White Collars & Black Hats: Bitcoin, Dark Nets and Insider Trading by Ken Westin

Show transcript [en]
so today I'm gonna be talking about black hats and white collars this is some research that I did really looking through a lot of actual criminal complaint documents it's actually I found that there those documents are actually really great for threat intelligence you can actually start to learn a lot about you know folks that are criminal hackers what they're using for infrastructure and things like that in this particular topic I found really interesting because we always talk about how much money that hackers can make you know doing stolen credit cards things like that but there's actually a lot more money to be made when you're actually looking at doing stock trades and things like that and I'll kind of
walk through you know how they actually conducted some of those particular breaches about me I'm based in Portland Oregon I work for a company called spunk it's kind of my dream job I get access to large sets of data and I get to do all sorts of fun things I teach workshops around threat hunting how to go and actually find adversaries in your environment when you're your automated boundary defenses fail I'm also very interested in insider threat at our user conference I'll actually be talking about how to leverage machine learning for looking at insider threats so if you guys are coming to comp if you're a Splunk customer i'll see you there but prior to my work at Splunk i actually
developed various tools to help track stolen devices and when I did that I actually ended up also unveiling large organized crime rings a stolen laptop for example would basically function as a Trojan into various Russian organized crime groups that were in Portland for example and so I learned a lot about sort of investigative theory and process around that worked really closely with the FBI law enforcement a lot of those investigations so the cool thing is I've actually put people in data all right sorry in jail with data right so that's that's kind of where I've done a lot of presentations around this I actually presented it at Def Con around so that topic as well but I really kind of go
down rabbit holes I look at particular types of attacks and I try to unveil how the attackers actually went about and their crimes so why are this topic I think this is really interesting because it's involves criminal hacking it also involves fraud insider trading insider threat I'm going to go through a lot of these different cases and you'll see all these different components sometimes we think of securities you know your boundary defenses your firewalls and things like that but what I found is particularly when you're conducting investigations a lot of times you have to bring in other different types of data sources you may even need to get data sources from another service provider we'll see that with this some
one of the breaches where a PR firm like at newswire they didn't actually protect their information they didn't have the right logs in place so the FBI when they came in to ask for those logs they didn't have them and that made the investigation quite a bit difficult so a lot of times when you're talking about the data that you need it's not always just for your immediate investigations they might be required for other types of investigations depending on your industry yeah this also involves some things around using darknets and tor there's a lot of international things that happen I actually found a lot of collaboration with hackers that are in the UK in Ukraine and Russia actually
collaborating with white-collar criminals and actually people that are one guy was actually a VP at Morgan Stanley and he was actually leveraging some of the these hackers to actually go out and do some of this dirty work and I'll talk about how those guys met as well and this type of attack is really difficult to detect you'll see in a lot of these cases the reason these guys got caught is because they got greedy they're arrogant or someone just made a stupid mistake and I think when if you actually look at some of these I think there's a lot more of this going on than we would like to admit the SEC is involved in some of this and even the
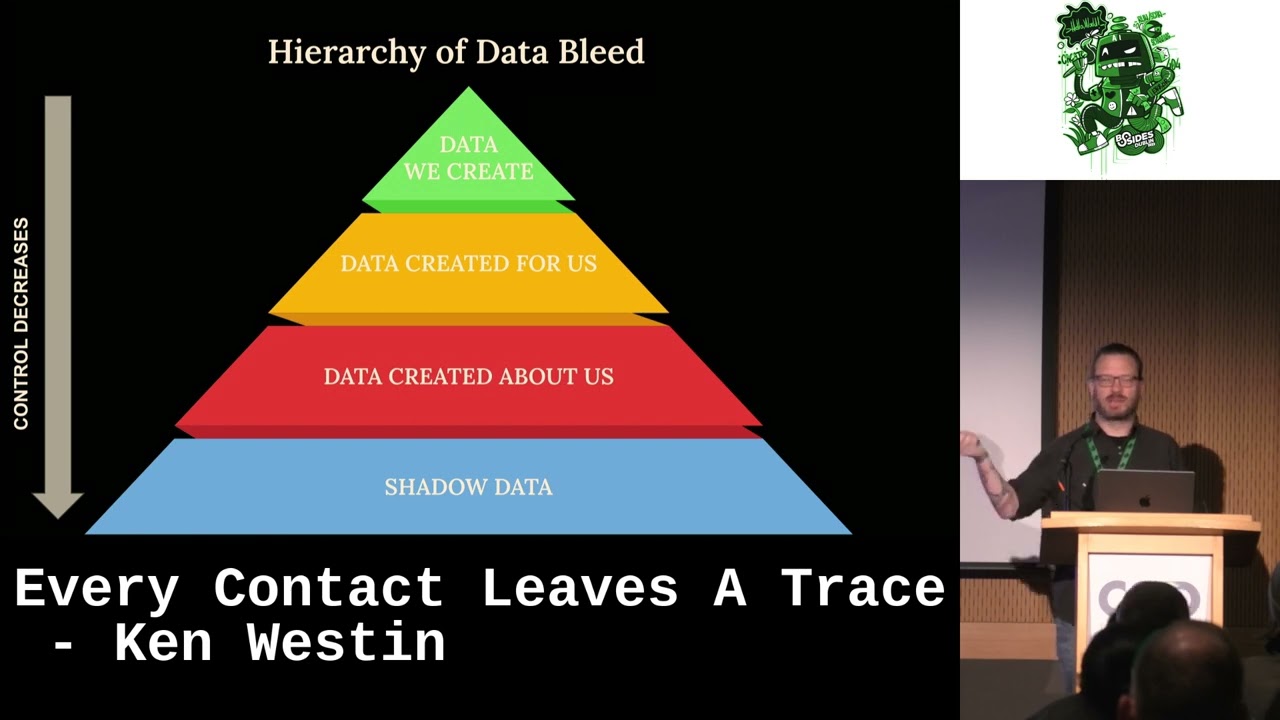
SEC themselves have been hacked and I'll talk about that as well but there's a lot of money fee made and I think there's are a lot of money being made as a result of these types of compromise and I'm still conducting additional research I'm actually in some of dark net forums where I'm actually looking at some of these folks that are actually trading this information I'm hoping to unveil some of that at blackhat next year so we always think about you know who's targeting an organization I always like to you know think of you know the tools toxic and procedures depending on our industry right we we can look at hey if we are intellectual
property that's going to be a target of an organization if we have credit cards if we have customer information that can be sold know that that's all your valuable information for a hacker so when we start to do our threat modeling it should be around that based on our industry but there's other types of information if you're a publicly traded company and you have earnings reports that data can be incredibly valuable to the right people who know how to make money off of it and you'll see that in our example one group actually generated over a hundred million dollars in trades the SEC was able to get recover about 53 million of that so one guy in particular
