The Dark World Of SMS Phishing Kits: An Insider's Perspective
Show transcript [en]
um thank you very much for coming I appreciate you've all had lunch so hopefully this isn't too difficult um and our heads are can get back into the swing of things um I'd like to talk to you all today about the Dark World of SMS fishing kits um from an Insider's perspective no that doesn't mean that I do it before anyone panics I'm not texting you and engaging in this um I'm Jake Sloan I'm the threat intelligence manager for a threat Intel company called WMC Global um you've also got my Twitter up there just you can always can it be fine um any questions we keep them to the end I'd appreciate it because there's quite
a lot to get through um I'll be hanging around after the end as well if you if you can't answer your question I can't speak to me just come and find me I've got some stickers as well so in fact normally encourages people to talk to me so the way the talk will work I'm going to start talking um very briefly about sort of how SMS actually works so the technology behind the scenes that we don't really see and understand equally I don't really understand it so please don't ask me any other questions this is what my boss normally talks about and he's not here and then we'll move on to actually looking at the fishing kits themselves
and how these kits Target SMS and what we as Defenders can actually do about it moving to sort of talking about disruptive takedowns so how can we stop this sort of fraud wave if you like how can we do more than just play whack-a-mole with domain names so looking at SMS delivery methods so in the uh Network we call it peer-to-peer so this is when you send a text message from yourself to somebody else how you send a text message it's known as peer-to-peer messaging the next type we have is called application to personal ATP and we've got two types of this so we've got a short code and a 10 digit long code or
10 DLC uh shortcode messaging um it's usually five to seven digits it is highly regulated so that's something we need to consider at this point they're the vetted campaigns if you want to run a SMS campaign of a shortcode you have to have that campaign vetted by the servicer it is run through a direct bind into the carrier Network so it's not Central from a mobile it goes straight into a t giffgaff 02 however to actually deliver this to users end points there is very little fraud occurring on shortcode Note the word very little there is some but it is minor there is also no spoofing of short codes short codes are not Alpha tags so when
you get a text message and it might say Santander HSBC Bank that's normally a short code either something Alpha tag sorry shortcodes can't be spoofed Alpha tags can be spooked talking about 10 digit long code so 10 DLC this is slightly different this ironically 10 digit numbers they're provisioned through CPAs platforms so things like Google numbers bandwidth numbers text now text free they provision these numbers for people to use it is again not peer-to-peer messaging we also have a system called email to SMS this is a absolutely horrible net system that someone created and we wish I hadn't it's a viewed by threat actors constantly and it is as the name suggests you can send an email it will
be delivered on a mobile phone you can normally tell at the top of the screen so it doesn't come from a number it comes from an email address but this is known as email to SMS there is very little sort of security on this end huge amount of fraud takes place there's some stuff we can do but it's not easy or simplistic okay and the last type of delivery method is a what's called toll-free numbers um so in the US we have prefix such as 800 888 877 in the UK's oh 800 I'm afraid I don't know what if there's an Irish equivalent I'm sure there is um but these numbers are provisioned by carriers to send a text message and they
could send hundreds of thousands per minute uh depending on the text message provider and the carrier relationship as well so this uh Gucci graphic looks a bit confusing but it's it's essentially how an SMS Tron traverses a carriers Network I do want to point out this is us-based all right so it does differ around the world and this is how the US network works so at the bottom you've got your little person um note the difference between an SMS and an MMS so an SMS is just going to be your plain text your MMS is going to be uh your sort of multimedia message you can still send basic text strings through MMS they work differently threat
actors are aware of this they are handled differently by the networks you can see as it goes through the network um you've got your gateways at the top each Gateway has its individual filter so if you send a 10 DLC SMS it gets picked up by a filter and gets blocked send it through a different thing send it to a shortcode it has a different filter the filters do not talk to each other again yay networks um it then moves in through the filters into number blocking we have sort of DNS blocking IP gateways mobile security systems Etc and then it lands on a user's mobile phone over to the right there so there's a number of steps which
