Command-Line Obfuscation: You Can Run, _and_ You Can Hide

Show transcript [en]
[Music] all right Brian let's make a start starting a bit late so apologies for that but we got it to work exciting times um welcome everyone tell thank you for taking out the time to come to this talk um you may be familiar with the term you can run but you can't hide but today when we look at command line ofation we will challenge that notion by looking at how you can run and hide so um the boring bit first my name is vit that is a Dutch name I'm originally from Amsterdam but I live in London now where I work in trat detection and response uh in that role um I see a lot of command
lisc and I thought i' would share some of these insights with you so hopefully for people on the defensive side like myself get a lot of inspiration to look at your own detection rules and how you look at um detecting the Badness um for those on the offensive side hopefully some inspiration as to how you can uh make my life and uh other Defender lives a lot harder um yes I'm involved in a number of uh open source Community projects one of them is the LA bass projects which will also feature later so um yeah hopefully um that also gives some inspiration and uh yeah I'm very um honored to be able to add this
conference to my list of uh places I've spoken at so thank you very much for for having me all right so let's just Dive Right In um as I said we started a couple minutes late and I don't want to keep you from lunch so um let's dig into the good stuff so um command lines let's start very basic what are command lines because I know some of you are very technical some of you might be completely new to the field so um when you start a process on your computer there is always a command line Associated basically it's a bunch of parameters that tell the program what you want to do from the very start
whether it's a guey application or a terminal application uh it's very useful information for the program because it can change the flow based on what you tell it to do um so a couple of examples here for a Windows perspective if you just call notepad.exe there's not any arguments but that is still a command line there one argument is the program but um it's still a command line the next one slightly more useful perhaps also tells you what file you want to open you can also use the [ __ ] of course it opened a file but if you want to do it right away um disand line will help you do that if you're familiar with u Windows
you will know that you they love their forward slashes for command line options or Flags so here you see shutdown exe SLR that means reboot so um not only do you tell to start the program and to do something but you give it a specific instruction as you see with the final one um it's it's all convention based it just depends on how the program implements that command line uh argument so um this is reg.exe for registry operations export it's sort of an instruction and then we see a registry location and a file location so um why does this matter well for threat detection right um command line arguments tell you a lot even those examples I've just shown you
right we we walked through them like by just reading them you don't even need to see what the program did because the command line arguments tell you what the intention was that first one opens just not bad but with that second one you know the intention was to open hello txt so if you're a Defender you will know like detections build off command line arguments are super useful um because they tell you a lot they tell a story now you can also imagine that if you are a Defender and you trying to uh get away with your evil activity you you're trying to masquerade what you're doing you try to hide what you're doing because you don't want to stand out you
want to be detected you want to stay under the radar so when I talk about command line off fisc which is the topic of this talk it is the trying to hide or masquerade what you're doing but still executing the thing you want execute so that sounds a bit high level still but we I have plenty of examples um across Windows Mac and Linux today so hopefully it will come to life a bit more now again why does this matter you want to stay under the radar but why well many EDR tools AV Tools and obviously if you do threat hunting um you will often very often rely on these command line arguments to find the thing
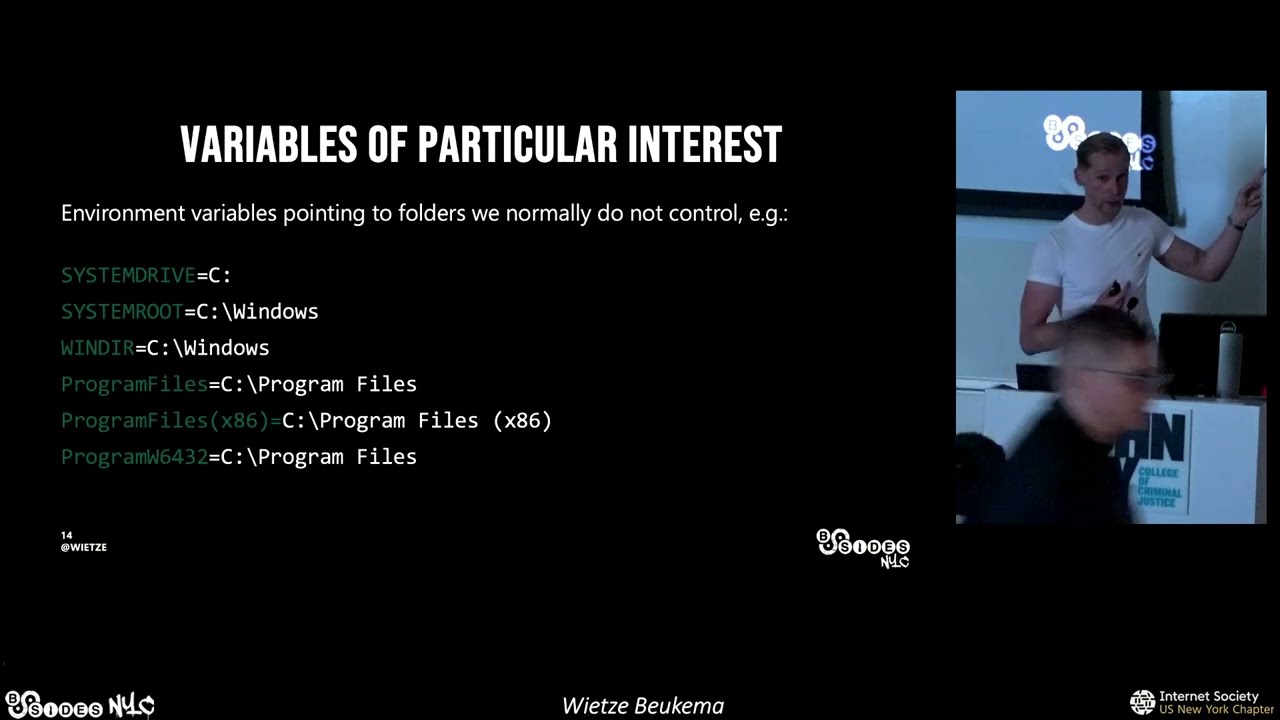
you're after the bad behavior and you look for a process and a certain keyword or sequence of keywords that's how you define um an activity of Interest very often um so um as an attacker finding an a way to achieve the same thing I don't know dumping uh a process's memory or disabling some security feature in a way that doesn't use the normal keywords is therefore super useful right so that's why command line confiscation matters enough high level talk um Talk is structured as follows we start with Windows um because most of will defend some windows machines hopefully um so we'll talk at start a bit about what command lines typically look like I will
