Offensive PCAP

Show transcript [en]
yep hear me you can't hear me how about now can you hear me now
hello Bea says CC that's that's good energy for an end of this Sunday kind of talk so all right well here's Stuart he says he doesn't have a cool hacker name so I just have to introduce him is Stuart so Stuart take it away thank you no I mean I'm a dorky a grenade I've been told by my wife today's hi I'm Stuart McMurray thanks for coming to the talk on a Sunday afternoon this is actually usually after hangover time so I think we're probably good there I'm a red teamer dire net all right let's try this again hi I'm Stuart I'm not carrying the plague as it turns out I'm red teamer and iron net sort of doing
UNIX and network e things Twitter get on panels that's a Twitter QR code what you really want to do is point your phone at a QR code that a hacker puts in front of you worth mentioning I'm not affiliated with map use meetup Wireshark or really anybody who's great tools we're gonna be using for this talk real quick come the guys in the back here me Mike is maybe up button
I'm gonna shout so we're the mystery man cuz they're uh I've done that about six times thought about that alright can you hear me the back now awesome thank you mister AV dude alright um so now but we can hear me we get to the important bit that the views my company would like me to tell you that the views in this talk are not my company's use also when you're doing networking sniffing an injection and whatnot it's um you can you can do some things that maybe you shouldn't do without telling somebody so consult consult the appropriate authorities and don't don't just start watching a network without or shoving things onto a network without asking so before we get
into this what is lib pcap it's it's what underlies there we go so it's what underlies nmap Wireshark bits and map Wireshark TCP dump so on and so forth it really is just an API a nice nice abstraction layer over layer two sniffing an injection the genesis of it was in the 80s if Lawrence Livermore and they were like here we have some bugs and just ARPANET at that point we have some bugs in our network stack we don't really have a great way to watch it like you can you can hook up a debugger to code but it's not really so much on the network stack so I call right well I'll just write an API and nowadays what it
does is it attracts away the low-level interface to your network card low-level programmer interface to your network card to a nice little platform independent interface use packet sockets on the in Linux these BPF devices in the UNIX world and the bsd world on the windows world he uses n disks it's a little wonky on windows it supports like 100 odd platforms it's really cool it's a c library just about every language i looked at has some sort of foreign function interface for it to varying degrees of ease of use I mean if you're you know further reading TCP dump and map github Google's go packet library is quite nice in the go world escapees is really cool
it it just gives you a Python interface to almost all things network so it's really easy to just test things proof of concept things so what we have all right we have our power strip miked so what we have graphically is we have our application it's my pointer cool so we have our application sitting there and it's attached to the NIC notice the firewall is here so we have is comms come in over here our pcap application gets notionally now in real life it's not actually exactly like this but notionally you get frames some of the NIC and you can do whatever else an application land and then then you know hands is the current fire on
the firewall so it's it's you outside the firewall it's almost like NIC level access to the network which comes with some ups and downs all right so why why would we want to do this what are the ups well in the c2 side of things and the Red Team side of things HTTP is is well known it's really easy to use there's libraries everywhere for it unfortunately defenders know it very well it's very easy for them to look at there's libraries everywhere for it so it's you know it'll work most of the time especially if you domain front out it'll you know you'll probably win but every so often it's like somebody is looking really hard at that I'm speaking
