Hardware Hacking: DVRs and Dildos

Show original YouTube description
Show transcript [en]
okay folks that's us good start right so many of you will have seen Cain on TV heard on the radio he has the cane Monroe show this could be very interesting so here's our closing keynote please welcome Ken Monroe I think this is probably the bravest we've ever been with a demo before we've definitely been winging this one in a big way well it will work yes yeah the chance of this go to plan are very limited but anyway it's gonna be fine um so as many of you probably know we spend a lot of time doing hardware hacking reverse engineering firmware extraction that sort of stuff an area of great interest for us recently has been
DVRs I'll explain more in a minute but some what I thought was most amusing is how these skills transfer quite easily into other things and thingies and I'm sure some of you have seen a story in the press over the last couple of days which put an interesting thing which we're gonna go and talk you through the whole reverse try and do it live hopefully we'll get get it to pop and everything and we'll be good I'm sure it'll be fine anyway I'm gonna start on the safe side of this I would say this talk is definitely not suitable for work then it was like to be offended now is the time to leave okay anyway so I'm
gonna start with DVRs it's scenario that's introduced for a long time back in February last year we started looking at DVR EMV power DVR it's a it was about 28 quit or find us in really cheap chips chips worth buying just have a play around with and what I think frankly goddess about it was just utterly utterly insecure it makes someone later DVRs the ones that are fundable to me I look positively secure this one for example use you PMP opens put in 80 inbound from the internet there's no telling it on it buttburn mind we're talking about before where I came out so no one was really looking at telnet port 80 embarrassment public Internet okay
lack of encryption a bit of a problem there it had a webbings face but we thought great what the first thing you do with a web interface have a look on show and found 44,000 of them I think so out there on the public internet guy okay this is we're spending some time looking at them so started poking around a bit and this is where the train wreck started to happen the webbings face has authentication username password if you need to authenticate all you do is you change the cookie values to anything anything and it authenticates you it really is that simple which is just thinking wow so from this point you can see people's video feed to see what the
cameras are seeing yeah pretty invasive but perhaps not critical but then it get really bad because it's got an inbuilt shell command so from the web interface you just type the pen shell and your command so you've now got Bri shell oh this is getting quite serious isn't it so now we've got a potential pivot point on to the customers network and and we thought this is just about as bad as are gonna get but it got worse yeah it actually got even worse than this which is really quite scary once we got the firmer often started looking at in some real detail we noticed an email address in there Laura's here at year dotnet and we started looking at the
phone we're seeing how it's working and realized that every six seconds it was taking us still of a video feed and sending it to that mail address Nikki why oh this this is quite hard cool now the credentials for no account were obviously in the firmware and someone took that credential and authenticated the mail account and found all these stills as well now we choice disclosures we tried quite hard it was a bit of a pain in the backside and they didn't respond to us so with his stuff it yeah we waited the obligatory period of time and disclosed and then we got an email from him in response to the email we sent several times previously saying you
know why won't you talk to us yeah he asked us take it down changed his mind yeah all set to take take the post down okay reply to us before but it was pissing yourself so we decided it would have some fun with him and stream the introduction to button moon frame-by-frame to it it was without the audio so he did miss out the feeling but but in fairness I think it was accidental that this email functionality was left in he claimed it was pre-production but we got it from a production box so clearly there's been some mishmash going on there and some of the devices that were out there sold in public had this functionality and we're
