Who uses LOIC these days anyway

Show original YouTube description
Show transcript [en]
we're going to get going on the final final talking here on the roof rack they're also talked about doing lightning talks afters and we're not sure whether I signed up for them there's a couple of tops been listed but we're not quite sure the series hang around think so Mikey doesn't to say then the floor is open after his talk so and this is a final repeat of today it's not what pins from him to do our way too much well startle you yeah yeah kind of apologizing for the fan base I've got the back apologist so here's no I know I'm kind of these days and who might and so I started back month ago workin for
EM you are my new managed services called concept don't look there and I'm a graduate of stash you need I did a degree in cosmetics and security as part of that a dissertation fun of your project I mean put it on the evolution of D dozen tanks which is kind of where this talks kind of stand from I also did an industrial placement of glaxosmithkline firewall engineered is complete as a bit there so I've kind of got a little bit of an idea an industry perspective so another little plug cyber challenge everyone who hasn't heard of and fantastic opportunity for anyone looking to get into the industry and there's always a kind of drive for
getting people involved in a challenge so do check it out and send me the white rattus which is the CSC and a random and so quick agenda by the last different tax motives and then prevention education and finally soaring so what is a beam attack and typically people have this kind of misconception that people may be done what they're doing its scoop kitties and kind of performing some kind of cyber attack and quite often the case that is quite often that is the case I'll similarly kind of upset person that's trying to do that someone or just any of those other Scottish throw in as many as I can and and typically that was all results in this car
here's a little bit disappointed that their favorite website is gunned down that sound we can't on the mikado pieces that are quite following on for Manchester so essentially d does is attack of Vale ability and so if we look at the cihr mob is attacking availability it's one of the best and potentially only in the text you can do on availability so how well we'll get to that but why well D does this massive loads of hopefully most of you have heard of the dustiness attack so I'll growing and if we look at this map it kind of shows us that over time the size of Jesus attacks are massively growing if we step back ten years these are tax
inside terms of size wouldn't nothing because it's only been really over the past two or three years that they've massively catalyzed a bro but people always kind of think of Jesus tax in terms of size and that's not always the case so if you look at the media you've got all kinds of new stories about massive ddos had broke the internet and except it's always kind of concentrated on size so they did to the tap map it's a fantastic resource through our best friend telekis cloud and google and it shows with real time and he started d doesn't ask and i went on the other day randomly just click today's took a screenshot and we've got a reasonably
and substantial ICMP deed us on through no idea why someone's attacking through I didn't go into and investigate it similarly is a must lead us there on the US 23 peewit seconds and si UD p image is so if you combine that with all the oven dealers attacks that are taking place at the time you probably are closer to Inga bits with Dino's traffic which is quite a lot but like I said it's not all down to the bandwidth it's not all down to size and sometimes the more strategic normal tactical approach is effective if we can cleverly left attack to our target we may be stealthy movement meeting so that you can't exactly be the
