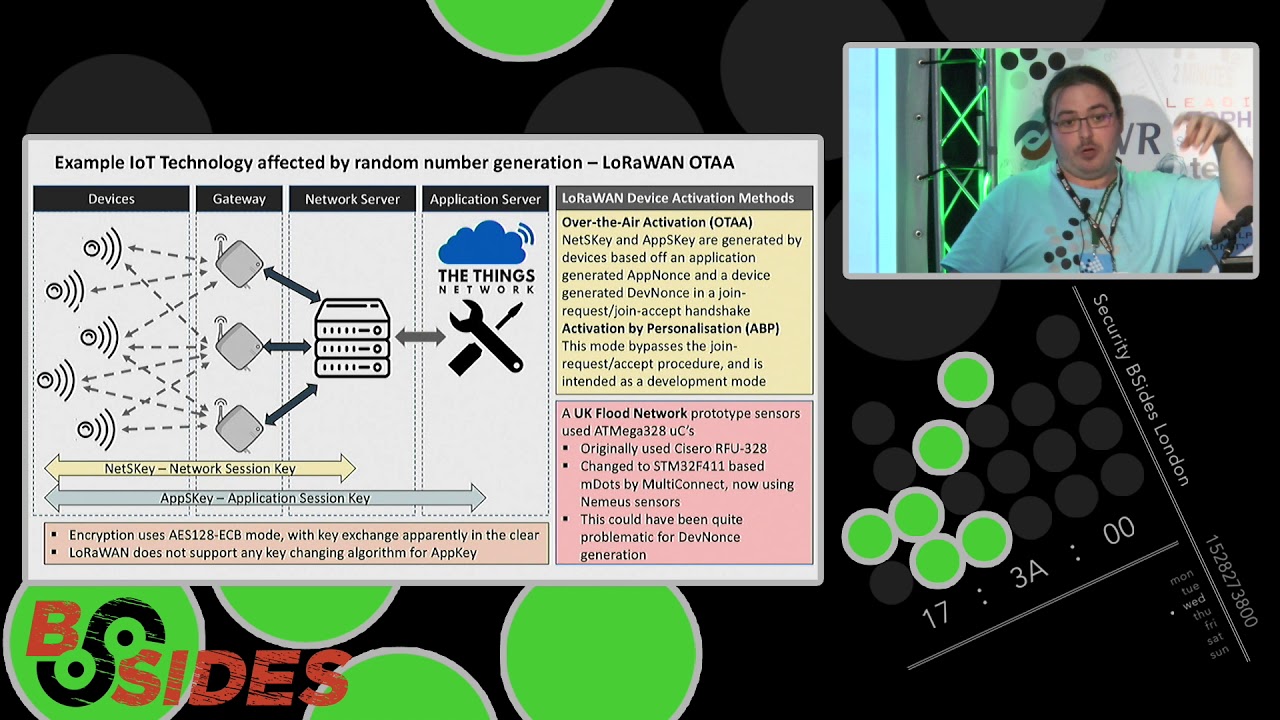
computer what does that mean in practice well let's take a quick reminder here of say something like a TLS session ini initiation we've got several different types of crypto involved the first type is we've got some kind of key negotiation phase at the start of that TLS session uh that agrees a session key that is used to then apply some uh symmetric encryption for that particular session and typically we also apply a digital signature so that a client side can verify the authenticity of a server side few different types of encryption here uh the key exchange mechanism and our digital signature typically using uh asymmetric crypto therefore at a large chance of uh cracking under a
sufficiently powerful quantum computer our session encryption here the use of a symmetric Cipher a little bit less of a concern if we want to improve the security of our symmetric ciphers we've actually got quite an easy task we just need to double the length of that key size so if we want to regain that 128 bits of security for AES well we could just use AES 256 even when faced with a quantum computer running Grover's algorithm we're still able are to retain a decent level of security unfortunately that's not the case with our asymmetric ciphers like I say that's um exponential speed up that shaes algorithm delivers means that we need to do something a bit
different either we need to use the weirdness of quantum physics to create some kind of uh new cryptographic system or maybe we need to find a cryptographic system that operates on our traditional machines that just can't be accelerated through a Quantum algorithm so let's have a look at some of those options um starting off with with some of the quantum Technologies the sort of things that there's lots of vendors out there uh trying to sell you at things like Quantum key distribution Quantum key distribution uses those wonderful properties of quantum mechanics in order to uh get a session key agreed between two parties over an untrusted Link in a way that means if there is anyone undertaking any kind of
ease dropping on on that connection we're able to identify that and we can just not use that session key usually this uses things like the the polarization of photons things like entanglement between uh different photons in order to achieve that of course this requires lots of fancy Hardware you can't just undertake Quantum key distribution on the laptops and mobile phones that you're using today uh also bear in mind that the the uh use of quantum key distribution is maybe a little bit Limited in that sense the fact that if we aren't going to be baking in this funky Quantum technology into our laptops and our mobile phones we're typically only going to be able to
use uh qkd on point too links then that introduces a question on well how useful really is that technology I'm not saying it's completely useless there are cases where being able to have a Quantum secure link today right now is valuable but probably for most organizations and most individuals going to have limited applicability the other type of quantum powered uh technology in the crypto space that you might have vendors trying to sell you uh is quantum random number generation the ability to create random numbers using Quantum and well yes random numbers are important in crypto we we know that right but actually is there anything that wrong with our current random number generation Solutions today not really yes there are
definitely cryptographic attacks that have been successful because someone has not used a sufficiently cryptographically secure random number generator but that's an implementation error so again I caution you around believing uh some vendor claims that a Quantum random number generation is somehow going to solve your Quantum crypto concerns also bear in mind that neither of these two technologies help us uh achieve uh security um against the um the threat of quantum uh computers breaking things like digital signatures uh other forms of public key encryption maybe there's something else we need to look at instead and so this is where I would like to steer you folks towards uh the fact that we have Quantum resistant cryptographic algorithms uh that we can
run on our standard traditional computers today on our laptops on our mobile phones Quantum resistant crypto drilling home the point here algorithms that can run on a classical computer you do not need any funky quantum computer to run a Quantum resistant cryptographic algorithm the power Behind These algorithms are that they are based on mathematical problems where there's no Quantum algorithm to speed up the breaking of that encryption we don't have an equivalent of a Grover's algorithm or a shaes algorithm uh that can break the uh these new Quantum resistant cryptographic algorithms they're just based on a different mathematical problem you will note the asteris next to that statement that we know of today sure who knows at some point in
the future someone may come up with a cool funky new way to break some of those new mathematical problems uh but today uh we feel like they are sufficiently secure uh most of the algorithms that have been going through uh the selection process that nist have been running uh leverage what's called ltis based cryptography as the uh that hard mathematical problem to give strength to those algorithms there are a couple of other mechanisms as well uh that use things like um uh stateless hashing um so we've got a couple of different of those mathematical problems that our postquantum crypto is being based on the pro process that nist have been running uh to find some Quantum
