Getting In: Initial Access In 2023 by Tony Gee

Show transcript [en]
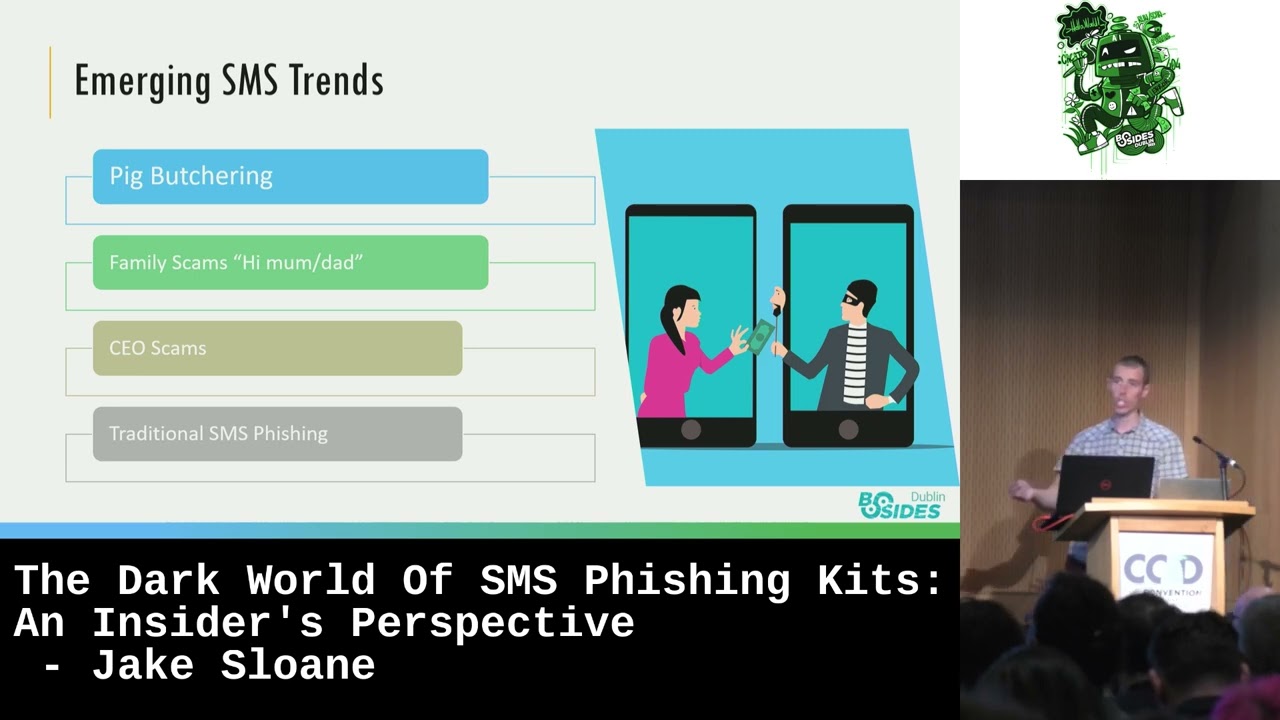
so welcome everybody thank you very much for firstly having me and also coming along to my talk which is really cool um so this talk is about initial access uh and pretty much just about initial access I'll talk about that in a second but uh but who am I uh so I'm Tony G uh I'm a bit of a EX blue team as you can read all there um my passion really lies in open source intelligence and social engineering uh both physical and remote uh although I do kind of want to be a purple teamer because I really do like I like purple team and I think it's pretty cool um but I guess coming from that blue team background it kind of lends itself quite well um but anyway you can reach out to me there if you want but let's crack on and talk about this talk so I'm sure you know what that is that's the miter attack framework and what I want to really explain is that what I'm gonna talk about is the stuff in red pretty much everything up to execution not including all execution and the reason for that is this talk is about initial access it's not about what you do after that um so hopefully we're on the same page and hopefully we're all we're all happy with that um so let's start off with our reconnaissance so ahead of any job of course we need to do some open source intelligence um and so for us I think for us when we're trying to gain access to an organization the key things obviously are email configuration so we need to find out things like SPF dmarc and dkim uh find out what that looks like and whether there's any weaknesses there is really important we need to find out what their male security Gateway look is you know are they using a particular type of product um that we might be able to bypass or we've got bypasses for text records I cannot underline how important tax records are for us as attackers and the reason they're important is because quite often they will include supplier information and that supplier information we can use in our pretext um if they're using Office 365 do they have a smart host available that can be extremely useful and if you know about that you'll know why that's useful um if they've got teams or they've got slack that's really cool because you can direct message stuff bypass all of the controls and just contact them directly obviously any services that their staff use so things like vpns and Citrix those are really useful um there's a couple of seats over here guys but you will have to sort of slide past people I'll give you a minute to get in there's four seats at the front there if you if you want I won't buy honestly we're good right we got everyone in Happy Days uh hey uh so you know obviously things like as I say teams and slack is really useful uh but finding out what things stuff access those are going to be the things that you're going to try and manipulate or try and try and claim right it's obvious um obviously contact details as well if you're lucky and especially if you're doing uh sort of a social engineering engagement as opposed to a pure red team style assessment the chances are you can ask the client for for contact info and I really recommend doing that especially if you're going to start using smushing style attacks because the last thing you want to do is start submission someone on their personal mobile or or even on a mobile that's not theirs anymore so it's really useful if you can get contact info from the client so in this talk I said I'm talking about initial access I'm primarily talking about the social aspects of initial access obviously a really simple path into an organization is through a vulnerability and some of the services that they've got installed so their vpns or or their Citrix servers but it really does have to be those Services explicitly because the reality is that if you exploit some random web server on their Network the chances are in most mature organizations that's going to be in a DMZ so you're not really going to then be able to move anyway you're going to have to perform quite a lot of lateral movement to get out of that and get onto the network where staff actually work so for me I think you know realistically exploits exploits against Services unless it's targeting some of those systems I wouldn't even bother nowadays most attacks need to be socially motivated to have any kind of success um so realistically fishing is where we see most of our red teams start and also our D fear investigations almost always start with a phishing email that is realistically the ways that you get into organizations these days if you're lucky you might find exploits like that but be very unlikely in my opinion unless you've got a particularly immature organization and then have a field day Happy Days um so as I say fishing is probably the easiest way in this type of attack basic phishing attacks like these probably less likely to work now they're pretty dead corporate security