Lessons Learned From The Verizon Data Breach Investigation Report

Show original YouTube description
Show transcript [en]
thank you thank you for the interaction and thank you all for joining me today really appreciate it thank you very much the organizers as well it's a pleasure to be here I've never been to Luxembourg before and absolutely loved it so far so thank you today we'll be talking about the Verizon data breach investigation report here's a brief agenda for the day or the next 45 minutes at least first we'll talk about briefly what the VD BIR is I'll call it the full name VD BIR the report kind of all of those interchangeably let's talk about some of the top trends that are focused on in the report hot industries this is all things that are these are all things
that Verizon defines then I'm going to talk about some defensive techniques and we'll open it up for some discussion afterwards so what is the VG Br this is the 11th year of the report just a quick note it's the 2018 report and so that's focusing on 2017 s data I like to think of it as kind of a pseudo-random meta threat intelligence report the pseudo-random nature of it is defining where the data comes from there are three main repositories that Verizon calls the biggest one and the one that has the most confidence in terms of the rice and reporters when they're creating the report is from their own third-party investigations so this isn't to say
Verizon's breached every single year that's kind of a misnomer I think sometimes when the report comes out Verizon has an enterprise security team that does Incident Response in forensics much like any other kind of mandiant type of functionality if an organization feels like they have an issue they can bring in Verizon and they'll do a triage and investigation so a Verizon uses the various framework Varys is the vocabulary for event reporting and information sharing it's a great framework I've used it in the past and previously in the list positions outside of I've never worked for a Verizon but I didn't even know that they created it until I came across that in the report but it's a great way to classify and
categorize investigations and breaches the second repository of data is investigators that are not part of Verizon's enterprise security teams that submit their data to Verizon already in the various framework so that kind of has ii love of confidence moving one down verizon also has very good relationships with independent researchers in the field that don't use varus at all they'll go and talk to them get kind of a sample of different investigations that they've been working on and Verizon will integrate that into the Bears framework so focusing on the meta nature of the report we're not looking at specific techniques in a single incident throw over 53,000 incidents that Verizon classifies in this report 2,000 of which
turned into actual breaches and the distinction there is that an incident is anything that affects the CIA triad so confidentiality integrity and availability of a system whereas a breach is as I put it data walking out the door so that's the kind of final and Dalby all at RSA I've worked in our Cirque and we talk about incidents versus declared incidents so that's kind of the divide or division between the two threat intelligence is pretty self-explanatory freising produces this report in the hopes that we can all as an industry learn from the incidents that have happened in the past and hopefully prevent them in the future why does this matter why does this report matter
well marketing material I mean that's it's a joke but it is quoted pretty much everywhere and so it's good to understand the actual data because different vendors including my employer will twist the statistics in this report to whatever need they they would like to fill so it's very good to understand the report as the data itself that being said it is a great way to translate some of what's going on in our industry to lay people it's very palatable very easy to read from a non security minded expertise additionally and I think most important to me is that it's very difficult to get kind of impartial data sets of breaches from wide range of different verticals and industries and
so I look to Verizon and mandiant has their m trends report every year as very good sources for this I wish in our industry we had more of those but I think it's hard to monetize them that's probably why doctrines so there are a number of top trends throughout the Verizon data breach investigation report I'm only going to focus on a few of the biggest ones including social engineering ransomware we'll have a discussion discussion of insider versus outsider threats then we'll talk about dwell time and cryptocurrency mining was pretty much completely absent in the Verizon data breach investigation report so we'll have a brief discussion about why that may be the case so social engineering I