shipping stills from your CCTV out to this third party which is just a train wreck in Ewing yes it's the worst security I think we've seen anything yet but course that got us interested didn't it so I'm sure everyone here knows all about me right that's where things start to get more me more interesting um that blog by the way the envy pair that we put up was the most hip blog on our website by quite some margin yeah until until me right and then it still something happened this week anyway um a few points I want to clear up about me right there's been a lot of misleading information there's been some amazing work and a lot of kudos goes out
to Brian Krebs and some people who worked with him did some really cool stuff got the source code analyzed the credentials but men made some mistakes when they're trying to attribute what the differences were that mirror was exploiting and I think what they did is they looked through default credential sets and matched what they saw and then that must be a device so what that led was a lot of people thinking that mirror I was actually about things like printers Reuters IP cameras VoIP phones routed all sorts of crazy stuff it's not me right is all about DVRs now we went through that list and spent some time filling in the gaps and correcting things so for example there's a two-way
speaker there um Evie said LX and I think the attribution that got was the password said l XX . was the root password they didn't make the connection correctly actually it's terrific evaced DVR and that's when we demonstrated about six months ago yeah live on BBC and we've got to go through dysplasia but that's another story yeah they weren't very happy about that but actually if you go through the rest of the default potential sets you see actually it's all just DVRs me right is DVRs nothing else there are a few cases where applies to CCTV cameras but that's where it's not all in one CCTV camera and DVR the price that is exploiting the
DVR help the process that's the one is going for so just a bit of clarity there now we thought we'd have some fun and see what else we could do so we went out and spent a stack of cash on over 30 DVRs some new some secondhand some 20 quid some 2,000 quid so a complete range what we're interested what do you mean I actually miss because what are we loved about Mir I was it was beautifully simple the exploited d4 credentials over telnet great fantastic how utterly straightforward we wanted to see well if we were preferred to spend a bit more time what else could we find and the list must it's still growing is
stonking so we found DVRs that were vulnerable to me right but no it near abouts we found extra credits over telnet extra root creds that telnet could have used but didn't so you could actually make me I'm more effective we found DVRs that if I had used telnet put put on a non-standard port so 10 20 30 for example so mirror I could have optimized itself that way and we also and this is quite scary so mirroring doesn't persist beyond the power of reboot so you pull the power and their eyes gone and along the way we found a route to persistence and read you want to talk about that yes so then I wanted
to find a way to fix me right because the problem with these is you can't update the firmware there is no firmer out there for these so I thought I would find a way to fix that and I did find a way to fix it I can't really discuss how it's quite hard to find but the problem is if we release it the guys who arrive mirror I can use that to persist on the boxes so if they come out quicker than us to repair the boxes and we can just tell users to do it we can't actually do it ourselves they're going to gain the upper-hand so we're kind of in this quandary we
don't know what to do that's interest yeah so we can fix me right but in releasing the fix you make it persistent that's kind of bad really but we found a lot worse than that as well and this is still ongoing we're still halfway through the project we found a lovely shell over debug we got directory traversal and a low buffer overflow which we think is going to lead to a nice wearable remote code execution get in so that makes me write one shedload worse but the bit that made us laugh as a few vendors have integrated DVRs with home security systems and we've seen cases where you can actually use mere I compromise the
box and then disable your house alarm I lock the door because some of them is great locks as well so you can unlock the door turn the alarm off and delete the CCTV it's just bananas like wow this is just fantastic so I guess you go through disclosure on that bit with the vendor at the moment so watch this space um and then I think one thing that just blew my mind is you're probably aware of the involvement of can be called Zhang lie now Zhang lie build the the firmware that runs on all these devices they got a quite a bit of stick a little while back and quite rightly so now song by XM
