Hands-on Writing Malware in Go

Show transcript [en]
next presenter Stuart McMurray and Carson cease and thank you for coming to our talk hi I'm Stuart McMurray we'll talk about a bit of programming go so background for me real quick I'm Stuart I'm a red team or Dyer net it's a Twitter QR code really what you want to do in a hacker puts a QR code in front of you is take a picture of it I'm rich in retired Nedim I'm on the UNIX side of things mostly and more and more in the windows East Sider excuse me on the networking side of things as my company makes a network traffic analysis product and one thing I've learned when we've been developing this in emulating
various types of malware and various types of activities but not as go is a really great language for writing bad things people run a honeypot you'll find a lot of go in there nowadays so Twitter github so on and so forth I'm not affiliated with Google go is a Google product to Google project I guess I have no affiliation with Google my company would like me to point out that they've used in this talk or not there's also I'd like to point out myself that if you write malware and use it or even if you write malware and put it on the Internet somebody might use it so like schools it's like hey I wrote this really cool
thing I think I'm going to send it through Canada that would be awesome please don't do that and when you do it I'm Justin Trudeau pleased to meet you my name is Carson cease I'm a current student at the Pennsylvania College of Technology this past summer I interned with thanks guys classmates I interned with Stu at iron net and a couple of other folks there did a little bit of go development which kind of sort of led to this talk there's my equally legitimate Twitter QR code if you're interested in that sort of thing my github as well I'm also not affiliated with Google and in addition to my past employers my school does not necessarily endorse what we're
going to talk about today so speaking of talk what are we talking about first of all just a quick overview of go kind of why it's good why it's maybe not so good a little hello world demo and finally some malware bits real quick some notes that you might want to follow along with or you can see that link at the end of the talk has pretty much everything we're going to talk about linka fide so to speak so go it's general-purpose curly braces developed by Google it's boring which is nice and at first that term seems a little bit unusual but let me put it this way so you spend some time a couple
of hours writing Lisp and man you just feel great you get all of this code done you you spend like three hours on it and you're just fired up you feel like you're the best programmer ever you just process some strings and you feel great about it well with go you spend some hours and it your code is pretty good you're happy with it but when you step back and take a look you realize hold on wait a minute I just wrote a worm that can actually take over the Internet let's do might know a thing or two about that mr. trudeau right so goes compiled it doesn't require anything you know to be on the target like a Java Virtual
Machine or something with Python some sort of interpreters compile makes a binary it's good for a couple of things Network clients and servers and kind of systems level programming with what's interesting about those three parts is there's all kind of when you put them all together it kind of makes malware which is what led to this talk so so why malware why go to parts it's easy and it works it's easy it has a large standard library it there's pretty much everything you need in that standard library when you want to get started however if you can't find something there you might have better luck finding something in a library somebody else made or make your own and put it on
github you can't really get fancy and that kind of goes back to the nicely boring the codes easy to read if you're reading somebody else's code and more importantly it's easy to write and kind of talking about easy easy means fast fast means cheap cheap code to write and that means that when your malware eventually gets caught instead of going through tons of time to make the malware really difficult to catch really hard to interpret you can just keep writing more malware on the note of fast it takes a weekend to learn just a quick side story about that this time last year I think it was in this very room I was sitting there was a talk still was giving about
some go and some other bits and is there and I thought huh let go seems pretty interesting I had heard of it before but never really followed it but when I heard it could be used for malware and I'm a cybersecurity student I thought I'll check it out I went back to school took a weekend learned go and then the following summer I was writing some go for iron net so that's the easy bits and it works and when it works it works nearly everywhere you can cross compiled to a bunch of different architectures and when I say that that means when you have a Linux toaster and it's runs some it running some obscure distribution go will