he's going to jail for 20 years but for about four or five years he lived a pretty good life so it's always good to think about this and your log sources and things like that the data sources that you actually have in your environment and you'll see in a lot of cases you need more than just firewalls and VPN things like that a lot of times very sophisticated malware can be put on system so you're gonna need really high fidelity logs from your endpoint so I found actually a lot of folks in the financial industry are actually becoming really interested in cryptocurrency right especially a Bitcoin and things like that they're actually trading on this themselves and with that what's
happened is a lot of these folks have become a little bit more technical technically savvy they're actually leveraging tor they're going into darknet forums and they're actually meeting hackers right so what's happening is these guys have really good knowledge around finance they know how to do white-collar crime and they're meeting with these hackers who have really nice technical jobs so what happens is you they're paying the hackers to go out and you know hack some of these systems and get access to some of this information and then the they're giving that information to the traders and the traders are ours are just giving them straight-up Bitcoin for that is really difficult to trace or in some
cases they're even setting up trading accounts for those hackers so that they can make money as well and you'll see that in these guys it's one case in particular they got a really really greedy and that's really how they got caught because there was a lot of irregularities that were being detected I really like to show billions so talks a lot about this kind of stuff right how to get some of the information if you guys have ever watched the show I like Paul Giamatti too but they do talk about some of these types of scenarios as well and it's just amazing how much money these folks can actually make so the definition of insider trading so
it's the illegal practice of trading on stock exchange to one's own advantage through having access to confidential confidential information it's a little bit deeper than that too what's interesting is that when we start looking at hackers accessing information it's a little bit different because it actually doesn't it originally wasn't actually classified as insider trading they actually developed a term called outsider trading because a hacker who I exact access to information does not have a fiduciary duty around that information right he's not an officer he doesn't he's not a maybe a family member of someone who might have access to some of that information right they're actually conducting crimes so a lot of times folks will actually get sentenced
for crime but they won't get sentenced insider trading but there was actually a change that was made when one of these cases actually came to light so this is the sec versus a fellow named dora zoko and i'm gonna totally brutal i it's ukraine ukrainian and russian names so I apologize in advance this fellow he was a hacker there was some interesting things that happened he actually was trading with this particular trading company they're called Interactive Brokers he put about 42,000 dollars in there and they made around almost three hundred thousand dollars in one trade he was really not too smart because that he just opened that account and this was his first transaction right and of
course that's gonna throw some red flags his account got suspended while the Interactive Brokers conducted the investigation and contacted the SEC so it's actually happening is that he was doing reconnaissance he was actually targeting one particular company and a lot of times when companies would they have to announce their earnings they would provide this information to Thompson financial they would have slides excuse me this would be maybe a day or so in advance they would have this system all set up and then they would actually conduct the presentation and then of course you know the stock price would change as a result of that every report so he was doing some industry reconnaissance he was able to actually
do a brute force the credentials of a particular person from this one company he was then able to intrude at around 2:15 and he was actually exfiltrating that earnings and the non-public information so what happened was again this IMS health incorporated a company they published that information to this particular server and he was waiting for it he got access to it he knew what folder it was going to be in what directory and so he just sat there and he waited he kept looking for it kept looking for it and then when it actually got landed he pulled the data down and then that's where we actually see that he was conducting his trades and that's
how he got he got busted so summary judgment he had to pay back that money plus the interest right he actually never appeared in court because you know he's in the Ukraine he did not move future Guinea to the source of the information or those persons with whom he had transacted in the market so the court determined that he was not liable for insider trading at the time so the SEC actually modified the definition of insider trading so that if another case like this did appear it would get Cuba we get covered under insider trading so now they have actually called this particular term outsider trading so another one this was actually this a group of hackers got really smart they
actually targeted PR firms you know when you're a public traded company you get your press releases ready you know game you announce your earnings you send that out it's another awesome target if you're looking for this type of information and this is where we actually found like folks that were communicating via darknets there was a lot of other investors involved this particular case that actually these guys were doing these trades up to i was actually passed 2014 almost into 2015 the hackers well one of the guys was names of vadimovich and i'm realizing these names so what happened was he got busted in the ukraine for stolen credit cards when they actually went they think