think we can all agree that social engineering is a pretty prevalent problem in our industry especially phishing basically at least two-thirds of the incidents in the Verizon did breach investigation report directly come back to fishing and I think you know it's it's pretty common knowledge that it's much easier and oftentimes at least to ask someone to hack a human as opposed to hack an actual system so that's very likely what's causing the spike here using stolen credentials is also the top of a list of data breaches and again that goes back to the fact that if you can you know get your way into someone's head and get passwords and information from them there's no
need to take a technical approach so ransomware everyone's probably familiar with the wanna cry attack if you're not all you need to do is ask any one of those companies and many more it did not go well for them this was probably I know as an industry we have a lot more insight into the attacks but outside of our industry this is probably one of the biggest wake-up calls in recent years which is often good for business for us but it had some pretty damaging effects not only did FedEx crawl to a halt but the National Health Service of England and Scotland were also heavily affected as were some US hospitals so speaking of the data that Verizon presented
regarding ransomware it was the number one Avenue of malware or use of malware across all the data set so represented around 39 percent of attacks again number one this year it rose from four last year and it was all the way down to 22 in 2014 so ransom wares definitely had a pretty fast increase in terms of prevalence we're also seeing more impact to critical systems than ever before so it looks like attackers are becoming a bit more targeted and the ransomware campaigns at least advanced and more sophisticated attackers are doing some recognizance and discovery to determine what an organization's crown jewels are and then infect those specifically oftentimes that enables them to ask for
much higher payout as an organization really you know relies on that data or those systems in order to function Rass as I call it ransomware as a service is also another branch of ransomware that's becoming increasingly more prevalent there's an entire industry being created around ransomware this is more commodity based malware not those targeted attacks that are impacting business critical systems but in these instances it's very easy to access ransomware services and so they traditionally have lower ransoms that are asked of them but with the increase in prevalence comes an increased costs like we've never seen before email again 92% of ransomware was delivered via email so I think it's clear at this point that email isn't a infection
vector is incredibly popular for attack campaigns so now let's move to a discussion of internal versus external threats this graph was pretty surprising when I first saw it I don't know if I was drinking too much of the kool-aid when it comes to marketing but I think we as an industry really overemphasize insider attacks in truth only 27% of attacks are insider the vast majority are external threats there are a couple of reasons I think this could be the case there are definitely some popular examples that we can all think of as insider attacks whether that be Edward Snowden more recently reality winter in the United States there's a lot of damage that can be done by an insider insiders
often have privileged access to our systems but as we spoke about previously in social engineering it's very easy for a an external actor to become an insider through credential reuse and theft something that I found remarkable was 4% of users will click on any link that they're presented with so even if it says like danger danger this is bad this will hack you please click they will click before percent sounds relatively small but that means in a user base of 25 people someone's going to be that individual that always clicks on that link so this goes to a kind of outside of the report but a different mentality of designing systems secure by default I think that's something that we
would really need to focus on in security user training is great awareness is amazing but it's it's not solving the problem let's talk about insider threats for a little bit the vast majority of these are due to error carelessness so that rogue IT administrator really doesn't happen that often it's definitely a scary possibility and and it does happen from time to time but the vast majority of threats that we're seeing are just kind of carelessness I found it particularly interesting that healthcare is the only industry that has more prevalence of insider threats than external and again the vast majority is doing duty or carelessness and we'll talk about that a bit more when I talk
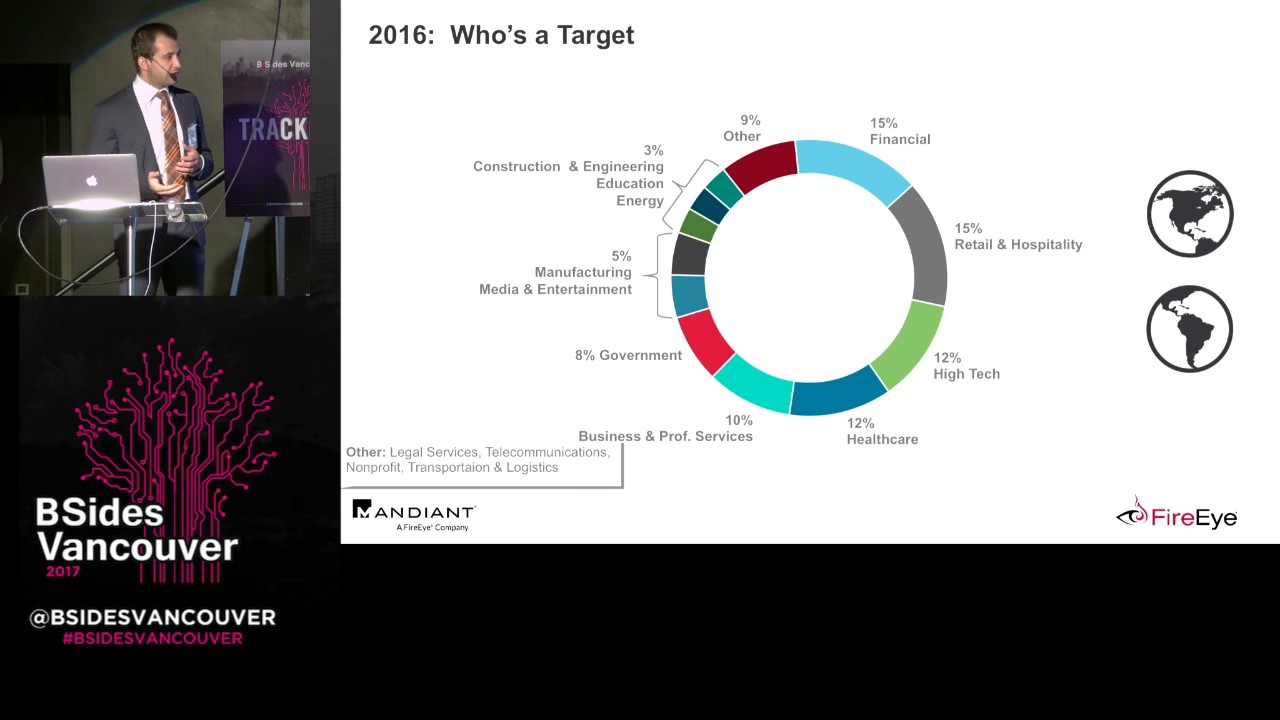
about healthcare is one of the top industries external threats vast majority are financially motivated I was surprised that only 50% were organized crime syndicates I kind of expected that to be a bit higher but the financial motives are rife throughout any sort of attack campaign and so you don't need to be you know an organized crime syndicate like you once did necessarily because you can get a lot of these tools off the internet now with very scripted type of capabilities only 13% of the data set was found incident incidents in the data set were found to be a result of espionage similarly only 12% of the actors in the data set were advanced persistent threats so I think much like