do take place with an SMS there's a number of ways around it this is publicly available information threat actors understand this network they understand how it works if they need to get rounded if a url's been blocked they know how they can utilize the issues if we can use that word with the filters to get their SMS delivered to a end user's mobile phone when it does land on a user's device there's a number of things that a user can then do to try and prevent this moving forward so there's reporting functionality um I don't know if you've heard of 7726 it spells spam on a phone keyboard and back in the oldie days um 7726 is run by each mobile operator
it collects spam messages their sensor blocking system threat Intel companies like ourselves get access to this information and we can then feed that back into the telcos to put into their filters it feels really stupid to forward a message to four numbers 7726 nothing happens you go why do I bother it does do something we do appreciate it it does help um you've got apps out there we've got something called spam response there's loads of them out there that you can report um now has a functionality if you get a message from an unknown number there's a big report junk button this is called 7727 because why not um essentially that reports the message back into the system it gets analyzed
and we can push it back through those filters so we do encourage people to act take action you get SMS or emails you forward it to places you click report phishing whatever you can do the same with a text message report report it does help although it might not feel like it and I do appreciate that foreign so not only do we have different SMS uh sort of sending abilities we've also got different delivery methods the most common one the one that everyone thinks about if you say text message and mobile is a SIM card that's obvious we know what SIM card is we've also got CPAs platforms um so things like twilio um cancer CPAs
platform nexmo Vonage and these guys are direct bind again into carriers they have quite unique access they have unique abilities to provision phone numbers for campaigns without literally sending a SIM card so that's another way that things can work I forgot to click my little mouse button we've got something called free app supported carriers um these run through ad support systems so please places like text tree text now you can send text messages for free they run through ad generation they utilize CPAs Platforms in the back end so they will utilize twilio next mode whatever but they buy their access through ads because people use it for free because nothing in life is free is it
oh you've got open source software uh it's on GitHub you can find python packages that send text messages and see plus plus programs that send text messages again most of these systems will just utilize an API into a CPAs platform but it does mean that you can plug and play SMS capabilities into programs into Packages Etc and the last one is e-marketing tools as the name suggests you're sort of I'm sure your marketing team has the ability to mass send text messages and we all sit there and go oh my God you didn't do that did you they use these systems again they mainly you see pass platforms to do this but it's another way of interfacing so
rather than accessing twilio directly we give them sort of a nice SMS Marketing Systems to utilize this one of the other issues we've got is a lot of these uh systems use 10 DLCs I spoke about getting those 10 digit numbers they are a direct bind into a carrier Network there's very little analysis of the messages it's just sent through 10 DLC there's a lot of resellers on the market so a lot of these app supported carriers are giving you the ability to use numbers which they've bought from a c pass platform which a c pass has been provisioned through a carrier equally they might resell those numbers to another carrier we see lots of reselling
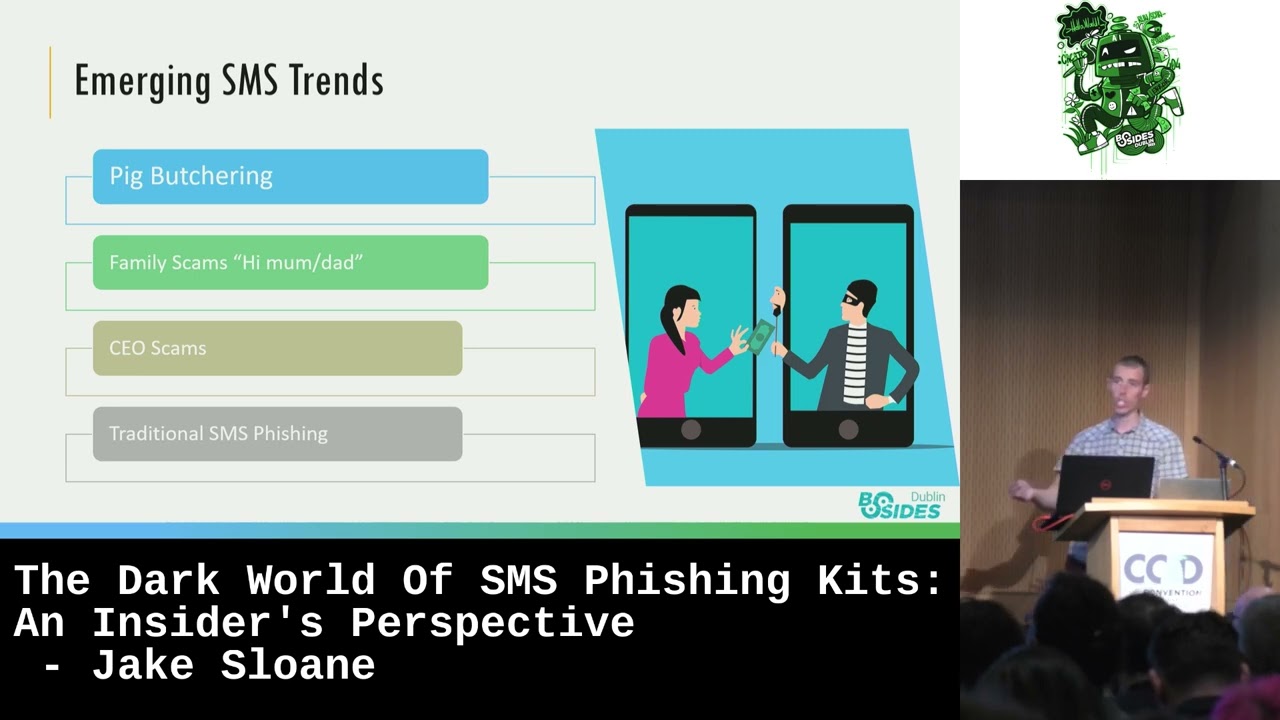
of reselling of reselling of numbers so when you get a text message and you report it and we go oh it belongs to three three goes oh actually I sold that to twilio Twitter go actually I sold that to this company and this comes to actually I sold it to this guy and you it's just an endless chain of disgusting so 10dlc a number of issues reselling is a big one because no one ultimately holds responsibility for that end point so talking about some emerging SMS Trends I think the word emerging is probably a bit rough in there but some SMS Trends we are seeing at the moment um Pig butchering I hate that phrase I
think it's horrible um it's talking about romance based SMS scam so we've all heard of some of these emails that sort of lure you in with oh I'm your girlfriend and she'll send me some money we're seeing over text message now where actually you'll start a communication system and people will start sort of Performing these relationships from these attachments to people um it's just social engineering essentially um Via SMS um a big one at the moment um High mum scams I don't know if people recognize these mum I've dropped my phone can you text me on this random number it's my friend um these are ultimately mule accounts I'm going to speak a bit more about
