IoT From An Attacker's Perspective
Show transcript [en]
morning guys I'm Rankin and I'm here to present a talk on IOT from an attackers perspective so yeah I'm a security researcher at one of the largest ship making companies so I've flown all the way from India just for this conference so I hope I don't screw this up and have something of quality so my areas of expertise include our web mobile in frog code reviews and the regular stuff so the past few years have been performing researchers on linux kernel's and IOT related stuff ranging from the devices platforms to the applications so yeah the agenda or the takeaways that we can expect from today's talk is that we will be able to understand what I 80 exactly
is and what are the components that are required to build an IOT solution and understand what kind of attack surface it reveals to an attacker and yeah basically that's what we will be looking at today in the interest of time I will try to keep this as short or as short as possible but in case you find me going to cast please feel free to interrupt so the first this is the foothold at this point of time we can understand from this kind of a diagram that IOT have reached various verticals ranging from home automation healthcare transportation retail and so on and so forth so we are pretty familiar with all these smart devices that we have on our
phones so we have dumb devices like coffee makers even our television is becoming smarter and smarter so they call it smart device but I I call it an entry point for an attacker because all it does is brew coffee and have an N IC which we shall sit to cry to the Internet so here and IOT is grow pretty remarkable it's growing pretty significantly so there if you research out there that suggests that IOT could be a few trillion dollar industry in the in the coming year so this is a great space to ventured into right now and make some money so yeah this is another screen slide that gives you an idea of what kind of components or what
kind of smart devices we have in each vertical so we should be we are pretty familiar with the home consumer stuff right so smart security devices and even the motion sensor that is here I'm sure it should be working on CB protocol so we should have some hub within this auditorium or theater so these home automation or home consumer devices have something that we will we find in our day to day life moving on to transport and mobility verticals so we find all these autonomous driving or self-driving cars that are gaining traction a lot of traction these days right so we also I mean vamo is are trying to build a fleet image which is self driving so in the
near future we can find ourselves being driven to destinations we thought driver or a chauffeur so that's something that we have to look forward to and healthcare here Healthcare also has a lot of IOT implementations where the patients don't necessarily have to stay in the hospital to get get 24/7 health care so essentially what that means is the patients could have some variables that that keep monitoring their health that that boils down to home consumer devices as well so as we can as we saw Apple watch the latest version of it it has an ECG built in so they are also trying to they're also trying to embed that pressure monitors engineer SmartWatch so healthcare healthcare is a
huge consumer I would say when it comes to IOT space and we have smart building smart cities smart buildings yeah we we see all these are temperature sensors motion sensors within within all the buildings that we are huge buildings around these days so that is something that that significantly increases the attack surface so what is IOT ionely is nothing but it is a coalition of various devices embedded devices sensors and applications basically so all of these components work in tandem do it's basically like neatly choreographed dance right so all the all the sensors kind of collect data from the physical world and this data fn2 cloud infrastructure which is the backend which which goes ahead and process all
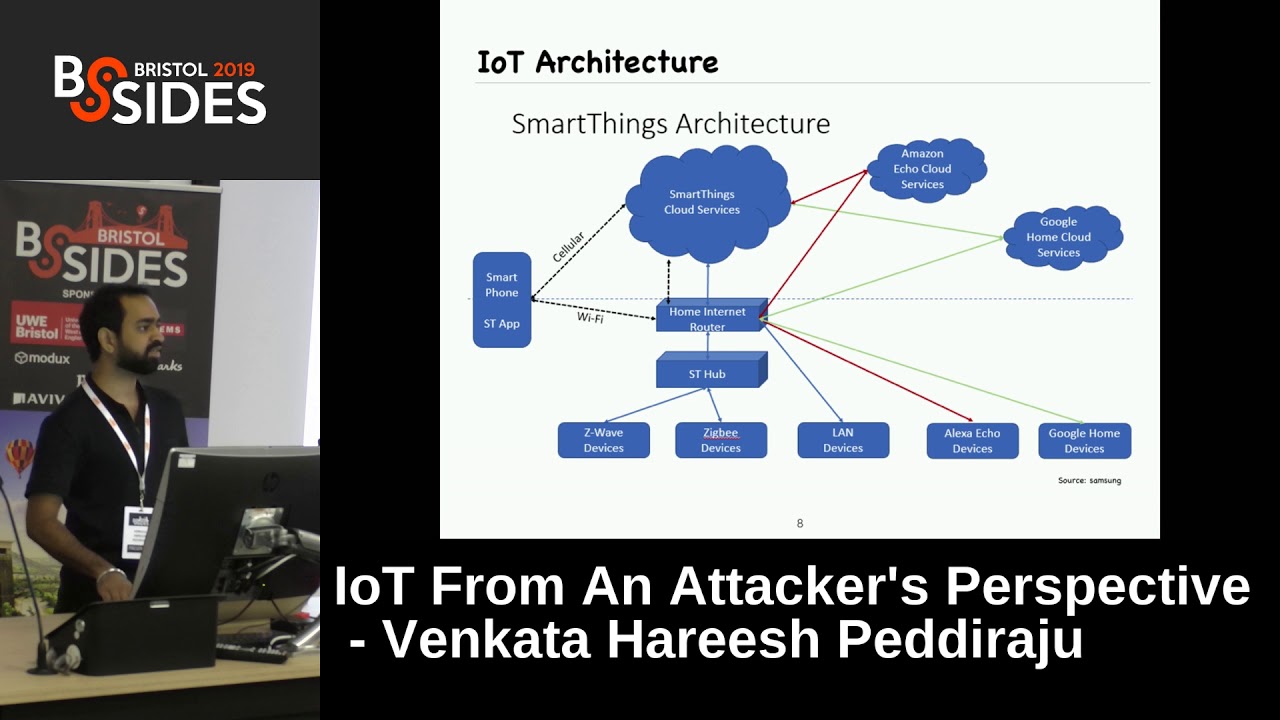
this data and does the work for you the work can be anything ranging from turning on a light to driving your car sure to better understand this let's take a look at the Samsung smartthings and architecture so what we can see here there are a bunch of devices right so devices require a language or a protocol to communicate with each other and the hub so the protocols that we can see here are V wave and we'll be using B if we have a v-mail or a CB device then these math things have or essentially they have should be speaking the same language it should be able to communicate with the devices on the same protocols
and this hub would essentially be located in the same premises this does not have a huge range or something so whatever data is being collected from the devices are fin sent to the hub which then connects to the internet using a home router so the architecture that we are looking at is for home automation right so it connects your home home router and then that data is uploaded to the cloud services so the reason why cloud infrastructure is a huge deal when it comes to IOT is that the embedded devices or the endpoint devices that we have installed in our homes buildings whatnot so they are all essentially they have a very limited storage the storage that we are talking