insider threats we focus a lot on our industry on kind of apt apt apt while that does happen and in public administration as I'll talk about later if you work for the government it is a legitimate concern but in private enterprise it's just not seen very much this pretty much matches what I see in the field when I'm doing Incident Response and working on engagements it's very rare that I'll see an incredibly advanced sophisticated adversary really maintaining that the persistence I see a lot of persistent threats through commodity malware but not many advanced persistent threats 12-time this is where we could all do a lot better this is kind of an embarrassing slide for us as an industry because 87% of
breaches happen or compromises rather happened within minutes or seconds whereas only 3% of the discovery happen in a similar amount of time so in over two-thirds of the cases the vast majority it took months if not years for incidences incidents to be discovered an interesting corollary to this is working for RSA no witness I often see enterprises coming to me with a requirement of 90 days of log retention and so I think if we look at that number most people quote about three months as the typical dwell time but had actually challenged that and say that we can only see it for three months because you only have those 90 days of logs it's very
likely that a attacker was inside of your environment for much longer so it's an interesting point I don't know what that says about retention I think instead of focusing on retention we need to focus on visibility and getting out in front of these issues much sooner so cryptocurrency mining cryptocurrency mining was mentioned in the Verizon data breach report all the way 60 pages through the report for the first time in appendix D appendix D was their Year in Review and so it kind of goes through month by month the 2017 just mentioning some of the most notable attacks eight of those twelve months had cryptocurrency mining so Verizon knows that this is the thing it knows this is
an issue that we're facing in the field but it wasn't mentioned at all in any of the top trends really anywhere in the report other than that one appendix so I think something is a bit off here I don't think it's any maliciousness or kind of turning a blind eye what I think really happened and in talking something with some colleagues most of them agreed that takes a little bit for us to react to a threat as sake analysts it then takes even long for our industry analyst to write and report on them so I think it's just a bit of a lag time that we're seeing here my guess is that in the 2019 Verizon
day-trip data breach investigation report cryptocurrency mining is going to be front and center probably not dethroning ransomware but way up there in terms of the top trends looking outside of the report I think it's just logical to see cryptocurrency mining increasing in prevalence not only do you get immediate return on your investment you can siphon out funds much quicker especially at scale but it's also relatively non-destructive if you're doing it right or wrong from a defender standpoint because it can be very easy to fly under the radar if you're doing a low and slow type of campaign you can persist in the environment for months if not years without anyone really noticing that anything is going wrong there's
also an interesting thought that I had when it came to cryptocurrency mining I'd be interested to know if anyone in the crowd has any kind of thoughts towards this but the rise of the crypto currency markets himself in terms of financial gain and my personal experience also kind of correlated to the rise that I saw cryptocurrency mining in the field and so I'm interested to see now that the cryptocurrency markets have kind of dropped off if cryptocurrency mining is no longer as prevalent as it once before something else that has been talked about is that the former actors of ransomware campaigns have pivoted to cryptocurrency mining that's not necessarily what I've seen and not what
my colleagues have seen we still see ransomware pretty prevalent cryptocurrency mining is just now supplementing that so on business-critical systems if you have a very advanced attacker do a ransomware campaign otherwise if you have a whole bunch of hosts cryptocurrency mined in them and do that low and slow gain over time so now let's focus on some hot industries Verizon breaks up the report into I believe 12 different industries but we're just gonna focus on a couple of the most important ones so healthcare healthcare is the only industry where again insider threats are more prevalent than external threats however human error is a major contributor again that element of error and carelessness is incredibly rife within healthcare
