Keynote

Show transcript [en]
think of Jefferson Airplane White Rabbit 1967. let's take you back I've got the lyrics here one pill makes you larger one pill makes you small and uh yeah let's take Ken's hand and let let him lead us down the rabbit hole
okay uh so uh yeah my name is Ken Weston I live here in Portland Oregon uh I want to thank besides for having me it's quite an honor to actually be asked to Keynote here I've been born and raised here in Portland I'm going to be talking about going down the rabbit hole and I'll tell you what that means in just a little bit but I am an organ native I actually grew up without the internet so that tells you that how old I am um uh I actually didn't get really involved in computers until late probably high school or so really I actually have some learning disabilities one of them was dysgraphia so I I was
raised a lot um well with schools I didn't do so well I always thought I was really stupid but once I was actually diagnosed and they actually identify what it was I was able to get access to computers and all of a sudden I felt like I had a superpower I was always struggling with how to communicate things like that and now using computers I was doing really well I was able to do a lot of writing I had a lot to say I ended up going to college I went to Lewis and Clark I got an English degree because I loved writing I took all the free classes that they had at the time
around this thing called the internet that was starting to be a big deal so I learned how to build web pages I got really excited about this and started to really like get into technology my first job out of college was actually the sake Brewery where I actually ended up not just working in The Tasting Room but I actually built an online store to sell rice wine things like that then I went to work for a startup and things like that I even ended up working at Pacific University where I was on their first webmaster I also ended up being an adject instructor a nice thing about being there is that I got to take all
the free classes I wanted so I took all the computer science courses I possibly could I then transferred and got a master's degree in Internet systems development um uh and then I went to work and a lot of startups and things I was doing a lot of web development started getting more into web administrator uh started doing a web application development things like that and that's when I started getting involved in security um and so I'll start to talk a little bit about that and how I kind of fell down the rabbit hole in a lot of respects when it came to security and how it led to other rabbit holes along the way so the idea here is I'm going to
talk about some of the investigations I've been part of how that led to development of Technologies and things like that and really how it kind of led to my career and where I am today um I'm also my hobbies I play guitar I play in a band called sevilla's ghost here in Portland sometimes we uh we play McMenamins and things like that I'm also a record hoarder um and uh yeah if you guys ever want to jam let me know so what do I mean by rabbit holes um when I look at security particularly I think some of us particularly with like ADHD we understand what a rabbit hole is uh we have some challenges when
it comes to organization and things like that but when you get us hyper focused on something we don't stop we do not give up right and sometimes that can be a good thing sometimes that can be a bad thing and it can also set you up for Burnout also on the other side of that I think it's also this effing around and finding out it's experimenting it's about trying new things and I think what really attracted me security was that ability to be able to innovate to be able to go down these rabbit holes to be able to try new things you can't necessarily do to utilize technology in ways that they weren't meant to be
utilized and even break it at some point so I kind of pulled a few quotes because uh you know going down the rabbit hole the idiom the metaphor actually comes from Alice in Wonderland uh with a great story uh you know we talk about going down rabbit holes um and it's interesting is like sometimes I wake up and I'm like how the heck did I get here and then I realized you know it wasn't just me alone like what I was able to actually rely on a community and um we always talk about the the caterpillar uh or you know we're all mad here right I think everyone is doing security they're a little bit I
think a little bit different than you might find in other areas of technology and other um in other sectors as well um and uh I think that Rings true for for most of us um so um a while back when I was doing uh security I ended up having a startup I I got involved in um riding some usb-based Trojans I was really interested in it and I was trying to find ways to actually utilize this technology for good for actually tracking stolen devices this led me down to multiple rabbit holes I ended up developing technology to track USB devices laptops mobile phones even started getting into tracking stolen cameras by looking at exif data that's embedded in images and
building search engines that were around that I actually presented this at Defcon it was Defcon 23. it was kind of my first time actually presenting a big conference scared the crap out of me but I'm glad I did it but of course after I did that when I was talking about these recoveries um I even got a lot of media exposure so media exposure that wasn't so good sometimes being called a professional cyber stalker being called to realize Mr Robot you can imagine how that puts a nice big Target on your back for doxing and things like that at um but this was great I actually ended up becoming a talking head I've worked at tripwire I had the opportunity to
talk to the media a lot I think even like Travis here refers to me as a media I think he's just jealous because he's always stealing my slides um but you know it was a it was it was actually a really good thing I was able to get out there the startup that I had it failed and it was probably one of the lowest points of my life I had a really hard time but once I I kind of came out of it and I was going out in the sector I realized just how much I learned in that process so I'm going to walk you guys through some of the investigations I worked on and talk about how you know