of domain fronting that actually works really good just about everywhere except when the provider like turns off your thing I was it was a Friday was giving some demo to the some math nerds using Google's DNS domain fronted to YouTube the Monday was like at a client-side dudes I got this great demo hey let me show you and it would not work I was like yeah DNS over YouTube so um you know it's roll your own works quite well you could use DNS tunneling 4c2 it's quite nice and slow um sometimes it gets caught pretty easily if you want to go fast so you know maybe just roll your own on the sniffing side of things you
know the not the injection see to making coms there's a lot that happens on the wire if you just sit and watch the wires just TCP dump on a box you pop there's like all sorts of good things there it's not a box wants to like hey I wonder what's on here I found LDAP just kind of normal on a linux box and I found an LDAP was using hashes like just sending hashes in the clear which is not great but kind of how this hashes weird s and I'm like hey I'll just wrap TCP dump and grab some ashes so worked pretty good there and you can you can just kind of make your own little bespoke adder cap
or better cap or Cain and Abel or whatever without the fuss or the signatures that that brings and and on the sniffing side we'll see you in several slides later it'll give you some coms that you can you can do coms but without actual network sockets issue the packet socket also if I've just you know fiddled around with we'll just say send out packets but with a source that's not the box that fenders like hey where'd that come from I don't know sorry you can you could just totally roll your own protocol pretty easily and the fenders like hey I px that doesn't exist anymore kneeling right more more importantly none of this shows up in
netstat so host base defenses are like easy that's cool one of those talks this morning alright so that's me right there right now how do we use this man pages are your best friend tcp nubs man pages are actually really good they're really helpful the OpenBSD man pages for pcap actually are quite well cousin time are quite well done failing that just a quick google search so using using the library going going stepping through the api at sea right so that's like six function calls later and you're like hector done that one line and go but six function calls later first thing we do is we attach to interface we say i want to sniff on this
interface or i want to inject through this interface pcap open live is one way to do that see the other one in a second you give it the source interface you give it how many bytes you want to grab off the wire at once promiscuous mode was cool back when adapters were like hey i don't care about this packet so I won't tell the colonel nowadays we don't really do that so much anymore giving an error buffer handle errors by the way as I go through the API calls I'm just going to skip mostly over the how you do them the examples slides are on Twitter so if you would like to go back the
great reference it's about what that looks like the other way besides from attaching to a device the more modern ways using pcap create see create your pcap handle tell it what what to attach to set some options you can set the promiscuous mode or if we're gonna turn on RF monitor mode for our crack ish things switch on activate it looks like this in you know more or less in real life so we're gonna attach TM 0 and set the snap shop length 250 bytes so maybe we don't care about the rest of the packet and turn it on activate it alright one of the nice things that pcap gives us or the underlying subsystems
could give us and then P captures wraps it nicely is it's actually a virtual machine believe it oh that's like a bytecode interpreter that bytecode will determine whether or not the practice processed so sort of a fail early you know return early so you don't have to process everything reduces your processor load which means that your malware is less likely to get caught you just send it in as a string and it's the same BPI filter we give to Wireshark or TCP um you know a TCP port 80 and source address whatever source whatever so you set it on the pcap device compile it set it as a filter and then free the memory C being not garbage