they also do the ability to see your CCTV on your mobile studio mobile app so you can stream your footage that's called the XM I now we found this list of daily changing su passwords on the Internet so you can compromise certain DVRs using XM I system just by knowing that the one-time daily password Wow now it's a one-time pad right and that's always been the problem with one-time pads is transmitting them putting them on LinkedIn isn't a great way of doing it we found this on a Nigerian CCTV cameras installers feed on leaked info really Wow the thing is even if we hadn't found it like that reverse engineering the binary that does the
authentication would have uncovered the same issue so it's bad around yeah it's just a train wreck isn't it and I think I think where things got really interesting is is starting to realize that actually Zhang my a fundamentally responsible for almost all the mirror related problems that we see they got very strong when they were first accused of having problems with the original telnet issues actually we think Zhang my responsible for the whole lot that's our perception anyway and that's really because we hit upon the mother lode I think Andrew you should explain this yes so my house is just a stack of DVRs at the moment and I was looking into one particular one the one just sat down
there and at Google the serial number of it and this page came up with Quito X M 0 3 0 and this is X end wiki for development and it contains a lot of really quite GC information now it's all in Chinese which makes it quite hard to read but we found this this thing called the it's a repacking tool that takes the firmware and customizes it so it gets your logo and it puts it into the binaries it changes the telnet password and this is the thing that's joined together xn through to all these different vulnerable DVRs I think we should try and reverse one life yeah and so I think we're gonna show you and some stuff we can do with
one of these DVRs now this is all going to be live which means it's probably going to go very badly wrong so what we've got here is a DVR and it's an ARM based machine it's got quite a powerful ARM processor on it it's got RAM external flash and so on and the first thing we do when we get these boxes we want to get the firmware off of them because if we can get the firmware we change a black box test where we can't see inside it into kind of gray box or white box and this gives us a lot of power and we've got so many different ways that we can manage to get the
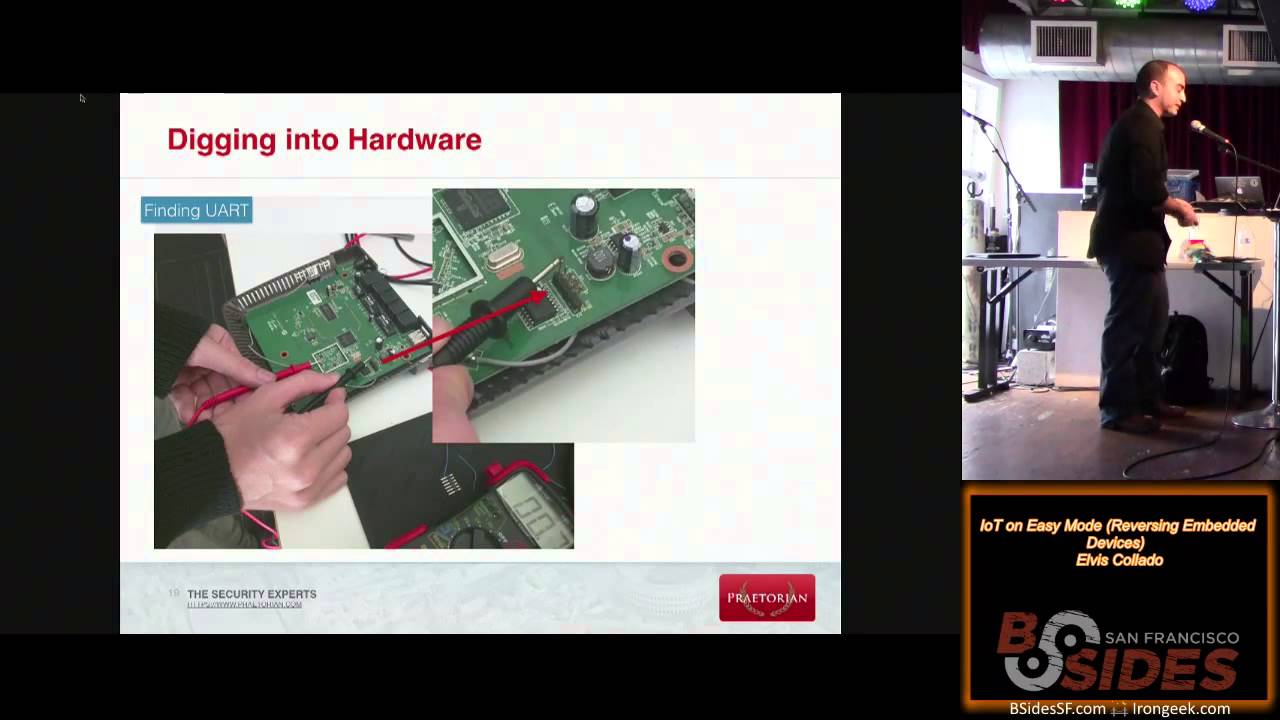
firmware out the first one and you see this on Reuters loads of embedded devices is a serial port and that actually gives you quite a lot of power I'm going to jump through - well first off I'll show you I'm here and what we've done is we've connected a serial console so it's just three wise transmit receive and grounds going from here it's connected to a BeagleBone black which just receives the serial when we come through to the right terminal window
we're already connected to it I'm just going to reboot it so you can see what happens so you immediately see stop coming out the serial port so the first thing that happens is you boot which is called the bootloader then it starts loading the kernel when we get to this stage where it's actually loading the kernel the serial port shuts down so this is closed off our access through to the device and which isn't very helpful for us we can't get a root shell and but there's ways around that we can still call the thermos so the first thing I'm going to do is reboot it but this time you'll notice it says press control-c
and to break out of you boot so if I press it at the right moment lots and lots of times we get a prompt come up this is the e boot prompt then type help gives us a nice list of commands it's a bit slow because it's cereal and but one of the key ones is memory display and what that does is allows us to dump the flash memory through UV so what we do to get the firmware we can't recover this through the serial port we reconstruct this ASCII representation the thermo takes several hours and we've got the firm off of the device that's just one way of doing it loads and loads of
devices don't allow you to do this though and we've got other routes into the device so the first one I'm going to show you is is the obvious on the Murai crate so we've already got the mirror i creds here and some of them are a bit weird we still don't know what that bottom ones about to be honest and it worked on one of my honey pots but oddly so what we're going to do is a little tool called Hydra and you can give it the creds give it the IP address in the protocol let that run that it will try all of those credentials against the device and hopefully in a second it will tell us what the root
