IoT on Easy Mode: Reversing Embedded Devices
Show original YouTube description
Show transcript [en]
to you guys so this is uh a loading screen one second so okay this is uh like I said iot and easy mode this is the outline I'm not going to go through it we have like 30 minutes right so let's just get right into the good details who am I my name is Elvis like before I got into iot completely by accident we'll go in that story for a little bit um fun facts I play games just like everyone else I make music that's really bad uh I enjoy CTF challenges I'm always on ctfs you can find me on free no doing stuff like that I'm also on Twitter as black owl so okay so iot stuff right
everything that we have coming out is like everything is getting the network stack right we have water bottles that can connect to your phone wirelessly and tell you when to drink water it makes no sense but you know we still have to look at these cuz they're still microcontrollers so anyways what kind of sparked all this research was that I had a former coworker that found a nice vulnerability inside of a uh a real Tech chip uh it was because he was running a fuzzer that he created for his uh TP Link just finding command injection just straight up fuzzing just whatever found it in 5 minutes big deal so I was like whoa well let me look at
my devices just like everyone else that's probably here I have a bunch of electronic equipment in my you know my closet whatever I just want to find what's going on so like I said this bug that he found was a big deal so what I did was like all right I have this small Belin device and let me look for this unique string that it's responding with which is BOA HTTP server and it's got this I was like what is the actual attack surface for this for this you know these type of devices cuz I don't know anyone else I've never been to somebody house where they're like hey check out my motem that's connected directly to the
internet no but you know just like everyone else that does research or anything like that we go on Showdown look for Server boa and we have over a Million results cool so this is actually a legit like scale we can actually maybe attack something and it could be a problem so I was like all right I'll start digging into it and so within just a few weeks I found like over about 12 vulnerabilities in different routers different vendors they all went from like command injection passing stuff that was uh from like HP instance over to system uh or stack buff overflows like hey I'm going to do a straight stir copy from this HP header great so one
thing that I failed at though when I was doing all this research was fuzzing just like my cooworker did Ricky had laique uh I fuzzed everything up and down left and right I was doing Konami codes nothing was sticking and it was getting me a little bit upset you know I was trying to find command injection through H every single HP like you know uh parameter everything that was soap related everything nothing was working so what I actually had to do was actually start looking at the firmware itself and so the way I got started and you can get started as well it's like you know everyone's try of binwalk most likely is ever done like any iot stuff
or firmware related uh it extracts stuff based on um magic biter inside the inside the binary itself and you can parse out like the squash of Fest get your binary stting the Ida or radar whatever you use for disassembly and start going at it so but at the same time we have all these microprocessors and if a lot of us are in the xid 664 space we may not know thank you the assembly instructions that go on for this and nobody nobody wants to read a big manual for like mips 32 assembly it's just boring and kind of tedious right so what we can do instead is that we can build a tool chain a tool
kit you can say and have these cross compilers and we can make C code that we know what to do we make C so let's just have the compilers spit out the instructions so right off the bat I'm like all right I'm going to initialize a integer uh variable of zero so we have a zero register being populated into that sack address or frame pointer address awesome going forward like hey 68 in decimals hex 44 argument value one being passed to my function so we also see a z okay when I see a Z being populated as can to be an argument to some sort of function same thing with the second one A1 with the second argument and then we
have the return so we have hex 66 and just like before it's the same uh frame pointer offset for my R value so now we know that v0 is going to be a return you know return value from a function and then we can just keep going like print de this is the second argument again we see A1 so we can use these type of things uh in the 4343 and then also to dig into this I saw this Lui you you are yeah o sorry instructions and I was like well what did they kind of do it's kind of ambiguous right and looking at the in uh assembly like you know manual and stuff
like that it may seem a little bit ambiguous but what we can do when we're not sure about inly instructions is that we can set break points right we can set break points and see it visually so I set a breakpoint at these two instructions I look at the very first value and I step one set step mode on into GDB step mode one and I look at the um Mi sure you know executing the instruction then look at the the output I see that 43 43 is in the most significant side cool so now I have an idea a visual concept of what Lui does do another step one and then look at it