probably run on it and if your toaster doesn't have all of the dependencies you need to run go that's okay because it builds them all into the binary so you don't have to worry about any dependencies on your toaster that you're trying to do something with finally it plays nice with C okay so that you know that sounds like all kind of rosy things for for working with malware but what's the catch what's what's important here and what can be a drawback they're really big binaries if your toaster only has four megabytes of storage on there you can't really fit such a big binary in such a small space it's kind of POSIX focused and that it works well on
Windows pretty okay that's really the only reason to do can write windows code however you're gonna have a tough time writing me me cats it's mostly cross-platform there are some caches to that might not work on all toasters but for the most part it works pretty well cross-platform there's some different like webassembly kind of things that go can do but not everything's quite there and finally dependency management is still a little bit young and go and it's in active development there's also one other catch all right so we kind of know what the catches are what's nice what's not so nice so what do you need to get started first of all you're obviously going to
need to go compiler it's not terribly big or complicated download it from their website extract it set a couple of environment variables and you're pretty much good to go and if you're not so interested in downloading a big you know binary compiler to actually work with it you just want to kind of play around go has a great website play golang.org where you can run a little bit of everything not quite everything and it's a good way to just kind of learn go experiment goes nice because it doesn't require any crazy IDE or anything complicated to use you just need a text editor you could use ed if you're into that sort of thing if you're less into that sort of thing
VIMS not a bad option vim has a nice plugin for go and then if you're really soft and I admit to this you could use vs code vs code also has a nice go plug-in finally if you want to use some external libraries that other people created it gets helpful to have hi so I've gone to a lot of these like hey use this thing it's awesome talks and they're like hey here's like why you should use it it's really cool and then you're like oh that's nice and then all of a sudden is like BAM we've just got on target and like whoa how do we get there so we're just gonna take a couple
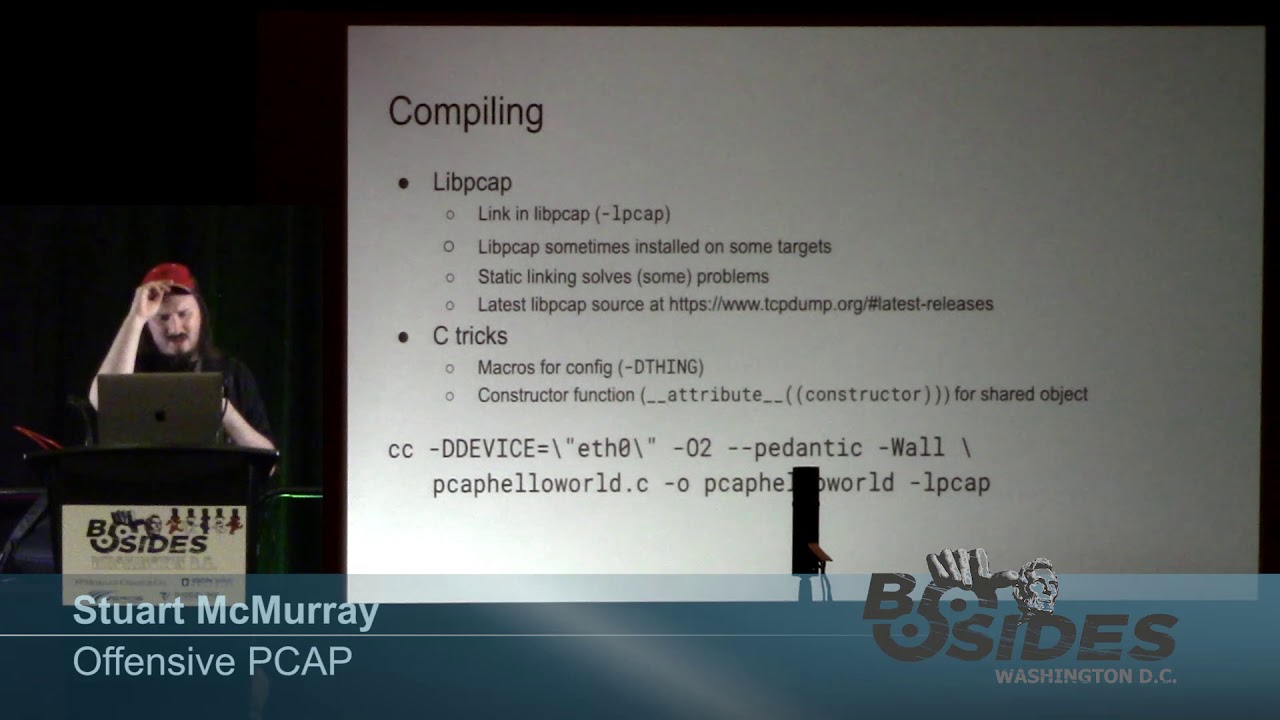
seconds and do a like how to compile a thing it's real simple you write your code in them which is okay nowadays we don't you don't chain people for this anymore you write your code you know in whatever text editor you'd like and we all tend to use the same formatting style it's actually like everybody does go imports will take care of that for you so you write your code you like a indentation and then you find yourself nicely indented we'll see that a couple of minutes after that go has this sort of like a linter ish thing is a little like linter plus built in so let's check and see if you have unused variables or
strange return values or whatnot go vet does that we'll see it somewhere we'll see in a demo later in the talk and then you just built and run it it's a binary you build a run you put on target running something along those lines so here's quick quick little demo of what it looks like so we'll program in cat because um really ed is not cool anymore so right it cam you can see this is not perhaps the way you would like your code to look that's okay so go imports will handle a few things for us handles the package statement so main just like you're like a most languages nowadays handles your imports what libraries you can use so I figured
out we're gonna import something from the format package and it makes it nice to look at well vet it okay clean bill of health that's cool compile it we'll see that it is in fact a an LSB and elf binary it's nicely statically linked which is quite good it has a build ID in there that might make things trackable but it's okay I'll just put on target and run it and sure enough we have our hello world so really easy to do it's also nicely injectable both as a DLL on Windows it works quite well we'll see it on Linux here but it's it's pretty much the same thing go has this concept of build modes so you can build
it as a binary you can build it as a go archive like a legacy archive ish and we'll just we'll inject it however you'd normally inject things so quick demo there by the way if anybody can tell me how to get rid of this black bar it's like six conferences in a row now I've been trying to figure out to get rid of this thing I'll buy you a beer here did not turn it off and on again peanut gallery all right so here we go we have a little program it'll take and write a file temp X with you know a little hello from app it message Oh grunt go imports it's nicely formatted