password is and it should be back up again I know it won't be thank you oh good I'm glad someone's on the ball and so yeah once wrong to the device to telnet we can recover the firmware so should just take a second to come back up again thanks for the warning on that those it could have been there for some time they're probably gonna be there for some time and we do have other attacks we can carry out against it and I jump through to one of those actually whilst it smells it's beating so and what we can do is we can carry out a glitching attack when you can't just press control C in you boots to escape after you boot
we can perform a glitch so we let the device load you V and then we stop it loading the kernel and it's really easy to do that all we have to do is pull one of the member the data out pins on the memory chip down to zero we pull that down to zero the right moment in time it can't read the kernel but it can read you boot so I'll show you how that works and this is probably gonna be quite challenging to do this life change it's the presenter so you can see what I'm doing there see on here is a flash memory chip this little black chip here it's got 16 pins
on it the lower-left-hand pin is the data out that goes back to the processor and to glitch it should be quite easy what we need to do is connect between that and ground and it will allow us to break out the UB console without doing anything through the serial port so we jump back to here I'll just show you it's booting still so you can see that's the normal boot there and it will normally go to uncompressing the linux kernel and all I'm going to do I've got a multimeter here it's just got a direct short between the probes and I'm going to short between ground and here at the right moment in time which is now takes
a second and you can see we've got the prompt again so this attack by pulling that pin down to low it's stopped the kernel loading and we've got exactly the same situation we had before so you can read the memory arbitrary memory reads you can dump the flash and so now we're going to reboot it again give that second uh T and now were just going to show how you can tell MIT into it and we can still get the firm off of it and it really is key to our jobs in attacking these devices to work out what's going on with them to be able to get the firmware and this this change from black
box to grey box right wait for the beep yes so you get really annoyed by the beep on these every time it reboots it beeped and it would be fair to say and I've made this thing beep an awful lot during its sad miserable short life and
it's also got this annoying habit of changing IP address
come on see if it's just gonna respond to night live demos thank you love them it's been 257 that's why it's not working right so we'll do the mirai crate so it will try doing them and there you go within a second after you're competent enough to actually get the device booted you've got roots and the password XC three five one one and and of course it's really easy to just turn it into the device at this stage so 1042 0:57 root XC three five one one really onto the device so this is exactly how mere I was now if we want to get the firmer off of this device we've still got a load of different ways we
can do it and the box has got a USB memory stick a USB port get normal USB memory stick it will show up so just run the message and you can see we've got SDA there just a normal disc we can then go and mount this and we've got access to the USB memory stick that you clearly see I've used before and to get the firm off of it it's really quite simple we just do a count of one of the MTD devices which is the memory in it sending to a file and now we've got MTD block five that's part of the firmware onto the USB memory stick unplug it bring it back to here now that's quite
useful and what we can't often do with firmers unpack it using a tool called bin walk and try and find vulnerabilities but we wanted to find some really deep vulnerabilities that looking at code and scripts probably wasn't gonna give us what we quickly found was when you were looking at this with Burt as we found a buffer overflow on a get request to the device so a very very long get request will cause it to reboot so this is clearly not a good thing but a denial-of-service buffer overflows not that interesting we want to turn that into an exploitable buffer overflow and that can be really quite difficult on a device where you don't have the oversight to be able to see you