controls are pretty good these days especially in mature organizations so an end user awareness as well let's not forget that because end user awareness is also increasing and people are getting wise to phishing emails and fishing messages but they do still work you just have to work harder and you have to do a lot more research and you have to use your oceans to guide you on the best pretext and the best technique for that delivery so as I mentioned key things for me txt records find out who their suppliers are if you can find out whether they use something like no before it gives you great pleasure to use the note before phishing header and bypass their fishing security controls which is brilliant works really well and I strongly recommend doing it I add it to every one of my fishing emails just on the off chance that they use now before it really works quite effectively um and it'll just sail past all the spam controls and end up in their mailbox which is quite cool and job sites are also really quite useful they can tell you the technology that's in use so you can find out what's uh what you can fake or consider faking um email Trails as well so you can create a fake email Trail if you can find a full email Trail you can with the signatures and and the email Footers you can use that to create an email Trail which will add legitimacy to your phishing email um I think nowadays it's really important to use trusted domains for your links I think these days you can't just stand up a website and send in a link and expect that link to work uh most proxy servers will block that straight away or at least they'll put a reputational risk on it and then end users will become more aware that there's something not quite right there so for me you've got to use trusted sites github's quite useful um using uh sort of other other sites sort of more trusted that you've got a lot of um experience in it's very useful but what I really like using is I like using domain fronting so you know domain funding is not just for your C2 you can use it for your phishing links as well and what's really cool about domain fronting is you can use something like a zero Edge or Cloud fun they're probably my favorite favors I actually really like Azure Edge and the reason I do is because Microsoft really don't care about it if you've got a Microsoft organization that you're targeting and that's where your icing will tell you that um you can't realistically nowadays just go and buy a a domain that's kind of like Microsoft you know you can't buy M1 create soft or whatever it just doesn't work but if you use a zero Edge you can create a subdomain that looks exactly like their brands you can literally squat on their brands I had numerous domains uh on Azure Edge that were you know OneDrive or OneDrive download or whatever you know just usual sort of stuff that you would expect that Microsoft would use I really do recommend using it it works quite well it's quite effective I have to say um and it just gets straight through and because it's a trusted domain most proxies were just allow stuff to just click on it and Away you go happy days and you can really get creative with it you think how a lot of people use um as your Edge is quite often they'll use it for hosting content so you can mimic that so you can have really long URLs that kind of look like something that is is more genuine it's pretty cool um if you are going to deliver things payloads for example realistically your payloads do need to be fairly custom now they do need to be built to bypass whatever defenses you've managed to identify in in Ocean um attachments I think these days are dead um you've got to be quite lucky to get an attachment into an organization these days um yeah you might do in less mature organizations but most mature organizations you're not getting attachments in um not your uh not your your Commodore Garden once put it that way I think it's worthwhile testing your spam so testing your messages so users use Spam testers to find out what reputation it's got um the other thing to do is if you can get a copy of your phishing email back from the client review the headers find out what their mail proxy is done to it and find out whether or not it's been been blocked obviously you can't do that on a red team but on something like an agreed social engineering exercises there's a lot more flexibility to do that so do that and and allow you to to potentially get past their controls fundamentally I don't think that is cheating because realistically you could email an organization and then they would reply back to you and give you ahead give you headers of their emails so you know you can you can you can do that quite happily um I'd also recommend checking your domain categorization so if you are going to use something that's not fronted do check your domain categorization because that'll tell you whether their proxies are going to block it uh techniques I find work really really well though is is spoofing