notice we have main here that does nothing just like in C where you have attribute constructor and go because we're gonna make this a library we have in it which is a constructor function so it'll run before before the main function or before whatever function is exported it's good for malware you just inject it and then you have a thread going you're like man cool got a callback Sears go vet in action up here is hello from paid and I got a formatting directive but I didn't put anything in there I mean it's printf works like Esper enough and see hopefully using some better an esper enough but yeah so hey we need a percent V which is just you
know any any verb at the end it'll go change that real quick you know find the line where we goofed was line 11 it told us and we'll add a get pit in there to print the pit there you go ports gives us clean bill of health nicely formatted so on and so forth we got our little import line taking care of us nicely which means you don't have like a billion includes like you haven't see really I really need all these is that debugging toko files nicely turns out it's a shared object but heads-up it's dynamically linked you can statically link shared objects it gets a little wonky so I'm specially for cross compiling him put on target shove it in
notice we got a bunch of threads now and that's pretty typical to go runtime it's not an interpreted language by any means but it's garbage collected so you do actually have a runtime there and then we got the threads started and then we get deal open mode returning so racy ish but it's writing for you it's kind of normal and yet we got our hello so there you go so the first little bit of malware we're going to talk about is domain generation algorithms there DGA and sort of the high-level overview of this idea is you have a defender and you have your malware inside his network and your defender blocking couple ip's a couple of domains couple thousand IP
as a couple thousand domains how did your malware reach out so one way of doing this is creating sort of predictable no mains that the where reaches out to and then you the attacker will register a handful of those that the malware can eventually connect to it can still be blocked and there's different ways of doing that but for the most part it's a little bit harder to get around since it's just random however it's not totally random under the hood what you're doing is you're using something like the current day which might involve the year the month the day some combination you might have a seed you might have an additional string in there and at you the malware
author it's predictable to you you know what to expect the defenders don't necessarily know what to expect it's pretty easy to implement and it's hard to detect but what does it look like so here's some of our domains alright we use our DGA algorithm to generate a handful of domains a couple for Monday Tuesday Wednesday and our malware he's gonna try every single one doesn't know which ones registered which ones not be he's gonna try them all and we're gonna register two of them one on Tuesday one on Wednesday so when our man reaches out on Tuesday it gets in touch with that domain and same for Wednesday our poor defender though he doesn't know what to
block he sees all of this getting reached out to and he can block some things but he can't block you know a seven-letter string you know for popular video site YouTube so it's it's not exactly easy to get around and it's easy to implement so what's going on here under the hood first we we have our in this case our string of our year-month-day and then some sort of counter to make it change for all the domains you want to generate every day we hashed that in this case md5 and then we use that we append our top-level domains or com we append that to that string and then we return it I actually wrote a DG a library in go both sort of
for the purpose of this talk to show how easy go is and also to kind of put this together and say hey look we can get a time we create and create a new domain generator using the Year month the day we give it our our top-level domain and then we just call generator next ever time we want a new domain and we can use this on the malware side that's implanted somewhere and then we can use this on the other end to create a whole list of domains and pick the ones we want to register so what does this look like just a quick bit of code already formatted we have the domain generation
library that I wrote RS DG a imported we're just grabbing the current time we're creating a new generator and that generator is used in current year month day com the thing here is the way libraries written could be calm or calm and of course this isn't exactly what you do in real malware but just to give an example we're just gonna have a for loop run five times and print out five domains so we run our go imports looks good we run our go-go vet looks good we build it and we run it and there's our five domains so there's it's a great way to establish your c2 now you've got coms usually HTTP sometimes HTTP is not quite
