Endpoint to Internet: Security Control Validation Using Threat Behavior Emulation
Speakers
About this talk
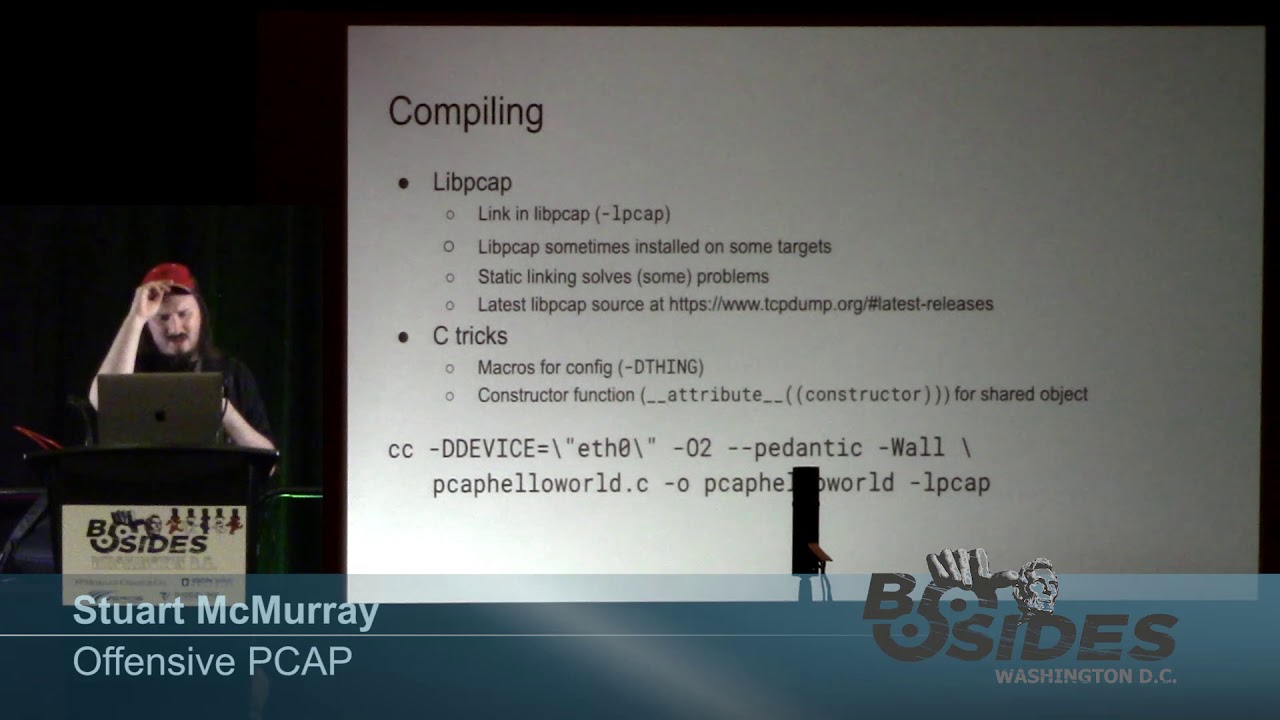
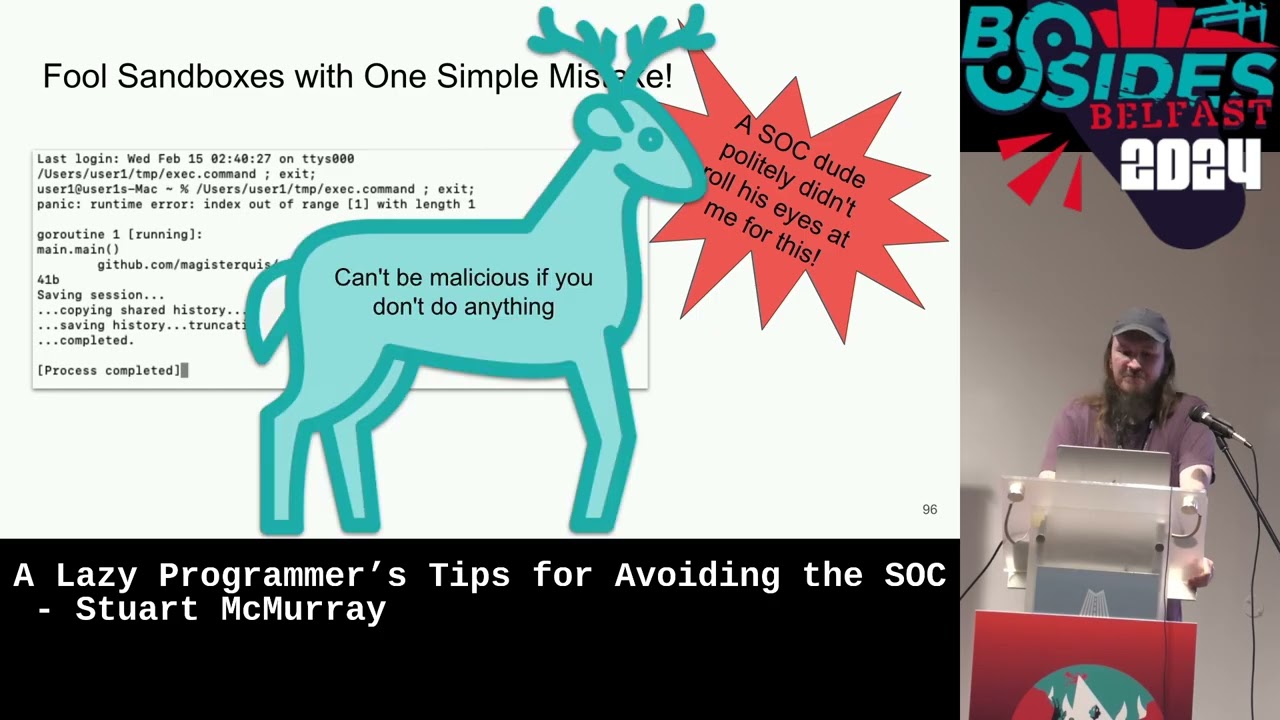
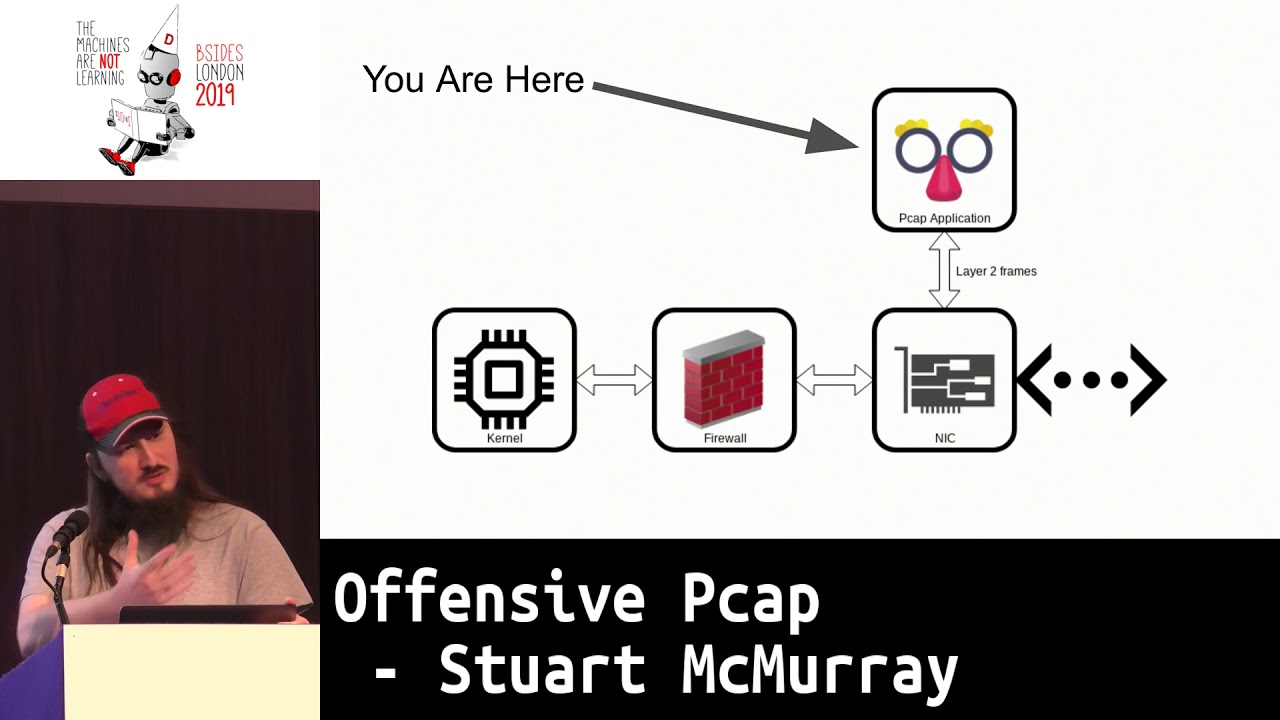
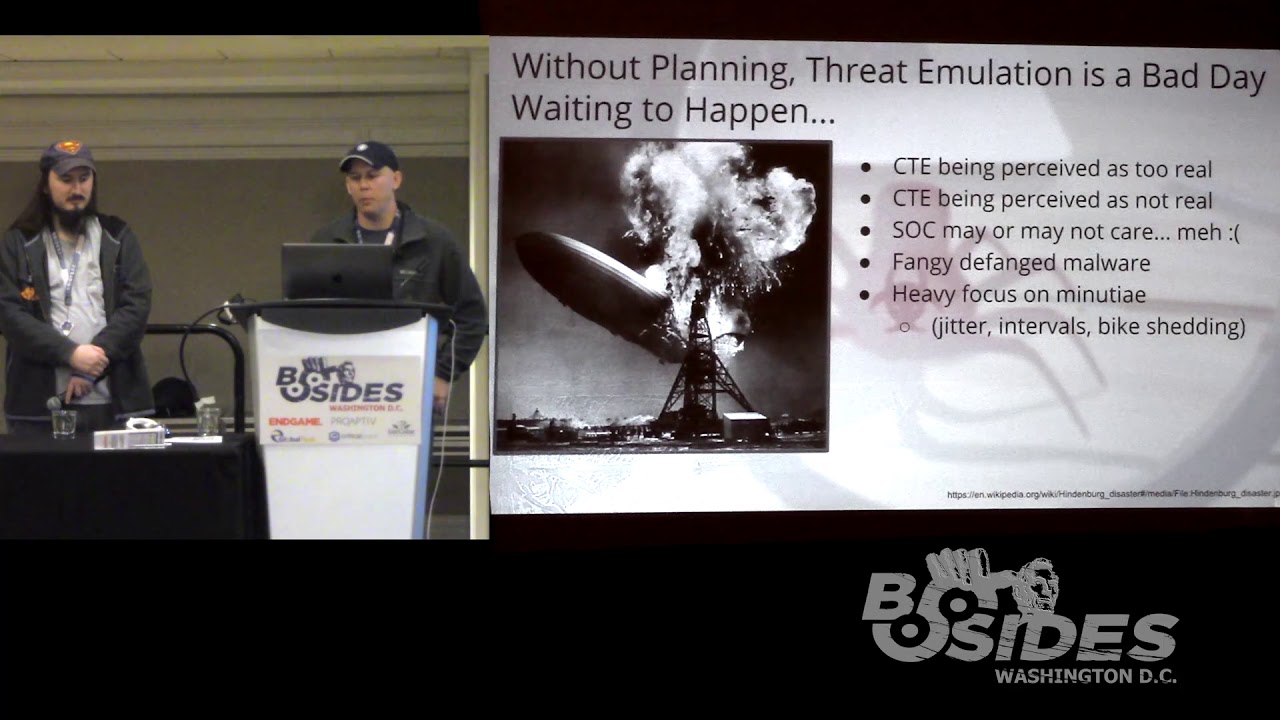
In our networks we employ many layers of security controls, but networks are extremely complex and evolving systems. How we think these controls function and how they actually function in practice can vary dramatically. A simple incorrect assumption, such as the type of traffic passing a network sensor might negate an intrusion detection system, or a minor configuration or operational change could negate the effectiveness of a previously vetted control and open up vulnerabilities thought to be covered. Threat emulation using malicious traffic generation can assist both with validating the entire defense-in-depth posture from endpoint to the internet using safe, low-cost, low-complexity tools and also serves as a complement to penetration testing and red teaming engagements. In this talk we provide lessons learned from building malware emulation tools and running threat emulation engagements