The Human Factor in Cyber Security
Show original YouTube description
Show transcript [en]
john take it away can you turn john on [Laughter] i'm off scott's going to turn around it's fine let me fiddle with your buttons is that me on that good right i don't know i can beat the uh john mcafee video but let's let's just let's just go for it because uh yeah that was something but yeah who am i i'm a master's student at napier cybers advanced cyber security program with edmund aker i am third year running any site treasurer still and i'm also now working for cso stretching architecture within tsb and the masters is now part-time unfortunately where you can see i'm always very productive um so yeah jumping on straight into it
let's just jump straight into the scenario um there's been a breach there's been a leak data has been lost someone screwed up but they got access via an ex-employees account i'm buzzing anyway and some person is looking like that there's a fire someone who used to work at the company has accessed this data and has been leaked has been lost is it a breach is a leak that depends by definition but first other things that could have been lost the important things you've got customer data you've got any source code of any applications you're working on if you're a bank if you're a software service company any of your source code you've got the inventory
data any of your infrastructure any of your applications any of your key items oh wrong button any of your employee dates as well it's just as i'm just going to avoid this side of the stage because one thing that's getting annoying any of your employee data is just as valuable as your customer data and it means all the same she also have your national insurance number for your payslips and everything as well and any trade secrets anything that you might not want your competitors to know anything you might not want your staff to know and then last one is any research your company's conducting anything you guys are looking into that is anything that you're ready to publish
ready to present and it can all be lost now back to the definition of a breach or a leak breach is a very deliberate very forceful attack whereas a leak is someone somewhere within your company is done [ __ ] up and there's a vulnerability or there's a flaw somewhere that has just been exploited um a good metaphor for determining distance the difference is your car has just been stolen they smash the window hot roared the car and right off into the sunrise so it's on set it's a breach very forceful but if you left the door open key in the ignition and nice bit of piece of candies leading up to the door that's a
leak you lied them to it or you left it vulnerable for them to then just take although the ex-employee did they have weak credentials do they have with uh disgruntled with the company was he leaving under a great crowd hello it's always the intern it's always the end not wrong it could be as always but he could have done it for a number of reasons he could have done accidentally and left on a post-it note in starbucks or in the background of a photo you had is it the user management team did they remove the account after he left how was he active on it recently and they just didn't think to look at it but then
again that's defined by the policies if my button works the policies is there a policy in place to remove levers from your company remove their access to accounts this guy could have been high up in the company and access to numerous systems your cloud platforms your um internal messaging your emails everything and anything and his access is left there because he accessed it the day before he left he's not been inactive for six months he's not been inactive for however long and it's not being paid to you but is there a policy in place to actually remove him from the credentials or i'll turn to if there is is there one to remove him after he's not been active
for so long if an employee's not been active on their account on a platform within x months will they get removed but then that also oh this thing is so temperamental that also comes down to the application owners either the people that manage the application or even the service provider if it's a software as a service do they have a communication method for them to inform you saying okay hey this month these accounts haven't been active in so long do they get notified is there a monthly meeting or something between you and your third party provider is there an internal meeting to review this or is it something that's just going to get picked up by an audit are you going