know view registers like you do on a traditional machine so what we do is we cross compile something called gdb server so gdb allows us to get debug access onto the device now this really has the potential to not work so we'll give it a go though so what we're going to do we run gdb server and it's going to be running on port 1 2 3 4 and I'm going to attach it to the already running process which is called Sofia Sofia is the root of all of these problems it's the binary that does the web interface it does the debug interface absolutely everything so now we're connected there I'm gonna start gdb I'm gonna connect to it and what
happened is it seems you start gdb it will stop the code executing so now the web server and this device will be unresponsive so if we retry going to the device on 57 nothing will happen it just won't work and so we come through to GD beam which press C and it'll continue now if we come back we've got the web interface come up on the device so it's pretty simple to do that and now we can exploit that buffer overflow and actually see what's happening so what we're gonna do is just give it a really really really long string yeah that brand names not there so lots and lots and lots of Hayes days
as the standard character it'll ask us to download a file the second time it won't work if I come back to gdb it says it's a segmentation fault so it's crashed due to a bit of memory being accessed that shouldn't type IR for the registers and you can quite clearly see how our sixth root our 11 a replaced with 41 the ASCII rope intention of a so we've got arbitrary overwrite of registers the program counter isn't showing faulty ones because it's actually moved several steps down the chain off to be overwritten it but let's just say we're quite a long way through getting this into our c e territory at the moment explain about a male yes so we've we've
been looking at this XM site they don't just make products like DVRs and stuff they make other kind of household alarms or things but this is really weird on that we can't quite work out what it means they've got this whole range of products called look at the mail so I was giving you a insight into some of the crazy things you can do to get firmer and I thought will be quite good fun was show all this hard core work that we've done on DVRs and so how you can actually use basically the same techniques to get persistent rope remote route on a sex toy yes anyway let's start a few years ago we did a bit work on a few sex toys and
we started working on this room still events and I was a bit shocked to discover actually the field of teledildonics is quite a quite a big one it's quite a popular market the idea being is that you you hook this up to a mobile app your partner you want to communicate has another similar one that like this and then and then over the Internet's using a mobile app you can control each other's thingies and that's yes anyway and it's I was just a bit fell of its soil this demon understanding these these thingies existed but I felt fair enough we need to go and do a little bit research and figure out what we can what
we can find and so the first major issue was that you can actually take stills during this process okay there we go yeah so you have video streaming live and then it can also take stills from these things and one of the things that really shocked me I'm actually started playing around was there's a process that some takes the bitmap that the the mobile device takes and then renders it into a jpg and in the process we just covered that during the rendering procession actually creates a temporary file in the SD card so the emulated or sometimes physical SD card so that's not really good idea because that means that other apps can access those temporary
files they're not remove properly which is really pretty worrying as for I think anyway um but the bit that made me laugh even more is it's got a default Bluetooth pin and four zeros so you could in here if you wish to go out driving and attach to people's dildos and take control of them but we this mother things you do once you've got access to you can actually you can drive it over a Bluetooth serial port so we had some vibrator races in the office a product you Cyril that was quite fun and then there's this the other end of it as well so we were initially working on this same because that's that's the
super for work side where we're trying to get the farmer out of it well anyway and then Wayne's the other in now obviously that there's a sheath in there which obviously is removable obviously