collected what it looks like so compile it let's look at TCP port 80 you get layer two frames when you TCP dump or excuse me when you lit pcap you later two frames so one of the things you have to do is figure out the layer two sides you almost never care about that you might but you almost never do and also you're not really guaranteed to get Ethernet it turns out that if you're dumping on loopback you'll get a different sized layer or two header if you're dumping on the any virtual pseudo interface you'll get a strange layer 2 header so pcap datalink pick up datalink valda name and description will give you a nice way to
get that looks about like that okay so now we've we've done the legwork the boilerplate so to speak we've attached to our interface this is the interesting bit so we'll loop over it so we give a callback function that's where our application stuff actually ends up and looks like that so you're taking a a user because it's C just like hey give me the memory I need and it'll give you the packet header as well as the packet bytes itself starting with layer two so you write that and you start looping handle packets as they come in looks like this the return errors are a little weird but it works quite nicely in real life and then a handler looks
something like this so we'll look at the maybe we'll get the lengths of bytes on the wire or excuse me the length yeah I think the bytes on the wire length we've captured they're not always the same so you might get a truncated packet heads-up for that last thing we look at pcap inject to send packets onto the wire um this is how you make your strange protocols or this is how you're like hey here's a packet from brass that doesn't exist hope you don't mind it's really simply you you give it some memory and the pcap handle you've created and it puts it on the wire so you're responsible for all all things layer 2 and layer 3 and it just goes so
it's it's pretty unforgiving if you do the wrong thing you can you can hope to network so don't do that a couple other handy things when you're writing this pcap look up dev will give you a capture interface if you don't know what the earn pickup final tabs will give you the capture interface on the UNIX world it's easy it's easy row or a.m. zero or something in Windows the interface names are very long and they have friendly names like Ethernet adapter Pro 110 gigabit or they have like GUI gooood I guess in the windows world they have uu IDs on them so those and you can give especially find I'll find all tabs you can give your user
like just a select one of these adapters being layer 2 and layer 3 is up to you packet checksum packet checksum calculates nice little library it'll calculate your tcp UDP and ICMP checksum so you just like say hey here's my packet go and it'll add the check sums in there scape he's worth mentioning again it's a library that takes care of just about all this for you so a few proof-of-concept dings right a dude is like hey can you like actually really send data out with ICMP and I'm like yeah so escaping when your past is processing packets that you get when you pcap loop and your handler function um instead of having to calculate offsets
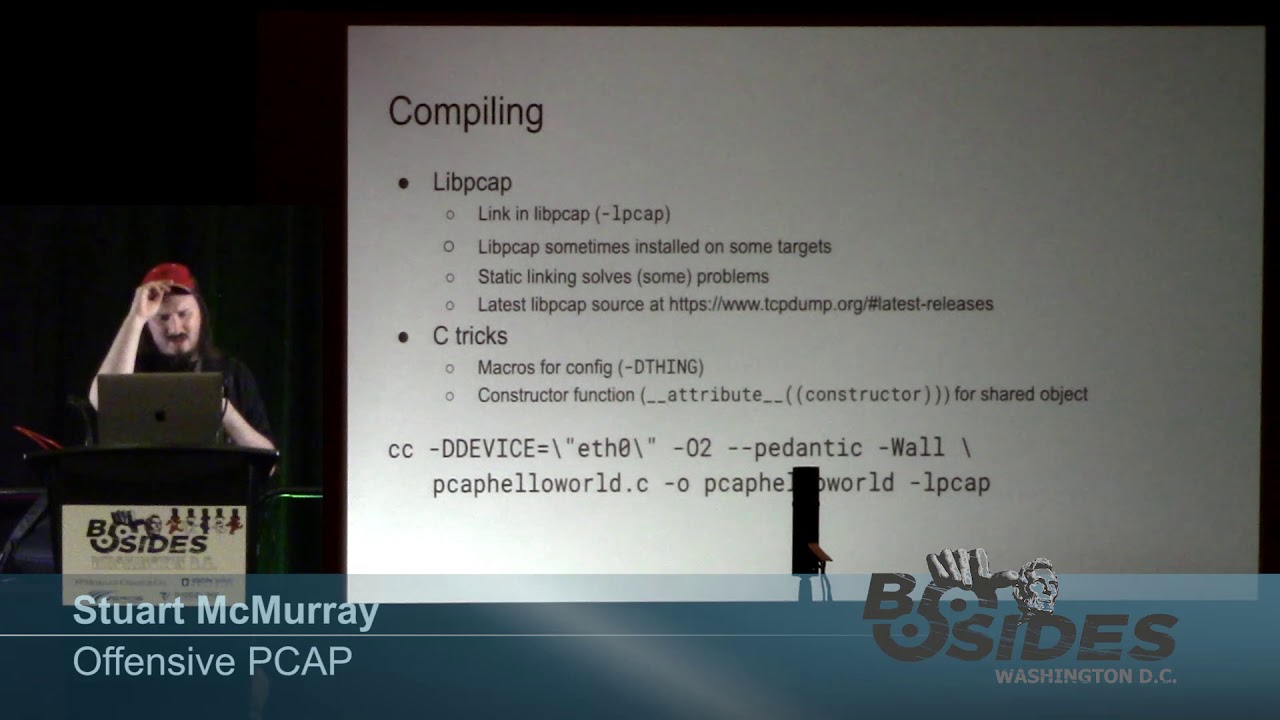
to the various header bits for your manually most unix systems and I think the pcap library and windows gives you a whole bunch of structs that you can just point memory to is like hey destructor starts here and that's where your offsets are so it's really easy just to grab like take struct IP and this the IP checksum or something to grab it out of there alright so notionally we've written some code how do we actually use it compiling it in is pretty simple just Lincoln lib pcap like you'd link in any other library it's al pcap i'm assuming your import paths in whatever are set up on debian systems Debian based systems you know apt-get P captive or Lippe up