resistant algorithms been running for a number of years now uh last year nist came out and said here are the first four algorithms we're going to standardize and in the past few months uh we've had that standardization process finish for the first three so mlkm MLD DSA and slh DSA the first three algorithms that nist have finalized the standardization process before you might have seen these algorithms uh being refer to by different names uh the names given to these algorithms as they were working their way through the standardization process uh are Kaiba dilithium and sphinx but those were the names that the inventors came up with and nist in a way just to to make things
a bit more boring came up with some uh definitely far less exciting names module latis based key encapsulation algorithm nice and generic right H so these are the new algorithms that we should be looking to migrate towards uh the nist website has lots of really great standards documentation that go into a lot of detail on those implementations uh also for quite a few years the open Quantum safe project has been providing uh free open-source implementations of all of these algorithms as they've been working their way through the standardization process so that it's given uh security researchers crypto analysts uh the some implementations to be analyzing and exploring with now that nist have actually finally finished the standardization for these
first few algorith algorithms we're starting to see some production implementations as well and and this is really really cool stuff the fact that some of the these Quantum resistant algorithms are now present in things like Firefox things like Chrome a cloud Flare have been supporting uh one of the quantum resistant algorithms uh for a good year or so um so it's the sort of thing that we're now starting to be able to get our hands on and that's why I I wanted to give this talk at this point in time because for a number of years we've been able to talk about postquantum crypto and say you should do something okay what should I do um wait till nist have made a
decision then do what they say okay we've been waiting we've been waiting we've been waiting and nist have now finally come out with these standards so we can start now implementing them and moving towards them I called out here one of the specific Quantum resistant algorithms uh supported by Chrome Firefox and Cloud flare uh ml cam 768 so that's a uh iteration or a version of the mlkm or kaiber algorithm for key exchange uh plus also x25519 x25519 that might sound familiar to some of you that's one of our elliptic curves one of those old classical key exchange mechanisms or public key crypto that we're saying is supposedly broken by Quantum Computing what's going on here well this is in fact an example
of hybrid crypto the fact that we are using a combination of both a classical or a traditional uh algorithm plus also a Quantum resistant one we're effectively encrypting the key exchange twice what this means is that in a Quant if in an era of a cryptographically relevant quantum computer that can break the elliptic curve part of that key exchange well we still have a layer of security provided by mlkm however imagine a world where maybe in a year's time a very smart person comes out with a way of actually breaking mlkm if that's the only algorithm we're using then okay that's going to be a bad day week and maybe even month for us so um the this concept
here of hybrid crypto gives us that safeguard that protection against a cryptographically relevant quantum computer whilst at the same time providing us with that kind of that that that comfort blanket that safety net of a more classical algorithm that's may have been tried and tested for a longer period of time and that's not to say that I I believe the mm or any of these other Quantum resistant algorithms are likely to be weak I mean let's face it they've gone through years and years of analysis but uh for those of you that have been following the standardization process uh you may have seen the psych algorithm fall at the last hurdle that got through several rounds of the um
assessment and standardization process uh only for someone to realize that they could run an algorithm actually just on a laptop computer using some slightly obscure maths from I think it was the '90s uh to break Psych in a surprisingly short amount of time so again that's where a bit of that comfort blanket of using more of a classical algorithm along with our Quantum resistant algorithm is the way to go what we call that hybrid crypto and like to say this exists today um I I was thinking of doing a bit of a live demo but trying to look behind me at the same time as doing stuff on the screen might have been challenging but
this is a little screenshot that I just took earlier today uh this is just the standard version of Firefox installed on my laptop here uh navigating to a particular website the cloud flare host and uh hitting the the magic hacking button F12 to open up Dev tools and taking a look at the uh TLS handshake and if we look a little bit closer we can see the key exchange group for this communication is mlkm 768 plus x25519 so the communication between my laptop here at the using the bsides Wi-Fi connect to just a random website that cloud flare is hosting is actually using a Quantum resistant key key exchange algorithm this stuff is already here one of the other things I wanted to