how I think about running investigations and also how some of those investigations led to new Innovations so when you think about doing investigations it's it's never just like one alert like if you're doing instant response you know you can't just rely on one alert you have to be able to Pivot maybe you're using Splunk or other other data sources um it's always going to be gathering a lot of different um sources if you ever look at any of the sort of murder shows or any detective shows you always see these walls where they're drawing lines between um you know the pieces of evidence they're called crazy walls appropriately named and that's really how A lot of
these investigations start you may start with one piece of information but you're going to Pivot and then it's really not necessarily technical exercise it's really a exercise of creativity to be able to identify and make more sense of that particular alert does anyone know who this guy is very close yes forensics this is the OG hacker when it comes to uh criminals his name is Edmund lecard um he's the grandfather of forensic science he actually developed a lot of like forensic techniques even fingerprints that we utilize today some of the techniques he actually pioneered he was referred to as the Sherlock Holmes of uh in France this was in like I think he died in 1966 or so but he really
developed a lot of the techniques and he had this concept this sort of Axiom is every contact leaves the trace and I was reading about him and I was like holy crap this is it his idea was that this is dealing with physical crimes where when you commit a crime you leave something and you take something with you and I was thinking about this when it comes to investigations I'd say every digital contact also leaves a trace it's just a matter of do we have the the mechanisms to detect it do we have the ways to actually archive or sorry search for that data and you'll kind of see that as we go through some of these
investigations so I was working for a company before I was doing web development I was sort of a one-man web Army I was my only experience with security at that point was securing a web server I was responsible for basically securing a lamp stack but the company I worked for started building a product that would actually block USB flash drives this became a big issue with things like auto run Windows XP things like that it was becoming a really big problem where you know forget trying to hack a network if I can actually plug a flash drive into a computer it's a heck of a lot easier for me to compromise that Network also there's tools that would actually allow
me to slurp data I can grab all sorts of information from it and so they wanted to be able to block it and I got really interested in this they started looking into some of these tools and I was like this is neat and I started actually playing with them and actually started writing some of my own and I was like I'm going to build a website to raise awareness around this so I I was called usbhacks.com I put it up and actually started putting up some of these tools and the idea here was that you could download them and you could play with them and to raise awareness anyway that was the first time the FBI contacted me
but uh once I explained to them what I was trying to do in the intent you know this is kind of what we're talking about with security research now you know you know hacking is not a crime and uh when they started realizing my intent and in some cases I actually even helped them in some cases where I had some really weird people that were approaching me um in one case there was a guy that was approached me that um uh looked like he had a physical access to a facility and he was asking for some specific payloads in asking if I would help I actually sent that over to the FBI because this was really fishy
come to find out yes he was a well-known bad guy uh bad hacker in in the Middle East and um they they thanked me for it so anyway check out the FBI off my back for a little while so uh next idea was how do I turn that into something that's actually useful I started playing with it and at the time I was actually working on my Master's Degree and I was like you know I was playing with this and um uh you know messing with friends sending them flash drives that we do all sorts of nasty things to their computer pop-ups things like that direct them to fun websites um and so I said well what if I did this
for theft recovery so I built a little a friendly Trojan that went executed it would hijack the computer it's connected to gather user information and then it would send it to a Mothership and I tested this out I was like I'm going to put it on dig.com so um who anyone know dig.com all right for all the kids out there dig.com is like uh Reddit for old people okay um uh so uh and the idea was you know I just I wanted to get a few people to test it and uh it ended up being on the homepage of dig um and I ended up having like 20 000 devices um of being registered I could I can't
believe the server actually held up um but I also utilized that when they're running the agents I was gathering information about the devices that they were connected so I actually created this huge database of all of the potential devices that I could compromise with on this these executables um and uh we even started getting some recoveries it was really interesting um you know we were covering iPods we were covering all these different devices and this is the information we were able to gather it was really simple it was just you know internal Network information IP address getting some geoip location um the username and things like that which would be really helpful but you know I really wanted to limit it I