these later these are a massive Trend we've seen them in the UK we've seen them in Ireland Australia America not so much um don't quite understand why not in America but it's it will come eventually but we are seeing these hi Mum hi Dad um Family scams as we like to call them we've also got CEO scams um these are quite clever these quite interesting actually we are seeing threat actors finding people when they newly join a company and so using osync to sort of do this work they're looking at LinkedIn they're seeing when people go I've just started a new position they will then message them from pretending to be the company's CEO or someone very high up in the company
going can you just pop out and buy me some gift cards because everyone's CEO always asks this the amount of gift cards I've got for him is mad but they will do this and go can you buy me some gift cards scratch number off and send it to me and then resell this online the reason we put this in here is because it's going through SMS in your organizations do have an ability for a employee to report an SMS probably not you might do but it might be quite convoluted if you're a new employee you're going to want to impress if the CEO is even texting you again can you help me I'm in a meeting I need you
to pick something up a lot of people would do it and then they'll be too embarrassed if they realize it was a mistake to actually say anything because oh no I've just joined the company I don't want to be fired um so yes CEO scams it happens on emails I'm quite a lot as well I think threat actors are appreciating now that SMS is maybe the way forward because there's harder reporting channels people are less likely to know what to do with it [Music] we also have the traditional SMS fishing campaigns I appreciate these aren't Irish specific but we certainly see a number of irish-based brands in SMS fishing just with the traditional uh text link straight to a mobile phone
we're also seeing um callback scams as we like to call them where you have to interact with the SMS before it will send a link this is causing us a bit of an issue because people send us a clearly malicious message going this is your bank did you just deposit eight thousand pounds and send it to America if you didn't reply no they send it to us and it's like I can't do anything I haven't got the link because you need to interact with the fish so they are able to Target humans that only interact with it or they then get the link um so they're quite clever as well rather than these ones we can do a lot
of work on these we've got the ioc straight there in the message we don't need to engage with it so when I say fishing we're talking about credential fishing and I say oh we can do something about it well what can we do and what is efficient kit I keep talking about so a fishing cake is the threat actor source code if you like it's a collection of HTML CSS JavaScript PHP as well I know it's rendered server side but in a fishing kit we can capture that information we capture databases txt files the reason we have these is because when a threat actor goes to deploy a phishing site online they
oops there you go um when they threat actor gets a domain the last thing they're going to do is start re-coding the phishing site from scratch every time no one does that we all have a Dev and a pod environment they create their fishing kits their fishing websites their exfiltration methods their images their resources they get their phishing domain and they just dump a zip file extract and they have a live working fishing site this takes under a minute if you see a new domain getting stood up a threat actor can deploy phishing site in easily under one minute okay fishing kits are really important for us they give a huge amount of visibility ultimately they masquerade as a real
website so we're going in there they're pretending to be a legitimate website they are highly customizable fantastic this I love them is they are highly customizable fishing sites it's not the same thing you can't have one fishing site and it'd be identical to another one each controlling threat actor will add different configuration different options they might want a different dollar amount they might want a different image I want lots of different password or back end page a different Landing site a different lure message it's still the same fishing kit it's just a different configuration we can all have the same Ford car but we can have different Wheels different colors different number of doors but
it's still a Ford car and that's what makes fishing kits so appealing to threat actors oh they're also really cheap you can you can pick up fishing kits really cheap online you can repeat them online you can put them in multiple places but ultimately they are really cheap to buy and they're widely available as well they're not difficult to collect we're collecting them at work I've never paid for one obviously so they're widely available you can get them on telegram you can get them on Discord Facebook we find them being sold on you can get them offline there's lots of places that just pick them up online uh threats it will give them away for free to get a bit of