try to portray today is a little bit of intuition as to how some of these algorithms are operating if you've ever looked at any type of crypto before you're probably familiar with the basics of RSA it's kind of like security 101 the fact that if we pick two large prime numbers and multiply them together well it's actually easy to go in that direction but it's really really hard computationally hard to take uh that um that combined number and then try to derive the original two Primes from that that's the the intuition that we have around why RSA is strong what about latis based crypto then the fact that you this is the type of crypto that many of those Quantum
resistant algorithms use not all but many most of the time they're leveraging an algorithm uh called learning with errors or lwe and I really like this because this is quite simple mathematics really at the face of it we create a big long array of equations that follow this format of ax + b y + c zal n a big long array of those the A's B's the C's the n's form the public key the private key is the X the Y and the Zed and it turns out it's really really hard to derive the values of X Y and Zed given the public key for two main reasons uh one reason is the fact that there's lots and
lots of these equations to try and satisfy those values for but also crucially we're adding in a little error this little error E into each of those equations that makes it really really hard to work out what that x y and Zed are when I was going through the process of trying to wrap my head around around this I spent a long time diving into lesses after all this is ltis based crypto lesses are these um uh big arrays of points in multi-dimensional space and there's different ways you could describe lesses and gets all very complicated it turns out that the learning with errors problem doesn't actually use lesses at all there's no ltis maths in these equations but what
happens is that if you want to try and solve these learning with errors equations the best way of doing that is to apply some of the same mathematics as we would apply to a ltis based problem and so effectively it's equivalent to a latis based problem that's where the term latis based crypto comes from in this sense I've given a very brief overview here of learning with errors if you want to see a little more about this some really nice uh graphical visualizations and kind of worked examples um that go into a bit more detail uh I really recommend the YouTube channel uh chalk talk math uh they have a really great video around learning with errors uh
really really nice uh demonstration of the mathematics behind that process okay so uh we have spoken here about uh what the the the threat is uh We've Spoken a little bit about some of the options for dealing with the threat uh let's take some time to talk about the timeline when should we uh really start to worry after all we know that quantum computers are getting more and more powerful they're getting more capable um they can perform uh more operations more reliably with less noise and at the same time we've got very smart people doing research to try and make it easier are less computationally intensive to break some of our crypto so the the point at which a
cryptographically relevant quantum computer exists is created it's sufficiently powerful to break RSA 2048 is kind of what we refer to as Q day little bit like dday but Quantum day it's that point where the cryptography that we use today will be broken bearing in mind that today Quantum Compu can only Factor pretty small numbers um but yes the pace of development is fast uh not just about the number of cubits of course we need to consider uh the overall Quantum depth um of a quantum computer uh the amount of noise in that system and so on and we also need to think about uh what's referred to as the Harvest now decrypt later attack the fact that there may not
be a cryptographically relevant quantum computer to today but if someone can capture a whole bunch of sensitive information or traffic uh flowing over our networks now and then keep that until a sufficiently powerful quantum computer is created then that can be used to break the data that's being captured today it's often discussed as a more significant threat than I personally believe it is the reason being is I take a view from the other side if I'm an attacker if I'm an attacker that maybe wants to pull off one of these Harvest now decrypt later attacks I need to be capturing a lot of traffic I need to be capturing a lot of data and potentially
for a very very very long time maybe a decade or longer how practical how feasible is that particularly when you add on the fact that when you're looking at encrypted information it's all the same if you're looking at an encrypted um packet capture in wi shark you can't tell which of the packets are associated with super top secret information versus which of the packets associated with uh the menu for the Christmas party right so in my view the whole Harvest now decrypt later scenario is is absolutely possible but it will only apply to certain organizations in certain industries I think also it apply a lot more to um the the types of attacks where an adversary is able to