again and I see that or I all right lower bytes cool so now I can start getting like kind of like an idea so whenever I'm looking at radar at Ida I can do manual analysis a lot quicker instead of just looking at the manual and trying to Pig you know figure things out we can do this quicker and faster so okay so we have all these binaries we have all this firmware out there we can probably extract it we can do all these fun things but what's better than just looking at you know assembly like well not really better but what we can do is learn about GPL right A lot of these devices are on the G new
public license and a lot of these things right you provide source code for these binaries so we can kind of take the easy route kind of go on Google and go well how about firmware for this vendor cool I can download the I can download the source code for that firmware and have all the binaries and all the the source code for that so instead of looking at Ida which is a great way we can also look at the source code to get a better idea of what each function does or what we can do to manipulate memory in the fa in our favor going forward I have a TV it's on a GPL great I also have other
firmware for another vendor I'm bluring out vendor names because this is not supposed to be vendor like shaming or anything like that at all this is just the idea that this is out there there this is how you can get started and I'll show you some more the list goes on and on and on so okay so I'm talking about software I talked about how if you have C you can kind of get started off the bat and start teaching yourself the assembly for your Target architecture would be myips arm whatever so your iot shopping list so if you just want to get started you can get started for very very little it says a 100 bucks but
that's everything brand new brand spanking new if you like everything brand new 100 bucks will get you all the available tools that you need to do in order to get hacking right so the first things is the the serial interface it's a ftdi ft232h break up board by aduit it's great it does SPI JTAG ITC uh and Ur it's fantastic and it's 15 bucks so if you blow it up who cares right from there you going forward like you get a multimeter to check for ground you're checking for DC power all that good stuff and then your soldering iron to solder header pins and then your miscellaneous stuff to you know get soldering right as you go on and you
start you know becoming more advanced you're going to start you know integrating and buying more things and the list goes on and on and on and you can build yourself the super lab of your dreams for like over $2,000 and just goes on but you don't need that you can start with the barebone stuff get creative with what you have and go forward if you need to but for most a lot of iot devices or router stuff you only need the beginner stuff you don't need to invest a lot of money into this in fact you can buy a lot of these used except for the ft232h but you can buy like a used soldering iron if you have a
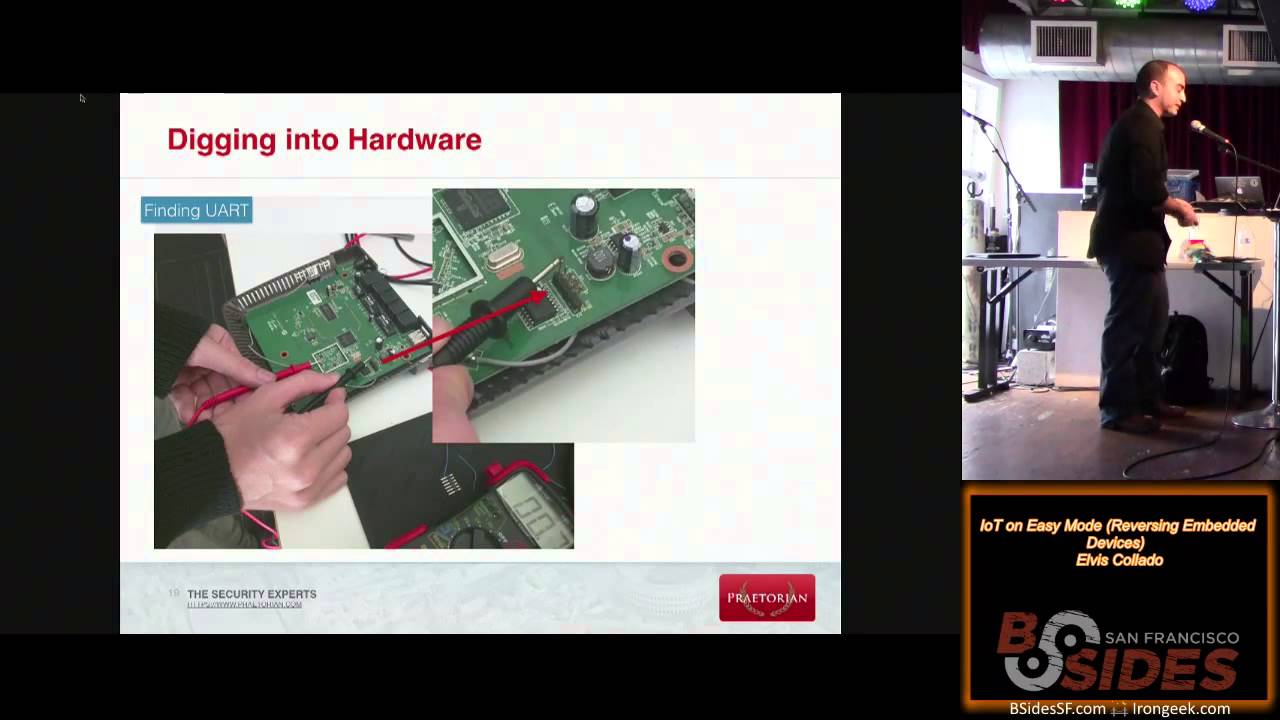
buddy that a multim it's just got laying around you can borrow that you can do it for a lot cheaper you don't need to spend money for this so to talk about the hardware stuff I want to talk about like uart so as a lot of people may know uart is a Serial interface it looks like you just Tel neted into a device or sssh and you got that command line right if it's a Linux operating system so funing you are you can do it without opening up the box you don't have to open up the box if you're worried about oh I'm going to avoid the warranty that's cool you don't need it so every single wireless
device out there has to go through FCC quality ifications right and it has something called an FCC ID you can go on the fcc's website like this and you can find the internal photos awesome they taken this thing apart for me so I don't have to take it apart and possibly cause some damage cuz I'm a little on the you know being careful right so I open up the internal photos and boom I start seeing kind of like a pattern a lot of people in here who have ever done this kind of stuff before recognize that pattern those five pins right there that are not soldered it looks like you are it looks like a sereral interface so let's try it
out so first things first so one things I've done by accident and I don't want anyone else to do what I did find ground first I have plugged power into ground before and it's not fun so you always want to find ground and the way I did it that is the ground pin because with this multimeter it is sound feedback right once I find ground it'll go and you'll get your ground if it doesn't have sound missions it's kind of a pain to have to look at the multimeter and see if it's continuity or not so this is a common ground that I found out as well not everything uses ground like this but you