have four practical examples of processes that are on every Windows machine that you might use as an admin but that attack is also like to use as a living of the land sort of situation and I will show you a number of ways in which with minor tweaks you can bypass detections and I Will Show You by um looking at actual security tools as well as open source detections to sort of prove that the minor changes we make actually do byp pass so we start with Windows um some Linux then and then at the very end hopefully we have time uh a simple mac example but just to show you that it's not specific to one
technology cool so some of this we already discussed but on Windows command lines what do they typically look like well um for slashes already mentioned it um typically you see them in this structure ping sln1 CMD SLC um that sort of thing so lots of forward slashers but sometimes programs system native programs also accept the single Hy or Dash if you use Windows you will also know that a lot of this stuff is case insensitive so file paths for example doesn't matter if you do it upper case lower case doesn't matter and um programs often do that too so these commands here for IP config um they all result in the same thing doesn't matter
like the program doesn't care third double quotes used a lot I will have a number of examples later but what I mean by that is that if you have a space on the command line for example U it's very often that you quote the entire argument uh with double quotes you wrap it in double quotes that means that the program understands that you include spaces um more than Linux and Mac OS for some weird reason Windows loves the double quotes because you can put them in various places how you can abuse that we will see shortly and then the final going is really important um all these things here are observations and conventions none of these are rules there's nothing
in Windows that forces you to write a program that is case insensitive or that only accepts forward slashes just convention um lots of built-in programs do it therefore lots of software Developers for Windows do it but um if you want it to be case sensitive you can if you want to use a hyphen you can the point therefore is that between these system dat programs there's no hard line as to like this is how it works depends on who wrote it depends on when it was written and that means um scope reviews so as promised for Windows we will be looking at four um built-in tools often used um Powershell first we're going to be looking at Option
characters AMAC and C script for um Unicode stuff and double CES and then the last one which is more of an interactive one um we'll be looking at a d that you with r dealer often used for credential dumping and I will show you like how there is like a gazillion ways in which you can bypass defender or the basic Defender for um doing that so let's start simple power shell hope you're familiar if you've ever used Windows you will know of this one it's great for automating task if you're on the it side if you're an attacker it's great for automating your um batters so very simple example of how you might run a po shell command it's like this
Powershell for/ command then right post J which say that right oh almost almost okay classic for now um so if you run that and all it does is sort of echoing it so you would get um the same output back on your shell so this is what that might look like um now so far pretty straightforward right um now as the bullet point suggests there are multiple option characters that you can use so we already talked about forward slash sometimes you can also do a hyphen um but you don't see what it looks like here right it looks like forward slash and then the same command again with four times hyen what you might not see is that
these are actually four different hyphens if you were to look at this in your EDR tool or even in task manager might look like something like this this is a process monitor procmon from the CIS internal Suite very useful tool basically shows you what your EDR would see um so if closely might be a bit small for people at the back but you see the bo slash you see a regular hyphen what do we see then we see a slightly wider or longer hyphen and we see a massive hyphen and then I know some sort of hyphen at the at the top um so this is what edrc but if as we've seen from the actual terminal all these commands
work like they all do the job so what what's going on here many programs not all of them but Power shell is one of them excepts many of these different option characters um we call them Unicode equivalent because they all mean the these last four they all mean regular hyphens but Powershell is being helpful by um accepting also these weird hyphens and as you've seen I've added the um Unicode um um decimal representation or heximal heximal representation there um these are actually different U dashes so to you and me they all look the same you might not even even from the screen right you might not even be able to properly distinguish them but um your EDR tool