target doesn't know that the attacks coming they didn't get away with something else so historically bandwidth was limited and they might been hard to the tap because obviously getting the bandage was harder and also defending it's harder to get the bandwidth and stove actually mitigating was much harder but they were also attacks on often misunderstood people was just going into the violence or idx yps systems and upon the go away there was a lack of dedicated service providers and a lack of dedicated and eNOS mitigations hardware and it wasn't really until 2006 that is outlawed so there was a number of cases before where people who were going and performing these t-that's attacks and nothing was really happening
out at the back of them and kind of after 2006 things will start to pick up wherever you're actually in comfort and performing these do those attacks so I'm going to quickly run through the three different kind of types of attack if you go and speak to different vendors the law give you different kind of catalyst how to categorize them and but these are the three that I chose follow the research that I did for my money in project so starting off at the top you've got a volumetric attacks these are the bandwidth bastes attacks this in which everyone and mostly is loaded up is you floods you send a little loads of traffic to a target in the hope that we
can fill up the pipes and noted it in a trap and get through the letter said couple of slides back if we really more stealthy or even wants to teach it about things we can use protocol attacks or application text where and if we attack them to my protocols or the actual applications we don't need a lot traffic so volumetric attacks that's an element we'll all head up I simply floods videos univ influence and then we take another step further so we can say election taps Beauty p.m. repair amplification attacks so these are literally where you're taking shape brute force amounts of bandwidth and fire them at target I read a really nice article that describe
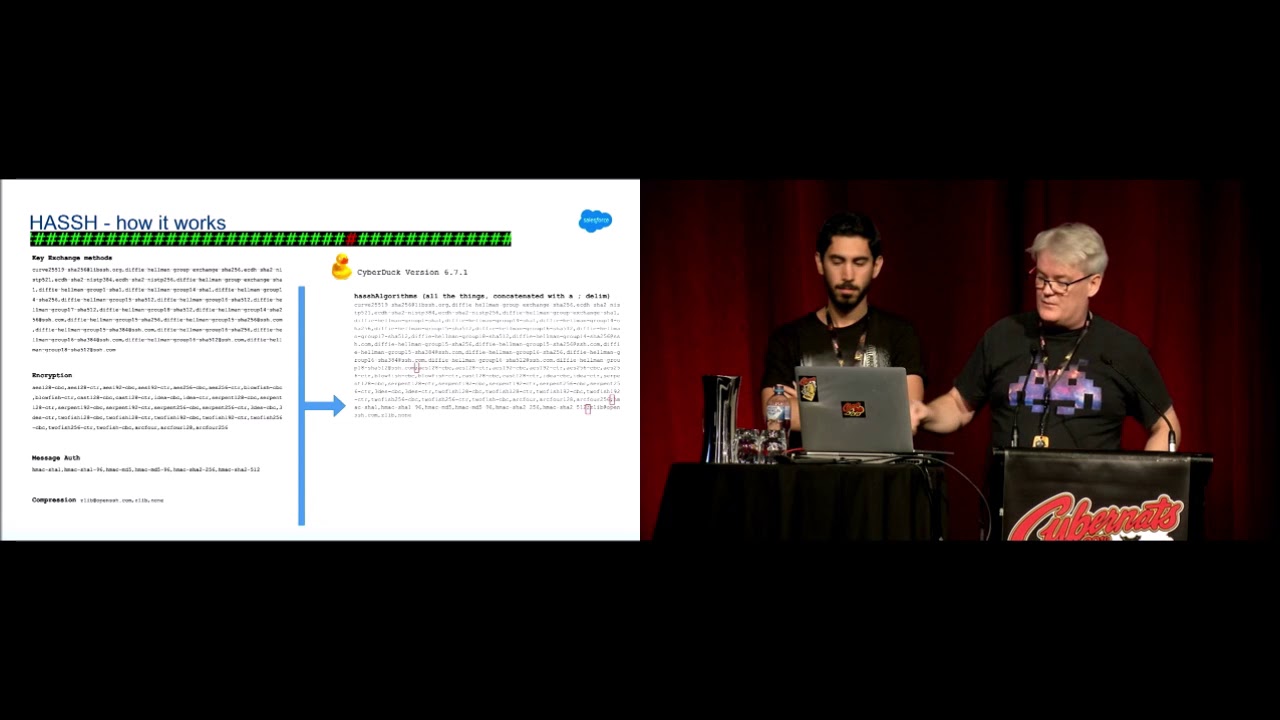
those cave months down and minimum complexity and you typically have a huge botnet that actually is performed in textin of a botnet master sensitive quest software but net and then they would actually perform the attack and they require a large amount of bandwidth for them to be successful so kind of going back to the title that's a screenshot of a little I'm kind of come in at all use by so it is nice little easy GUI that allows anyone to drop in a target URL toilet IP and change view settings hold the threats and sibley spam and the hell out any target the one it is also higher than iron cannon which is pretty much the same thing but
they're both really not that effective and stand alone it kind of really comes into power and lots of hosts actually perform in this tax so how can we kind of improve on this standard volumetric attacks so this one we've kind of getting a bit more clever about our attack in and we add reflection so if we spoof the source address that we're trying to attack from we can actually make it so that our our attack is sent firstly to an initial target but then the response center set the target so not only are we hiding where the attack is coming from but we can also hide you know who we are we can make you so that
no one knows who we are because a lot harder to to mitigate obviously when it comes to defend it is then much harder to implement any defenses it works best with any section nurse'll states profiles UDP particular and but commonly if we're trying to do a volumetric attack we're not particularly interested in the application working so you can just wrote ecp tracking parity and I'm saying Hydra source address makes it more difficult to block so we can do a reflection or we can turn up one step further and add application this is where we use different protocols different services and I result in the application of traffic so too commonly use protocols our dns and ntp so so in
dns servers on the Internet can be provided for involved with rest of dns lookups and so you can send the DNS request to the dns server and ask for everything it potentially has about once and hosts now sometimes out from that is quite a small request but quite commonly you'll get quite a big request back and so the request and be a much smaller than doing the respective response similarly with AGP there is the modest manners it gives back i fin in last 600 IP addresses the query the ntp server and i have not found any documentation as to why don't you p support from on this command if anyone has no ideas let me know and but essentially it allows