one of my colleagues not and raise you another one's called needed to get the innards out in order to get so on the chipsets try and pull the firmware so she shoves his fingers deep into pull it out at which point wouldn't want other colleagues tends the Bluetooth seal interface on and inflates its reached they're stuck he's running around the office two fingers stuck but the reason why we came back to sex toys because Frank that was a bit of fun that we did two and a half years ago is you've probably all seen the issue around we've had two researchers presented at DEFCON in Vegas last summer met them both follower and got milk both really cool
Kiwis and what they discovered were a shedload of security flaws but the one that gang she got caused trouble was a previous invasion issue because the manufacturer of the we-vibe device was collecting usage data and that's kind of fine now how do people use it how to improve my product but they're also collecting location data email addresses and other things so they actually could correlate that data to individual how he used it when used it who you were and where you lived and that kind of the yeah there was a class-action suit that it's settled last week I think for 3.7 million us so I think that brought everything back to the for now I had
done just yesterday had a quick poke around and have a look at some of the permissions these devices were using and those the Lovings ones events this one that also has approximate location okay there's no specific location it's approximate but the one that got me is this is a copy of the permissions from the we-vibe we connect app from yesterday this is after they settled their lawsuit and they're still collecting location data Wow how much you have to sue these guys to get me to update their apps unbelievable but anyway um this is where it all gets a bit grim stop it so I want to share hands here has anybody not seen this story okay all
right this is for you okay Wow I've been hiding this is probably singing the most grim device I think I've ever had the pleasure of encountering it is absolutely horrible this is called the Syme eye and it is a dildo camera vibrator ah yeah that's all that's what we kind of said so yeah what what do you do it it's called this we're not sure we it comes across a sigh my we think actually sly might be better but yeah so anyway it uses Wi-Fi there's nothing wrong with using Wi-Fi that's fine it needs to use three video so Bluetooth probably wouldn't have enough bandwidth but what's weird and unlike most IOT Wi-Fi devices is it works as a
wireless access point not as a wireless client now unconfigured you've expected to be AP you configure it and flip it into a client so you can join your other devices yeah but it acts as a wireless access point and it stays as a wireless access point and that comes up with a very interesting feature and that you can use wiggled on there to find them so you can go and find people's dildos them they're only actually a couple I found on the internet so far but that's in that you Harbor a district of Tokyo I think that's probably a sex shop but I'm waiting for more to pop up as we go that's one the really unfortunate
problems with using it as an AP the other really creepy bit so as an access point it has a PS k the PS k is a Tate's what a surprise the really freaky bit is when we started pulling apart the mobile app things started getting a bit weird so hopefully over here I've got it and the sy my app have a look at the claim of some of these classes winged cam sky Viper what has fundamentally happened here is there's been a serious case of code reuse this is a dildo camera that thinks it's a drone believe it or not they're actually propeller and motor control classes in the the same the same apk which is just crazy so we're doing a
video I don't know throughout anyway whatever I actually managed to get some somebody put me in contact with the guys of sky Viper and they were amused to say the least that then brand name was in a dildo camera apk it turns out on chattington was actually quite an earlier version of the camera manufactured for them by company called Shenzhen recan and it looks like they'd actually asked the camera provider to write the code for them so they didn't I own the IP to the code which is a real shame because they couldn't actually do very much about it and went a little bit further and pull the apk part of it a bit further I found more so I've got an
IP address so it's working he's an AP so good TsUP 102 once you take one one great port 80 fantastic using them a twin password blank gets in what could possibly go wrong at this point Henry everything found that and yeah so we actually connect to it I think it'd be fun yeah I need to get it I need to connect it via Wi-Fi yeah this is running yeah most useless battery life by the way she's real issue for a sex toy to kiss vibrating sex to it see if you can get up yeah we're up yeah cuz I'm already connected pop up in a browser there you go image stream fantastic no you guys so you can now see it's a bit