to EV or whatever um sometimes installed in the target world as well so when you put a thing on target it's good to say hey is this you know is this P cap actually on here just attica li link it solves those problems statically link P cap and your binding it's just a library that wraps an AP the system call so P cap sources are a TCP dump org latest releases it's not a bad idea to grab the latest one so that you know that your pcap enabled application malware is using the version of the library you expect a couple tricks and see that I've come up with compile time config just use macros for that D thing D something D interface
d device is a great way to set a device if you know what's on target but you don't want to have to do some sort of like config file or like just guess at the right interface and it's also really handy to use a constructor function if you're shoving a shared object having shared object in a memory constructor function is a great way just fork a couple three respond a couple threads and it will will save you a lot of pain all right so now we've built it notionally it's a couple ways we can run it standalone binary if we're gonna run it as a program as a process you typically need root on Linux you need
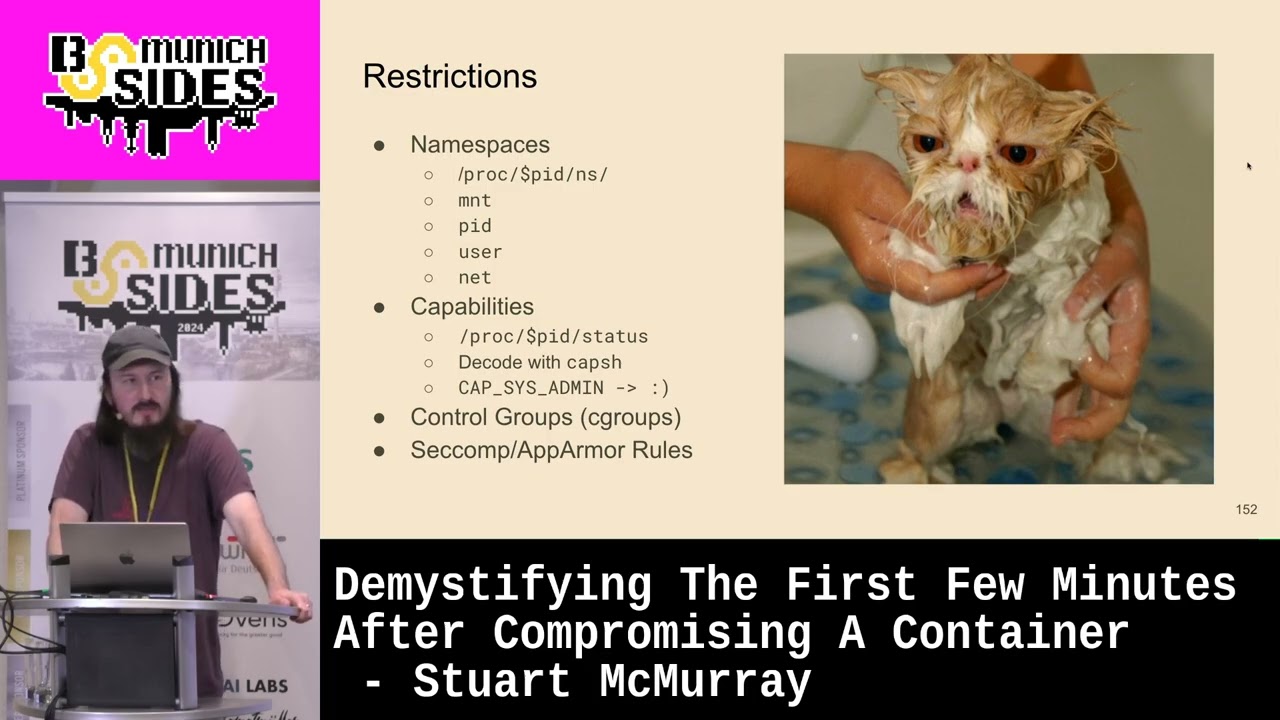
cap net raw on Windows depending on how the libraries installed mini rocks with n just you might need administrator you might not it's good idea to drop privileges especially if you're taking a peak app or a bps filter from a user because compiled bytecode is always a great place to find exploits and when you put it on target it's not a bad idea if it's a Linux UNIX target to run ldd on it and so you see if the libraries are actually there if it's not it'll say hey library missing or library wrong version or whatever else and you build it statically or bring your own needs LD preload for that if you're using it as
an injectable library if you're shoving it into something whatever process is running needs access to whatever underlying mechanism pcap used for that target so if it's a if it's a Linux box you need that process to be able to make a packet socket which is not Universal pretty much anything that starts on boot will cron system D system D is interesting to inject into but that works containers get kind of funny because of how they interact with interfaces so make sure you're not preferably not in a container environment or maybe you're just sniffing that's fine too I found out when doing this if I either your pre thread create or just fork and fork it
solves a lot of problems still pretty hard to see if you inject into syslog and you have another syslog process it was really gonna notice or if you have another thread I'm just really gonna notice if you're just like taking over a process it gets kind of funny if you're using LD I so preload to inject and you're doing something like catching a trigger pack ad or you're sniffing something it just like sniffing the wire turns out that loads into every process so like 600 callbacks later you're like oh hey maybe I should not do that I'm LD preload can get you around that nicely alright so we'll have a quick demo we'll just send hello world as a
layer 3 payload so like instead of IP we'll just have hello world and we'll send it to the broadcast in your face what we'll do is we'll use a preprocessor macro to select the interface we're going to use so we're not gonna have any runtime selecting it and this will all work in as a constructor function so we inject it the constructor function spawns a thread I think as I recall but there's no main function so it it's a little weird like that there's a source for the little demo it's also online as an ASCII cast and it looks like this so hope you kept down unpack it compile it um this is unfortunately what happens when you
build a peak app I found that just about every one of these I've looked into has been okay but it's um it's not necessarily what you're hoping for so we'll build on the source save it as pickup hello world and this is what it looks like so what we're gonna put on top of our Ethernet frame hello world we will hey go back we've defined device with the macro soar in pause some time and then this is how you roll a frame so we'll just you know make a buffer pretty large there you go here we go we make a buffer um it's just enough size for an Ethernet header and our hello hello it says