across multiple sectors including Finance, Energy, Government, and Healthcare. We’ll cover how to generate emulations so they safely exhibit desired malicious behaviors based on known threat actors, how to plan and execute threat emulation engagements, what pitfalls to avoid when conducting threat emulation, and how to maximize effectiveness and confidence that security controls are working as intended. Ken Jenkins (Red Team Director at IronNet Cybersecurity) Ken leads IronNet’s Red Team Operations and is responsible for penetration testing, vulnerability assessments and red team engagements. Ken specializes in incident response, red teaming, networking, and systems engineering as well as host and network forensics. Prior to joining IronNet, Ken served as an Army Warrant Officer responsible for the defense of DoD information systems. Some of Ken’s previous assignments include tours in Afghanistan, the Army’s Criminal Investigations Command, United States Cyber Command, the National Security Agency and numerous combat units spanning 20 years of military service. Ken holds a BS in Technical Management from DeVry University and is preparing for the GIAC Security Expert (GSE) lab later this year. Ken currently holds numerous security certifications including: OSCP, CISSP, GPEN, GCIA, GSEC, and GCIH, among numerous others. Stuart McMurray (Red Team Operator / Developer at IronNet Cybersecurity) Stuart is responsible for conducting penetration testing and red teaming, as well as creating and maintaining Red Team infrastructure. His offensive focus and experience is in Unix-like operating systems, from which he draws development inspiration. Additionally, Stuart is responsible for assessing the security of the IronNet software suite. Prior to joining IronNet, Stuart was on the Red Team of a Fortune 50 financial institution where he delivered internal training, created and maintained Red Team infrastructure, and performed operations. Stuart served in the US Navy for 4 years, where he provided cryptologic support to deployed Naval assets, conducted offensive cyber operations in support of national intelligence priorities, and performed training in cyber-domain subject areas. Stuart holds a BS in Computer Science from The Catholic University of America. He currently holds the GXPN and OSCP certifications.