Every Contact Leaves A Trace by Ken Westin
Show transcript [en]
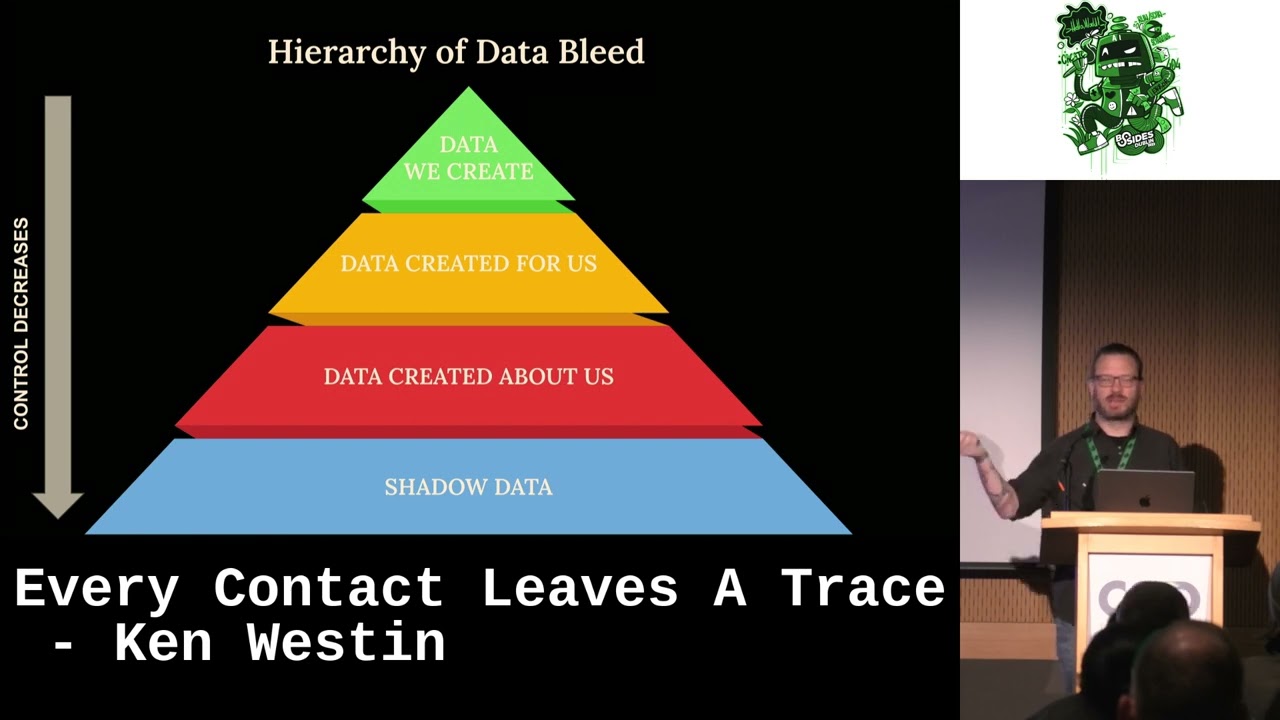
great so uh yes uh hi my name is Ken Weston um today I'm going to be talking about every contact leaves a trace I'm going to talk about this some investigations that I've been part of I've been involved in security for a little over 15 years now um again I live on the Oregon coast I currently work for a company called Panther we're a modern Sim I'm not sure if anyone doing the purple teaming workshop with me today okay I got one person in the workshop great um so uh yes we'll be doing uh some fun things with some Sim and some investigations and running defensive operations on OCTA so it's gonna be a lot of fun if you have space you know recommend you show up um so uh yeah I've been involved in security for the last 15 years but prior to working for various vendors I've really like doing investigations so I've worked for companies like Splunk elastic I really like the analytics space and really trying to do Deep dive investigations particularly with a lot of times pieces of data that people may not consider forensic artifacts and things like that so I'm going to talk about some investigations that I've done where I've actually unveiled organized crime rings and also talk about how some of these tools and techniques that I've used can also be used against you one of the challenges I think that we have right now is that a lot of marketing especially in the US they have a lot of information around you so when information gets compromised it actually makes you a bigger Target and a lot of people aren't aware of some of that so this is what I kind of refer to as my Wall of Shame so these are photos of people that I've actually put in prison um I had some technology that I was actually tracking um around stolen devices so it was a kind of fun little startup where you deploy an agent and then if it got stolen you'd activate a web camera I would get location from Wi-Fi networks do all the really fun things and along the way I ended up getting really heavily involved in helping law enforcement I know you guys may not believe this but sometimes law enforcement are incredibly lazy and a lot of times they don't have the some of the resources to and or some of the tools to be able to conduct some of these investigations and sometimes they would piss me off and so that's when I would go out and I would try to dig a little bit deeper so I would gather more information around some of my targets and as a result of that I ended up unveiling organized crime Rings there was a lot of Russian organized crime groups in particular and where I live and um they would fence stolen a property a bunch of other things that were they were doing that were pretty nasty um so uh I did a presentation around this at Defcon 23. um and of course uh you know the the talk I I titled it you know confessions of professional cyber stalker I thought it was being funny um but of course the BBC then says hey I'm a professional cyber stalker and they put this big face up there uh motherboard called me the real real life Mr Robot so if you ever want to get become a docs Target um you know get these kind of headlines it's all horse crap it's I'm not I'm not that great if I have a hacker I'm actually incredibly lazy you'll you'll kind of see that um so I'm kind of curious did anyone know who this is this photo has anyone ever taken a forensics class like not digital forensics but like real forensics like all right so this is Edmund lecard so Edmund lecard was he was sort of the forensic uh I guess the grandfather of forensic science they referred to him in France as the um like whatever the French uh it was like a great investigator right uh Sherlock Holmes The Great the French Sherlock Holmes so he actually uh developed a lot of the concepts that we have for forensic science today um he uh his before DNA he was born in 1877. um this was before DNA and fingerprints and all that stuff but a lot of the things that he was telling us about forensic science are things that we learned I mean he has this concept um and it's called a lecard's exchange principle and it's every contact leaves a trace now the idea behind this is that when someone commits a crime let's say a murder the idea is that they leave something behind but they also take something with them and what I found true when I was I started reading about this guy I was like this carries over so much into the digital world the trick is how do we know where that data data might reside there's always a way there's always a trace there's always something in a log that we can actually identify a suspect there's got to be a way for us to do it when someone's committing a digital crime what have you and I'm finding that this is even more so now we have iot like we carry our devices with us everywhere pretty much any sort of Investigation into a crime that's happening now is going to have a digital or a forensics component so just kind