definitely sees a difference so why does this matter again because it's it's only one character like what's the big grop um I'll be looking at different detection engines open source detections I don't mean to pick on any of these because they're actually great resources if you work with the fender for endpoint this is a great resource but just as an example to show that even great resources have flaws um this is a detection that looks for encoded commands which is very similar to the example I showed you um but in doing so it looks for hyphen encoded command or hyphen ENC um if we now look at that very simple demo I gave earlier um if you use
any of the four other Alternatives even just that forward slash right but um if you you see special dashes this rule would not fire so you can have amazing detection logic in there it's like literally changing one character that a human could not even distinguish you might for detection like this so I hope this gives you an idea of what command line appication is about it doesn't have to be very complicated it can be very simple cool um related example next one msac um the Microsoft installer executable um can be used for installing packages again system admins do this a lot to put software on your machine um attackers also like to use this because
m exac is built in and if you want to use well you can install mware with it I guess but um what they often do is install legitimate tools TOS say any desk you know a remoting tool um using this utility and then configure that so they can use that legitimate tool for that purposes so we've already talked about the option characters so I'm not going to bother with the um forward slash what about other characters right we saw that hyen had multiple command line equivalents um can we do that with other characters as well perhaps so um look at the screenshot we see um the same thing up put there m as exac for package and
then any desk in this case but as you can tell the A's are not normal A's are these weird superscript A's uh and within the Unicode range that is actually a separate character it's not some sort of weird formatting it's it's a character M exec is one of the executables that is again being helpful um by saying well you gave me a superscript a but you of course menant the normal a so I'm going to press ahead anyway and just pretend you said a so um weirdly enough if you run this command it it does the thing you would expected to do uh it would install any desk um yeah you can already see there
on pron again um even on your terminal you might think oh it's just weirdly represented on my terminal your EDR would see the tiny Ace so again if you have a rule looking for the word package it's not going to find this so um very similar technique to the previous one but again consequences could be pric now we're going to look at what I think is the most problematic one because this is the most unversal one that the Unicode trick that really depends program to program this one is I want to say 95% of the built-in programs has some sort of issue with this at the Double ques so cscript is um a building tool
for Windows script host scripts it's a whole mouthful but it's basically running FB scripts and J scripts um historically very useful for automating tasks nowadays we have po shell Microsoft really doesn't want you to use these anymore um but attack is obvious still do the great thing is that it's not properly logged so attackers still love using cscript uh which is to uh console or terminal version of of executing D scripts what an attacker might execute is something like this so you see cscript for/ no logo that's just to get rid of the banner um then for/ e for engine colon PB script which tells you following script even though it doesn't end with VB is a VB script and then uh
the path through some file file I'm using only echo's hello world nothing fancy um but have a look at this so the top one is just filla right that's how most of you would execute the script um if you want to um if you want to part of the argument you can wrap them in double quotes So that second one doesn't look even too crazy but it's a e colon and then VB script wrapped in double qus but as you can tell that still works if you look at the the can the following examples again I I probably don't need to explain what's going on here by just adding an arbitrary number of double quotes they have to be a