about in kilobytes so within that storage it should it should run a bootloader it should run and kernel it should run in an operating system and it should also run an application so given so due to the description the devices cannot they usually don't have the compute power required to process all the data or all the information that they collect from the physical world so all that compute power is given to an IOT solution from the cloud service so yeah and we can also understand from this diagram that these devices can also be controlled by Amazon Amazon's Alexa and Google home the reason why that is possible is that so they have so there is this thing called a third party
integration right so Amazon Google and Samsung have come together and they have they have opened up certain services that each of them can leverage to communicate with each other and control the devices essentially so you can this this is also being implemented by Philips whew it's just not like a Samsung thing or something so essentially what this means is you use your big cell phone or your Amazon Alexa to control any Samsung bulb that you might have but your home or even their refrigerators and their waters and dryers so - from a convenience perspective all these home automation solutions come with a smart home smart phone application and also a web interface so even that is a attack
surface when you look at from an IOT solution as a whole so let's dive into each of them in their features right so yeah these are the IOT components so as we talked about so there will be a device it can either be an embedded device that is placed in your coffee maker or it can be an actual sensor like definition that we have right here in the corner and so each device will have an operating system so the operating system that we are talking about is not an apple - or a Macintosh so it is something called as a real-time operating system or commonly known this are known as Aptos so there are a bunch
of real-time operating systems out there like free free are two tiny OS and stuff like that so the IOT OS that they often lack kind of regulation where so what happens here is that each vendor they come up with their own operating system and when we take these operating systems into consideration they lack all these traditional security measures that mitigations that we have in our OS right like a SLR DB and so on and so forth so that is something that needs to be addressed and as discussed via mobile application and web interface is still a huge attack surface in an IOT solution because that is basically how all these devices are controlled and how ya hub is
something that collides the data from all the devices and so hub is essentially proxy which which which takes the require from the user and sensitive to the devices and vice versa it also collects data and send the information back to the user so of course I an IOT physician hugely depends on communications so the communication protocols may range from ZigBee free wave bluetooth to your regular Ethernet cable and yeah cloud infrastructure is pretty pivotal in an IOT solution so moving on to the security perspective of an IOT solution the CIA triad stays true here and this is this is basically the pillars of security even when it comes to an IT solution so confidentiality the state of
being secret is ok so as we discussed earlier smart devices are present everywhere right so we have security cameras around our homes and we have all the fencers laying around for example if you take Amazon echo it has a webcam it has a camera built-in right so we may have them in our bedrooms and we're not so that is something so whatever data or whatever video feed it is getting it is capturing should should remain confidential and it should only be accessed by the product owners who I mean the device owners and that is a huge if this is breached then there's a huge privacy violation right so confidentiality is pivotal so as integrity so integrity is the
state of being unmodified by an author edit and unauthorized entities right so if we have the security system in our home so we only want us to be able to unlock the door and not anyone else so that is something being addressed by the integrity of the solution availability is just a state of being available so if we have all these devices and if they don't respond to our commands they are no good to us so moving on to the attack vectors there are three attacked with tears similar okay this is not similar so political is something that gets add-on added on to IOT solution so physical attack winter is where and an attacker routine would require physical access to
the hardware itself so this essentially means that okay the kind of attacks that fall into this category are like getting a root shell on the device itself and offloading data from the devices local network is something where the attacker needs to be on the local network or your home network when it comes to home automation to carry out these attacks so remote is the holy grail of attacks here where an attacker essentially carries out the exploit from halfway across the globe so this is a brief list of attack surface that gets opened up when an ideal solution is introduced anywhere so ranging from your industries to basic home automation so yeah we can see that