define macro sure we'll cast that or we'll point that at a nice truck ether header so we don't have to figure out where to put in the the source and Mac desk MAC address and so we do that I'm just like that it's pretty easy we'll we'll set the ethertype to chaos just in case somebody has a list machine running around and copy copy in the hello so open a device pcap open live just like that that's 8 0 I think send it out with pcap inject and that's that's it notice that was in in it or in a constructor function main just returns so that way it's a nice little trick so you can use
the same code as an injectable library and as a standalone binary there you go so we build it builds nicely it's there it's a shared object so we built it with no write very shared object anyways it's dynamically linked so we have to make sure that Lipsy and whatever else are on target but we linked in statically pcap right there so it's a nifty way to not have to deal with entire static linking but you get your your library in there alternatively we can build it old-school way as a library there we go but still the pcap is there even though it's a shared object file just nifty way and we'll TCP dump in the background so
we'll look for anything not IP because chaos or ipv6 and we'll put that in the background because tabs are hard with s kinema we're not a little thing there we go and we see that TCP dump says yes there is some strange ether type we have a hello world out and that's injection in a network it's really quite simple show it into a library as well notice it it goes into the library it works but because we said it as a constructor function not in main works quite nicely downside of course is its you know little easy to find if you're digging through memory maps so there we go well close the close that and it's like a
never happened cool demo okay so that that's cool too the neat little demo you can put a little words worlds on the wire you can make your blue team wonder what on earth you're up to I'm just couple of like actual useful things you can do with it so number one sniff the wire I mentioned when I was I found that UNIX box is LDAP by the way I had like 16,000 different sets of creds off of that it was awesome which also meant the blue team when I was using them I was like eh you would have put it just try them all was like what are you doing dude but anyways we'll just if the wire and
and nowadays most things use encryption they say turns out they don't actually turns out banks really like FTP to send transactions like batch transactions between each other I'm not SFTP not FTPS like just FTP FTP so if you're on a box where you can see this you either on an end point you can see the end point coms and that's your FTP or something like it or you just found yourself on a router that's running sub friendly version of an OS that you can shove code in to see what you find so we'll have a very contrived scenario here I want two things we're gonna do is we're going to narrowly filter one of those days we're going to narrowly
filter just to look for push packets so no sins no UDP nothing like that and that just keeps the resource consumption low especially if you're on some small routing device you don't really want to do that tools that do this already TCP dump and D sniff are very old same with T shark very old I mean they you know you can wrap it pretty simply to do most of this sometimes you want your own bespoke code we'll use this tool called telnet watcher it's online there's the source and just it watches the network actually I wrote it when I had to tell him how many pot going it was ok I wonder what these dudes are actually doing so I'll
just watch telnet TCP dump will work in a pinch it's written for OpenBSD you can compile it for other things fairly easily but I've learned not to put malware straight use ibly on the internet because turns out it gets used SSH worms are really popular by the way just let you know so our little cookie scenario here we've laid it on a host it's FTP matched financial transactions off and we've got root it looks a bit like this so we're some some transaction transfer box running an FTP D and we are lepak stores we're on this box and there's some bank and ssh coms going be around there there we go so we're on target is root we'll just start this