I think as an American at least I can't speak for the European health care system which tends to be much better but when I go to the doctor between doctors nurses administrators there are infinite number of systems that they need to touch on a daily basis just to get their work done they're also not necessarily the most technical technologically savvy individuals nor should they necessarily need to be but this is probably what's causing a lot of the error and carelessness here one thing to note with an employee employee abuse though is that around 40 to 50 percent of the insider threats in healthcare are due to employee abuse these are things like if a celebrity was treated at one of your
health care institutions employees are very likely going to go in and try and find information not necessarily to monetize it but just purely out of interest thought that was relatively interesting Chervin in terms of external threats ransomware is huge in health care I don't know if you heard but Atlanta the city of Atlanta and Georgia and New York or Georgia in the United States suffered from a huge ransom or attack it mostly focused on government institutions such as health care police critical infrastructure so you know locking up patient records that it comfort so that an organization can treat patients is a huge concern public administration so this is where apt matters in public administration public
sector over 40% of the breaches were caused by advanced persistent threat actors relatively nation-state actors and so whether it's critical infrastructure such as voting industrial control more and more in the future we're looking at connected cities spies are definitely inside of our infrastructure in America we often focus on the Russians but I would firmly hold the American intelligence apparatus are firmly in a lot of other foreign nations infrastructure so it goes both ways and it's something that we definitely need to keep an eye on if you're in any industry but Public Administration advanced persistent threats again not a big concern this is where you do need to pay attention to them so the financial industry I'm very proud
and that I have a lot of customers that are financial enterprises and they are doing quite well these days they're the only organization over the past three years to show a reduction in incidence and in fact it's a pretty dramatic reduction the current threats these days are mainly physical whether it's ATM card skimming you hear that a lot about at gas stations or Bakke bank ATMs or ATM jackpot Eng Barnaby jacked the famous ATM jack potting at blackhat in 2010 still incredibly current today education education is a interesting industry when it comes to this report because over ten percent of the attacks in education listed fun as the primary motive that kind of gave me like a warm
and fuzzy feeling inside because when I was a student I was definitely doing things I shouldn't be not a malice at all but purely out of interest and curiosity and so we still see that that is ripe and alive in education these days this is also a great graph because it means absolutely nothing to me if anyone in this in this audience can determine a you know sensical trend out of this I would love to hear it the one nugget of gold that I kind of get from this is you can make a lot of trends in our industry as I'll talk about in the defensive techniques section reports such as these can be invaluable to your
organization but they're also certain things that you can't make transitive so if you're a defender in education you're not gonna try and you know focus on cyber espionage as your main attack vector that you're protecting because while that may matter one year it clearly won't matter the next so you need to take a very robust defensive posture when you're in a field like this so now going on to defensive techniques visibility is one of the biggest things that I wish I had more of when I was an analyst in organizations when I talk about visibility I'm not just talking about logs I'm talking about network and endpoint data as well logs are great for getting that kind of knock at the door
kind of a little bit of information about what's going on but it's really the network and packet day that our network and endpoint data that I use in my investigations to do the deep forensic look into what's going on it's impossible to really get the entire scope of the attack campaign surely from logs so this is a great graph that Verizon puts out in the data breach investigation report if there's anything that you see in the report if there's only one thing you see I recommend you take a look at this it's probably very hard to see from here and so let's just take a little look at a subset of that so these are incidents of those four
industries that I talked about previously and this just is going to say that you really need to tailor your defenses not only to your industry but your specific environment so looking at industry specific determine what threats are most prevalent in your industry you can do this using Verizon you can look at you can take these kind of overarching patterns and layer them on top of something like miters attack framework I'm a huge fan of that I understand they're giving a training upstairs I'm pretty jealous that I'm not in that but it's incredibly valuable to do this type of intelligence whether you have a dedicated threat intelligence team in your organization or if you're just layering it on top of some of your