what you need either it's heavily scrutinized maybe they do some TLS man in the middle or something you're like it's not a great way to go so another easy thing either easy way to get data off of a network is DNS you can always trust HTTP HTTP and DNS to get out of a network DNS is often a little less scrutinized it's like I don't like control plain stuff I'm not gonna watch that too much or hey we've encrypted all our DNS we can't see it but we encrypted it so it's cool so easy way to just say take a bit of data not too much perhaps is just chunk it and code it encrypt it
and it's taking a DNS label could you run the DNS server you'll get that query because if you're doing it right it's gonna be a never-before-seen query a couple caveats here a DNS packet usually is about it's supposed to be under half a kilobyte ish usually you get like 100 bytes ish if that it's actually kind of a big packet so it's not it's not fast also it's case insensitive so if you're playing with this expect cases to change in your queries as they go from implant to server and it's it's kind of one of the cool things that's used nowadays so it's what it looks like graphically we have our implanted victim machine and it says hey
on the network it says what's internal DNS server probably it's DC hey I'd like this ridiculously long thing please and the DC is like well ask us guy and this guy is like I don't know ask this guy the upstream DNS so you're Infoblox or something and you know typical normal DNS recursion goes on and at some point you go and boring CDN kamo bad guy and you get this long query and you're like oh I'll just decrypt that and now I have a bit of exfil so a little more concrete example grep out at our routes hash from Etsy shadow this is made up from a dummy account by the way see people like on
their phone was based 32 encoded base 32 is like a 64 ish there's one fewer bit per byte you get but it also is case insensitive so it doesn't you know case changes on the wire won't won't affect it and servers do change case so we'll take this nice encrypted large thing we'll just chuck it into bite-sized chunks put it on put it into create by the way it's good to have a bit of randomness so that no caching happens so you get everything to your server it's being an example speaking from experience and then we'll look fill it so this example will just say we've done some host survey we've run a net stat and we
have enumerated the drives and we've looked at the process listing or whatever else Chuck that stick that in some variable it's just a blob of bytes I'm will track the bytes and these typically are not just a function call but you know we'll chuck it into some bits and then each Chuck will X fill it so we'll take make sure to chuck is thank you google that was helpful make sure our chunk is small enough and we'll just yeah we'll just call the the you knows look it up as an IP address like you'd look up any other IP address except well hex encoded stick it on our domain X sample comp or ICD and whatever
just registered and put your name server records I mean probably we'll do some sort of encryption with it encryption thanks by the way it adds entropy so won't get cached it's actually doesn't make that great a demo so I didn't record one so apologies however that said go playground not really a demo this link you can see in the the notes that'll be linked at the end but also in the slide deck not a great demo but it does kind of show what's going on here as far as hey you can hit play and go playground and you can see here's your input and here's the output and then here's how it decodes it so just
something worth mentioning it's also a nice library carson's put together to do exfil over go and take care of some of the boring bits next thing talk about that go makes particularly easy is domain fronting domain training it's kind of a hot topic a few months ago maybe here so ago and and really under the hood is it's just your yeah every TLS connection that says hey server I want this I want to make a connection to this thing that's just like an encrypted tunnel basically and then you have the HTTP under the hood and HTTP is just HTTP wrapped in TLS that's all really is an HTTP already has this like hey I want
to talk to this thing so you have to two sets of hey I want this and normally they're the same and sometimes they're not and if they're not on the wire all you can see unless you're do TLS man in the middle on the wire all you see is the outside the TLS s and I the server name indication today I want to talk to you tube and then you know it's whatever provider and the provider is like oh I have this HTTP request I know how to route this awesome and it's they don't really always check the major providers Google I think Amazon now they've they've made this hard or impossible but yeah some of the smaller ones it works
pretty good and it's it's really quite hard to find on the wire unless you're doing some really cool endpoint stuff which that works it's pretty easy to implement if men in the middle T last man in the middle happens oftentimes those two streams are not reassembled there's no like correlation between the TLS and the plaintext and it's pretty much every tool nowadays supports it because it's just simple this is what it looks like graphically I'm you got some implanted victim box and he says hey I'm going to make this thanks work we see it now I can't see that he's gonna say hey I'm going to make this TLS request to kittens not boring CD end and XYZ it's