didn't want to you know go go nasty like with some of these things I could have you know gotten credentials and done a lot more malicious things but the idea here was just what do I need to be able to track on that device and where it is if it got stolen and then I had another case where it got a lot more interesting um we had a professor who had his dissertation that was taken off of a flash drive from his desk um and it was this is a time where I was like okay I'll see if I can help I started looking at the data and we were getting connections from uh an ISP
that's not really helpful it gives me the IP address but unless I get like a subpoena from law enforcement to go in and actually get the address and all that it's not going to be useful and that could take anywhere from weeks to months if you can get it at all but then we started getting connections from a computer lab um in a uh at the University of North Texas what's interesting is we were able to actually identify a specific computer lab just from the internal Network information and then we cut talking to campus security we realized that they'd actually put in cameras and some key cars because they recently had a bunch of laptop thefts so we were able to
correlate the time stamps that we had on the USB connection uh the the internet connections from the USB Trojan to the the key swipes as well as the camera and we're able to identify who is in the room at the time and they were able to get a recovery so this is kind of those crazy well types of things where you start looking at not just the that data source you start to look at other data sources that are available for your investigation and they ended up getting it back I'm not sure if the kid actually stole it or they took it but the important thing is that he he got his dissertation information back and also
another reason why you need backups and then uh I was getting a lot of press with some of this stuff and I was approached by FLIR and they make very high-end thermal imaging cameras now these cameras cost anywhere from three thousand to three hundred thousand dollars and I ended up selling idea this was one of my my bigger deals and this is actually around the time I quit my job and started focusing on this full time I was able to not only build the Trojans because we had a challenge with this because if it wrote to an SD card if you take the SD card out great you put a new one in then we don't have the
agent so this is where we actually installed something in the firmware that would check to see if the agent was enabled if it wasn't then it would rewrite it and we're able to get access to it what's interesting with this too is that it wasn't just used for theft recovery they had issues with export controls some of these devices are not allowed to be in certain countries and they had situations where they were being sold to some of these countries they were showing up in Iran for example and so they couldn't tell me all the details but they did utilize this to identify a distributor that might have been selling places they shouldn't and you'll notice that there's this little
cat here I actually disguised the the um the Trojan on the on the card as my cat they gave me some of the thermal engine cameras I got to play with them and that's my cat and hobby so then further down the rabbit hole I was like okay this is all fun and all but um well let's go after Stephanie that actually has a lot more value at the time laptops well at the time laptops all had most of them were coming out with web cameras and it wasn't necessarily being utilized I think there was one Mac developer that was utilizing that for uh for some things but um you know it's that's helpful but you
don't have all the information that you need um I though at the time there was the iPhone that came out and I was interested because the first iPhone didn't have a GPS chip it was able to get location and it was using um a Wi-Fi for a location and I dug deeper into it and I contacted the company that had that technology called Skyhook Wireless and I was able to actually put that into the product so this is the first time we actually had a laptop a theft recovery product that when you activate tracking it will gather the photo of the person that's using your computer it would also gather other information about the network and then we'll also get the
location of that device and it was accurate within five to ten meters and at the time I didn't want to have to secure a server and I was also really concerned about privacy because I didn't I wanted to make sure that if we're going to gather people's photos and things like that that you know we have that secured uh we also I was worried about what if we get hacked and all of a sudden now someone's photos are compromised so instead of me taking that on that liability I integrate with Flickr so you would integrate with your Flickr account and then that was only thing I tracked is if you had tracking activated offer on we then over time we
we modified that and we did have a central server to control all this when I actually got some funding and I was able to hire real developers to um to help build that architecture out we actually got our first recovery it was in Brooklyn New York um uh this was really interesting it was a a guy he had an iMac and he had a bunch of camera equipment that were stolen from his house and I got a call from a New York detective and he was really frustrated he was like he was kind of mad about these types of things because it was another company that was doing theft recovery and it's a it's a
lot of paperwork he had to file because it's iip address you have to get the go to the care the ISP you have to you know write all this information validate it I'm going to take anywhere from two weeks to several months and he was like frustrated he was like this is a waste of my time and I'm like no I'm getting location we have Wi-Fi location look just take a photo of this photo and then go look around that area and ask people around and then of course he told me not no not to you know tell him how to do his job or whatever but he finally did it and and sure enough they found the