you to send in really small request an interview server and get a huge response and return so that's a little table that shows you the potential application factors and dean xfinity TV and fell in common and charging less DP or no increasing in size interviews so what's the idea what is volumetric attacks well primarily its bandwidth saturation we can flip the targets so that and no legitimate traffic will get through with what this is most commonly what we're trying to do but also a going conflict on its edge and a bit of crafting we can work it so that we can result in resource dilation and that's so that's where by we we target the targets
infrastructure such that the target is south and can't deal with legitimate traffic so for example if we cleverly crap requests we can result in hundreds and CPU time their utilization at which point no requests are gonna be accepted so those that have to kind of scenarios that we can really push for more attacking so essentially really simple if we can generate more traffic than the fact that take then it was also in denial of service and that's typically what people use an overrun can get enough with online dog then you can take my service there's also a commonly increase in tactical smokescreen attack and that's where we use the volumetric attack as part of a much larger side of
attack so the volumetric attack actually kinda max is a smokescreen and so while the sock is literally running around panicking that all services are offline and nothing's working and in through the back doors actual cyber attackers can get straight in and no one even realizes that attacked taking place and and so there's been quite a few instances in the news where this has actually happened people who had no idea that this is taking place so funny electric attack attack seemed pretty pretty good why would you use anything else well the start is there noisily the recent spot and if I work for a nice p you know it doesn't take really much to identify shoot gulps of traffic potentially if
they're spread out and then it might be a little bit more difficult to these texts and but with the correct mitigation it can easily be detected and the traffic can be redirected as planned other techniques which are going to later on how we can actually block the traffic and is bandwidth becomes cheaper internet prices and rub in and not only other defenses increasing I companies combined more bandwidth the attackers are also darn opportunities for more and more traffic so we don't always need to use log and Canada there are alternatives so the protocol attacks and so these are where we kind of abuse senate prototypes and TCP syn throats are a common one now participation but
kind of varies between the bounds of volumetric and a protocol attack but essentially we're flooding the target with TCP syn packets and I results in a multitude of pop open connections now hose can only support so many connections at any one time and so once that limit is reached no more requests are accepted and over a set period of time you can the half-open request will be closed and so it's really extent and it's only a temporary measure but as long as the attack is continued and continually attacking on the target it's quite easy to be better than the host upline and in terms of Defense's is quite a few and TCP syn caption disappears in cookies are a common one
and what i won't i won't go into those just dirt just yet if we drove back 15 years the king of death was quite common protocol tap and all you do is you send packet and last them the potential you before so plus seats five thousand bytes and any misconfigured hosts will accept that packet and build it back up and a little crush because handle it essentially an overflow sup stress one of my personal favorites it's not heavy documented on the internet and it's a shame really because it's quite useful attack and so it's kind of a collection of different attacks the use-value all tcp sup hit and but there's different kind of scenarios the