normal under the hoodies can be a I want I want bad guy the bad guy that boring CD ended XYZ in the fire was like yeah cool kids are like nice I like kittens I was told to watch out for this bad guy thing but yeah that's not there I can only see the TLS at the web server that serves all of the the CDN and CD ends do this pretty well like yeah sure here's here's the cert going this way for kittens and I'll route it to bad guy going this way so we have our nice T to that you is whatever so we've set up on the back end but on the wire it's just kind of
cool it's a couple ways you can do it and go so one way is like this you make your nice HTTP client obstruct and it's you make your HTTP client and you say hey for anything when we connect TLS make the sni something benign looking and then you know when we do our get request get something sneaky but on the wire it'll because you've set the TLS configured I'll do that and you know you get your response and do whatever you do with your response thank you that's cool we'll just print it out I totally pipe it to a shell or whatever another way to do it just like this quick detour one of the cool things
about go is you can change variables at compile time so it's really good for like an implant ID or like you know I know there's this particular thing in this box so just declare them globally so the s and I will keep as this benign domain fronting demo thing GA and we'll play with the host header in a bit there you go so we'll just work the other way to do it you roll a request just like you uh you know say hey I would like to make this HTTP request but you set the host here and you set the host to something that is not the s and I so in this case by default it'll be a DF demo GA and
then you knows make an HTTP response and this is as easy as it is actually and we'll just in this case I'm pretty to standard out we could totally have piped at Rachelle when we run it so running it looks like this clean bill health good venture RS and I is DF demo Duchy a our host headers DF demo JJ and it was not found because the the way go back the you know request for tasking you know Jannik demo is not gonna give us any sort of tasking if however we set that host header at compile time to something like a bad move stodgy a something something is gonna give us tasking violet run it
there we go it's like oh hey that's kind of cool and you totally could just pipe this to a shell Linux lady did something like that it's just like curl typed SH and cron and it actually works pretty good so is domain fronting and go it's really quite easy it fits in a tweet I found out and good luck catching him so unless you do a TLS decrypt tailless man-in-the-middle in it okay sometimes last thing we will talk about propagation dssh dssh worm these have been around since mr. Morris got himself in trouble so I was telling it or something but he's been around quite a while a long time this is the same SSH
we use all the time it's the same even even Windows is getting SSH nowadays ish kind of really what they did was they just took Linux on put it on when it was like hey we have SSH now so what this one will do is they'll just try a set username and password or everywhere and and then you know I always get yeah but in our environment you can't do that because everything has a unique password and you're like sure about that buddy so um curiosity how many of us have seen somewhere maybe creds we use like crazy there's like a lot of people who are like kind of what's your company also path or a password off is pretty common
it's actually watching watching a honeypot one so it's like man everything is trying password you're not trying any other authentication mechanism SSH supports so we'll do we will take a TCP port and we'll just listen on it's kind of a mutex kind of like a hey we only want to implant once what mr. one of the reasons that Morris got in trouble with his worm is he kind of brought the the little nascent Internet to his knees there's no like okay that's enough so you know when this thing implants a box first you lose try and listen and if it can't listen it'll die and then I'll just take this creds a pair that we've
built in and you'll try it everywhere it can I've written this one to only go after ten wack eight turns out if you put a worm on the internet people will use it and then it turns out people notice that people use it and ask you about it so don't do that so again if it all succeeds it'll take is Linux specific so we Tommy Carson mentioned like hey sometimes it's not totally cross-platform well we'll go even worse and we'll just read from proc self exe which does not exist not on Linux but okay well copy the worm we'll start it the next box we'll just drop a binary and then we'll we'll iterate there we go