multiple of two but if you just keep adding double quotes um C script is being nice to you and just sort of filters them out it tries to interpret them double checks if there's no spaces and stuff and then just presses ahead now you might think um this is what it looks like in your terminal it's just a c cmd.exe thing but no these double quotes is again what your Ed would see and that is problematic so yeah here again you see it this is not just in your terminal this is literally what your um defending tool will see so again what what's the big group here now most U command line based detections look for keywords um this is
one taken from the sigma project I hope you know that um if you're not familiar with it honestly write this one down great resource with open source detections it's different it's a tool agnostic so whatever you use it's great for inspiration and sometimes you can even directly translate it to a um attender rule um but yeah they have lots of content in there again is great it's open source but um look at this this is one of their detections they look for at the very top look for image ends with C script that's what we're doing if you then look at the very end it looks for/ e colon PB script so if we Now link that back to
what we were just discussing um the top one the vanilla execution it would detect but any of the other versions where we just add double quotes in random places it would not find so just adding quotes arbitrary places um whether it's just two or whether it's 24 and that will bypass a detection like this so um yeah as I said I'm I'm most worried about this one because it's it's only present in lots of Windows tools and it doesn't really stand out as an analyst either right if you see someone using double quotes in the command line you just shrug um but it could really break some of your detections so um please bew this
one cool now a bit of a longer one which is not really related to um this sort of command line stuff per say but it's again an example and I hope for both sides it helps you think how to analyze um detections or how to analy bypassing detections um I mentioned before I'm involved in the law bass project if you've not heard of that again please write it down or or there QR code texture there as well it's a great open source project with all sorts of living off the land binaries scripts so it's a collection of system native um tools utilities that you can abuse for bad one of the currently 200 entries is this one
here comp svcsd it is a dll that is on Windows since I believe like Windows me or something like that like it's it's everywhere and it can be used for debugging and one of the debugging options it has is dumping a processor's memory attackers love that and specifically of the Elsas project process is the security process in Windows uh typically is lots of sensitive data like hashes tokens sometimes even clear text credentials um so attackers if they have the right level of access they might leverage this dlll because it's it's on your computer anyway in order to dump the contents of that process and then take that file offline and perhaps crack it or reuse a
token that sort of thing so if you look on the law bass website this is an example of how you I execute it um it suggests using run dll 32 just a native tool for executing DLS um then the path to comcs then the entry point mini dump which is um in in that dll the the the function that's responsible for making the memory dump then you need the process ID which is in our case alas so it's going to be a number then a path where you want to keep the memory dump and then the word full to say I want a full memory dump so um now what I'm going to do it moves moves
on okay not so fast my little okay go back please there we go all right so I'm just going to walk you through it what we're going to do first is we're going to execute it as suggested by the law bass project which is what most people do including myself just to see how it works um I have a vanilla Windows 11 with a vanilla Windows Defender AV um which is designed to stop some of these attacks and we're going to see how well it does and what you and I can do when you encounter that to see what could I do to bypass that so um yeah as said we need the LSS process IDE so
that's what I run very first so we see 68 Z that's a number I will repeatedly use um to execute this particular Command right so I copied it from the El sorry from the L bass project I I um the path a bit shorter but we we see the same pattern run com svcs and the word mini dump 680 is our process ID of interest um because I'm going to be trying different versions I start with variant one and then world four so if I execute this so just um go um just playing from the lawas website it tells me I W let you do that day um access isem mind um Windows AV Windows Defender AV says like I I
recognize pattern um we're not going to do that what you would hope from a pro from a well mature vendor like Microsoft defending their own product no less is that they obviously not only look at command lines but also at the underlying behaviors um but maybe they don't so what I'm going to propose here is we're going to try a few things and see if we can work around this um this um just prevention going to do the whole time that again s all right press play and it's going work this I think cool um now if you used rund l32 before you may know that instead of calling mini dump with a space you can