info chief so the connection floods stress is based on a similar tool knapper and and essentially all you'll do is you'll send and share amounts of traffic you're not keeping track of the tcp connection state and so again it kind of and they're pushing the boundary between volumetric and and protocol attack and the sooner windows loads which again livable payment crafted advertises size of 0 so in following the tcp through a handshake and the attack that sets the window size 20 and so the house is like okay let's send you the data or when window sizes 0 sergeant put it in memory and you've progressed again so the memory used to us up and up and
up and up and eventually very exhausting happens and server crashes and as far as I'm aware windows 7 and by default you can do that and 10 50 minutes and the box will just fall over so a little bit more complex little bit less bandwidth per client so you know pros and cons alternatively you've got your application tax so these actually attack the application protocols themselves layer 7 specifically at the other side level and slow loris is common one we use parchment HD to go back to the connection call of the target and and by partial all you do is miss up these conf into the request services they're waiting for the end of the requests
which obviously never returns eventually drops off but as long as you keep trophies in these requests utilization continues to go up and no more requests can be accepted I knew dead yet and is another similar taxes low noise and so I always uses HTTP get to the rudy utilizes hesitant to be post all it does is appetizers own content then and then just drink feeds data to the target and all the while there's a session being held up the pizza over and over and over again you can fill up the connection table and ends of the absorption happens and we requires minimum bandwidth and this kind of mini reports and where has been performed by mobile phone over TV 2g so
you know any1 pretty much can do it you don't need a massive botnet and loads of bandwidth and so I sort of similar diagrams this I kind of pulled this up in Visio and few nights today the kind of gives you an idea between when you take the volumetric attacks on high volume and failover simplicity and you drop the volume at increasing sophistication you kind of move toward that patient so forth is quite a nice graphic kind of moving the future our visualization of how the attacks differ the words people form does attacks so before kind of doing any research for my project I'm presumes what extortion obviously I've read some articles and smoke screen attacks activism anonymous
pretty self-explanatory and script kiddies you know you always will get those kids that will just attack can you gain at any time general websites but no reason and so yeah they do quite often but interestingly came across this so this is a report it's why our networks it was in the worldwide secure infrastructure for 2014 I didn't read all of it but I read quite a lot of it and not the most interesting of literature it kind of so the background for this there was this survey of 400 different and very and IT companies and other networks actually still made and they asked them what do those attacks of the receipt that they deserved what were the motives behind
them and it's it's interesting the vandalism comes will be taught online gaming related is also there what kind of criminal extortion is down at twenty percent I'm with the financial market manipulation so people aren't always doing this to make money people simply will perform a deal at attack for the safe and perform the Dean of attack so in terms of prevention and mitigation well that depends entirely on the attack and there's a few best practices and that is also consume up with a piece of you 38 which is just source IP address spoofing that just stops any kind of amplification or reflection attack and merely because you can't spoof the social dressing will just get dropped as