of keep that in mind if you're going to commit a crime make sure you leave your cell phone at home so uh you kind of think about this I kind of think about this as like the Quantified Self cell phone you think about all the pieces of data that you actually have about you and they're sort of these little artifacts you have your social security number in the US you have you know these device IDs phone numbers Mac addresses you think about all these little pieces of information out there we're actually leaving trails of this every single device that we have our our watches on all of our maybe home automation systems that we have like everything that we're doing here we're actually leaving a digital exhaust uh Trail as as well the trick is being able to try to connect some of those dots when we're conducting investigations so um everyone here seeing these kind of things and you're like your your investigation like your CSI right they're called crazy walls so it's great to have all these little pieces of information but you really need to be able to connect those dots and what I found is once once you can connect one dot it may be part of another dot that's when an investigations really start to unveil themselves and you can actually get a lot of information about a particular individual or a particular group um you guys are familiar with Maslow's hierarchy of needs you might also be familiar with the Pyramid of pain with ttps so I I figured in infosec we all like our pyramids right so um this is what I like to refer to as the hierarchy of data bleed so it starts at the top as data that we create so it used to be you know back in the day before the cloud when we had our computers we had we had we had software we would run on a computer called Microsoft Office and we would be word and we would generate that we would generate these documents we wouldn't necessarily be sharing with them but that's information there as soon as I I upload that or I email that that's when um you know there's additional logs and traces that get associated with it but when we're interacting with websites and applications and apis what happens is there's actually data that gets created for us what happens here is as we start to move down this hierarchy that our control of that data gets lost particularly when we start to get further down the Spire here when we get into Data created about us so when I go and I buy a plane ticket right a lot lot of information gets sent to them to the airline the airline maybe cross references some of that information with no fly list there's a lot of places where this information is actually getting shared in almost real time and then we have Shadow data and that's where a lot of times we have data that gets compromised in data breaches we have sometimes that information is collected for us from like credit bureaus all sorts of information data Brokers people always talk about doxing back in the day as a form of hacking nowadays the only tool you really need to docs anyone is called a credit card that's all you need to be able to get information about particular individuals so if you get access to to this information whether it's from data Brokers or if it's compromised data Maybe from a breach you can actually you know search for that information in the dark web and get access to again a lot of information that you shouldn't really have but if you really are wanting to learn something about someone their passwords there's all these sorts of things it's very easy information to get nowadays which could scare the crap out of all of us so um how I got started with a lot of this stuff was um I was working for a company I was sort of a one-man web Army I was building their websites I ended up having to secure the web servers that was sort of my introduction to security just basically securing a lamp server um the company I worked for they then started selling a tool that would actually block USB flash drives there was an issue now like great we're securing the perimeter but if I can plug a flash drive into a computer I can install Trojans I can do all sorts of interesting things with stealing data and this tool that they were selling would actually block that and give you more control over who would be able to download or use those particular tools and so I got really interested in a lot of the black hat tools that were out there so I started downloading them playing with them started creating some of my own and I thought you know it'd be really great to build a website to raise awareness around this because this is a big issue very easy for me to download these tools put it on a flash drive plug it into a flash drive or a network and I can compromise the entire thing you guys ever heard of a little spyware or a piece of malware called stuxnet yeah that's how that's one of the attack factors where the USB flash drive I happen to work for some people that were involved in that um but uh um so I I wanted to uh create this just the idea