laptop it was in the back of a tattoo parlor this is the back of an office and if you see there's a bunch of other really cool stuff like mixers and audio equipment they went in and they found all sorts of on property and this is where I started realizing that this is how I can actually get law enforcement to care they don't care about the individuals or laptops but if I can unveil larger organized crime Rings if I can find other fencing operations and I can find these larger things that are being done then that's when they become the hero and and we started doing a lot more of that
so this was a really fun case there was a bunch of uh schools in Portland here that were getting hit repeatedly it was the weirdest thing like they would have a bunch of laptops stolen they would replace them and then a week or two later they would be stolen again and they couldn't figure out why how it was happening and so we decided let's give them some bait laptops so they they put them out and sure enough within two weeks they started they got stolen and we started getting connections and you can see there's a photo of the fellow and the detective went out there it was actually traced to Vancouver and the the I told slain the police officer what
what their detective what you want to do just you know it's within 10 to 20 meters he goes there and knocks on the door and the guy that works on his roof answers the door and he's like you don't know what you're talking about Ken like this is I know this guy you know you're wasting our time I got mad so I drove out there to Vancouver I'm sitting there and I was actually scanning the Wi-Fi network to make sure that the information we were gathering was correct now one of the Wi-Fi networks that was on on there was it was said Russia and then I looked over and there was like where the detective had gone it
was a duplex he had gone to the one on the left and the one on the right there's a car right in front of the driveway with this giant Russian pride bumper sticker so I'm I'm there and I'm actually I had my laptop open and I swear the guy actually walks out the door and he looks at me and I'm like an idiot on my laptop with this huge antenna sticking out of my car and I'm just like actually I'm like acting like I'm lost like oh I'm just looking for directions or whatever I don't think you suspect anything but I told the detectives they finally came out um and uh and they said they they ended
up getting them um I thought I was going to have to testify this was kind of a scary time I found out these guys were um pretty bad news um he even like the guy even told me it's like yeah it's not that guy you got to worry about it um he's actually friends with the guy across the street like he's part of his gang um the where you have your car parked right now in front of his house he's really bad news but they they ended up um uh busting there was like six or seven people that were involved I didn't have to be involved in to testify they listed me as an anonymous whatever
source and they got them all to turn on each other thinking that they had all ratted each other out so I was I was relieved uh we had another interesting case where um this one was this is where I started getting really a lot more into the OS inside of things on the investigations uh we had a laptop that was stolen and I didn't get any connections for like two weeks I was like ah crap they probably reformatted the drive or sold it for parts or something like that but then we started getting Connections in Missouri I'm like what the hell and we were getting tons of photos there was this guy named Victor it was really nice of
him because he actually changed the username on the computer to his full name so I had first name last name it was great so when I looked him up I found all kinds of stuff he was a big car nut so Scions really he really liked those cars he's only forums and so he posted photos of his car so he also had a license plate number on his Myspace and then on eBay he was a big eBay seller and he was selling used car parts so you can kind of get an idea of the business working with the police this was the first case we actually provided this to district attorney and they said holy crap you have so much evidence here
like even if they don't have the laptop we can still bust them for possession of stolen property he ended up selling the laptop in a stolen bike to his friend Omar I found out that he actually received the bike and the laptop from his father who was actually part of this group what they do is they they there was two another Russian organized crime group they they work in Missouri and then Portland they basically share stolen property because if you get something stolen here in Portland where's the first place you're going to look Craigslist locally so what they did was they they still bunch of property loaded up into a white truck driving to Missouri exchange goods and then that's
how they're able to defend some of this this stuff so this was a really interesting case we started getting a better understanding of how some of these these groups are actually operating it also worked internationally um we had a friend Skye Alberto who's in Brazil he was a Veterinary student he was in a car with a friend they were held at gunpoint told to get out of the car his friend was punched and knocked down to the ground and they took off with the car with his laptop in the back seat we were able to get connections we were getting photos on the Brazilian police at the time they were they work closely with us because they uh I guess
these guys were involved in a lot of these cases and I think their their one person was in the hospital he almost died and that they had attacked so it was kind of nice like we're not just solving you know your cyber crimes and things like that we're also helping to solve physical crimes
so again further down the rabbit hole like I was like what else more can we do at the time smartphones are becoming much more prominent and what I found is that people don't really care too much about the value of the device itself what they really cared about was the data um but I was really nervous again I didn't want to like um or you know back up people's photos or contact information things like that so we actually built a way that you would actually put an encryption key on your phone only you knew it and then when you activate tracking or whatever you could download this a file and then you would decrypt it with that key so I