it's a good start right so once you find ground remember connect ground to ground never click like put plus five or plus three or whatever into ground it's something I'm still kicking myself about but this is like a high level stuff this is just how it works transmit to receive receive the transmit just like a phone call you put up your ear to the receive your ear receives and somebody talks it's the same thing just with computers right but if you don't want to like you know Brute Force around for the the TX for the transmit on the device and you want to use a logic analyzer you can do that too and I can show you how to
calculate the B rate and all that stuff so you're not brute forcing so you're not like oh I'm going to put I found the TX pin but I'm getting garbage and I have to find let me try it again attach screen to this device using uh like 9600 115200 whatever it gets kind of annoying to Brute Force these things but if you have a logic analyzer we can take like a 20 second digital capture which is great but we're going to Pretend We're CSI cyber and we enhance and we get this so what I'm looking for in this entire thing is the shortest width bit right it's the shortest amount when the falling Edge and the rising Edge happens
again goes down and goes up and in this case it's 8.8 microseconds so with that we can calculate and so if we take 1 second over the shortest bit length divided by the you know monc like microseconds whatever it is we can get the B rate and if anyone's ever used a Cay logic analyzer they do have like protocol decoders and there's a serial one so I put my you know 113 636 whatever which is about 115200 right for standards but if I plug in this number right into here and have it analyze the protocol it will tell me this is the word start with the space great so now I know the B rate I know the port
everything else to get started and this is just basic uart and it's very very easy you may come into the future where you have uh password protected your just like you have with talet and stuff like that but there's ways around it as well I will talk about that maybe offline if you guys are interested about booting to single user mode the bypass these type of things or later on the talk I'll also talk about pulling off flash chips that talk over the SPI protocol in order to dump everything that's inside of it so speaking of that so this is my little rout like a little repeater thing that I have laying around the image is a little
bad I apologize for that but just again enhance and I find the the serial number for this this is the mx25 l166 and when you just use Google cuz everything is great when you use Google you will find the data sheet the data sheet will tell you everything about this chip it will tell you how it works it will tell you the commands that it has and it'll tell you what the pins do just like this it's an eight pin it tells me where the power and ground is VCC power it'll tell me where the clock is it will tell me where the input output and also in uh further down the document it will tell me which pens I
have to short in order to get into a particular mode so I can start reading from it and also tell me the commands I can use to send to it over the SPI protocol to be like read this amount of data and send it back and it's very very simple we can also use our logic analyzer so when we just hook it straight up and we just probe to it when the device is talking to it we can verify that when there's a riseon edge or anything else like that it matches exactly this so we can say this is exactly the right data sheet I know how to talk to it we can pull it off or we
can use something called an s soic in this case eight for eight pins uh probe thing for s SOA clip sorry and we can just attach the leads off of it and do everything ourselves we have to be careful with this because if we're doing power we're supplying power to and the thing is off we may break other components it's a maybe but not always so I always like to remove the flash chip but if you don't want to be intuitive you don't want to possibly break something you can always clip onto it this clip is about $6 and it's awesome so okay so what about exploitation right like who cares yeah I have a device I you know can talk to it
but I want to exploit this I want some I want to like you know if I have a buffer overflow I want to exploit this I'm with you so a lot of software out there that you know maybe maybe some binaries whatever A lot of people are very verbose about error messages very verbose over the serial interface so for example this may or may not be a zero dig on something who knows but you can see the return address is now 43 43 43 43 which is all capital C's so this is an indicator of a stack buffer overflow because the return address is being corrupted so just to verify it I can do that as well and if
anyone's ever done any kind of Stack buff overflow exploitations where do you do pattern create pattern offset boom run away right great so you can analyze the crash you can also use something called quu to emulate the binary whether it be a fullone VM or just user land quu using statically you know statically built userland quu in a SE C roote environment but you can create your own exploit but you have to be careful about the libraries because they do shift around so you have to jump by offet but we'll talk about that later and create your exploit if you have JTAG if you have JTAG you win like you like hands down win because you have complete