um so you can make nice command-line arguments and if your if your software is meant to be used by users is a nice thing to use the flag package to build command-line arguments the other way to do that is just to have this massive VAR block at the top and say hey this is this is the config and do compile time config if you want to change it so you know simple things set the credit the first octet of all the the hosts we're gonna go after so on and so forth set the bite it's what the binary names interesting a little thing that we won't see in this demo but won't seen the slides I don't a demo for this one but I
was like hey cool so I have this like network of a hundred VM set up which is really good for your processors Heat by the way I have 100 VM set up and I was like I wonder if it's done it's like oh yeah I should have it like talk to me so I'll just make a query to kittens calm I mean I I could not find a good way to record a demo other than like watching DNS queries come back and they're all for kittens on yeah that's kind of boring so we'll just look at chunks of the code if you would like it's on get it so I think again I'm just I put it in there
so the mutex the preventing multiple executions and listening listening and see is great you asked for a socket then you bind to an address then you call this and then you call accept then you maybe do a bunch of gawk tolls and all sorts of great stuff here listening and go is sort of a one-liner and this is like a go one-liner go is a very vertically long language but it's it's a go îsh one letter one-liner ish but anyways if it fails then were like oh probably gonna listen on that and life goes on making an ssh connection is you just make a config and you tell it to connect almost like command-line SSH
except encode so you just give it a username you like a list of authorization methods it actually lets you validate the host keys which was really nice some sort of connect timeout and it's thanks yeah we should have gone with a PD on yeah yeah we totally should we were giving a talker like hey PDF or Google slides so yeah and that's that by the way if you replace SSH tile with net I'll tell you make a TCP connection so it's always a pretty regular like boring boring language and they'll propagate so we'll take you you have your SSH connection we'll call it C thank you SSH is a multiplexing protocol like SSH really if you boil it down to it it's
just a tunneling protocol and it makes like channels inside of it so we'll make a channel that session Channel and we'll connect standard into that channel to the worm we'll have read the worm in from proc self exe and we'll just say hey in this session run this R in this really massive command and we'll that payload bin from like 3 slides before works like yeah we'll call it cron D cuz I mean nobody gonna kill crown to hear it so we'll write two cron D and temp because cron D always runs out of ten you'd be surprised like actually this words like oh hey don't worry go ahead sneaky yeah totally should use a PDF and
going back to the whole the whole easy thing that combined output thing you place s session with like Oh s dot Venice H or something or other on command I've been sha-3 what it is I mean that's how you run a command so it's you know the theme and variation is kind of it it's really not the most exciting language to write but then you do awesome things with it so that's that's in a nutshell some cool things you can do with go if you stitch them together you have like some pretty cool malware there there's all sorts of stuff there's a lot of frameworks out there that use go under the hood a few
few things I found from just from experience it's much easier to write if you have some sort of editor plugin it doesn't particularly matter what editor use cuz you can form it you're gonna format it the same anyways using vim there's vim go if you're if you're using GS code some people use the BS code Microsoft has a library out there or at plug it out there of course you mentioned both the tour and the playground before the tour is really nice it's like when people like how do you program I'm like here take this to her and like two days later the programming we don't have a repo and go it's a compiled language it compiles
really fast like I've not seen anything take more in a couple minutes but the playground is pretty close to that and actually a lot of the plugins at least on good editors well we'll just send things to the playground if you ask so a couple more things trim path when you pass it to the go environment or any facet of the go compiler will trim the path of files out up to some namespace II thing so you just have something sitting in your home directory a single file and build it won't put your fire your home directory in it but I was my boss at one point was old job was like kind of giggling I was like okay you're