here was to raise awareness right I didn't want to go out and show like here's a bunch of hacking tools go do crime um I wanted to raise awareness to administrators so I created a website called USB hacks where I would upload some of these tools explain how they work started creating my own um that was the first time the FBI contacted me um they are you know they want to know what the hell I was doing once they realized you know this is about raising awareness um and I even had situations where I had people that were true cyber criminals I think they were nation state actors actually reaching out to me asking me how to set up certain things it sounded like sometimes they actually had um an Insider in some of these facilities and they were looking for help and how to compromise networks I just forwarded those on to the FBI right away like hey see like I'm helping you um and uh yeah I end up collaborating with them on a lot of Investigations later on this doesn't work there we go um so basically what I did was I decided to take some of the the malware um that was being written and um I was working on my Master's dissertation at the time and I was like what there's got to be a way to turn this into a good thing um and I started messing around a lot of my friends I would be putting these flash drives on um or the the malware on flash drives and send it to my friends you know see them plug it in um you know I'd send all this other information that was able to get about their computer and I said hey I'm going to put this out there and see if people are interested in this for theft recovery purposes so if someone steals a flash drive or an external drive you know the idea here is it has this USB Trojan you plug it into the computer it hijacks the computer it's connected to when you try to access the drive and it sends information to the Mothership the username the IP address and things like that and I was just curious I put it up on dig.com so for those of you who are young it's like Reddit for old people like back in the day um it got on the home page and it got dug to death I twenty thousand people sign up for this free service and what was awesome about this is I was basically crowd sourcing what devices were actually supported because I had a little bit of code in there that would actually tell me what devices were being uh were being accessed so I found it was working with external flash drives I found those working with the old school GPS devices I know it's hard to believe that it wasn't actually in your car like you know just kind of letting you guys know how old I am but I even have the specific models and everything and then that's when I decided I was actually going to do a little startup around some of this stuff and it actually worked I started actually getting people that were installing on um on like iPods and there would be that people would change their usernames and their family this were very easy for us to identify who actually unstole the iPod most stuff was like high school kids things like that screwing around with this stuff and then it got uh pretty serious I got one case where a university Professor had installed it on his flash drive where he had his PhD dissertation um and he had a student that looks like they they stole the flash drive off of his desk and it was difficult because initially we were getting just an um IP pings from just a t like an ISP it's very difficult to get information just from an IP address unless you have law enforcement involved to actually fill out all the paperwork and again I'm lazy and a lot of law enforcement are lazy so we don't want to deal with that but I started getting additional connections from the University of North Texas and then I contacted their campus security and they on their I.T folks and they work with me we're able to identify that in that particular IP range it was actually one specific computer lab the year prior they had actually had a bunch of laptops stolen or a computer stolen out of that particular lab so they actually installed cameras and they also have this these sort of card swipers so I was able to give them the time when this occurred the computer that was affected and we're able to figure out specifically who was actually in that room at that time and there was only two or three students and they were able to narrow down to one they waited outside of a class as he was leaving and they were able to get the flash drive back but it was just an interesting thing is that we had IP address but it wasn't until we had access to all this other information we had a video of the person doing their card swipe right so we had plenty of evidence to identify who specifically that was um and then um I kind of got a lot of noise in the media and there's this company called FLIR anyone heard a Fleer before they make a very high-end thermal imaging cameras these cameras cost anywhere from like three thousand to three hundred thousand dollars um and they were really interested