control over the processor itself now we'll talk more about this so JTAG you can actually have a GDB instance to the processor itself and set break points and analyze everything so you you already win you can craft your exploit right there on the box you're using J tag and it's very very handy if you don't have J tag you're going to have to start emulating some stuff or you can start recreating what the code looks like in assembly make it in C and start making your templates for your rchain or whatever you need to do like if NX is enabled but you can also look at the processor because some processes don't support NX so uh the first thing I
always like to do is always cat the processor uh the processor I'm looking at get the maps so I can know my lipy addresses and all that good stuff so I can R via offset so everything else is on here but the slides will be available and that's all the good stuff but I wanted to show that when you emulate in quu using land quo you can also take your same exact payload which is this is from my uh dvf project Dam vulnerable router firmware and so this is the stack bu overflow one I have a function in here that will call system/ you know bination system and also exit take that same exploit and I change the you know
the pading a little bit but it's same offset same everything and I still get the same output I did was able to hit that function that is not called anywhere else so the stack B flow did work on both the quu environment and the actual device so this is an Arduino zero it uses a cortex processor by arm so there's no memory management on it at all this is when you start running into devices that use realtime stuff they start using binaries that don't really need a full-fledged operating system it does trivial tests like every so Cycles I'm going to check out this uh this uh sensor or whatever so I'm also creating some vulnerable applications for this
thing as well so it forces you to use JTAG so you have to start using JTAG in order to create your exploits and if you do this you will be able to do it on actual devices and going forward this is the jtagulator as well it's a bit expensive and I'm currently working to see if I can make a much cheaper one so people can get into this kind of space without spending a lot of money so this is just a a quick output from jtagulator you find your input your output your clock and it's great you can also test it to make sure that it's the right ports because sometimes with the detag you do get false positives
so with that when you use JTAG people throw JTAG everywhere but not a lot of people like know how to use it so one thing that I use is something called open OCD which is onchip debugger and from here you can create a configuration we can talk about this offline about creating a configuration file so to talk to the processor directly in order to get a GDB instance so when you start connecting to it you'll start seeing that GDB did open I have this certain processor and have six Hardware breakpoints awesome so when it launches the default one for open OCD will open a listening port on Port 3333 locally so you connect to it
127 just Local Host 3333 with GDB for that Target architecture just Target remote that and you'll start getting everything and you can start dumping memory look at the data sheet for that cortex processor and see what memory areas are are uh are for what purpose so not everything you're not going to get a device that's going to use you know null to all FS for 32 bit space you're not going to have 4 gigs so you're going to find the specific areas and you can dump all that stuff and you might get some useful information like for example on one thing I saw the AAS keys right there in plain text and aski in memory and I
was able to pull that down for some sort of protocol I can't go into that right now but there's also a talent interface so you can talk to um open OCD directly and say I want to maybe halt the processor I want to restart all this I want to restart but don't do anything halt the processor and you can start doing like help and it'll give you a bunch of things this is just to get started you can measure the clock you can start your JTAG interface and start launching the GDB instance so okay so we're kind of wrapping up towards the end of this so I have something I'm working on and it's for everybody it's I
got the idea randomly one day when I was inspired by something called it Dan vulnerable web app Dan vulnerable Linux whatever right there's so many of these but I didn't find anything that was a hands-on experience for routers for any kind of embedded devices and since we're like again we're living in a world where everything is getting a network stack which is a b silly my opinion but I'm not going to go into it uh this is one way that I'm starting to bring back to the community to say this is how you can get started for very very cheap you don't need to have this particular device I did have an Old Link say e1550 laying around which is a M32