thing you can get whatever options in in real life you probably want most of these to either be good defaults or baked in at compile time but we'll watch port 21 we'll watch the interface vio 0 if we were making a be PF filter that's what it would look like we're not obviously Surigao and we see somebody's already starting to come in so we see banker Joe and his neat password so that's already a win we've got a transaction we've seen him batching some transactions that's cool so that's that's neat we can also do something like this so we take we just happen to find that an ID RSA key we found it mount root so probably somebody doing
something funny with NFS and we'll just exfil that we use a watcher to catch it doing this notionally on another box there we go we've wrapped it with a bunch of XS so we can group it out pretty easily and now we have his SSH key ok that worked so a little bit better grepping and we got a message he just just by watching the password line we've had to have been on the other server to do that of course that was cool another thing you can do is socket list coms so if you do not for whatever reason want a socket there there is a socket of course there's the the packet socket which you can see in SS if you
really ask for it and that's not on the other hand you can't so I was at University of Wilmington helping their CCDC team I think we have Wilmington dudes there we go yes I was helping their CCDC team and they were like they figured out if they run netstat peanut constantly they'll see anything with a network connection and the box the target had like SSH and FTP or SSH and something is like not a rat basically like hey if it's not SSH and whatever that thing was kill it I was like well okay so I need no socket with network comes that that works SOTA came up with the idea was just I would use pcap to sniff the network and
if I got a packet that looked interesting I would use it so it's cool umberto tool called pcap NOC it's on the internet their source literally does just sniff the wire and look for something interesting it'll look for something that says command my command to run in the word command or call back and address to call back to in the call back it's nice and injectable runs standalone it's cross-platform um it's not weapons-grade I was talking to fellow yesterday he's like hey man this to of yours is really great except when I try to inject it into system D and then it crashes the box I'm like it's not weapons-grade but cool so we're gonna we're gonna say we already have
the log server run compromise we've got root and we're going to try and get a call back based on what we can send the transaction transfer box so we're us we're gonna try and log into this box in such a way that the syslog D server will call us back so there's vio zero so we're at on dot 42 and we'll ssh to dot 43 with this address with this username call me back to dock at 42 port 4 4 4 4 and a bunch of things up here to just make less noise and we got a connection dot 44 which is not 43 which recess is H 2 and not 42 so that's that log server
this was the log log entry by the way we can see yet we're on there we're on there's route this is our little shell cane it is something that nobody's ever going to kill just in case and it's it's just shoved in his lip PK so you shove something in there using pcap shoved into its system d by the way too in it showed in doing it nobody'll notice there we go that's how we did it that's the LDS in a preload so and this is what it actually looked like on the wire there was a syslog message that said in Valerie user a callback that says log messages on the wire so pcap picked it