in this not just for theft recovery they want to offer it as a sort of a premium service but also they were having issues with export controls these are devices that are not allowed to be um they're an embargoed into certain countries because they can be used for nuclear purposes um and they were running into situations where these cameras were showing up in places they shouldn't and they wanted to see if they can utilize my technology to solve it one challenge we had though is that the the agent would get installed on the SD card and one thing is if someone rips the SD card out and then puts a new one in right the agent's gone so I actually work with them to actually embed something in the firmware so it would actually look for the SD card if it was new is the agent been deployed if not redeploy the agent along with some other files and then I disguise the the the executable and that's my cat knobby there's a thermal image camera so that's why I disguise the application as and they ended up using this for quite a few cases they they got a few cases where it was stolen um they couldn't tell me specifically where um but they did also track down um a couple of cases where uh devices were being sold by a particular distributor they were going to countries that they shouldn't be selling they couldn't give me all the details because you know of course investigations but it did work so that was the important thing um so then I I started getting interested more and okay the flash drives are great but what about laptops I started looking at the time and they actually had a company um called it was like LoJack for laptops it was a company by copy Trace they actually licensed the name and I was looking at how they were actually doing their theft recovery and it was incredibly invasive and basically when you have this technology you provide a back door into your computer and they hire like ex-law enforcement folks um and then if you get it gets stolen then they can log into your your computer and they can do various things for tracking it um and I was like there's got to be a different way at that time the first iPhone was just being released and I noticed that it didn't have a GPS chip but it was able to get location what they're able to do is use Wi-Fi location and so I contacted the company that um that made it called Skyhook and I said I want to I have this idea I want to apply this for theft recovery purposes for Max will you work with me and they gave me access to the API and we set it up so that if someone steals your laptop will activate tracking um and um I didn't want to have a server uh at this time I didn't want to have to deal with like photos you know being sent to my server then I have to secure it again I'm lazy I don't want to deal with that um and it's it's also a big issue if someone does get that compromise that server um you know there are certain liabilities associated with that when I can activate someone's web camera and send a photo every 30 minutes right uh so I I integrate with Flickr so if you you sign up for your Flickr account you download the software um and then you would activate tracking that's all you would do on our our end uh and then it would send photos it would send the GPS the GPS coordinates um uh to your Flickr account and it actually worked we actually ended up getting my first recovery it was this uh it was in New York it was a it was an iMac Not only was the iMac stolen but a bunch of camera equipment was also stolen from someone's apartment and we activated tracking and I was getting these uh photos and you'll see in the the background here there's a lot of other interesting toys like uh mixers tars you got all these musical instruments almost like a pawn shop and I had to work with law enforcement on this one and it was this cop from New York he was kind of an sorry I shouldn't swear but um but he was a real jerk and uh he um he's like you know I haven't had to deal with this stuff before you know I've dealt with his competrees jokes I have to get this IP address I got to go fill all this paperwork out to get information from the ISP and I'm like no no this is a wholly different approach like I I got the Wi-Fi positions within 10 to 20 meters of where it actually is um and and then all you need to do is just print a photo out here just ask around and he's like don't tell me how to do my job I was like okay like just do it of course he did it and uh come to find out it was actually a tattoo parlor and this was the owner um and he this is the office in the in the back they went in and they actually ended up recovering all sorts of other stolen property he was running a fencing operation out of the back of his tattoo parlor um and uh there was like four or five other laptops that were recovered in this one so is that when I said we had a 500 recovery great um but uh that was that was the first one that we had and then there was a bunch of other ones that we had in Portland Oregon where I li