hunting X exercises so for example if you're in public administration you're not gonna try and defend point-of-sale systems that's just not where the attackers are looking right now they mean this in the future you know things like DMV point-of-sale or Department of Motor Vehicle and other sort of institutions that have point-of-sale systems but currently that's not what they're going after far more interested again in that cyber espionage and that I didn't want to say it that will be my one cyber for the talk I promise you that so you also need to maintain a security posture relevant to your own organization and the the kind of capabilities of your organization manual had a great talk
earlier today in the top of the morning talked a lot about process people and technologies it's very much true for this as well if you're a junior organization and you have one intern on your security team you're not going to ask them to hunt all day so if you don't have a sim you shouldn't invest in AI machine learning deep dreaming technologies that aren't really gonna do much for you the last point is I also highly recommend that organizations create a report like this for themselves doesn't need to be anything external not nearly as robust as Verizon does but there are two main things that you can do here the first and probably the most important is
baselining the attacks that you see in your environment this will help you fine-tune graphs like this and you can layer your own data on top of someone like Verizon's additionally it will give you some ammunition to go to your board of directors your executive team and show what you've done oftentimes in security I think we're you know often ignored if we're not heard and so being heard from normally means knocking on someone's door that you don't want to and having an awkward conversation about a breach this is a great way to kind of get ahead of those conversations and show what you're doing and the value that you're bringing to the organization without necessarily need to do that in incident
investigation scenario so multi-factor authentication I had to do a little RSA throw up here but what we're really talking about today is Hardware tokens Google had an amazing report where Krebs had an amazing report on Google that found that since they rolled out Hardware tokens and they do actually use GB keys there they haven't had this was an early 2017 they rolled them out and since then about a couple months ago they haven't had a single incidence of phishing amongst their 85,000 plus employees so that's incredibly impressive and rolling out something like multi multi factor authentication is relatively low overhead and so if you can do that one thing in your organization it's a great way to get out
ahead of the threats that we're seeing finally just going back to basics talking about like sysadmin 101 you don't need to have you know the battle starship from day one you can just start patching and backing up we talked about patching a lot and I know it's not often as easy as it is said patch where you can try to have some political pressure bring awareness to why patching matters and backup is very very easy I've never seen an organization that has much friction when they try and roll out a robust backup plan that's gonna help you very much so with those ransomware campaigns instead of being to you know hoard Bitcoin and have a special bank
account where your company has Bitcoin on reserve just backup every night and if you get hit go back to a clean copy next thing is kind of CISSP 101 permissions so privileged suite permissions of least privilege only give people what they need access to to do on a daily basis review those privileges on a quarterly or at least yearly basis and make sure that people are still accessing the assets that they have access to Netflix has a great program I believe it's freely available on github forget the name of it right now but it will automatically roll way permissions I'm kind of a roving random basis so if someone complains very easily scripts it and turns the permission back on but if
no one notices that they lost their permission they probably shouldn't have had it in the first place so that is the entirety of my presentation any questions at all I do have some discussion topics just spur debate and comments everyone is so opinionated in our industry I can't believe no one has a question or so you are correctly pointing out the importance of patching and allowing for a patch where you can strategy if you if you can't patch everything you know you should patch the Delta there turns out to be really important so energy spent auditing your patching strategies so that you know what isn't patched is actually got a bigger payoff than patching what you can