is and leaves your network but also not relying on traditional defenses you can't just install the firewall and hope that all file they're all dead loss issues will go away and really need to include defensive depth you need both on-premise and cloud solutions to actually be able to keep it from the different tax and so no firewalls no so the volumetric attacks what can you do well what you essentially need to do is break all the traffic and so one of the best ways that doing that is to use property and if you put a proxy from a number of applications you can spread spread out of the rest between multiple locations so essentially you can split
up adidas similarly with load balancing you can use DNS bgp though based load balancing to take a joint with d last and separate that then between a number of different instances of the same host and until the d dust mitigation prevented appliances there's loads of vendors out there and met with your vendors do it there's also many specialists they all work in different ways some of their ones relators malaria layer 7 they're all give you a lot of spiel about how they work but essentially and they do different things I need to do some more tests on that I didn't get chance to particularly kind of review it's more of an up-and-coming market and as soon as a provider level
you can do route black hole in and sinkhole in so you can reroute traffic and just simply drop it or you can redirect it to some kind of trap and scrubbing AB service where Korean and analyzed and another fairly undocumented tell you exactly before any tests which so this is where the same IP is assigned horrible habits so why we're there rather than unicast where one IP is assignments in the host same IP evening sister multiple and so traffic is always rooted to the nearest host simply by routine but you call student in that space too so that allows volumetric attacks to be spread across geographical locations and a lot of DNS systems use I
can be for any cast because DNS is connectionless it doesn't matter if woman it goes to one dear so that next when it goes CloudFlare all you also use this quite heavily with all of their http-based mitigation so it just allows for any kind of massive blow volumetric attack to be kind of separated amongst the different geographical locations obviously the more points of presence you have the more spread out it's happy thumbs and trans con prevention protocol attacks so this is where you can use your firewalls from DPI I digit attention into adventure signature analysis heuristics you can put application reverse proxies that assuming c90 application should we expect to see this requests yes fine no
drop it and you can also use how space and travel to 12 so slow loris and Rudy are really quite easy to protect and intimate as Apache or is there's loads of modules that you can quickly install and it will completely rid off their optimum ability and you've lost in traffic statistical analysis are we seeing a droopy of traffic from one host yes well that's potentially something to master similarly application attacks there they're fairly very similar in terms of how you defend against the protocol attacks you've gotta to analysis look for the bursts or probes of traffic again files IDs reverse proxies and he has based on trials so essentially defensive death no one single technique
and community so who uses lower behind kind of these days i put this straight into sourceforge it's been six hundred thousand downloads over the last year at twenty-three percent of which were from the US okay fair enough and then i went to this apparently fifteen percent of all downloads were mac and linux users and seen this is a windows binary not sure exactly what I deal with it but I think it kind of gives an idea that the users that are downloads and then using know why but I intended don't even have a clue about what they did it and so well there you go so quick summary not all these attacks to say understand the