clout online or you should trust me look at my coding abilities so why do we care why do we care about fishing sites or fishing kits and fishing sites I've said oh they're cool they're cheap they're customizable here we've got a mygov this is Australian government uh it's a fishing site uh just trust me on that one it is um on the face of it every single mygov fishing site will look basically the same all right there might be the odd little line here in line there but ultimately it needs to look like the same website doesn't it we're trying to masquerade as a legitimate service so every site will look the same but if we look at a fishing kit we start
getting a visibility that back end behind it what makes this thing run if I asked you all to create a website that had a black background and a yellow circle you'd probably all do it very differently different variable names different ways of using it someone just canvas some user image some would copy it from here some would go on to chat GPT and cheat but there would be a whole everyone would do it differently and that's the same for threat Hatter we can utilize those uniquenesses to understand what's going on so this here is the fishing kit behind that mygov site we can see there's a number of PHP files we've got a config file uh we've got
me.php uh Pro hacker because I'm good with my least speak a pro hacker.php down at the bottom so let's take a look at one of these files so this is the pro hacker.php's page yeah I don't know if you can read that I'm back I do apologize if you can't I should have been keen and sat at the front here we've got the PHP elements of the website so we actually see the message body being built we've got threat attribution it can lose States my telegram idea is pro hacker easy in it you've got username uh passwords this will be built up dynamically when a victim enters credentials into the phishing website um you've then got the send function
you've got a weird looking array at the bottom we'll get to that later um and at the top you've got two requires you've got require config.php and require me dot PHP so if you have a look at config.php as I said to the highly customizable in here we also have a telegram exfiltration method um so we now have the bot API key so this gives us more ability to have a visibility into these fishing sites how are they sent who are they sent to what information are they gleaming and Gathering we've got a chat ID we could potentially reverse engineer this to understand what chat they're sending it to on Telegram inside me.php is is me it's me the
threat actor bizlogger hat myyahoo.com never heard of that domain but we've now got another ioc so we've gone from a simple basic here's a mygov fishing site I've now got Twitter names threat actor names email addresses I've got things I can work with and attribute this campaign back to an actor so what can we do about it um kit kill chain is what we're calling it inside and I hate that term but my boss told me how to put it don't zoom in on it then get killed chain half killed it okay so different ways that we can have disruptive takedowns yeah can you not hear me is it on is it on is it on Hello
oh fantastic um so we're talking about the kicks kill chain so how can we target these criminals and actually make their lives harder I'm here to annoy people obviously not you guys I'm here to annoy threat actors I want to make their lives harder I want to make it more difficult for them taking down a URL is easy if you have a phishing URL you can take it down dump it on Twitter make it public people can take down a URL it's not that difficult contact the web host contact the domain name Services we can get them taken down I'm not saying don't do this all right I do continue to do this there are systems there's
procedures people are very good at it it's very quick and easy to do but we should continue to take down the domain but we need to go further we need to look at the code behind the Seas this here is a piece of HTML from a campaign known as the compact campaign it targeted uh office 365. it was highly successful and it continues to proliferate online to this day it uses three quite interesting and unique uh web resource calls it's almost a CDN for a phishing site we have a media end point this is hosted on a third party it's a stood up domain there's nothing legitimate on this site it hosts the media elements for this campaign it
codes the images the background images the CSS the JavaScript it like we did if you can take this down it will it looks like utilizing the CDN from the compact campaign underneath here we have B uh B hosts the exfiltration uh code compact.php hence the name this hosts the PHP exfiltration method if you can take this down all the other sites utilizing this CDN as I like to call it will be killed so rather than taking off one site let's take down as many as we can with each hit obviously don't take down the last link that's a legitimate redirect link but it's really interesting these sites are stood up with three basic uh configuration
options for where that CDN sits so here's that media directory that spoke about um the CSS the fonts the images the favicon for the Office 365 phishing site here's the B link I spoke about you can see there compact.php you've also got an error log um you've also got logs and if you open logs you've got emails.txt so not only can you take it down you can also perform victim recovery these threat actors don't care about PCI DSS or your data protection policy they will quite happily store stolen usernames and passwords in dock txt files online so not only are you protecting your organization you're protecting other people from being fished you can also protect um some poor data controller