never had the decryption key there's no way I could view anyone's photos and this is helpful too like if law enforcement came to us and said hey we need this person's information I'm like well here's the The Blob of data you're going to have to go to them to get the encryption key and that provide a little bit of Peace of Mind when we were doing this but we had some interesting recoveries and I'm gonna I think I got a video here so I can stop talking for a minute or that's helping track them down NewsChannel 8 said teachout spent the past two days with police and investigators on the trail of swiped cell phones he's live outside the
Washington Square Mall where the theft took place at well the managers of the Sprint Store here at the Washington Square Mall behind me say they're very confident that tracking software developed only miles away from here and put onto their demo phones will lead to an arrest uh this is a 500 phone this ends up being a 450 phone two empty display cradles Are All That Remains after someone stole two demo cell phones from the Sprint store at Washington Square Mall on Saturday moments after surveillance video caught the theft on tape employees initiated tracking software installed on the stolen phones they were able to not only find the GPS location of the individuals that took them but also we've been able to uh to
monitor any activity that happens in the phone that activity turned out to be pictures someone took shortly after the phones were stolen Tigard police admit It's A Brave New World when pictures taken on cell phones can be told to send back pictures once they're stolen and that has not only piqued the interest of our investigators but in essence appears at this point could be very credible information for us to follow up on the Portland creator of the software tracking the theft says police are on the right track if they're not the thieves they definitely know who stole it and if you look over the head of this man you'll see in the window an organ
temporary permit Philip this is Ed with the help of a gadget track investigator on the phone we tracked the stolen phone signal to this Vancouver apartment complex there we found the exact temporary permit and hi a young woman who told us off camera a man she called Peter had sent this photo to her Saturday evening but says she knew nothing about the phones hi my name is we tracked the second cell phone signal to this duplex about eight blocks away you don't have an a Samsung Epic phone in this location police were here yesterday looking for it we're back live now outside the Washington Square Mall where we've just obtained within the hour those DMV
records on that temporary permit tiger police say they hope the men in the pictures will contact them soon so they can explain how their faces ended up on a stolen cell phone back to you thank you Ed teachout the contractor is accused of overspraying anyway that was um that was actually a lot of fun to work on that particular case uh um there were some challenges with it uh some of the the GPS coordinates that we're actually getting sent back weren't very reliable but what I did find was that we were able to get the the images again the Sprint store chain that actually had stalled this they gave me the encryption key to go
ahead and decrypt the the images and I found that there was a bunch of data that was actually embedded in the images that they were taking so those photos actually had the GPS coordinates and those were much more accurate that led me down to another rabbit hole on exif data but um one thing that uh nope back in the slides that's helping track but one thing I should say is that you know this is an application that people installed on their devices willingly right so if you steal my device I have the right to go ahead and I can activate track and I can do that um what's scary to me now is the direction that this is gone
um it's to a point now where we have a commercial spyware vendors that are providing technology that are leveraging zero day vulnerabilities against their citizens and this is I think is something that should raise concern that's helping one example is the NSO group have you all heard of Pegasus okay um so this is really worries me um you know they these these companies they'll say that hey these are uh we only do it for terrorists people that are criminals well who's a criminal how do you define a criminal some of these are being utilized um in in countries where you have very uh authoritative regimes this uh they're deploying some of these Technologies to people that they consider enemies that
are journalists that are dissidents and things like that and I think this is uh there's actually a case right now with the the EU and the Pega committee that are trying to control how we're deploying some of the software the NSO group is now blacklisted in the U.S there's been a lot of disinformation around this particular technology and things like that I've been doing my part to try to help to um to stop some of this this information but what's really interesting is that the community the infosec communities really come together to help stop this particular Threat by in many ways but uh just something I wanted to put as an aside uh but um kind
of go back to this I got really interested in the exif data again um I even built a tool if you go to exit.io you can actually upload images and it'll look for any um any valuable information that I might be able to find um in an image it'll look for GPS coordinates it'll look for the make and model of a camera and things like that um so I got really interested in this and I found that looking at maxif data a lot of the high-end cameras were actually embedding the make model and the serial number of the camera and I had this Theory well what if I was able to create a database if I could get all