thank you I think incredibly salient point once you do know what's not patched in your environment by increasing the visibility that you have there and increasing the monitoring that can be almost as good as patching something in the first place so if you have a high valued asset in your environment that you can't patch whether it's critical infrastructure or legacy system at least monitor the heck out of it because that's gonna give you a very high fidelity or return since she's not here to mention it himself Michi occult sec in Slovenia has a very interesting protic called Oh patch I don't know if you've seen it it's basically a micro patch where he patches one single
machine instruction where the vulnerability is so install an agent on a server or workstation he pushes out and a micro patch and the vulnerability is gone until the actual patch can be released or for unpassable things this one is harmless interesting that the project is called a patch and I'll definitely need to look into that thank you it will soon be available also for enterprises with a subscription where you can say for these types of devices and applications I want to be sure that there will be opiates available for this and this and that no that's great I can see a whole bunch of practical application yeah thank you for that anything else did what Verizon saw and reported on
does that make sense so there's the the top threats that you guys are seeing in your enterprises you just give like a yea or nay i I just have a question ho do you use this report and actually do you use the information that you find here in New Delhi job yep I absolutely do use this report I've been using the report since around the fifth version I think in late 2000s when I was a soccer analyst and so I would absolutely look at my industry look at the compromises that are prep and relate that back to the security posture that I was defining so it's a great way to kind of find holes that you
potentially have oftentimes we need to be so reactionary in our jobs that it's very difficult to stand back and take a look at the real landscape what we're essentially facing and so this was a great kind of level setter for me you know it's pretty beefy report but it only takes a you know weekend to turn through maybe once or twice and really get some actionable intelligence from so that was the goal today was just to kind of distill a bit of that to you guys hopefully you can take this back to your enterprise yeah so so I just fell in so I hope this question was not erased what I was thinking and I would like to have
your opinion because I was just like wondering would it make sense and I don't know if any of you ever did that since the horizon data Beach report is now a de facto thing and you've every time it comes out people just jump on it and claim that they read it but usually didn't at least they looked at the fancy charts and whatnot have you for example I don't know maybe you Walter but maybe someone in the in the participants have you guys ever used the things that they list out there all the metrics to measure it in your environment and then compare it what you have as an average there and would this make sense since we're looking at so it
did are probably not the best metrics but at least we have historical representation of I think the most common one is the time to detect thing that usually that's the most like referred one have you guys measuring that because still in a lot of cases in IR teams they're not really looking in that one but they do something stupid like the number of tickets so what would this make sense what do you think yet that that was actually something that I mentioned that was that was kind of a little golden nugget is is I encourage you know all the companies that I work with all my friends that work at companies to develop these reports
internally again don't need to be external at all but I don't know a single company that has taken me up on this that does publish it and they don't certainly need to be as robust it for aizen's but it's a great way to again layer your own data on top of horizons to kind of make it sense a little bit more for you and to baseline your own environment and so compared to what you have in and as an average like are they blow under like what is your experience that they're doing better than the average worse than the average are they even honest doing yeah so to speak to the honesty real quick a friend of mine a couple
years ago took a job with Verizon enterprise security and that was my first question I was like are they actually listening to you guys or is it like a marketing like a Gartner type of thing where they figure out what they want to say and then put some statistics behind it and he said that no the the report writers are heavily embedded with the enterprise security division of Verizon and all of this data comes straight from the investigations that they do so I was very glad to hear that the first part of the question in terms of really making this your own I generally see a little bit of deviation in some of the attack techniques that
are most used but the trends in terms of the you know the top three or five things that certain industries are facing are generally dead-on you know little standard deviation but I've been pretty impressed not only with kind of this year's report but historically how well lay chart some of some of the kind of trends in the industry and there's a really good companion site to the Verizon data breach investigation report that Verizon puts out that has all sorts of visualizations that you can interact with and modify to kind of even make it more your own I'm still waiting for them I've been trying to work with them to open-source some of the engines that