when they realize that all their emails and usernames and passwords were just online exposed we had a really interesting campaign uh targeting a client's HR System so this wasn't targeting consumers it was actually targeting uh employees in the HR System you can see that we have a constant base URL of formspree.io this was a third party uh form creation website it stood up as the exfiltration method we went to form sprue either a lovely company uh we spoke to their CEO they do legitimate work to help people make forms easily online like threat actors and we said look this is being abused take it down they took it down they also gave us the email address of
the user account that created it and they blocked it they blocked the IP address the threat actor is using the threat actor tried to create two or three more form spree campaigns we took them down they've never used form spree again so we are making threat actors lives harder going one step further investigating that threat we can take action so that's taking down urls talk about phone numbers we're talking about SMS stuff what can we do with phone numbers obviously when you get a SMS scam it all comes from a phone number you can report that phone number 7726 when you text it it will say thanks who sent this to you what's the what's the phone number and
you can send that phone number to 7726 and they will then investigate it and perform action on it so we can take down sending numbers but again let's talk about one step further One Step deeper we have link or we have phone numbers in messaging campaigns so we can see here the high mums scam again or high Mar this time send me a text on we need to take down the sending number and excuse me and that second number as well it is equally used in fraud the reason they have two numbers in these campaigns because the initial number is used as a Spam they have SIM boxes they plug this into and they just pound out hundreds of
thousands of messages telcos detect this they would take down that sending number very quickly but their secondary number is less reported it's less known when you get your communication with a threat actor they don't want to lose that communication so that secondary number stays online for a lot longer so we want to report both of these numbers we've also got a call Wells Fargo call my number um take down these numbers because what we do see is the same numbers being reused in multiple campaigns so we've got Wells Fargo using that 2265 we also have a Bank of America using exactly the same phone number so threat actors will reuse their own infrastructure we've got
to take it down so we're taking down ascending and those numbers in that call to action it's not just text messages where we see phone numbers we have a WhatsApp business account his it's targeting ICI Bank in India delivering malicious APK files um what's that business account has a really simple way of reporting a malicious business account again you can also report this number to the Telco provider as well so it's not just text messages that we see abuse we see abuse of phone numbers everywhere um this would continue this is our internal system when we store our fishing kits it gives us an easier visibility to search on things what I want to talk to you about is phone
numbers within fishing kits themselves um so this is a twilio number um again I'm not calling out twilio here but I see past platforms are also abused within uh systems we can say welcome to double a name your transfer verification is random opt um this is actually a fake bank I don't know if you've heard of fake banks these are again a CAT scan campaign that threat actors will create fake Banks to try and lure people in with you've won a million pounds we've all had those emails they create fake bang strategies show you that there's an account with a million pounds in it so that you think you believe it and they set up fake 2fa
and everything and that's what is actually occurring here what starts to get really interesting is when you start looking overlaps between phishing campaigns so we've got here a twilio sid this is sort of an API uh account Sid ID we can take this Sid ID and we can look between all the fishing kits we've collected we can see we start having overlap between all these Banks or fake Banks if you like and this makes us start understanding why disruptive takedown is so important you're not just taking down one campaign you're able to take down many other campaigns you might not have visibility of but they are out there things are like spidering taking one down is all interconnected
ultimately so taking down phone numbers taking down bank accounts whoa beautiful so
it looks fine on this screen so we're talking about bank accounts as it flickers around on screen um we're seeing a number of uh campaigns these high mum scams these high mum scams text to Mum and that's the other friend's phone I dropped mine on the floor um I smashed my phone I've lost all my pictures I use a number of different uh lures gamble baseball flashing at me when you communicate with these threat actors uh they usually move to Whatsapp um I don't quite understand the reason behind I think it's free they don't need to pay to text things around if you blink you can see it occasionally hey I know that