device hardware device firmware device memory or rather hardware and firmware are a pretty unique to one IOT solution and device memory local storage operating system they remain across I mean they remain the same right so we find this even when it comes to our mobile applications right so software update mechanism is also a new is also a new attack surface that IOT opens up network communications web interface mobile application cloud in front third party integration are basically similar to what we do in our day-to-day pen test so what if a device device as we discussed earlier could be an embedded device that is in in any dumb device like your refrigerator washers and so on and so forth so what
an embedded device will essentially have a minimal processor it will have a small and NAND flash storage we are not talking about megabytes or gigabytes here it's odd it's basically in kilobytes so that is an embedded device and sensors can range from anything anything from motion to a temperature sensor motion sensors are pretty prevalent in buildings and proximity sensors as well and temperature sensor is where you saw something where that is mandatory when it comes to your thermostat control and yeah basically that and hubs as we discussed hubs are required to offload the data to cloud servers and this is the only mode to communicate with the devices because they they communicate in a custom
protocol which and none of the mobile devices can at this point of time so
moving on to device security to carry out a physical attack you wouldn't require physical access right so the physical access means that you need to connect to the board via any one of these debug ports it can be a JTAG you are SPI I or I squared C so DS debug ports could be found pretty easily but in a in a production or in a secure device you will you may not find all these pins out in that case you will have to manually go ahead and identify those pins and solder on those to the board and then connect connect your system to those goals so if you can see that a red ring kind of thing so that's what a JTAG pin
looks like often what happens is the JTAG has made I mean the board mentions it to be a JTAG there will be a spring written FJ tag it can be JTAG easy tag on what not so J tag is something that you can use to connect to the board itself this is how you will be you will be able to get shells on the devices and so on and so forth so lack of or TLS that it speaks for itself right so any kind of communication if it is not encrypted can easily be captured by an attacker and they can easily eavesdrop on it and missing security patches yeah so any kind of device I mean breaches happen every day so I
mean no one no one can call their product completely secured so breaches do happen and when a when a researcher comes ahead I mean come forward and discloses that vulnerability it is up to the OEMs to go ahead and bastard vulnerability and send OTA updates so and we can find a lot of small companies that that that revealed that launched products and basically don't offer support they work more on updating or upgrading their hardware rather than sending updates to their current hardware so that is a huge gap there is a huge security gap when it comes to security patches and so yeah in a case that you if you don't have if you don't have from where with you which is the
case when it comes to security researchers so if you have to extract a firmware from the device you need something called as a bus pirate that is the red color boat that you can see on the top right corner so you can use that to connect to the board that you would like to offload or extract the firmware from and so the pink color board is something called as a Jetta you later jtagulator something that one can use to connect their laptop to the device that they are testing so this is how you would be establishing a connection between the PCB and your computer so to usage a tack you later all you need to
do is connect the jtagulator to your laptop via USB and it comes with a dongle kind of thing which plugs onto the board and you'll have to connect the other end of it to the JTAG pins of the PCB that you are testing all you need to do here give the imported that's basically it so you'll have to identify the pins like the B Fifi ground rx T X and stuff like that so generated or something it takes to do all those things for you if not you can also use something called as a logic analyzer logic analyzers tend to be a little on the pricey side but yeah they do a pretty decent job in letting you know
what what each pin does so if it is a 5 volt if you see and it will also tell you I'll let you know which is the transmission pin and with just a receiving pin so that makes your life easy so these two are just an example I mean you don't officially have to use the same device you could there are a bunch of other devices that a researcher could used to accomplish these tasks so yeah you would require a lot of jumper cables you connect these boats to the PCB and yeah if you are not able to identify the ground and be 50 then you will have to go ahead and grab a wood
meter and you'll have to figure it out yourself and as we discussed if there are no prints then you will have to take out your solving equipment and solder all the pins onto the boat so yeah how can the hardware be compromised so these are okay we can see the device you can see a bunch of vulnerability here like both shall be experiential security defaulter blank passwords in secure storage of root passwords and stuff like that so what happens here is a lot of devices what they didn't do is they okay already I have to become one okay so what essentially happens here is that if you connect we are you at or JTAG bones then