to shoot yourself in foot by not looking for this just a quick show of hands from everybody hands up with your students and i'm going by assumption that the rest of you if you don't put your hands up our industry hands up yeah it's about 50 50 split ish so for those that are in industry user probably heard stuff like this before is where you have okay your domain split up to manage different things you've got the applications team that manage all the applications in development for your company or you've got the infrastructure team that manage all the hardware and all the um platforms the tools you guys use you've got your sock or your threat intel team that
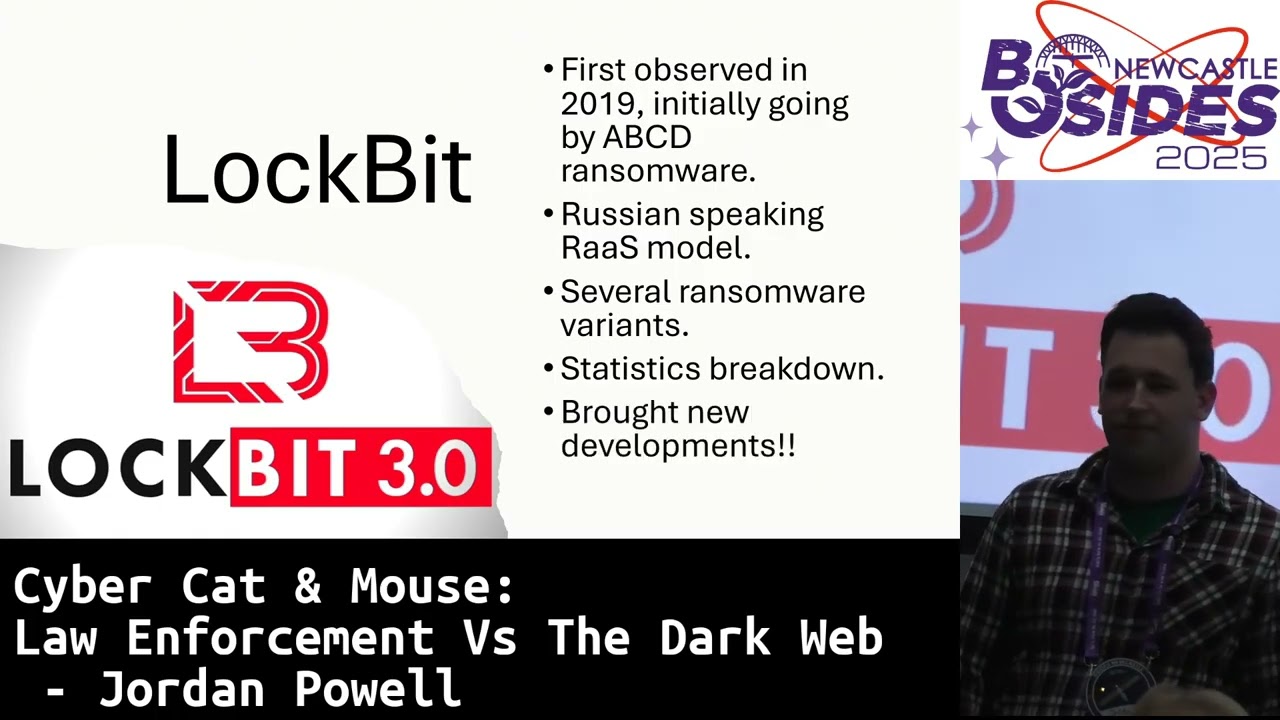
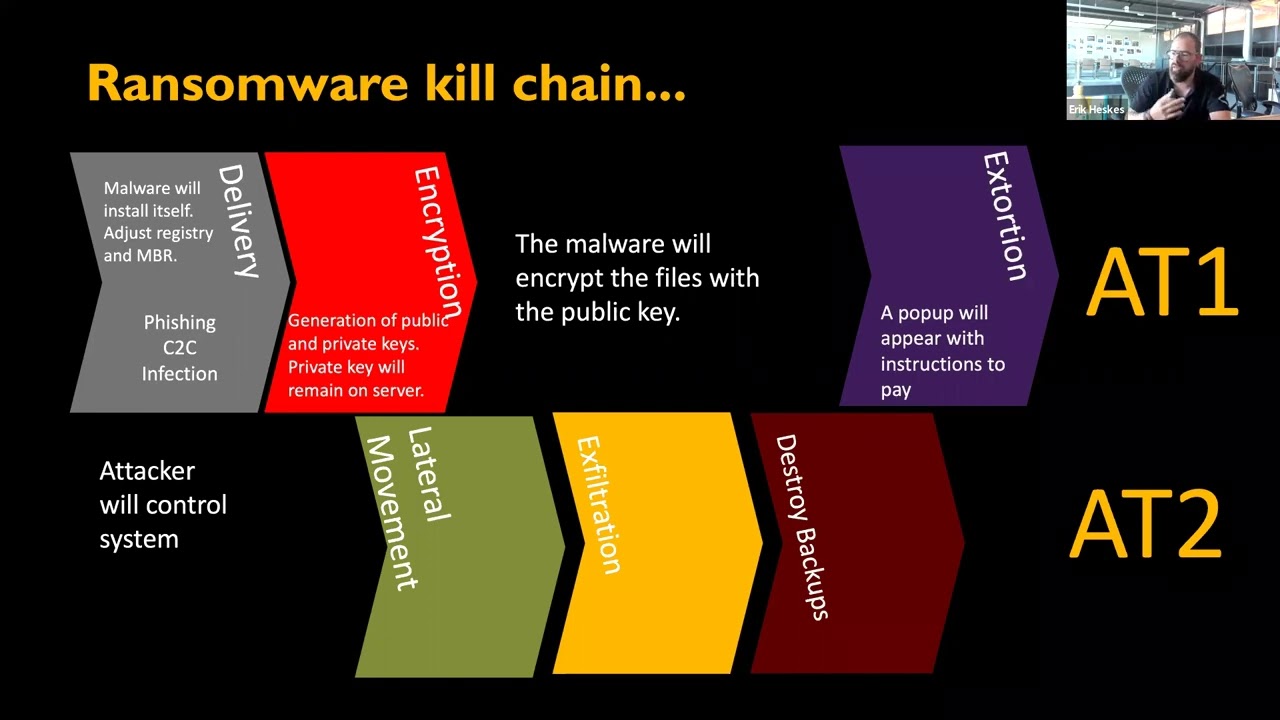
manage all the threats and security of your company or you've got the third party team that would work with and communicate with your third party companies to hopefully make sure this doesn't happen but then that also raises the question of do you communicate effectively with them if this button works then it comes down to how they got in so for a breach the top four based on a quick google i totally didn't do are ransomware malware phishing emails and denial of service so this comes back then to an earlier presentation and i can't see because they're very blind but i'm sure he's in here where he's talking about buying domains of misspelt like minor misspellings of a
company's website to then he put them there he is way forever there we go he put them as a 404 generous of you whereas other people could have redirected it stolen their data made it look like a real login page i remember reading a while back there was a fake facebook made up and and it captured tons of credentials of people trying to log in thinking it was the real deal but then is that how he the ex-employee's credentials were lost did he try logging by mistake and something that was spelt with an i instead of a u malware comes in anyway phishing emails that he wants to get in with the nigerian princes and denial of service
again with the buying domains and that jumps to leaks again how do leaks happen you've got your mishandled data did you leave it these unclassified ufo documents at the bus stop that genuinely did happen by someone in government i thought it was hilarious you've got misconfigurations of servers or network devices or anything on your site which can also lead to issues with logging in and security then you've got insider threats did your employee not get the promotion he wanted has he done [ __ ] up in general it can be malicious or blind uh benign for the fact that they can just come down to human error and then the last one there is system
errors again just as misconfigurations button button there we go and for preventing leaks you've got data classification now this one's kind of important and it's going to come up later again in the presentation but you've got this classification where you can classify your data from it's fine it's nothing you can't google to store this in fort knox we don't want anyone getting into this and the issue with this is you get people that come in and say you know what it's too much hassle to just sort this out neatly it's too much hassle to constantly go through the different authentication practices to then get into the data if we make it too secure so let's just shove it in lower
setting possible which meant um people can come in and be like oh hey that's really interesting should i be seeing that probably not and then you've also got i've missed something somewhere but anyway you've got training in your employees to make sure that they know to report things like this one example of this is any sex later to hack 2018 we ran a cta this was before my time on the committee so it's not my fault but we ran the ctf we're at the cr napier quick locker site and one of the committee members at the time had left a piece of paper with the flags written down on it some kind person handed it in without
actually taking any of the flags or so we think at least and didn't actually realize what they had just done so make sure your employees know how to physically handle the data don't leave it lying around don't leave a bus stop like someone in government did and you want to make sure that they're aware about phishing emails that they're aware about what access they should and should not have as well as maintaining active accounts so they don't get kicked off if you do have a strong account policy but then there's also data protection is your data that you are classing as more confidential more security required is it safe is it in a location where not