these different images and the serial numbers and you could search for the serial number of your camera and we'll show you all the places online that we found on that photo uh our photos were taken by that camera um it was um sort of an experiment I did um we had uh I had like maybe a few computers I was doing this on I was trying to index all of Flickr for example and I was just doing these Python and PHP scripts and I was like this is going to take forever it probably take me like 10 years to mine the whole thing but I had a friend that had a startup and he had this thing
where they're doing it where it's basically a legal botnet where it's kind of like a study at home where universities can provide their idle computer labs to go ahead and we can deploy you can put workloads to those computer labs and it's a lot cheaper than trying to go to the cloud so experiment I think we had over a thousand computers that were doing this and I just basically deployed my shitty python script I do have these Thousand Ones and we're able to actually index all of Flickr I also down was able to index some other websites where I was finding this data even Twitter I found that even though you upload an image to
Twitter it will scrub that information but I found for some reason a lot of the profiles photos didn't have it so I was finding these tiny little icons that how GPS coordinates and things like that so I was just bringing that in for um to see what I could find but the idea here was we did create this database and I put it out there and people started using it for free and holy crap it worked this guy named John Heller um he was on assignment for uh Getty Images at the Egyptian Theater he was talking to someone he turned around and nine thousand dollars worth of camera equipment was gone you heard about the
service that I built and he did a search and it's important to point out this was a year later about a year later and uh he uh found it uh we he found the image on Flickr and then he found that that account was also tied to a professional photographer on Facebook who had photos of all his professional camera gear and there was this camera um and so he uh the LAPD were involved um and so what the cat what happened was um the guy that stole it from him sold it on Craigslist he then went and um that person stole it on eBay and then the police recovered it the police went to the guy that got on eBay he had to
hire a lawyer he had to be able to prove that he didn't steal it and he ended up getting the money back from the seller they trace it back to the guy on Craigslist and the guy on Craigslist oh yeah I remember where I bought the camera it was this apartment I still have the address I have the text message the police went there this a year later they go to the apartment and they found all sorts of stolen property right so I just think this is interesting is that the serial number of a camera that was embedded in an image led to the unveiling of this type of crime and I always think about what other types of
of crimes can we solve if we have access to that sort of thing so again these sort of rabbit holes that we go down right always think about that there's always new Innovations and new ways that we can help solve some of these problems had another case where uh it was on Craigslist this one uh the guy like uh he was selling the camera he was going to move um and this guy came out there showed him the cash goes out to the garage pulls out the camera the guy knocks him to the ground punches him takes off in his car uh we we ended up tracing this up to uh this one guy he was this DJ
what's interesting is I started leveraging oscent and I started to find all these other images and it was he changed his cameras every month and he advertises himself as a professional photographer but it's interesting though is too is he likes to take photos of himself um going over the like over 100 miles an hour smoking weed on the freeway we had GPS coordinates time stamps everything provided that to law enforcement in this case law enforcement didn't do anything I tried everything I could I gave him all the evidence that we had at the time and uh yeah they they never got that one back um I was approached by Ice uh there's a group that they do a child exploitation
investigations unit these people are really cool some of the stuff that they're doing where they're actually looking at images like that are in a hotel they're looking at the the curtain patterns they're looking at the the bed spread patterns and things like that and they're able to identify what hotel that is if it's a Best Western they can even tell you the location and things like that and they started doing that and they they asked for Access and so I gave them an API so the idea here is that maybe Joe pervert is um uh he's taking bad images and he's sharing them with these sort of private networks and then we he goes to Disneyland with his family
and takes photos using the same camera if we're able to trace that that serial camera matches that they might be able to hopefully stop a crime they couldn't tell me if it was actually utilized or if it actually solved a crime but I like to hope that it maybe did so I mean kind of with all this stuff is like I started thinking about all the risks with this as well you think about all the different pieces of data that are out there um this was you know uh you know it started like 15 years ago uh started doing this stuff um and this has only gotten worse um the more we have tons of information that's
out there about us um it's gotten to the point now where I don't even consider doxing hacking because all you need to get information about a person is a credit card that's all it takes right now to get anything you want about any person a little bit of hunting and you know used to be things that we would do and oh that's illegal things like that nowadays all of our information is basically public whether we like it or not whether it's available through data Brokers whether it's available in underground markets it's something that we need to to deal with um and uh when it's kind of funny I presented uh some of this stuff at