they got his system and the FBI got access to that as well but they were working with the ukraine police that's when they actually discovered this particular scheme they would not have known that these guys were doing this unless that one guy he did something stupid he was doing still my cards and things like that and these guys made it over like 50 million dollars so these are the hackers and then there's a new boy group so there's a number of people that were actually part of this there were 35 different people that were involved in these trades they're all over the world these guys were financial wizards one of these guys he was actually a former VP at
Morgan Stanley so the hackers the way they worked the first target they went after was this one particular a PR like newswire called market wired they did a sequel injection and they were able to install reverse shells and then they were able to you know access various internal login credentials they were able to escalate their privileges fairly quickly for looking at some of the stuff with market wired they weren't logging a lot of information I was actually trying to dig deeper into this and really reading into some of the criminal complaints so that raised some challenges as well but luckily a lot of that information was on one fellow's computer and that's how they were able to use that as evidence
they downloaded over a hundred thousand press releases right that's what they did and then what they did is they they uploaded them they actually created a hidden service they uploaded it to a website and then they want on these various criminal hacker forums and they advertised their their access and for as little as ten thousand dollars you can get access to this huge repository of earnings information it's a pretty good deal especially when you can make you know three hundred thousand dollars in one of those transactions and one of these traders actually got access to that some information there was two or folks that started on this and then they started getting other people involved
but then they got greedy right they targeted another firm called a PR Newswire this group had a little bit more tighter security they actually threw these guys out three times the first time they got in they didn't attack the second time they actually installed malware on a system and they were able to excellent rate data that way and that was identified and then they lost access this was over the course of several years they lost access and then one of the guys actually bought on the darknet they bought a bunch of social media logins a huge repository of it and just happened to be that some of the login credentials that people are using for social media they're using the same
accounts for their admin accounts here I know that never happens in real life rightly so and then then another one they did was business wire and this one they actually bought access from a hacker who was advertising he told them hey I've already gotten inside here you know I don't want to get involved with the selling this information you guys obviously already have customers so they just sold access directly right so it is becoming a pretty big business enterprise right they're making it quite a bit of money from this they've got lots of customers they even have awesome customer service because one of the pieces of evidence that was used against them is they actually created a video
showing customers how to go about actually accessing this information on their repository
so the traders were actually opened up several different trade accounts like infidelity so all these different companies were actually involved in the trade leaving we're creating shell companies to try to hide this as well so they did a really good job I mean the the white-collar side of this they really knew what they were doing the hackers as well and they made around thirty million dollars that numbers actually changed one of the guys he actually he pled not guilty he was kind of the mastermind behind all this and it actually came out that it was over a hundred million dollars and they only recovered fifty three million um also they made some mistakes though too so
some of the IP addresses that they actually went in and they went to the PR Newswire they they luckily had kept their of their logs they actually found that one of the one or two of the traders actually set up trading accounts for the hackers that were actually involved in this right I think at some point they said hey you guys are making all this money once you guys help us and then what happened is the forgot to change the his IP or as VPN login and you think cover his tracks so there was actually the same IP address was logging into the PR Newswire that was doing the hacking and it was also logging into
some of those trading accounts and that was another correlation that was actually used against them as evidence so that's a really good case where sometimes you might have log files it may not be useful for you now but it could be useful for FBI or someone else that is conducting an investigation which could be good or bad right so this is sort of some of the transactions that they made there was a caterpillar was one of the big companies that they did this with but there were I mean there were over 800 trades were based on some of those press releases that they had actually made so you start to see you know you know this is a pretty good day's day's
