Shut the Front Door
Speakers
Tags
CategoryTechnical
About this talk
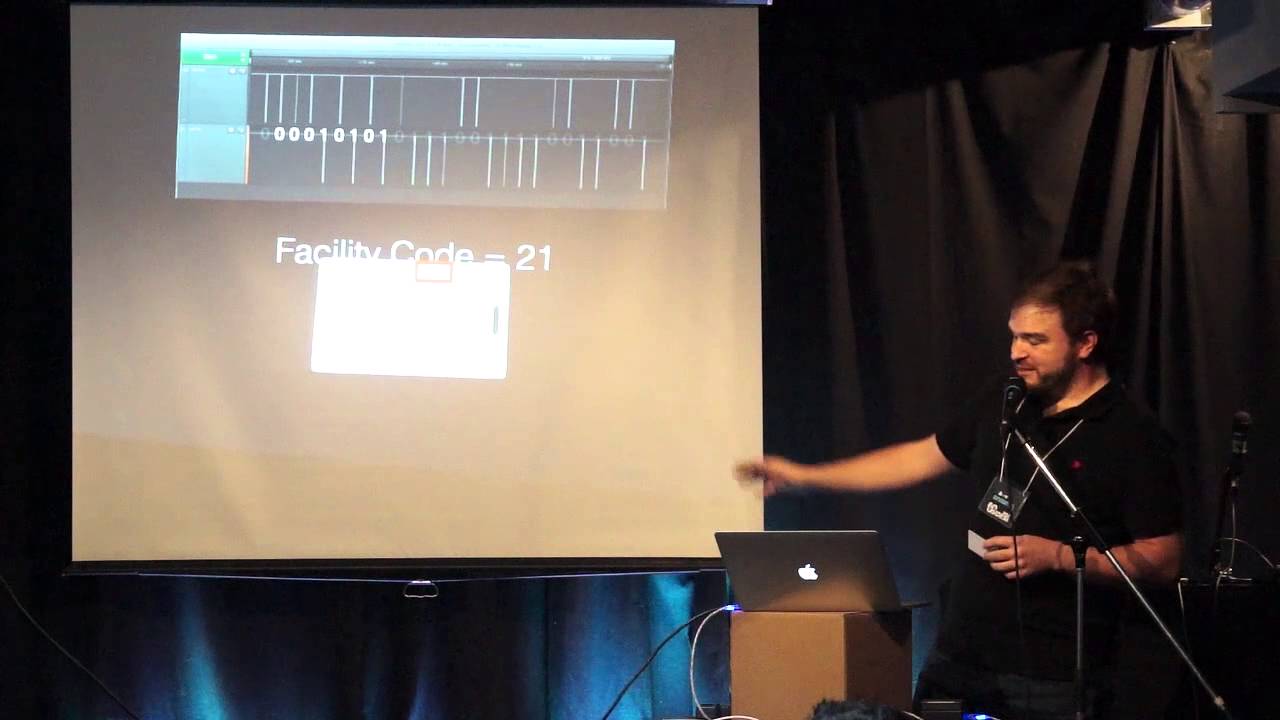
Mark says: In the past couple years some smart folks have put their minds to creating some clever tools that have completely obliterated the security of many popular RFID access systems. People don't get just how broken these systems are, so I'm is going to give some real examples of the flaws and the attacks which can be performed on the most commonly used systems found in the world today -- HID proximity, iClass, and mifare. I'll specifically focus on cloning iClass badges using my own solution, the actual iClass reader itself. I've developed a python script that can talk to an RW300/400 reader via serial and clone a badge. I'm currently in the process of porting it to the teensy platform to make a self-contained badge cloner for iClass cards. I think only one other person has done this, and he didn't tell anyone how to do it (except me, lol). Real life examples will be pretty fun. Eg. adding credit to an RFID badge used for a companies cafeteria, then cashing it in for cash. In addition, I have a lot of tools I can bring for people to see: a customized "Tastic RFID thief" (long range card thief), proxmark, RFIDler, cheap chinese cloners/tools.