also do with a comma it's just basically a different way of telling um to address that function inside the DL um so I tried a comma thought maybe maybe luck there but no luck um Defender is clever enough to see the same thing uh not going to let you do that so um let's try something else so we had 680 right which is the elss process ID maybe Defender is doing something clever with that because it knows that's a sensitive process so something very simple I tried is padding it with a zero um or sometimes you can also add a plus sign you know because the number is either positive or negative plus sign is us usually
redundant but um sometimes it helps you bypass detections so as you can see here no complaints no red letters we see on the left hand side we now have two files variant 2 a and 2 B because that's the names I gave these attempts so um that didn't take much right like two extra characters and um basic defenses like Defender a uh are no longer uh uh doing their thing let's make it more interesting see if we can do different things um if you've heard of ordinals is basically a numeric representation of a dl's function so you know how we use the word mini dump before so that is the that's the keyword that's the function name but
very often there is like a numeric version um so in this case you need to look that up um it's 24 there's tools to do that um so I thought maybe if I run them with ash24 that's the way you run de knows you mean the numeric version uh sometimes you can make that work as well so now without changing that 680 uh process ID and we did actually manage to get more memory dumps there because you see there's three more there so I tried # 24 # 0024 and # plus 24 so similar techniques to the previous one but now apply to this ordinal and again Defender did not um did not mind which is
good what I then tried because we're using a space here again right I thought does the same thing work if we use a comma again but weirdly enough it does not allow you to do that so if I execute the exact same things we did before but instead of a space use a comma suddenly that is an issue so what I think is going on here is that Microsoft maybe saw this technique on a Blog and they were like oh yeah if we see comma hasht 24 definitely bad news so we're going to block that but didn't think about the fact that you can also use a space instead of a comma so um partial
detention detection there but um obviously did not stop us what I then tried which I wasn't expecting to work but um we tried 0024 right um I thought what happens if I just keep adding more zeros is that maybe going to break here or maybe I don't know um what do you think is going to happen it should break right but um certainly not it did work weirdly I don't know adding more zeros broke this detection so I don't know exactly what their rex or what their logic is but um even with a comma # 24 works if you just keep adding enough zeros so weirdness cool now um let's try something else clear our screen first um
another way another way to look at this is to look at the um space my thing right because we see clearly the detections do something there with the comma mattering and sometimes the space does matter more um you can also do without any space of commas so using double quotes for the dll path so KCs followed immediately by entry point or in this case hash 24 um BR l32 is clever enough to understand that that is two separate components even though there is no space in between uh and it means again that we can bypass the detection so now we have R in five another memory done now the last um two or three ones
integer overflow so this is another interesting way to look at it um we've had this asht 24 right and we figured out if you add enough zeros it breaks somehow so I thought again def Fender is probably looking for hasht 24 somehow they have ax to do something clever is there a way where we can represent the number 24 differently it turns out you can because um as you may know integers are represented in different ways in programs um the ordinal is a 16bit integer so if you make the number big enough it sort of it doesn't fit in that 16bit allocated space and what normally happens it just wraps around so what I did here is I added the maximum number
that fits in 16bit space to 24 the number successfully wraps around and as you see here um that actually generated another file Varian six so um we still using the same entry point # 24 but um by making it big enough we fooled Defender and then I think the next one is it's kind of the same thing it doesn't really change to think but um you can do the same with the process ID we know Defender cared about the process ID so we can do the same trick with the process ID um however that is a different type of integer so that's a dword or unsigned long so the number that fits in a process ID space is a lot