they used to create the report so that it's easier for organizations to take it at their own data and have a a private version they of course want that to feed back into their cloud repository but I don't think they'd get much traction you know if that was the case so I'd love to see them have kind of a you know offline version of this that you can modify for your own I have a command again if I may um on the kpi's and of like say the most cited breach statistic a date there's a new book out that I is on my Christmas wish is that I really hope it's called that works I win
top old book which is called time-based security which according to him and several Rob several of the people who recommend the book online and in an in the book itself is a new security strategy that risk-based security by mots be aware but I'm looking forward to reading about it yeah that's really funny I was a dinner with when a couple of months ago and I hadn't heard of his new project and he was talking about it and it sounds amazing it sounds like it could be you know we have a few cannons in our industry type of go-to resources but a lot of them are relatively outdated at this point and so I'm very excited to see it I was kind of probing
him to get a sneak peek and he shared some things but I think I'll need to wait until I get my own copy but I believe it's out now right yeah yeah I think it was released about a month or two ago and so um yeah I should have read it um so I'm still just jumping back a bit what you say so you said that some of your friends and you as well started generating these numbers and seeing how well you're doing compared to the average how long they've been doing it or how long you've been doing it and how do you improve you managed to improve on those numbers or any and also
is it more something that you show to management so something more that you feed in as a more strategic thing or use it more for your like tactical needs and say that okay we're not doing well let's improve on our processes and and try to figure out better ways to detect compromise yeah I think both are very important I think from a tactical perspective of creating a report like this for your own organization it's a great way again to baseline you know you don't need a machine learning algorithm to baseline some of these simple statistics you can just put them in an Excel spreadsheet and see how it goes year by year at the most simple basis
again it's also incredibly useful to show to your management I spoke a little bit previously about how security only interfaces with the executive branch during a breach oftentimes basically when things go wrong so this is a great way to get out ahead of that and show the productiveness of your division within an enterprise without needing to kind of have a black eye in the process in terms of the longevity and how long I've seen people creating their own versions I work with one customer who didn't even need my recommendation during an engagement I present my report they gave me historical report believe I went back around five years so they've been doing this for for quite a long
time and what they've done now is they've integrated it with their soar platform their security orchestration and automation response platform to automate a lot of the collection of these these statistics so things like meantimes resolution they have a little bash lit in the top corner of their sock manager dashboard so they can always see where they are in their SLA is the analysts don't necessarily love that because it's very easy to profile them and see who's doing work and who's not but it's it's a great way to help improve even within a sock perspective you know if analyst X deals with certain incidents much better and analyst Y deals with other incidents much better it's a great way to kind of optimize
workflows so that's from a more tactical soft perspective I do have organizations I've started writing my Incident Response reports in more of a framework like this talking about trends TTP's and then vertical specific intelligence that I kind of layer on top of what I've seen in their environment and then I encourage them I leave portions blank kind of a template for them things that I didn't have the purview on but I encourage them to fill out and then maintain that year after year I think proactive hunting has become a big thing whether specific to an environment or if you bring in a third party to do it was kind of an incident response discovery I
would highly encourage folks to do that I've been a part of a number of those where companies have been going through mergers and acquisitions before they flip that switch and let the newly acquired company into their network they do not necessarily a pen test and not really a vulnerability scan kind of a mixture of the two or they do a proactive defensive exercise to see exactly what's going on in that that property before they bring it into the into the castle that answer yeah well this is getting back in in terms of improvement are they able to I'm not saying that they should you know strive for just moving the needle but they're really able to because once you see