Defcon and we were actually approached by uh some folks um in La they were working on a show for a crime watch Daily um and we uh I was able to work with uh one of our um uh researchers Craig at tripwire a lot smarter than me when it comes to um exploiting vulnerabilities and things but we were asked if we can hack a smart home um and so I'll give you guys just a quick video of the results Vicki Johnson's new beachfront house is not only spectacular it's smart she can control most everything from her phone or tablet it's pretty smart the drapes go up and down automatically we can close doors we can flush toilets
we can turn lights on and off we can turn the air conditioning on and off TVs music it's a brilliant house we were told it was hack proof we'll see about that they think they're coming to take a tour of a smart house but what we're really doing is hacking her house during the party and potentially the devices of every guest who walks through the front door helping me are two cyber Security Experts Craig young and Ken Weston so first we need to break into the Wi-Fi Vicki has 28 devices connected to the home's wireless internet once they were into the wi-fi system our hackers were quickly able to commandeer the home's cameras these are the security cameras
to the house that you've hacked into exactly here we actually can see this is actually our car out here this is the front door if you don't secure them properly then they become insecurity cameras first we turn off the lights [Music] then with control of the security cameras we divert the video signal and play it on the TV in the living room with everyone's attention on the TV the hackers talk to the guests we have taken control of this house the lights the security cameras now a special message from me in the car is piped in I'm Anna Garcia from Prime watch Daily and this house has just been hacked it was free or cheap for the people that are
actually implementing the the installation Vicky Johnson's new beachfront house is not only spect
yeah so that was a lot of fun uh what's interesting too is that uh Craig young who actually was there with me he's now at Tesla which is kind of cool um and uh when uh to crack the Wi-Fi password we use a cloud cracking service which um we had to pay like some money to do that but we actually found it was a number we did a search for the number and was actually the guy's cell phone number that was on his website um and a lot of people actually use their Wi-Fi network like his parents were there they connected to it that's why we could have compromised more when we were in there I actually also had
access to like a lot of their computer file shares that were wide open we did have access to the um the toilet that was fun um like it was it's a if there was a cleaning mechanism so you can actually make it so that it keeps flushing um it was it was good times um but uh so kind of when I think about all this stuff when I think about some of the dangers right we think about okay well there's information that can be compromised about us like even in our own home like I think about all of the the data if I get into someone's Wi-Fi network I could I could gather a lot of
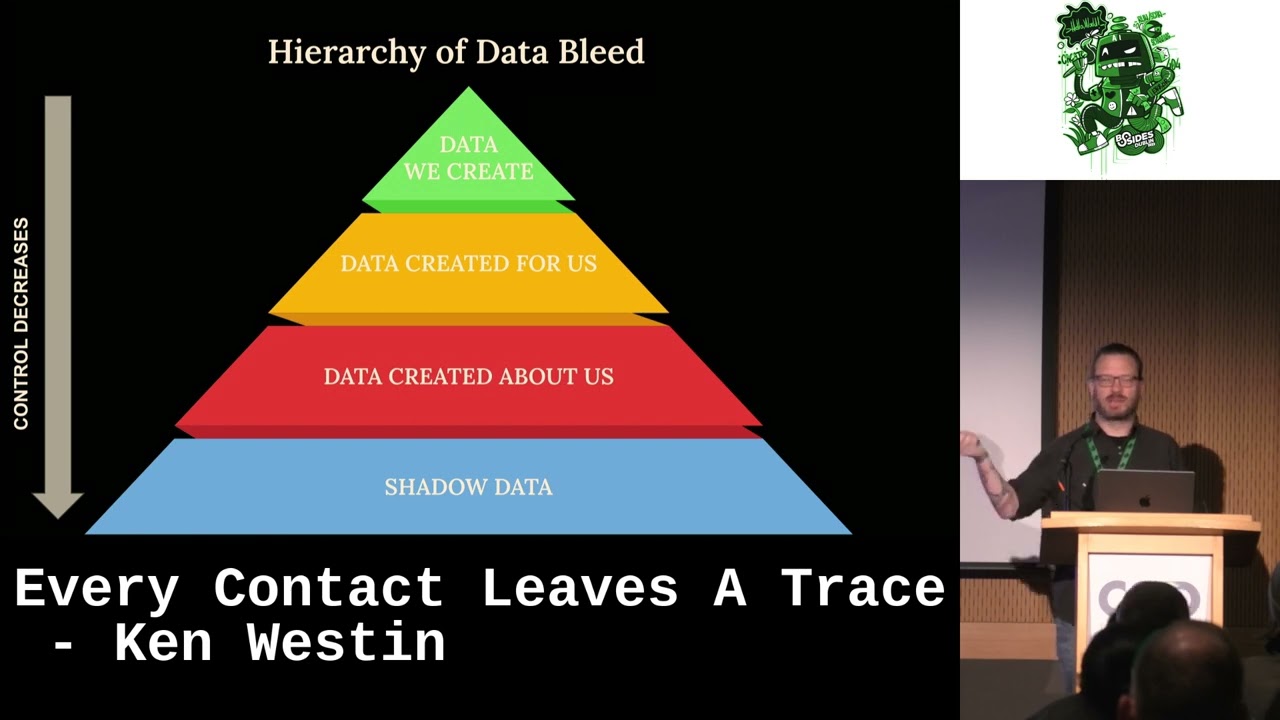
data there I can get a lot of information about them online um and so I started to think about this you know you might be familiar with Maslow's hierarchy of needs I sort of develop this is the hierarchy of data bleed um and so the idea here is at the top there's data that we create and and that's data that we have very we feel we have control over when I create an Office document I create a file on my computer I have control of that I can delete it I can back it up I can do whatever I want um but then what happens when we start moving things to the cloud we start
leveraging social media things like that there is data that gets created for us and that could be from you know uh you know when we upload things to the cloud is presented to us it can be when we make uh buy an airplane ticket when and we when we do all these sorts of things there's a lot of data that gets generated for us and we have a lot less control over that a lot of times that data is now in and whatever the policies are of that particular website or or that social service right where we're sort of tied to that we can request that data be deleted but we don't know if it's been archived we don't know how
many copies they were we don't know if they've sold that data and then further down there's data that's actually created about us and a lot of times we don't even know this is happening a lot of information when we talk about data Brokers they're Gathering all this different data they're leveraging machine learning that you can build a very rich profile of an individual and sometimes that data you know it can also be compromised and that's when we get into Shadow data and that's data that's sort of uh starting to get into the bounds of we consider it legal right if I can get all this information about an individual maybe their credit card number their social security number and
this is where you have underground markets where you can actually Harvest this information the more data breaches that we have I remember used to be when back in day when we had a data breach it was a big deal you know you get those letters that oh your your credit card was compromised or your social security number we're really sorry here's uh here's a free year of identity theft protection I think at this point we all have like a thousand years of free identity theft protection and we've become numb to it um so again uh so that's where I kind of talk about that's like the shadow day that's we have no control over that data
at all if there's no way that we can actually release it so I'm actually looking forward to Jacob's talk I think it's after me he's gonna be talking about things that you can do to protect your data so that should be pretty exciting um I could I could use it for sure um and sort of on that thing like I actually identified a vulnerability uh helped identify a vulnerability that was um out there there was a a server um that was um being it was like indexing emails from uh onto Google and uh started with like what was one person we looked at it and the starter actually wrote a script and that was I had access to over 2200