if you are if you are doing it for the first time then a lot of devices let you indirectly and they don't even ask for any password or anything and certain devices what they do is they let you go ahead and set the password if you are using it for the if you are connecting those devices for the first time of course I mean when we bring a smart device into our home we don't essentially go and remove the cover and connected to our laptop side so if an attacker walks into your home they can easily open up the device and connect connect it and have a shell access and what they can do from here is dick they
could essentially he pop a backdoor on it and that that's a very easy way for any attacker to get back into your home network at any at any given point of time so as we discussed extracting device firmware is something that is very important when it comes to an i/o dissolution right so okay let's discuss about firmware in the next slide and all this we want to look out for misconfigured all or one durable services okay device firmware is essentially okay we can compare a device firmware to your jar files in an android application so firmware is something that contains all the services and whatnot so if you are able to dump the firmware from a device and and if you
are lucky enough to find that your permit not to be encrypted then yeah you can basically do whatever you want and you've got you could look for any kind of accurate credentials you could look for any doorman service which you could activate and one more interesting thing is that okay whenever a firmware is being flashed on to a heart or whenever permits being flashed on to a device there should be a signature validation but often times you will not find that happening all the time so what you could do is you could you could modify the firmware you could create a militia premiere of your own version and you could just write it flash it onto the device and these are a
bunch of tools that you could use to analyze the firmware liftoff which is been work so been working something that helps you to extract a disc worshipers and the route Efes are basically the file systems from the firmware so the firmware essentially is a dot pin file which you cannot you cannot read directly like using cat or wim so you will have to extract the data from the binary and of course you will require a lot of debuggers and what to do here yeah one thing the first thing that you have to do is I check for encryption and yeah extract the firmware and do that right so go into the file systems look for any hard-coded credentials
you could also interestingly if you come across some I mean I should not say that but if you come across some Chinese Hardware oftentimes you will find some kind of a back door or something I mean which may not be unintended but yeah you may find a lot of those those things and yeah so also look for encryption algorithm so if you find any hard coded keys there then you could basically compromise the communication all the TLS basically and sensitive information sensitive URLs as well you could you could find the admin endpoints or any or any sensitive endpoints to the API is that they expose you could also look for vulnerable services and so on and so forth
moving on to device memory and local storage as we discussed earlier an embedded device would have limited storage because of which due to the all major majority of devices tend to have an SD card so if the card is something that the devices rely on to obtain the firmware and flash it onto the device so the firmware directly does not go into the device it gets downloaded to a nifty car and then get flashed onto the device so you could you could kind of perform mi TMI tag here and control what kind of firmware goes into the device and flash storage as we discussed so there is a technique where you could we had you
could leverage the non storage you could just short out a few pins and you could basically bypass the boot and I mean that that that makes the bootloader to fail and it'll give you a root shell on the hand on the device itself so volatile or non-volatile memory is something that you will definitely have to look at during runtime and after after the device is closed oh my god okay so also be on the lookout for sensitive product information and so on and so forth IOT security is not just hardware security I think we should be able to understand this by now so okay operating system as we discussed so real-time operating systems is something which is
fairly new to the industry and due to this Duty art was being fairly new they do not have a majority of operating system level security mitigations like a SLR for example and because our toes are - because of the operating system like in a 64 KB size you you it's very hard to extract kernel from the arctos itself so water essentially if it is a fugitive version of your bootloader your kernel your operating system and the application itself that drives the device so if you've calls you can use something called as a fifth caller two of the system calls that particular artists uses if it isn't if it is based on a Linux kernel if not then you'll have to