haul well I get a real job when you can just you know make tons of money just doing stock trades this is the fellow he was the former VP at Morgan Stanley and he made around 17.5 that actually has increased to around like 30 million or so and he pled not guilty what's really interesting though is you know after he left Morgan Stanley he became a pastor and his his congregation actually was trying to do fundraising for him so this was a really this gets really really weird I mean actually when he pled not guilty and act he was actually in court and a bunch of his person errors or whatever they actually came and we're actually trying to help
him through this and do you think he was guilty or not guilty yeah they found him guilty and he's going to be doing at least like a maximum I think it's 20 years in prison for his involvement in this several other people had pled guilty and they actually test ended up testifying against him so some of the data sources that are with this I like to kind of this is where I like to look at this is you know what data sources are actually involved so the online brokerage web servers and application logs was really helpful to have the bank records right being able to have access to that you can identify especially some of the folks on the white-collar fraud
side they have access to some of that I've actually done some things where I've Splunk some of that data I've actually did some investigations bringing that data in looking for irregularities some business registry data because they were actually creating a lot of different shell companies one of them even have an ice cream it was an ice cream company and all one year all of a sudden it became incredibly profitable the newswire user authentication of VPN logs the forensic images from Hermitage computer that's really what helped drive a lot of this stuff if he had covered his tracks better encrypted that or you know got rid of those who destroyed the drives there wouldn't be the evidence against a
lot of these folks there was a video tutorial made by Irma and how to actually download those files right that was really helpful for the FBI some of the tools compromised credentials so a lot of these accounts they didn't have any sort of multi-factor authentication it was just username and password that's that's not good right hopefully that's changing there was some advanced malware that was involved there was sequel and sequel injection definitely lack of appropriate logging and one of the news wires you know if they would have been looking for some of those regularities maybe the other two might have not popped and then of course tor and proxies right if you see someone logging
into tor and accessing your server that's pretty easy to do nowadays that's maybe something you want to pay attention to maybe they're just trying to you know protect their privacy but if they're accessing like a brokerage firm or something like that I'm saying I'm thinking like ninety-nine percent of the time that's going to be some sort of criminal activity another form was actually targeting another type of attack was targeting legal firms the use of guys were in China neither the hackers they even had a whole business plan around that they had PowerPoint decks of how they're gonna go about doing this so again that's really useful evidence they go through this process right so around July 31st they targeted their
first law firm it was a New York law firm in some of the criminal complaints the the law firms were able to mask who actually was so I didn't I don't know specifically what they were I have some guesses but they're pretty heavy hitters and then they're able to download some information and this is where they're actually looking for data that's tied around mergers and acquisitions right so we've gone from PR and earnings now we're looking at mergers and acquisitions so that's another piece of valuable data so they actually looked at so there was the Roche acquisition of inter mune Intel's acquisition of Volterra and then they were actually trading information that they discovered they target a second law firm and this
one they looked at the Pitney Bowes acquisition BorderFree and these guys generated around three million dollars in funds again that's that's pretty good day's work right and these what they actually ended up making so each of these guys made over a few of them made almost a million a few of them half a million they had to pay all of this back there was actually a few guys I'm not sure if you guys remember this it was findt four there was actually a fire I actually did a really cool write-up on this these guys were actually targeting primarily like pharmaceutical companies and they were doing the spearfishing campaigns they were actually trying to get in so they
can monitor email in in the companies right they're not necessarily exfiltrating sort of data what they just want to do is monitor and they're looking for anything that would be useful for trading in Viet M&A type of activity and things like that and they actually sent a request to breach decrease details to at least eight companies some of those companies didn't know they were compromised right and then the SEC is now involved and they actually found that some of those companies didn't have proper security controls in place so there can be some some legal results of that SEC wasn't they're not invulnerable either some brazen hackers actually access the Edgar database this is where companies