up and used that to figure out what address to call back to another thing you can do bypass the firewall so I was fiddling around with this and I realized that pcap sits outside of the firewall on linux unix so if I use pcap to grab something I can skip over the firewall and inject something into the network stack with the tap device I'll also work for the time device you would just want to go for layer three cobalt strike does something pretty similar with its it does a forget the VPN thing SSH will do this also for you just a little more complicated obvious if you actually want to weaponize this it's a pretty good
first Lippe cap project it's fairly simple so we'll have is the kernel talking receiving other network talking via lippy cap just some using lan process which will shove data into the kernel over tap zero this also works OpenBSD it's pretty trivial to port to anything else but not much like random people grabbing stuff fro from beastie off the internet so our scenario the same boxes we've been on ftp isn't working anymore for access we've got a credible you since ssh but we still wanted like open up that ftp again by the way you end up doing you end up doing a lot of filtering fiddling with BPF filters and if config when you do this so this is what it looks like we
have the network out here it'll send down it to the NIC normally the firewall will drop it and say no this isn't something we want you know we don't want FTP anymore but the NIC sends to the process bypassed fw the tcp dump Limpy kept using process which will send it then into its virtual NIC into a kernel so it's I'm just a 50 way to hop around a firewall looks like this so FTP no longer works for us we can't we can't grab it see password we can still SSH in though so we'll do banker drill will let us in same transaction transfer box and we see that sure enough we have a block
drop in a default block and just a pin hole punched for 22 that's a problem for us so what we'll do we'll just put bypass fw on the box because we can SSH in get back the box need to know the MAC address so this is a 6 4 FC is the MAC address for this the interface that we're going to mooch from and bypass hop over the firewall with there we go so we've make a tap device and we'll give it the same MAC address because the kernel expects things coming from the interface with the MAC address if you're gonna give it to it with the MAC address sure there we go they look pretty similar different IP
address but pretty similar and we'll run it and say anything coming in to any any art packet we'd like anything coming in to 1.2 54 so we've sort of functionally now have tapped 0 on the network with the address 254 also another good address cause people like it's probably something the network dudes using we'll just ignore that and now we try 254 and sure enough it works we get it C password down and hopped over firewall just easily with that last last demo is EDR D thing where I was writing these like hey these are all great they all work on UNIX most of them work on Linux which is what you'll find everywhere I
was like what about Windows what if what if I try to write pcap code for Windows and the answer is don't do that it's not a kind thing to do so but I was like what does Windows give me that's kind of neat and needed hacker ation turns out they have a nice API to drop a TCP state from the state table so you can say yeah I know we're doing TCP comes just forget about it not like send a reset not send a fin it just like it doesn't exist anymore so I was like hey if I catch ass into something I don't want somebody talking to I can tell windows to ignore it because it'll make a state I'm just
like hey no nevermind we're not doing that it's like well what what is worth dropping and edr is worth dropping so EDR usually nowadays has to call it to some see to management's use me server that's these things it's like yeah I can get a shell on your box dude admin stuff and I can transfer files and like the test is aged it's a rat what are you doing dudes but anyway so we'll catch us in and as soon as we see it from some defined range that we know the EDR uses or the other way around like we only want this box as the bad guys to be able to talk to us you make your users kind