write your own reserve treating is also something similar to scholar it is a little little easier to use and more versatile and what to do here yeah if initially next kernel then you could go ahead and try to exploit any known colonel exploits and also look for misconfigured operating system services so this is something that okay go ahead software update mechanism as we okay so this is something so software update or a firmware update if something is itself a huge gap here because the thing is if you are able to if you are able to bypass these okay if there is no signal validation being done you could easily flash your malicious form a right and if it's more okay
network communications these are the various communications communication protocols that IOT uses at this point of time which are pretty prevalent so Wi-Fi if it be via Bluetooth NFC MQTT and so on and so forth to to play around with the network communications you would require some custom devices like a hacker of one and the uber tooth one is the device that is shown in the right corner so hacker of one is basically used to capture any kind of radio frequency signal so it can capture anything from your Wi-Fi signal to GSM and uber tooth one is used to capture your Bluetooth communications and from a software standpoint then you would require a Wireshark to capture the
packets why I shot this pretty versatile right it lets you capture anything from HTTP to MQ Tyrian what not eater kappa the hitter camp is also a really great tool when it comes to packet capturing and GNU radio is something that you would require to I mean GNU radio basically paid appears with the hacker of to capture the data so what to look for in a network communication is that always look for unencrypted data and you will definitely find a lot of traffic that is not encrypted MQTT these days it is getting encrypted but if you are able to find an older device that uses impunity you definitely find the data not to be encrypted and there is an
issue with MQTT where MQTT connect command whenever the impurity current command is run it sends out username and the password along in that in that request in that request so that is something that you should be on the lookout for and so yeah map out the data flow basically just to understand what kind of data is being sent back and forth from the device and protocol fuzzing is really important so I mean if you are using the custom protocol then you should definitely go ahead and perform protocol fuzzing to identify any vulnerabilities within that so moving on to vapour mobile application so it is our home turf right so web applications for mobile applications have been out
there for quite a few years or rather a decade now and we we basically know what to look out what to look for in a web application or mobile application and these being the okay these being okay maybe application and mobile application is something these applications are the entry points to any of your solution and this is where you you get the data this is where you live how you send your commands as well so yeah we know this and I think we just four d4 credential is an encrypted communication logic okay infrastructure this is something that we discussed earlier so when it comes to huge enterprises then we really don't have to worry about cloud infrastructure
but still and in the recent past we we did have been preachers to Apple cloud services and things like that so relatively speaking of relatively smaller companies they tend to not have all the security medications in place and they even don't have a proper orders going on on their back-end servers so that is an easier way for an attacker to get into the IOT solution so it doesn't it doesn't really impact a home automation system but this plays a vital role in becomes shown industry in an in an IND of failure you tease a kind of a situation third party interaction this is something that a new attack surface when it comes to an i/o definition this
is where I mean Samsung Google and Amazon tries to work to work together work in tandem shared their data and okay this in a similar fashion when it comes to huge enterprises then you don't have to worry about it that much but while compared to a relatively smaller company when it comes to a smaller company the odds were that the third party or the data being shared is not particularly restricted right so unintentional data leaks are something that you could find very easily very easily and code review something that is really important when it comes to an ideal solution a proper a proper rundown of the total source code base is really important here you
to perform the KO tribute to plug all the all the all the security vulnerabilities because this is the easiest way to identify any security a shortcoming so yeah security is not a strip by the process so you will have to keep researching for vulnerabilities and releasing patches for all the identified vulnerabilities because let's face it the breaches is something breach is something that happens every day and we will have to there is no other way to get around it but to activate and fix sixty vulnerability and send out patches so yeah thank you for bearing with me I you know I have been really fast and I couldn't cover most of it but yeah I
will be happy to take any [Applause]