actually upload a lot of company filing information and things like that they got compromised but there wasn't a lot of information about this they they know that information was exposed but they didn't go into any other detail about how that information might have been used they were monitoring they're looking for you know if people that might be trading on that particular information but again that type of activity can be really difficult to identify between a legal versus illegal versus a legal trade you really have to be able to dig deeper into that especially if they're really smart and know how they're doing it you can do it in smaller transactions right and you can go go under the radar um so I did
dug pretty deep in some of the you know in dark web looking at some of these these services that we're offering insider information there's several forums where you can actually if you provide insider information they'll make you part of ember and then you can start to actually trade on that information as well so I'm not gonna give you guys the URLs for these I don't wanna get in trouble this was interesting there was a forum you know he's actually talking about he actually works for a major Wall Street company does millions of trades a day he has access to a bunch of information around some of this stuff and he was even saying hey I'll give you
this information will do it 50/50 you know give you hard cash or Bitcoin and he'll make sure that there's no paper trail right this website there was a I think I'm not sure if this was was or not again this one's where you actually have to provide them insider information to actually get to get become a member and I'm not sure if this is either it's real or it could be the SEC in law enforcement trying to get people so I did not submit anything not even fake stuff so I'm just telling so a lot of the trading firms they do a lot to monitor traitors right so I was actually actually talking to one
particular company that does this and they go yeah we monitor every single every phone call they monitor Skype they're monitoring all these types of things because they want to make sure that they're not doing any sort of insider trading because you know that can be a huge fine for them and can put them out of business well what's interesting is that they don't necessarily monitor what they're doing when they go home right so if someone has access to that some of that information that's that's that's really easy for them to you know they're using encrypted chat app you know going to tor there's also the good old paper route right just writing a note on a piece of
piece of paper and that's actually what happened in this next case there was a fellow he worked at Bank of America and he worked in IT and he had access to a bunch of information his name was Daniel Revis so he's had access to these these kind of big file shares that we're dealing with mergers and acquisitions of companies and what happened was he just would write these little notes to his girlfriend at the time they would be love notes but in those love notes would be communication about a particular stock he would say he would have a way of putting the the name of the the company of the stock ticker and then also some pricing information as well so
he made him look like there were these sort of paper love letters she would then hand them off to her father who would then he will also ended up sharing some of that information over time with other people that were involved and then he got a little dump he had some friend one friend that was having some financial difficulties so he started giving some of that information to him and they were using an encrypted chat app right they would actually destroy or supposed to destroy messages that's if the other person deletes it right so he would delete them on his phone what some of his friends weren't so smart and they still had them on the
phone when the law enforcement came so on that particular case so there was a lot of different types of organizations that are getting targeted for this type of information so the data we want to go after if you're a hacker you want to go look at for earnings reports patent information I've seen some cases with that so if you're a legal firm you know you're working with patents if you know that someone's going to get a patent approved or not that can be incredibly valuable information because that's going to have an impact on the stock any sort of M&A activity FDA status right so that can be a big deal if someone's gonna you know maybe a drug isn't gonna
be approved for whatever reason that's has it usually has a huge impact any sort of pharmaceutical company that's gonna you know if you can short the stock what-have-you I believe that vulnerabilities as well can be an issue or if there is a breach if I know that a company was breached before anyone else and I can trade on that information I think there have been some cases of that where organizations where they have been breached and those people actually did trade they knew that information was gonna go public at some point and so you made money that way Manufacturing yields so even looking at a factory and like ICS and even like SCADA types of systems right if I can
identify maybe a secret formula or I know how much product they're making I can then make an assumption around how much revenue they may have over the next quarter so intellectual properly and you sort of formulas so organizations are gonna get targeted or give me legal firms M&A firms PR firms investor relations firms a factory any sort of incident response and of course company HR legal and IT so again there's a lot of different organizations to be target we could see that the companies themselves may not necessarily be targeted in this case it's going to be your service providers so one thing you want to think about in your risk assessments is what type of information