difficult sitting my fingers ideas you fine so that's all great so we've got a stream coming from it now so you could quite literally go and find someone's dildo using Wiggles sit outside their house jump on concurrently except multiple concurrent connections and stream whatever they're streaming yeah nice a just lovely but that was frankly just too easy let's see if we can go a bit further can we get a persistent root shell on the dildo oh yes this is where it gets quite fun so I'm not gonna go into real detail on this because we've scripted it because it had no chance of this actually working for real life and it's got loads of functionality there's
a Lowe's another crazy stuff to show this is how it working yeah I'd say have it didn't see and it's quite a weird device I'll talk you through why it's got in it that's just an jump back to the presenter yes so you can see it's got this little Wi-Fi board with the flash memories on the other side of it and you can see down the bottom here we've soldered pin headers and she's got a serial port almost exactly like the DVR and this one I learned one thing never give your dildo to Dave because this is what happens to it when you give him one yeah we realize actually you had to actually take the outer sheath off on
[Music] what you have to do to get the faculty Kappa cheaper he actually needs to basically circumcise it around here now you can slip down the back and then you can peel the outer sheath off and rapport screws on there which is great it works a treat yeah it still works amazing yet still what a pinhead it might be a little painful I don't know Oh No so started playing around with it I found all the functionality you'd expect of a drone camera fantastic so I got everything we need loads and loads of functionality below the functionality could effectively be a wireless access point as well couldn't yes everything it's got motion detection and can email
you when there's motion detecting at sea being useful yeah very um spend a bit it to my playing area what she went through the entire firmware we monitored over you are spending quite a bit time playing with that it was quite difficult to actually mess around with the Wi-Fi MAC points sister Shenzhen recap that was great that's pretty obvious CGI's were playing around we've got all the documentation found them but we couldn't get the firmware off it one thing we did find from them was the ability to bring up telnet though so you sent that argument to the CGI script it'll bring up telnet we think fantastic Mirai off we go on the dil they great um brute
force tip nothing was working we could not get that brute force password to go so we're now stuck we now had to strip the dildo down a bit get some test tips on us a couple of app ads and scrape the firmware from it and that's where things got a bit interesting now it took about 30 minutes to get that firmware off it on there using a bus part but what really made things awkward was that the it was no sector parcel it was a different part of the story because one of em was that it's in nvram which is stored in a different place so yeah we can get him yeah quite annoying at this point we
couldn't actually get all the way in but got lucky my colleague was playing out he was monitoring you up whilst sending stuff into the web interface and he found an injection point which is fantastic and the point we got to was here what you need to do is go into the hosts IP parameters and the NFS settings in the on-board access point and if you start passing a couple of weird arguments to it you actually start getting mal problems you get the filesystem dumps itself and you get the contents of it set to password fantastic now we're in a good place stuck it in there the brute force file we couldn't group they and the telnet
password we have stuff we couldn't get there however we then Russ everything's running his route he'll just wrote a new route user into etc password and was sorted in a much better place now yeah bit annoying once we actually been through the firmware correct it for route we discover that the root password has actually recant for debug which is why we didn't get it which is a little bit annoying so what we're going to do is actually carry out this exploit now and it does take a little bit of time to run but once it goes it should open browser window that shows us the video and and well you've taken it over and we