these uh campaigns ultimately lead them to saying can you send me some money um mum I've dropped my phone only 250 pounds can you send me some money and they will send you Bank Account Details they are highlighted in blue actually I'll zoom in these Bank Account Details are mule accounts as they're known online um these mule accounts can be collected in a number ways either they're compromised accounts that threat actors are selling or they're victims of a scam themselves and don't realize it or they're just out to get a quick 10 quid we can report these two Banks it's really trivial in the UK I don't know how Irish banking works I'm so sorry in
the UK the sort code is really easy to work out which bank owns that account we can go straight to the bank and they can perform fraud monitoring controls on that account I'm not saying they take them down and out of action it could be a victim ultimately that we're dealing with it could be a vulnerable person who doesn't realize their account is being milled um but we can gather this intelligence from the threat actors with a bit of communication we can work with the banks and we can perform fraud monitoring on there once we have visibility of these accounts if the bank is willing to utilize the intelligence which most are I've got to give the credit to the banks
they are really good at taking this intelligence they can then look for victims of the scam by looking back at historic analysis of an account and they can perform victim fund recovery as well so if someone might not even realize they've been scammed utilizing this utilizing his productive approach we can protect people's funds cool the next one I want to talk about is API Keys we've spoken a very uh briefly about this earlier we have visibility of API Keys Within These fishing kits normally uses exfiltration methods here we have a Discord API key um quite obviously we can work with Discord Discord are really good at working with us and they have a CTI team they're very
open they've got good visibility into their own network we can give them an API key and they can perform controls on that checking victim logs shutting out users locking down accounts the phishing kit is your source of evidence you don't it's not going to the FBI and you've got to show them a huge amount of loss and controls and all these other evidence and here's a person's mother's maiden name the fishing kit is your evidence of fraud on that API you've got telegram um they're a little bit more fun to work with um we can do some work with telegram it is harder I'm not going to pretend to you that it's as easy telegram a little
bit more uh snakey but we can utilize this intelligence to do uh CTI work overlap pivots and we can sometimes get them taken down depending upon how they've been set up but having this visibility is really important here's nexmo nexmo is that c pass platform very much like twilio it's abused within kits they're able to utilize access into accounts and sending out Mass SMS we can reach out to next mode they're really good they're really responsive here is an API key which is being abused please if you take a look can you take it down take it out of action we're cutting the threat actors off for their ability to send and proliferate uh here we have a my my tapi
um it's a third-party WhatsApp API essentially um so it's using uh WhatsApp to send but it's having a little wrapper on the front of it um so you can send via API through WhatsApp again working with them we can get stuff taken down it's a disruptive takedown approach we're not playing whack with domain names we're taking the domain down but we're taking down the threat outer infrastructure behind the scenes to make it harder for them to re-stand up their campaign again this one's quite obvious I'm talking about emails how can we do email takedown and where do emails come from um wow so not only thinking about disco's not only thinking about uh sending email addresses they're quite
obvious we've seen them early in the presentations of my API I love it's flashing and all your faces sort of strobe it's great um we can also take down threat actor email addresses so when the screen decides to update we can see here we have a extra botus email address okay that worked this is a email address owned by threat actor so not only are we taking down that sort of uh user's email address that might be receiving the logs we can potentially take down the threat actors email address which is running these campaigns so it's making it harder for the threat actor to talk to his clients if you like um we're sort of severing it as they run
and what's the benefit of doing this well here's that X robotics uh Gmail account you can see it's in over 2 000 kits we've got access to if we can stop that threat actor from communicating with clients running that as his advertising name whatever if they have to Rebrand constantly it's going to annoy their clients and they're going to move to another threat actor taking down every opportunity we can what do we got in here so here's a sending email address uh Grace to logs gmail.com we're talking about email takedown but we're also thinking about how we can utilize a visibility within fishing kits to understand the threat more so we have this grace too long so we've got it