does still work um Believe It or Not especially if their DNS configuration is terrible which a lot of organizations they don't get it they really don't get the most basic stuff like something like an SPF uh record is so crucial to get that right dmarc is so important but many organizations just don't get that they they install something like DMACC but they put a policy of none so it has no points it's ineffective the SPF records more often than not there'll be a either a very wide SPF record sometimes it fails I've countless times I've found SPF records which have got too many DNS lookups so they're not going to work properly or they've got a soft fail on them rather than the hard fail so you know sort that basic out and you fix a load of problems on your mail Gateway anyway moving onwards um but where you can often can't often spoof email of their domain very very rarely do you find supplier domains are in their anti-spoofing lists so just type a squatter supplier you know just do that or even just spoof email from the supplier it will work more often than not um depending on the supply and depending on what their email configuration is of course the other thing I like doing is I like using outlook.com and uh and AWS email um so I actually prefer outlook.com because most organizations these days tend to use Office 365 so it kind of looks a bit more genuine and it's really easy to set up emails on outlook.com you don't need to give any information other than a phone number to verify it so use a burner number for that um and it looks more trustworthy you can also typo squat on their brands although they didn't let me register onedrive.outlook.com I did try but you can register teams or something like that it works quite well but but OneDrive didn't which is annoying um but yeah I I really like it and it's a really really neat way of of kind of um adding legitimacy because of course being an outlet.com address most mail service will will quite happily support that um uh the other thing that you can do is of course you can use the Office 365 smart hosts I'm not going to tell you how to do it but I do recommend having a look at those um because it's quite useful because you can send emails using it and it will invariably bypass whatever third-party security control they've got in place and end up in the end user's mailbox and it will also include things like presence indicators if they happen to have teams so if you send it spoofed from an individual it will look like it's come and land in that mailbox as if it's from that individual they'll double click the name and it will show the individual it's very worthwhile doing so you can literally send raw SMTP directly to it it's very cool um so right we can send some emails but what exactly do we send well I said pretty much attachments are heavily scrutinized now they're not realistically going to work but HTML smuggling is a really good way of being able to bypass that problem so send a link to a file hosted on a trusted site in HTML file hosted on a trusted site for those that don't know what HTML smuggling is effectively you create an HTML page and embedded within that is your malicious file whatever it happens to be it's encoded essentially when they load that page you can then decode it and it effectively downloads to the end to to the workstation and away they go the only caveat I would say is things like Mark of the web do still apply there um so we'll talk about that in a second but but there's there's some things you need to think about with that but certainly if you can host this on a trusted site then that's even better so if you host your your malicious HTML on a trusted site you're going to have a lot of luck with that I would suggest you can send the HTM email is an attachment I just wouldn't bother just host it it's easier stick it behind a fronted fronted web server and you're going to be in a much better position you know you can you you can have your your hearts content what kind of domain you want to use you can make it look more more legitimate more trustworthy it's really worth it I really do recommend it um so are those talks not about execution obviously we need to think about what we actually deliver and you know word excel executables they're pretty well detected they are challenging especially executables uh Mark of the web as I said does a really really good job of stopping those files from from working so smart screen will kick in which is a little bit annoying but of course you can just zip it or you can ISO it and that does still work it's becoming more detected now but it does still work so encrypt your or not encrypt sorry and zip up your file and then when they execute that file or they pull that out of that zip file it won't have the mark of the web attached to it which is really really useful um the other thing you can use is image files they work quite useful quite well as well one note is something we're seeing as well which is really really cool we've