grown man why are you giggling he's like hey this is your malware isn't it yeah it's like well I strings didn't I found your name I'm like yeah he's like there's an incident spun up because of this apparently if you leave things for months on a domain controllers people notice but they don't notice like strings it and find my name good stuff and the last thing if you use Segoe enabled equals zero it's an environment we pass to the compiler dynamic linking won't happen every so often the static thing is it's like hey win this one environment we're gonna use you know this box is DNS or something so I'm usually if you're writing malware you
you want to get as little as possible so that that's the bulk of the talk we're gonna open it up for questions before we do from giving this talk and smaller and larger and so on environments have learned a couple things that are better for Twitter or meeting us in the hall or IRC or something along the lines so asking how to just like hey how do you get started the tour that answers that I'm and then invariably somebody's like hey I tried go and I hated it because I had a bug question mark so whatever you talk about go also if you use open BSD you ever get to talk about that you'll get this to somebody always says
something to the tune of hey my my thing uses this language or design choice or editor pick seven advs code or paradigm or this is the best Power Ranger question mark so yes I'm happy to talk with you in all so I'd like to open it up to questions there's QR codes there's those notes again and then if you really don't like QR codes from a pair of hackers there's a Twitter user names I think it's the first time I've ever put the slide up that somebody is like taking a picture of me so yes
so the question is if Co is statically built by default build static binaries but you thought why would you think about this an answer is it's almost always statically built by default but in there's a the one I remember is on Linux if you're building on a Linux box and deploying to a Linux box I think if I recall correctly it'll call get host by name or get address info I think and not just make a UDP socket and roll its own packets we're also need apiece up a few things like that here and there and that might be cool and maybe you don't want that so I find it's a little easier that I just I don't have to worry
because Lib seed like your G Lib C likes to change get address info like subtly any other questions yes I so most that I'd say most of the time when we go to a client site we're not my company does network stuff right so mostly we're worried about what network defenses are gonna catch us and we tell them hey dudes like feel free to disable your AV or whatever and they kind of like snicker at us like yeah okay buddy we're gonna disable AV with some random stuff on our computer and then um we should spur stuff and github and we pulled it down from github and it works and we're like hey by the way this is malware in
the old old that's not malware cuz you wrote it it's like um we've got a shell so that's my experience if I forgot to repeat the question I'm sorry the question was how much does a B catch this kind of stuff and generally if you roll your own whatever language if you're rolling your own nobody's going to notice so I've asked a couple and I've got a the question was does using go prove any present any real challenge to reversers and I'm not one so I can't really speak hugely definitively on that like Carson was like yeah and then they catch your stuff just write more I'm on though just write more side of it but
I've asked that to a couple dudes and I've got a couple different answers one guy was like oh man I hate it when I get go because it's such a weird format and all the strings are funny and then another dude is like dude I love go they have debugging information everywhere so I don't know any other questions yes no question was have I ever seen sophisticated malware and go and the answer is I've not there's some open source frameworks that are pretty slick out there the malware that again not being on the defensive Reversi side of it I don't see a lot of my timão aware but there's no reason you wouldn't catch it but if it's actually really
sophisticated probably not getting kind so there's no reason you couldn't write it for sure the things that I've just fiddling around honey pots or I mean not great but you know haven't reverse them so sorry Red Team right in the back there so the question was since go brings everything and builds a massive binary have I run into any issues with binary size being a problem paraphrase yeah I've not been in that situation no I've I've not yet found a toaster to to implant but I back when I was fiddling with routers Soho routers it would have been a problem if I were putting go things on there some of them really only have a couple negative memory to fiddle
with and memory and RAM disk ish yes we're like four five Meg six Meg if you put a lot of cool stuff in there seven eight ten Meg if you're if like the worm if you're building another binary into your binary they get you know six make plus six Meg and yeah it's they actually get kind of sizable so but nowadays I mean it's not that usually big an issue yeah so any other questions all right well thank you for coming to our talk hopefully it's useful for you [Applause]