can turn it into it and do what we want to is it's crazy for a device that doesn't need this functionality in it it's just that no one is really oh there we go it's gonna take a little while to it takes two or three minutes to actually get it to pop but we've now got effectively a persistent root shell on a sex toy which is just utterly nuts while we're doing that I'm gonna talk a little bit about the disclosure process we went through so we sent one an email it was Christmas Eve but that's fine you know what else do you do on Christmas Eve other than exploit until days I don't got enough no response to that
even though well into January we tried them again in mid-january we've got absolutely nothing back from them again we tried them again got absolutely nothing back this standard and your customer service just want a response guys and they're just ignored us which is probably many of you very familiar with this is a very common issue and we feel it's tough yeah you know this this is just getting too silly now it's not good it's really not good it turns out that actually one of the reasons they didn't get back to us in January's because they're all at porn conference apparently that's that's what happens in the adult toy industry it does take a while to pop this one
unfortunate over go yeah it's not a it will come it does work then just took the world there you go fantastic and right so what we're gonna get here lovely persistent reassure we're waiting for the video extreme to come mister air it out or is it coming yeah it's just a little bit slow so yeah now now we can you know use this to see what you want it also makes a really good chicken I might get a weird look at the officer I don't know but some of the other things that are actually Co interesting in that Rochelle and you want to scroll down a my boundary which is top to down so you couple of interesting things in
there yes case it's got email capability it's also killed the ability to Skype which is quite something and then the free dessert it also what's the address it also sends data to a Chinese IP address that address appears to be offline now both but yeah it is important to note it doesn't connect the internet so it's like it's functionality that's completely unused but it's in there that's the weird thing yeah that's just beyond grim isn't it I just find that quite creepy right she will test the range on it I could do yeah now is anybody want to take out to the back if anyone's okay really if you've got one of these who's gonna admit to it we've put the
five per ticket for our website so you can see it there and how the exploit works a couple of useful resources so internet of dongs is an interesting website actually it's not ours it's run by a guy called cool uses hashtag the Twitter tag render man he does quite a lot of research into sex toys and other security he's he's trying to get the industry to up its game he had a bit of go at me but we get on the blog's up there as well that's fine you'll find everything you need to know to exploit the sex toy cost two hundred and fifty US dollars you can buy it on amazon doctor at UK they are in stock with a
couple of points is I never thought in all the tour the research we've done into iti would ever put the words dildo and camera in the same sentence but that's what happened but anyway that's us that's Andrew at the top that's me that's company that's the blog there's loads and loads of IOT research on there loads of great advice as well the blog is broadly suitable for work apart from the top story on the blog today so if you are yeah in the office I wouldn't recommend that just right now anyway thanks very much any questions
and we tend to disclose by the blog and the I don't know if anyone else's experience getting CVS at the moment seems really difficult unless you go through certs because of a difficult disclosure and bigger impact fundamentally the impact of this isn't that big so getting a CV for it they just don't respond if it's there's a lot of systems exposed they do we do have some TVs for stuff that had bigger impact but not much yeah it's tend to be IOT devices are relatively small markets say yeah yeah I agree I think it should be I think I think the problem is it I think certain area for whelmed with volume of submissions right
now particularly round IOT because it's just so straightforward in many cases any further questions out there no one else got the questions out question about a sex toy there's painful not on my Amazon account you could see my recommendations yeah that bloody thing out the house I did have a music in snack - yeah my wife dropped the kids off at school after I've been out doing a talk late at night and I just left my gear in the car she parks up at school and the Headmaster's office is right outside the parking spot opens the door in this falls out quite odd isn't it yeah any further questions fado has private questions they'd rather
not share of public will be around for like self an hour Thanks