bigger so um we can still see that um you need to add like what is it like 4.2 billion to um 680 but again if you add that memory D still gets created and again you might full defended there so um these are all the ones we tried you see a couple failed and also like some of them are very similar so it's also not like you know it's not not like how many is it five nine so there's nine ways of bypassing it some of them are slight variations of the other but I hope you can see here right that if you do the standard thing you look at the thing on the blog or on the security
report the cve that you read that um does the thing as a Defender you might think oh I got a cover now all done but by making minor tweaks you can really bypass that so what I hope that we've seen here is that very often there are many many ways in which you can represent the same command so different do computer it looks like a different command but the output is the exact same um what we've also seen is that including mature tools like defender or Defender AV um detections are not often resilient sometimes they are but if Microsoft can't get something like this right and again we're talking about a memory dump you would hope they
they try um like what does that mean for us right how can you be expected with your much smaller budget to also defend against this so um I hope that also brings home and then the final one looking beyond the surface Pace off so I think both Defenders and attackers I hope what we see here is that look beyond that you know uh command line you copy from stack Overflow or your um even law B project think about what else could you do to make to bypass the detection and make sure you are resilient that was Linux sorry that was Windows now some Linux time um we again let's start talking about conventions so if you know Linux you know it is
different from Windows and no forward slashes there for command line arguments they'll be Bonkers because those are represented as file paths right forward slashes so no on Linux almost exclusively things are hyen based um very often you see that the long version with the highy high hyphone and then a very descriptive a Bose name and sometimes you see the more compact single hyphone and then the single letter typically um what is really annoying and I don't think I have time to talk about that today is that um again to help users sometimes you can sort of compress multiple Single Character uh options in one so if you have hyen a hyen b hyen c very often you can also just say single
hyphen ABC and the program knows that you mean three different commands from a detection point of view as you can imagine that is a bit of a nightmare because imagine you're only interested in hyphen B because that's a bad switch um well good luck writing a Rex for that right you're going to have tons of false positives so um not fun great for users terrible for Menders then the fourth Point again I won't go into too much detail today but what is very notable difference between Windows and Linux is that on Windows command lines are proper strings um whereas in Linux um they are arrays so you pass them as uh collection of multiple inputs um you might think
that's in the end not a massive difference because especially when your EDR is going to end up as a string anyway but um it it does make a difference so it is slightly better designed in that way but um as I said it doesn't mean it's it's necessarily better because the final Point as we've seen before the implementing program decides Linux is also often case sensitive but it's not a rule if you write a program for Linux there's no one will forces you to do that if you want to make a case in sensitive you can if you want to use a forward slash for a command line tool you can so ultimately again it's down to the person who wrote
the program and I'm going to show that by looking at three examples base 64 and xxd which are both um string encoding and decoding tools then we're going to look at NCAP for IP address Madness so let's start simple again um basic C4 uh is a tool that you may have used for encoding and decoding content very simple on um my version of yuntu 2204 this is what it could look like you give it a blob Echo something and then you pipe it into Bas 64 D- decode one way of doing it if you've looked at the screenshot which you probably have you can see there that I have tried six different commands plus the