these data then you realize that your might not doing as well as you thought are they have in their program once they started measuring these a point where they try to improve on that and if they were able to do that so for example in one case like the the mean time to detect dropped in the past few years a lot of people tie that to the fact that now ransomware was was a thing so they take into teasing into account as well but it so how did it improve on it that would be interesting for me yeah I've definitely seen improvement I think the biggest way that I've seen improvement is budgetary if you have a
report like this explaining exactly what the trends are your environment you can take that to leadership and say you know this is the justification for this technology yeah giving giving them actual numbers yeah instead of just saying that we need more money yeah exactly but I have seen it improve with training as well so if you're an organization that's facing you know four different threats and you see one of them is affecting you a lot more that's a good indication that your knowledge base is lacking in that one area from a defensive standpoint so whether you bring someone in who's an expert in that field or if you pollinate your own existing analysts with training I've
seen that that work as well in one particular example someone was getting nailed with web application stuff they had no idea was coming in through that vector they thought it was a much different type of attack and so they schooled up one of their analysts actually through sans training and that didn't make a market decrease in that attack vector it was also a very limited actor so I think just recognizing it in the first place was a big step forward for them but then to have those technical chops on your team prevents those types of things from happening in the future
so no other questions yeah sure it's a good topic so a few years ago they changed the way that they presented the top vulnerabilities used to compromise companies and the data that went into the report was totally wrong every single vulnerability in there was wrong they messed it up somehow I think they republished with the correct vulnerabilities but then in the last one they took this out entirely which data which I found interesting and relevant because I can also tie it to the OS 10 which someone just analyzed in the respect of which vulnerabilities were actually used to compromise companies again similar to what we rise and wanted to do and stop doing what do
you think of Verizon taking out data from this report that some of us consider valuable yeah that to be completely honest that was very disappointing for me as well it is in the report here and there and some of the appendices the online companion tool actually does the best way of kind of getting to the granularity of the actual tactics and techniques that are being used I think so my perspective on that and correct me if you have a different one what I saw happening was a lot of attribution being surrounded by those certain tactics and techniques so if you saw a certain you know rootkit let's say being used there was such a media focus
now in our industry that they'd initially oughta automatically pretty much assign a specific attribution to that you know this was North Korea and I think you know we can probably all agree that's incredibly dangerous attribution is not a game that I ever want to play due to a number of factors but that's kind of where I sensed it going in terms of Verizon no longer wanted to put their name behind this as this technique equals this person they certainly weren't making that jump in the report but I think a lot of the media attention started going there where they're saying Verizon saying that you know fancy bear is using this against these industries that's not
what they were doing but it was easier and easier as more of these techniques we're getting associated with actors to make those leaps in popular media at least that I do wish there was a good resource for that I think mitre has really kind of filled that gap the attack framework does have pretty good granularity sometimes too much granularity when I show it to some of my you know customers they're like wow this is like a hundred and twenty eight boxes like can we get like four there's definitely value immense value I think in the granularity that they they take it but some middle ground at least for you know director manager levels would be appreciated
yeah I think that was the ohi's featured that in the executive summary so not only was it in the full report but even if you had you know somewhat of a lay person without really who doesn't live and breathe security like we do they could still easily digest those TTP's yeah and you know question clouds no yeah we still have fifteen minutes so who are not vents on the break okay so thank you Walter thank you guys [Applause]