actually used that ourselves but we're seeing that in our investigations quite a lot um so one note effectively opens up an HTA um which then calls uh living off the land binaries um so much more genuine looks really really uh real and um and much less likely to be detected by smart screen or Defender realistically macros don't really work now and most organizations have got a handle on it end users have got a handle on them as well um but you can use other applications so many organizations have blocked things like Word and Excel because natively they support um auto exec but PPT you can do macros in that so no one really thinks about blocking that you do need to if you want to make it kind of Auto execi you do need to use a custom UI but that's trivial to do you don't need to provide that to the end use it's all built into the file um so I would recommend office ribbon X editor for that it's pretty pretty cool for that um and then you just need to get creative with with your with your lure so you kind of make it look like it's come from a supply of perhaps um so I actually did that one that was a real one some someone might recognize that particular slide template I find it on on their their website and the client I was looking at actually used that company and so I just faked it I I used that and created a load of stuff on it to make it look like it it needed macros enabled yeah usual stuff I interested in the publisher and RTF files do support auto exec so you could use those um publisher probably less so many organizations don't deploy that stuff but RTF could work it's worth a try um the other thing you can do of course is you can use oauth apps they're pretty cool for getting yourself a foothold in a Microsoft environment um so they can allow you to then do things like internal fishing or just get access to data drive-by compromise is something many people still talk about but let's be honest if you're a researcher and you've got vulnerability in something like Chrome are you really going to use that on a red team no you're going to sell it to someone like xerodium for half a million dollars and then have a very nice holiday there's no point so I really wouldn't worry about that or wouldn't consider that as a viable attack technique unless your target is either very well funded and your red team is is a very big red team and you you want to use that or or realistically you're a nation state operator because no one's going to be using that why would you burn it same with a PDF exploit you know why would you burn that on something like a red team when you can sell it for a lot more money the office really what is really really powerful I think these days is credential theft um especially now more organizations using Microsoft 365 because of course that gives access to basically everything right so I would suggest the email delivered through uh uh you know a trusted Gateway something like that um can get into an inbox once it's in their inbox uh have a trusted link to a server which is hosting something like evil Jinx so you can then start capturing their full session information about five minutes left [ __ ] the bad I'm gonna be way over there's no way I've got five minutes left why well good luck whoever's speaking afterwards we might be in lunch uh sorry into break uh anyway um yeah I've got way way many to too many slides I'm like halfway through good luck um so the other thing is obviously once we've got creds we can get access to things like vpns um we can do internal phishing capture other things as well which is pretty cool um the other thing is smashing I think these days most staff are actually quite switched on to Smashing really interestingly they're fairly switched onto it I don't find it works that well now but I don't know whether that's just me baby I'm rubbish at it but uh but if you are going to use it things like typo squat domains evil Jinx works really well in that type of attack um the other thing is look-alike domains do work quite well if you set up your own Microsoft 365 service so set up a fake one that looks like theirs and then use that to send direct messages so teams messages you can also send links through OneDrive um most of the time though they will open in um in the web so what you need to do is change it to download from embed and uh and then it'll just download it it's really cool um but again Mark of the web will apply there so you need to do something around that oops gone too far way too far like you can see how many slides I've got left to go loads you'll be fine um so I mentioned teams is quite cool for fishing so you can send direct messages to people uh you can also use slack for this similar sort of situation um it used to be that it was open and you could message anybody with any outlook.com or any teams account you can just message them directly um by default now Microsoft have this turned off but most organizations that you're going to be targeting will have already had this turned on