everyone can access it and you've got recovery because there's always the human error there's always a human factor in which if there's a will there's a way and that can go down for two weeks for data breaches if someone wants to find a way in they will likely if not they'll just keep trying until they do same with employees if you force them to follow mfa on everything or do something that they just find tedious they'll find the way to do it lazily like making their passwords one two three four five six so on so recovery is something you need to always be ready for you need to make sure that you are ready to
say oh [ __ ] something's gone wrong let's make a nice public announcement say all right we're aware of this we're fixing it or we've fixed it but still slightly okay putting out the small fires at the end and then you've got the types of policies again this comes down to the count removal we were discussing a moment ago in whether or not you remove accounts after they've left after x months if an employee no longer requires access for it if it was like a six-month contract a six-month project if it's just for a quick oh hey i need a quick look into this do you even need an account at that point and then there's also password
policies so this comes down to two different factors as well so obviously password policies is your standard password lens different characters numbers capitals lowercase the standard stuff but then you can also enforce a password manager now this is a very touchy point for a lot of people is what's the best password manager out there opinions shout outs the one you use that's a good one exactly so you need to make sure your company's vetted out a password manager that they trust that their um certain is safe and then enforce your employees to use it so then they are following that their passwords are safe they're not in sticky notes sitting in starbucks sitting on your monitors
and that it then is done to the company itself for making sure that the passwords remain safe and then jumping onto portal media usbs i've totally not got a usb in this person's laptop and it could have had anything on it she's in there she has no idea anyway no it's only got this presentation like two three-year-old college work anyway and but that kind of is suggested that do you allow your employees to bring in your usbs to work on your devices but then it also is they bring your own device policies do you allow them to come in with their own laptops tablets mobile phones as well actually because coming in and connecting to the network
is opening up another vulnerability from it if they take this tablet home or connect to public wi-fi in different manners then their tablet is exposed to other things it might not always be on your secure network and that also comes then brings up the point of acceptable use so yes they might be able to come um at work they might work late every night and they might want to scroll through twitter or write it facebook catch up with some friends or something to make sure like just take a wee break and it's always good to do that it's always good to be taking me breaks be productive but what if they click on something sus
what if something is not what it seems to be there's probably tons of links on facebook twitter reddit that isn't the safest so do you stop your employees from visiting these sites all together do you stop them from visiting them do you limit what access they have one example of this is i find out recently unfortunately that the university don't allow you to watch videos in amazon prime in fairness i was just trying to watch indiana jones and jumping back to portal media as well when i used to work at starbucks ages ago that's about four years now originally when i started out you could plug your usb in no problem at all i used it because i
had to transport training videos between three different stores in scotland then all of a sudden when i was asked to do this again with the new updated training videos what's on and i can't use my usb and it's proof that they developed they've recognized that this is a threat and going with it and then there's also remote access and this has come up significantly in the last year and a half with work from home do you allow your employees to work off public-based websites if you've given them access to say all right that's fine go work out if a cafe today i know my manager i know guys my team have i know plenty of people have and
they say i'm working at cafeteria that's public wi-fi how does your network manage the traffic does it go through extra rigorous steps so different policies and different architectures on how to manage the traffic that's coming in from different locations is also a key factor and jumping back to the password policies most common passwords that were breached in 2020 and that's based on the top ten so going from one two three four five six one to nine picture one was a new one password one two seven eight one two three one three and then the new one at the bottom was senna this is a genuine question any idea anyone get any idea what that is