emails there was no authentication at all not only could I read all these emails but I could actually I could send emails I could reset Services I could get a password resets if I wanted to this is really a a pretty serious issue it was actually a telemax they'd acquired Prodigy and so that's where there was some sort of configuration issue when we approached them we we did this ethically first I contacted Google to get all the data removed we contacted them to let them know about the issue and then we worked with the reporter and we were talking about this in El economista and then they were saying this was industrial sabotage and blah blah blah
and it's like no you guys just misconfigured a server come on um and so but you know this is a situation where a vendor makes one simple mistake and then your entire you know Digital Life can be compromised right so um again this is kind of what we're dealing with and today um so uh Shameless plug I actually did some other research where um like when I was at a tripwire I was investigating a lot of the stolen credit cards and the karting markets and um and dark Nets and things like that the dark web and uh looking at how um uh the the markets work and I started running these forums where I actually found they were
uh hackers that were looking for Insider information so information around like earnings reports or something like that that can be traded and I was like that's really interesting because um with the cryptocurrencies that were happening I started seeing a lot more like white collar criminals that were in these forums that were looking for hackers and I and I was like if you have white collar criminals and hackers and they get together like you can just send the cryptocurrencies they don't have to know each other like they can make a ton of money and I started investigating some of the actual cases and I found one that was really interesting there was a a case where uh a group of people
um they they uh were accessing this uh server the pr servers they were getting news reports I found a bunch of cases and so I did some presentations around this and down the rabbit hole I was like I started doing this and then I found there was one where they made 30 million dollars right there was a group of people they made 30 million dollars off these illicit trades uh one's like one of the bunch of them ended up going to jail the hackers were in in Russia or Eastern Europe um they're still pretty much on the run and then just recently there was another case there was four Russians that were found guilty one of them was a former
Gru operative they made over 84 million dollars in illicit traits so if you want to learn more about this there's going to be a malicious Life podcast about this on the 17th it's going to come out so I really like those podcasts the way they're narrated so I think they'll tell a better story than I can so uh hopefully you guys can see that um and with that that that's for the end of my presentation but I think one thing I just want to kind of leave you with on this is you know think about people always ask me like how do I get started in cyber security and I like sometimes I look back and I'm like I didn't know how
I got started it's like how do I get in cyber security and I'm like I don't know I'm trying to get out um but I think the important thing is here is like you sort of Follow Your Passion like especially right now there's so many different areas of security that you can get involved in like Cloud security you can get into dfir there's all these different aspects and there's no way at this point I think that you can cover everything I I would recommend getting a general overview of kind of what you like uh like of security and kind of dig deeper into something but really Follow Your Passion if you're not passionate about something
if you're not passionate about what you're doing in infosec you're not going to do uh you're not going to go very far I don't think if you hate what you're doing you go to work every day and you just oh gosh this sucks right if you're not able to be excited and have passion about what you do and have have a pride in the work that you're doing it's going to be really difficult um you know I've been lucky very lucky just kind of find my path um and and what I've been doing and I really love what I do I love the people that I work with in particular I think infosec folks are some of the the most
creative and smart people you'll probably see in any other industry might be a little biased because all my friends are here um but uh but with that um uh should I open up for questions um I'll ask questions here but um if you're shy or anything like that I'm going to be around here all day so feel free to come up to me um I don't buy usually um so if you have questions or if there's anything I can do to help you let me know and we'll open up for questions or do we have time or okay great or answers if you guys have any answers too
yeah Smokehouse is she getting the refund I'm sorry what was the question oh oh no uh we uh we ended up before we left there we secured all our stuff we changed all the passwords and all that so yeah the the thing was everything was set to the default passwords so we had a Wi-Fi pen apple and we were getting information about the devices and we just go and looked up the default passwords like uh one of them was like one two three four five six to get into the security cameras so yeah but I don't she didn't get a refund unfortunately she did say that she should have got a big dog okay yeah
oh yeah I'm sorry great any other questions oh yeah
uh I asked me if I have a list of the people I've had prosecuted I I did uh I I have it a whole list of them but yeah uh there's this is just a few of the cases these are the more interesting ones a lot of the cases I worked on are really boring like you know just really simple in some of the cases I I don't necessarily know who the criminal was I just provided the evidence I didn't have to go to court you know I'm not a law enforcement myself I just told law enforcement what they should be doing great any other questions well awesome thank you so much for having me I really appreciate it
[Applause]