we've taken it down woo us what else can we do we can investigate where else that email address has been seen so we can see within here that that Grace true logs has been seen in four other fishing kits so taking one email address down four kits disrupted if we have a look in one of these uh kits which is that Grace two logs is also affiliated with a secondary email account the reason threat actors do this is a redundancy thing we have it at work redundancy threat actors like it too they would say well if one of my email accounts gets taken down I don't want to lose all my Victim logs I'll send it to
two places so we can start with one email address we do a bit of pivoting do a bit of hunting looking through what fishing kits we've now got a second email address we can affiliate back to that original threat actor we can take down the infrastructure we didn't even know existed before we had it so we can start really getting into the bones and annoying threat actors taking down vax 2 log um impact six kids so that's 10 kits in total 10 different domains all impacted by two basic takedowns
well here we go again stop it
I spoke to uh earlier right to the start about that array item remember we saw at the bottom of that initial HTML file I would say here it is again but it's not is it we found this in a uh an anti-bots fast anti-bots are a system where threat actors put in Protections in place to prevent people from seeing their site and we can see that email address coming up again we can actually decode this it's a very basic decimal decoding um it obviously decodes for an email address this is sort of what we call a back door if you like these threat actors will back door their fishing kits to try and exfiltrate logs out of kits
they don't even control or own anymore this was a really trivial example some are quite complex some are really well hidden um this is again another good disruptive takedown place it's not only the obvious email addresses it's sometimes a more hidden email addresses you can see taking that down actually impacts over 2 000 kids this exact same email address they've seen in 2 000 fishing kits online and last but not least uh talking about anti-bots anti-bots are a process uh that block people they don't want viewing their fishing sites um so you're thinking about uh IP blockers they block IP ranges we've got host names uh We've also got geographic regions so if it's an Irish targeted
fishing kit they don't want people in the US seeing it they're not going to be victims let's hide a whole country from viewing my site there's commercial options available this is one of those uh fishing logs you can see it literally blocked whole ranges of IP addresses if they think it belongs to a threat Intel company if they've seen some weird traffic from an IP address they'll just block it they don't care um it's not like you're panicking that I'm like block a victim they'd rather block a victim and keep all of the security researchers out than the other way around you're blocking whole host names fish tank dreamhost net pilot crawler Facebook message Labs whatever
they'll block everything if they can we've also got some more really funky text at the bottom this should stand out to everybody it's just it looks weird doesn't it you can decode that it's another secondary hidden exfiltration method they're all over the place again taking down those email addresses we've also got commercial options available yeah I'll skip that slide then come on play ball with me please there's commercial options available we can you can buy anti-bots this one is was killbot it's an option you can go on you get an IP API key and it will they will do the IP blocking for you so you just connect the API key and off it goes
this is what I like to represent internet as um I'm not really a a Superman or Batman I think it's grathom city is it I don't know but taking down these killbots what does it do well at the moment this is internet no one can see the fishing sites the remaining hidden the remaining Anonymous take down that kill block key and all of a sudden all the scanners everywhere can see them those fishing lights are popping up all over the place the visibility is enhancing we can see the sights because we're taking down their protection methods now am I just standing here rambling on thinking well it sounds great but does it work it does
work we have had successes with this we have taken down email addresses belonging to Google Yahoo Outlook Hotmail and Yandex we've taken down phone numbers carrier numbers twilio text now Google numbers we've taken down API Keys belonging to Discord telegram WhatsApp we've taken down over 110 kilowatt API Keys these companies are responsive if you know what to deliver to them if you have the motivation you can do this disruptive takedown don't play whack-a-mole with domain names it's constant it's boring and it's annoying actually annoy the threat actor slow them down prevent them standing everything up and that brings me to the end of my disco presentation I thank you very much for coming