no good i'm not the only one but yeah so those were the top passwords and this is essentially can i does this yeah this this is what policy work is kind of like so i'm just gonna leave that playing
i thought there was something with it but well
i don't know if anyone works here with writing policies with managing policies but i'm sure they can maybe relate when i say people find a way if there's a will there's a way this is this is kind of what i mean but yeah and that brings us into information security management systems nest is a great one and iso 2701 nest is a bit more technical it's more control based and consists of a range of recommended best practices for your company to follow for you to in um impose on different situations in different places and it also recommends a way to manage that as well whereas iso is less technical is more focused on risk more on addressing the risk but
however there's a bit of a misconception and i was actually taught this at university i was taught this misconception just last year and when we're discussing information security management systems which is that you have to pick one you were to you're told to focus in on one and make that your best one but what really is best is to get a synergy from them both and from that it is better for data security and application security to have a combination of the two where you address the risk but you're also working based off controls as well so jumping into this the maturity rating is based on nist's five no 853 security models so this is the
com not compatibility um capability maturity model from which you're rated zero to five on a six number scale zero being you've done [ __ ] all to five being continuously improving and there's another table that's going to come in a minute which discusses the fact that this actually is not a fixed metric system this can vary based on the size of your organization if you're a small organization and you've only got a few stores you've got a decent sized network different decent sized company you've got your own size security team and everything then you probably want some greens across the board a good chunk of them so looking at this now you've got the capability maturities which you've
got capabilities capabilities right presented by x and y the outcomes from one to three so you've got the main principle from x and y and you want to take out you can take out however many you want but you want to kind of pinpoint the key points you want to come out with this one example of this is security within the system development life cycle and from that you pick out the key factors and then you assess how they're doing within your company are they being followed are they actually being protected is there things you can do to prove is there things that you're just absolutely ignoring based on the way you're rated and then you've got your
overall maturity score based on that as well so jumping back to the rating model you've got the continuously improving which means you've essentially got everything nailed down you can just keep going where you're going and keep adapting to everything new that comes your way then you've got four which is the maturity is defined as a metric driven practice and standardized practices and detailed metrics to allow for a governance oversight so you've got a good overview of everything that is going on when you get down to about three two you've got more of uh practices are there they're across the brand and they're maybe maybe could do it a bit more then you get them to two whereas you know they're
there you know they should be there they're not there and then one and zero if you're at one in zero and you're a large organization you should be concerned that should not be the case and then it comes down to the tooling as well so you can't just assess the maturity of your domains and how they're running things and how they're managing things you have to assess the tools and um the the platforms in place as well and to do that you've got so this is a very rough draft i threw together hence general firewall question mark and you've got your different devices where you have to assess for like a laptop and ipads or your tablet your