identify valuable information even in its encrypted form so particularly where an organization is using things like um uh encryption on a storage device or maybe a document level encryption that could be something that allows an attacker to identify what's the really juicy encrypted information I'm only going to keep a copy of that rather than absolutely everything uh I throw up the date here 2035 is question mark for a cryptographically relevant quantum computer I mean that's a massive finger in the air right guess um it's probably not an unfair assessment uh to to use for planning uh particularly given that this is the date uh that the NSA are using for their postquantum migration so the NSA um have
called out uh a couple of deadlines both 2030 2033 to have migrated off of our traditional crypto and onto Quantum resistant crypto uh so of course NSA probably have a bit more of an interest in keeping things secret for longer than most of the rest of us H so yeah maybe 2035 could be a good date to to work too so it feels like that's a long way off um why do I need to do anything today well bear in mind that transitioning to new crypto systems is a long difficult journey I gave the example earlier of TLS and the various different bits of encryption uh within TLs but we use crypto in a whole bunch of other places
as well uh things like signing firmware uh we use it um for digital signature when it comes to certificate authorities um we have crypto embedded in Hardware that maybe doesn't get refreshed or changed uh say only every once a decade or every two decades there's lots of areas where we've got crypto in our world today that is really quite hard to replace so my suggestion to you is H as 2025 kick off start thinking about what can we do today to start that migration process given that it will likely take a decade or so also want to call out that we are likely to see some additional signals as we go along to help steer whether we
need to speed up or whether we could maybe slow down our migration activity the fact that there are a whole bunch of other uses of quantum Computing other than just breaking crypto so where we start to see those other uses of quantum Computing that's a good signal for either accelerating or slowing down our own migration efforts so uh some things to think about uh if you are developing software or Hardware I encourage you to think about cryptographic agility the uh that preparation to change what cryptographic routines you're using inside your software or Hardware make sure that your cryptographic libraries are kind of pluggable you can plug them in you can plug them out you're not hardcoding any
key sizes or putting in arbitrary limitations and restrictions into your code or your hardware for most organizations you're also going to want to undertake an element of cryptographic inventory to understand what cryptography do you have and where who's actually accountable for that bit of crypto in your organization asset inventory is one of the most boring things in cyber security but it's also one of the most important right and cryptographic Agility sorry cryptographic inventory is kind of the same right doing an inventory is not fun it's not exciting it's not sexy but it is the starting point for being able to understand uh what's my Baseline where's my starting point and therefore how big is that problem space where are the uh
Assets in my organization that are most sensitive what's got the most sensitive information or what are the assets that if there was a breach of in cryptographic Integrity maybe that would cause the biggest impact you know things like Financial transactions of course um and what are the parts of my infrastructure that are going to be the hardest to address so again where you've got crypto that's just running on nice little Windows laptop that's probably going to be fairly easy to replace where you've got that same crypto running on say an iot device or maybe an industrial control system somewhere those are devices that again might not be replaced um for a decade or more we need to be looking at um the the the
range of different types of crypto in terms of encryption in transits things like TLS also encryption at rest uh things like code signing digital certificates whole bunch of different elements of crypto uh we want to be able to identify I call out here Zeke is just one free open-source example of some tooling that can identify the cryptographic parameters as part of the TS handshake at the start of a TS session and I know having spoken to some of the folks at the quantum Village today that they're also working on some really uh awesome other open- source tooling uh to help perform some of that cryptographic inventry uh so if you haven't already done so uh definitely go and have a chat
with the uh the quantum Village on the middle floor today another key action is to speak to your vendors in most cases uh certainly you know where I have done most of my work uh a lot of the cryptography that we use is actually part of somebody else's product that we've bought so it's completely out of our hands to actually do anything about that we can't go and change that code because it's not our code but we can work with those vendors and offer some gentle encouragement around hey could you please look to upgrade those uh systems that software that Hardware whatever it is uh this is something that we can start off with with some gentle