shortterm or the short um line version um it turns out that the word decode doesn't have to spell decode it can spell decode Deco deck de even hyen hyen D Works despite there being a short version which is just hyen D so once again we see here that we found seven different ways in which we can express the exact same command um and you might think well okay leaving letters out before you were talking about adding letters now you're making a big deal about leaving letters out like what what are you on about again um if you use spun great resource resarch spun.com spun team does a great job there but is again an example where they are looking
for suspicious Bas 64 decoding and what they're looking for is BAS 64 Space HD or B 64 space I hi decode I hope you agree if you look closely at the logic and my screenshot that it would successfully find the first one and it would successfully find the last one but it wouldn't find any of the other ones so again leaving out a character sometimes can actually bypass a detection so so small changes big results and you might think oh that's just B 64 and who really does use these weird long-term um long long versions well again we've seen here by using the long version and then leaving out a character can bypass the detection these
tools here are confirmed to also have that logic and also use or accept these sort of abbreviated um long form arguments um W get Curl touch Ln LS um if you use Linux you probably have used one of these commands today and if you are an attacker you will definitely use one of these commands so uh it does matter right so again whitee problem uh and not necessarily A straightforward solution unless you're aware of the problem let's move on um xxd there another encoding utility so base 64 was for base 64 encoded content xxd is one for hex content so um we typically do is you pass it a string with hex content content so um all these characters go up
to the letter F and then in this case it um decodes to hey bid doublin now in order to decode with xxd you need two options hyen P and hyen R now we touched on this at the very first slide of this section what what should happen if you run xxd P AB C- rxyz you might think um well it might error because hyphen a doesn't exist in this content or maybe it's um I'm to give you a warning or maybe it's going to execute it's going to look for an option that's called pabc um sadly it does not do that have a close look at what it says here why is going on here what turns out um is that it only
looks at the first character and then it blatantly ignores whatever you put after that word in the same sentence so um this command xxd hyen pup should serve R breast whiskey is a valid command um and it's not because that's some sort of magic word but it's because it starts with a p and it starts with an R so I think this is the worst kind of um command line passing weirdness um is where it just ignores whatever is after that because what does that mean it basically means that there is well virtually an infinite number of acceptable command line options that translate to the exact same output so how are you going to defend against that
right again you need to be aware that this is a thing so a very to be very few tools that have this floor but a tool like xxd that that can lead to Mis detections and what is even worse is the thing on screen here I think you can make decoy commands that um not only fool a machine they can fool you because if you have an EDR detection and you see this on your screen right says xxd hi print equals some path and then read only is true right you you might be like oh I've never seen that before but it looks like it's trying to you know print something to the terminal and it's only doing better read only but
this these are not valid options it's again this is just hen p and hen up I fool you into thinking it's doing something else because it looks very I don't know liny so um again this can be a problem because if you're not aware you might full your analyst as well into thinking that the command isn't that harmless or is doing something completely different whereas in practice what it's doing is in this case decoding a command cool um I'm going to make some more progress so I addresses we have netcat here which is a mostly a built-in tool not on every distribution but it's great for testing Network options so a typical execution might look like this
NC followed by the options V and Zed V4 for both Z for I know I don't know what is that came from but it's like reports the connection status and in this case I'm asking if the IP address 8888 has P 53 Open DNS so this case if you run it you see that on your screenshot it tells me uh yes I could reach 888 on 53 and that is DNS what I want to talk about now in the last few minutes is IP addresses because um what is an IP address we know we know what it is like what why is it always in this dot notation what what is that what is that all