desktops anything like that you have to assess the tooling and operational maturity of them both so i screwed up when making those cells but then you have to go through each device so if you've got a cisco firewall palatal and generic firewall they're obviously different placed across your network if you've got a different architecture for different ways traffic comes into your organization you're going to want to place them in specific areas so that if you've got tablet coming in obviously that's maybe a company tablet is it localized is it for so one example for tsp would be is it a branch tablet is it something used internally or is it your employee's tablet is it something they bring in
like a work from home is it bring your own device laptop will redefine where [Music] the traffic flows and redefine where the firewalls encounter its traffic so to assess the maturity of that you have to ensure that you've covered the basis and that they're actually being monitored and re-reassessed regularly as well and that brings us my press the wrong button that brings us back to the table i mentioned a minute ago where based on the size of your organization for a small organization if you're in zero you've got nothing there fair but for medium to large organizations that shouldn't be the case if you are coming down to five now it's unrealistic for kind of small based
medium-based organizations to have that type of thing this is based on a source by the way this is my opinion it's based on a source you'll see at the end of the presentation however that's based on a unrealistic uh goal for a small organization you might think you'll be there but there are things you're obviously not going to be able to afford or able to do due to lack of skill lack of financing and jumping onto the next thing another thing to do when assessing maturity levels you can't just take them for their face value sometimes you need evidence attestation are you going to get them to give code samples if they're providing an application or if they're writing
a code to run within your organization one example of this is i um wrote a webscraper or something for uh coursework ages ago and if i was to use it in my company is it trusted do they want to see what it does do they want to see that it's not doing anything male content can provide it they can review it and say yeah no that looks good to go then you've got the discussion with the team so obviously you want to discuss with your actual different domains on a regular basis that you are reviewing where they sit on the maturity levels and that you are coming back and reviewing that they're following the policies you've put in
place the capabilities that you're assessing them against and you want to make sure that you're not doing okay or going on a downward slope it's okay for me level and as soon as you get to the maybe like the fourth level we discussed a moment ago then you're kind of doing all right it's okay not to have any fives because it just gives you more to strive for but then you also want to see if they have any policy documentation so if they're they're working with azure if they're working for a juror to assess threats then uh sentinel sorry is your stencil is what i'm thinking of if they're working with that to assess threats coming into
the organization attacks heading your way do they have any documentation for the rules and alerts they've got set up or work more importantly if you've got firewalls sat on the network do you have any policy documentation for what is and what is not allowed is that documentation following the capabilities and the constraints and the policies defined previously and yeah i'm noticing that i'm a bit short on time so i'm just going to wrap it up there there's the references i mentioned the common most password list and that table i found if anyone wants to contest that any questions i'll excellent can we get a round of applause please it's very fun thank you very much i can oh it's dark
it's kind of cooler with the lights can we get show hands if anybody has questions good in front cool yep chris you're up so out of uh everything that you explained which um uh which model is your favorite so personally when i came back to that coursework that i mentioned previously i actually looked more at nist uh not necessarily i avoided this because it seemed a bit messy at the time and i went with iso and i realized iso was just as messy so personally i do prefer nist because they've got the nice tables as i just demonstrated to follow the capability maturities so yeah this is probably my go-to next anybody else oh this is not really a question but i did
some rapid googling and apparently sen hat is portuguese for password you're kidding nice password's cool just in a different language kind of reminiscent of the oshko 321 password story if you ever heard of that and they found out it was the russian for butthole that was a really interesting talk i hadn't heard of that one either anybody else have any more questions cool well final round of applause for johnny please