of mad like don't do this if you don't have to but it works so we get a syn a drop a syn ACK the box is like hey I'd have no record of this connection and a reset TCP kill is pretty similar except it forges a bunch of resets because back back then windows or excuse me Linux did not have a an API for this so we're gonna watch pockets matching the filter a BPF filter set TCP entry the only thing set TCP entry does in typical Windows fashion is it drops TCP entries service for Windows if you're reading my Windows code I I would like to apologize for the lack of Windows II things I use I use functions like open
and printf this is probably something you want to incorporate is another tool you probably don't want to write yeah just a standalone tool but it works so in this in this scenario well pretend we found a Windows box after hours we 'print really know where the management servers are but what we want to do is just wipe the box sort of a corny sony ish thing source for the EGR sniper the pcap is tool and the source of the wiper wiper is actually like don't put it somewhere you don't expect to wipe but it's a nifty little way to say hey you're like super late a guy ml AV that detects things before they run doesn't
one thing to note about Windows though is pcaps it's inside the firewall so you have the NIC and it sends data first it gets firewalled and then through end this the the driver layer it'll go to your pcap process so it's not it's not quite as nice and friendly you can't do it do so many crazy things on Windows but that's what you got so there is no s Kinema for this just some screenshots this is what you know I started wiping started deleting things I understand that you should not be deleting all these things on Windows I've been told in the seven address here is gents in the back can you see that gentleman
ladies in the back is that new is gonna be interesting
hey I didn't work well that's cool I apologize to the people in the back you have to take my word for it that this address is and I grade it out but it's the address of the servers for whatever I just googled like best free malware fs4 anti-malware 2019 or something put it on the box and that that was in fact their address and it it's trying to get out meanwhile we're losing loads and loads of data I've also been told that things in C Windows you shouldn't really remove from a Windows box and I tried and and the AV was like hey hey C to server or AV server can I can I let this happen
and the server didn't say anything so sure why not I'm also told that like C windows system died and I is not something you're supposed to remove the windows site up like it worked and then and then Microsoft like Windows itself started calling out to Microsoft addresses and I was like maybe we don't do that so that happened all right so it's summer if you're gonna if you're gonna use pcap and I recommend it and it's a neat thing to learn just how networking and how things work under the hood with a little bit of abstraction layer you got to attach to a device so either a pcap open live or pcap create set and activate it's
usually good to set up bps filter you don't necessarily have to but if you're gonna do it compile the filter set the filter and free the memory depending on what you're doing it's usually good to grab the data link type and then sniffing inject off you go um I'm not going to read this but it's good reference for how you can compile it likewise reference for how you would have confute it a couple ideas so it's like hey what but you know if I if I had an intern what would I say hey intern here's a cool thing to learn pcap so a VPN device like we showed in the couple demos ago take your favorite rat a ter
sniper and it doesn't it's not necessarily a C specific thing so if you're using one of the Nifty go frameworks nowadays add it in there weaponize pcap noch maybe add some encryption add some authentication add some replay protection a port scan would be kind of cool an injectable port scanner may be using a different source address so that you have you know you own another box and that's where you're getting the syntax or something like that we kind of cool to get your shell output or exfil or whatever over send packets or ICMP or whatnot alright so thank you for coming any questions that by the way is another legit QR code is that a hand or is that a nope that was a
scratching of a neck all right well no questions thanks for coming [Applause]