about if you studied computer science or some sort of networking course you might know that an IP address is basically a representation of a number every IP address is just a or I4 anyway in particular it's just a number it's just it's a clever representation to make it less aone or easier to remember I don't know um the fun fact is is that lots of old Linux tools still accept um order versions or sometimes even combinations of order versions in an attempt to be backwards compatible or to show off that oh we know it's an integer so um look at the screen here I hope it's not too small the very top is what you would
normally see um so we're going to reach out to 1271 that works um if you look at the couple lines later you see that it all it all successfully works out if you look at the second one right 1271 does that sound like an IP address not to me but to naat it's like oh yeah I I knew you left out to zeros I'm I'm you know I'm helping you so it actually brags about like oh yeah you told me 1271 but um I know you meant 1271 well the next two ones um hexad desimal we see octal we see decimal um different numeric representations of that IP address so again how many of you
would know that the number 21307 06433 is actually 1271 not that many right so with simple trick like this you might obfuscate um the IP address you're reaching out to or even the fact that you are using an IP if you're a Defender you will probably have some sort of rule that looks for I don't know power shell reaching out to an IP address you have a Rex looking for IP addresses how many of those would would match on the the other ones here on screen now I've been told I've only a few minutes left um I'm going to very quickly show another example from Mac OS um to show again it's not just Linux
it's not just Windows uh very simple one similar to The Run 32 example um Osa script is kind of like the C script equivalent on on Mac Osos allows you to uh execute fun scripts again attackers love that um simple one is um hyphen e and then you you pass the scripts on your command line um if you look at screenshot very carefully you see that I left out space so again you might think what what is that space going to do well again it can break a detection this is from the sigma project again they look for space hyen e space um so having a detection like that um might actually or having a command line like that might
bypass that so I hope that has shown you that it's not specific to one uh operating system from Mac most of those Linux ones apply anyway but um there are our slide variations now final two slides if you're on the offensive side I hope the takeaway is is that command lines are great they're excellent right how amazing was that um there's lots of chaos there and by making small tweaks you can bypass detections what it's not likee I hope to have encouraged you today that by looking beyond the surface right so beyond that blood Poe beyond the the obvious um by just tincturing with it like play with it you might find surprising results with possibly big
consequences my recommendation however will be don't overdo it like if you remember the double quotes one like the one where I added like I don't know 45 double quotes that's going to stand out right but um if you do it subtly um not too many unic code Replacements but maybe just one or two might effectively bypass the detection uh and you still have your goal without ITT standing out as a detection um defense side my side um please don't cry it's not all bad um there are upsides to this I think the key here I want to hammer home is don't rely on detections oh sorry on command lines for detections that doesn't mean don't use them because they're great
like you're going to find lots of stuff but just looking at command lines my point is don't overly rely on them don't think you have covered it because you have a command line detection because we've seen you can bypass them you can tweak them um what I would recommend is look for the underlying behavior that that IP example for example um maybe instead of looking for it in the command line which is a bit silly anyway look for the underlying Network detection because or events because the network events will always have a um a normalized IP address so it doesn't matter what you put on the command line the network event will be true as to
what what where it's going so try and make resilient detections try to find think again about like how you could bypass it make them as broad as possible but don't uh if you can avoid the command line try and write a detection or something else um but yeah resilient detections are key and then I promise you the final slide before we had to Launch um wouldn't it be great if there was some sort of overview with all these weird anecdotal examples of built-in tools on Linux on Windows in one coh here and place um I hope to release a tool later this year that has a platform with all of these on there it's once
again going to be open source so everyone can contribute or um point out uh things that no longer valid so um if you're interested in that please follow me on Twitter or find me on LinkedIn if you're not on Twitter once again thank you very much for your time I hope this was useful