questions uh maybe then as the years progress some more robust questions maybe add in some additional requirements we are only going to continue to buy your software if you have a road map that demonstrates how that is going to be Quantum um resistant or how how that is going to use quantum resistant crypto within a certain time frame within a certain road map and then again over time as that threat starts to increase we can also increase the level of robustness around working with third parties again I encourage you to think about this because this is a way that collectively we as a industry can encourage some of those vendors those suppliers to actually make the changes
that we're entirely dependent on them for they're only going to make those changes if they see that we as the uh purchasers of their Solutions actually care about having Quantum resistant crypto I also really encourage you to get handson with Quantum resistant crypto uh I called out open Quantum safe as a an open source project providing implementations for you to work with to experiment with um also uh called out things like Firefox Chrome and others that are starting to bake some of those algorithms in really really worth exploring that and becoming familiar with those a reason being is that until we do some testing we might not find some of those incompatibilities uh that start to come
out as we start to do that migration key here is also looking at what is the level of support within our security Technologies can our security Technologies actually understand some of these Quantum resistant Al algorithms in the sense of uh things like our sensors our Network sensors uh our scanners across our environments so wrapping up there um clearly Quantum Computing poses a long-term threat but I would encourage you not to keep kicking the can down the road because doing that migration to Quantum resistant crypto is a long-term activity uh certainly there's no Panic and if you're still struggling with SQL injection on your public facing web apps please fix that first and then come back
to postquantum crypto right so let's be fair in terms of prioritization and also please keep an eye out for some of that fear uncertainty and doubt uh that some of our vendors uh and some of the media May uh May portray got a couple of other links up there to some further reading in terms of uh Quantum risk report uh Cloud Flare have published some really awesome technical information information on implementations and of course there's the the quantum Village that's also publishing some really great material on the topic uh so with that I think we've probably got a couple of minutes for a few questions um so if there's any questions gears a wave and
there'll be a microphone coming down
hello you mentioned um TLS Sport and Firefox um which sounds great but the other on the wire one that I care about is SSH unfortunately a completely different Nam space SSH 2 alos and TLS 1.3 alos are not shared can you comment on the state of SSH is it behind is it anywhere okay what is the status of uh the SSH protocol as part of that transition to postquantum crypto and yeah I have not seen anything of any kind of material nature around implementing some of those postquantum algorithms in ssh in a production sense uh certainly the um open Quantum safe projects have released some of those experimental binaries to run SSH using uh Quantum resistant
algorithms but if you go to their website you'll see in a big big red box these are experimental do not use these for production and so can start to explore them but yeah I'm not aware of any um kind of production implementation as yet um hopefully though this year now that we've got those algorithms standardized we should start to see a bit more movement any other questions go then go for another one sorry I have got three I'll just keep going um you mentioned harvesting so is the implication there that anything using let's call it classic perfect forward secrecy or DIY Helman is potentially at risk uh there and is there is there anything I can do
today about that if I was EXT extremely paranoid so yes um with the Potential Threat of harvesting attacks um yeah it doesn't matter if you're using perfect forward secrecy you Diffy Helman the fact thaty Helman is considered a broken algorithm in face of a sufficiently powerful cryptographically relevant quantum computer means yeah didn't didn't give you anything I'm afraid is there anything you can do today um well actually now there is again start using some of the um algorithms that nist to standardize they're now available they are now standardized so and they're starting to be built into libraries so you can start to use them uh if you're getting a bit paranoid absolutely and I think we had a question
over here so we'll give someone else a chance for a question but I'll be around later for you to throw more questions at me if you like hi inde thanks so much for your talk um I think with regards to um an I on the future and saying what we need to do for prep um looking at it from a hardware vendor perspective do you need to start worrying earlier yes given the fact that uh Hardware changes less often and it's more difficult to change Hardware right um yes absolutely so um any like iot devices any hardware devices yeah you want to bump those up the priority list in terms of at least making sure that
you've baked cryptographic agility into them you might not actually implement the quantum resistant crypto today but do you have the ab ility to I don't know push out a firmware update at some point in the future would that work uh but yes definitely prioritize the hardware cool right so that's all the time that I have but as I say I'm going to be around uh for any more questions thank you folks so much for coming along