little Indian architecture and I made vulnerable applications for it it's a real binary that you can upload to your router and it will accept it it will install it it works great but you can also emulate and I encourage people to do emulations as well you can do both ways so and also anyone who's developing for iot and is interested about exploitation memory corruption for their architecture and stuff like that can play with this so for now like I said it's only myips 32 but I am going to go forward and start developing for other architectures and if other people want to join in on that is great as well it's supposed to be for the entire community so this is
where you can download it GitHub awesome you can Fork it you can download it do however you want and I will be posting the source code in about a few days so you can build it yourself so having just the raw binary so future plans I'm going to like I said continue development on dvf I'm going to you know expand it on a bit I'm going to be looking at our TOS based stuff so for that adino zero so you can start exploting things that don't have a full-fledged operating system or a command line interface that you have in serial um I'll be creating blog post on my company's blog which is petoran it would be anything from basic
exploitation to like Hey how do I do this spe stack buff overflow like an x86 jump ESP or whatever right that's pretty basic or anything that does uh use NX and how to like Dr into that and maybe like all right so like I have libc and stuff like that how do I actually create this Rob T for this architecture well I can start showing you if you know roing an x86 he's putting his pointers on the stack I can show you exactly the equivalent of that and I'm going to be writing about that as well but for every single level that I solv for my dvf that I put on the internet there will be a
new challenge out there so this is again it's supposed to be an ongoing thing people to learn about exploitation Hardware stuff the complete hardware and software stack and I'll also go on to like future stuff cuz I believe the FCC just came out a few days ago saying they want to start hardening firmware they want to start locking down these things to make it more secure y y y and also this Hardware protections like the silliest ones I've seen is where the JTAG Trace outs when you look at the pins um are just cut so you can just put like maybe some continuity there boom you got JTAG or they just completely disable all together but that's another
story and once I dig into that a little bit further I'll be posting about that so you guys can be more aware and also be having more fun with your Hardware so and again anything that I find that is electron if I go to like fries or any kind of like electronic store I'm I'm buying it I'm destroying it I'm looking around that water bottle I'm still on that waiting list from Kickstarter so it's going to be some fun stuff and I want you guys to also get involved into Hardware hacking especially if you're interested don't be intimidated by Hardware the easiest thing you can do is go to Goodwill and they have routers out
there for $5 $2 and they're like current routers like current lynxes Netgear whatever Asus and you can just buy these things and take them apart they're $2 break it who cares right start playing around with these things and then they take it to your more expensive products that you want to take apart as well $400 watch or whatever it is you can do these things and it's very very easy but I'm going to provide the hands-on experience so you guys can learn from it so just writing about blogs that people can read but not actually do so again I'm going to put this online and everything else so these are like the hardware stuff for
the beginner stuff where they buy them all that good stuff there's blogs out there to get started um I'm always available on Twitter as well so you have any questions concerns I'm always there to help out I will not hold your hand for exploitation or anything like that I will point you in the right direction that make you learn so that's my promise to you guys and this is the end of my talk so any
questions uh yes the guy in the back huh I am planning that for uh possibly by the end of March so I'm making sure I got my sockets and everything already and they're working great and I make sure I can create exploit for it so I don't want to send something out that's like hey yeah it's vulnerable but I can't exploit it that makes no sense yes what what uh JTAG debugger do you normally use do you do do you use the 232 what do you actually use for your JTAG debug so I use so for my JTAG interface I did use the ft232h if you heard of the shiker as well that does that it's the same ftdi chip but I use
that as the interface any more question questions concerns comments cool thank you okay great thank you i' just like to thank you for sharing your valuable knowledge Elvis um and on behalf of uh uh bsides and Fitbit I'd like to give you a Fitbit oh great thank you so there may be an exploit for this pretty soon stay tuned and please do not leave yet we have an announcement to make just a quick announcement so in about an hour we have we actually have food downstairs there's going to be an open bar but you need to get drink tickets first and then we're doing a raffle for a pair of high-end Beats headphones so if you haven't gotten a
car to fill out I think there's probably maybe 125 of them left you might want to go do that after this so thanks for coming