anything here are we sharing with maybe our PR firm our legal firm what do they have access to then we can actually start to ask them questions about how they're they're protecting that information and hopefully when you show them this deck you can you can show them why why you care about that so some of the tools you would look for a lot of endpoint monitoring I'm always frustrated when I go in and people say yeah we're monitoring endpoints but they're just getting regular windows law event logs you need to get a little bit more fidelity especially when you're doing malware investigations sis Mons really great like it's a free tool there's also OS query which is open
source commercial tools like CrowdStrike Falcon carbon black all those types of tools are gonna give you a little more fidelity you may not necessarily win or deploy to every single device in your environment but maybe some of those critical assets that house some of the sensitive information that's what we really want to make sure we're monitoring for the love of God multi-factor authentication please looking at data loss prevention you know a lot of DLP solutions that are out there I've even seen people homegrown homegrown some of this stuff I'm using like plagiarize plagiarize ation software so you can actually you know see if any of that data is leaving your organization via email what-have-you proxy firewalls can be useful I do a lot
with our this one TVA product looking at user behavior analytics where you're not just looking at signatures you're actually baselining behavior of individuals assets and applications in your environment and then you're looking for anything that may stray from that if all of a sudden someone in my organization maybe accesses a file share that they usually don't access and it's a late in the evening right that's something that I may want to pay attention to it doesn't mean this is how they're doing something bad but it is something that might want to maybe develop a hypothesis around doing this assessment of your partners again so it can be legal in PR I'm really surprised how many companies don't actually do
this they do a great job of securing their own infrastructure but they don't ask the right questions when they're looking at their service providers where but whether it's a PR firm your legal firm anyone maybe that's even handling your HR data right you really want to be able to understand how they're securing that particular data do a phishing exercises can be helpful a lot of threat intelligence sharing if you see that some of those PR firms are all being targeted right if they start sharing information about some of these things hey we've noticed this this suspicious activity have you guys been seeing something similar here are some of the IP addresses that are associated with this you know maybe if the they
collaborate a little bit more they can identify some of these things before law enforcement does looking at all the data - I do a lot with the insider threat so you know some of these look familiar I mean a lot of technical data courses that you may have around your network and in about your environment but there's also a lot of great non-technical data sources that can come from HR and from other or other organizations within your company I do a lot around insider threat I like kill chains you guys are probably familiar with the Lockheed Martin kill chain so this is an insider threat kill chain I actually stole it from a fellow at the
FBI they actually leverage this for conducting their own insider investigations for FBI agents when they're actually looking into them but there's things you can look for if you know that someone is having financial difficulties for example that can be an indicator of someone we may want to have more verbose logging again it doesn't mean that they've they're doing something malicious or illegal but depending on you know your your industry and what you're doing you may want to monitor that a little bit more closely there's things you can do on the search and recon looking at not more technical data sources usually if someone's going to break bad as I refer to it they usually probe first they usually
see what they have access to they try to identify what data they can actually get into and then you'll actually start to see the acquisition and collection of that particular data and then there's the exfiltration or our damage to systems so again there's non technical indicators this is kind of where you'd be able to start to actually look for indicators there this can also leverage a lot of like UVA if you use machine learning things like that you can start to identify things that are suspicious and then you're gonna have the more technical indicators right those are things that we're probably more familiar with and with our traditional security data sources I'm doing more research on
this there's quite a bit more to this that's coming I'm digging into some other where who are actually having cases where there's a breach and we're actually seeing the hackers trading on that knowing that the breach is going to be notified there's also a concern now too is if someone identifies a zero-day vulnerability and they know that they're going to announce that at a certain point and they share that with someone and they trade on that information that can still also be considered insider trading as well or outsider trading so if you guys have any questions ideas or stock tips for free to reach out to me Splunk we're actually going to be sponsoring a happy
hour from 5 to 7 it's going to be over at nest so if you guys want to talk to me more about this and you want to maybe you know again we can we can talk about stocks more than happy to stick around so thank you so much [Applause]