difference and they're going to keep Gareth growing voting complexity and size so it is a mannequins volumetric protocol basis and following understands the different attacks and you can't use one defensive mechanism needs you've been depth and also I should have mentioned this earlier and in terms of extortion never gave it to Jesus threats and commonly you might get an extortion request saying maybe 1 million pounds or we will deduct the cost of actually perform that lead us is probably fairly minimal so even if you do pay laughs it is that just so never pay and give in to those professors so this was kind of the outcome of the project ideas of my degree and I want to look a little bit
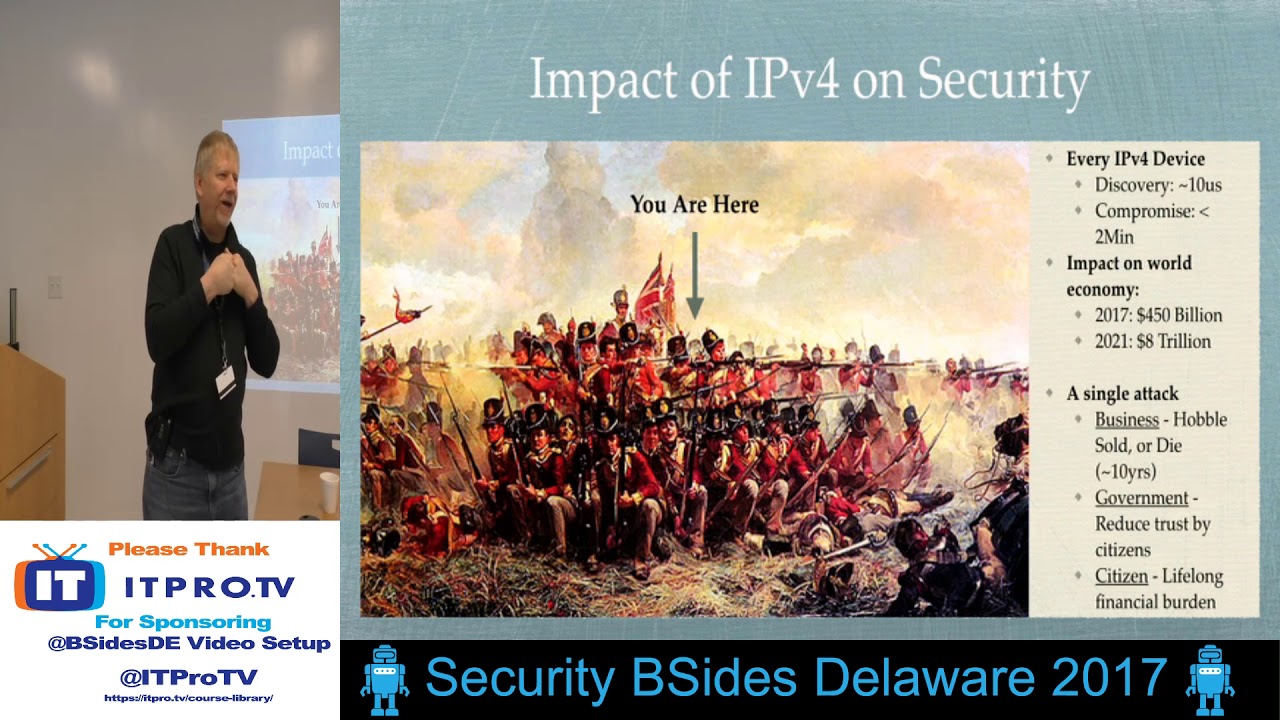
further into useful IP before any fasts and that could be a really leash way of mitigating the attacks and but also kind of look at all the potential and one abilities in motor cars so fuzz in ipv6 ipv6 a nice little more fresh more likely to be some vulnerabilities down there and i will see you know people are streaming out the luminol come in a piece of hardware we just um network and stacks all the old school and attacks going to work with these you know can we find something that I mean the death okay it's killing and also potentially looking to use of do those attacks absolutely more in terms of the summer with their and out they you know d
dusted service butta services as a massive come on my online market for apathy that so it's those scope of paperwork so quick thanks to Sam fair use the space earlier and and my tutor from my much going for help with research any questions and seniors as a rookie talk looking questions
yeah definitely and it was just kind of more vegetable than anything more I do a very quick how to source port sauce would determine the OS just in case it had some clever and technique not really came back so yeah there could be and that would likely be the reason potentially I just wasn't sure if maybe there was some clever way that they were doing it and yeah it could literally just be downloading the image pushing up that outer potential windows house it includes your robot master on it if you money so going back to defense in depth and I would utilize a cloud-based mitigation provider and there's quite a few out there lots of ISPs provide
leaders litigation services and some doing well to do it as well sort of cheap Samar chief and if you for me I would kind of look I know products in last time I read have walk when eight terabits of global network bandwidth so in terms of D data tak that probably going to be a pretty good company to be on the right side up in terms of mitigation but at the same time you know you can go out to walk in without a checkpoint you can put in your d ducks at appliances and then you can have an always-on solutions so that if you do MCD doesn't act on it you can then push the redirect traffic off to a classical
room service at which point then it becomes at home in the house making you on thinness and that the plan is slippery ones that can provide once I cloud secluded volumetrics you have to be lying wow so that rules out so if you're looking for a cloud and on-premise which would be doing my seminary for any half a phone whereas if you're lookin for cloud own battles acid then which is Arbor well checkpoint you can't my client service so you say like a cry yeah black where two of em actually back OMG monkey again they got from the clan MacLeod only yeah they've got some very interesting layer 2 stroke one appliance died rather pump which is
quite cool you know what is on yeah below is sometimes of course of the mouse yeah you've always got that issue that the traffic does get filtered out it should have come through there's lots of algorithms that the service providers are using I can find very much information about it top and there's kind of different infographics that kind of show roughly what they're doing but it's very unclear kind of how about how they're going about doing it and that might be a kind of a target to kind of explore down to and work out what it is exactly doing mr. and one of the things that I've seen working posting could make
yeah it's cheating yeah yeah you just looking snitch leave that single point failure doesn't matter how many kind of active standby routes or switches and all games that you pay for there's always going to be one single point of failure and what's that maxed out doesn't matter if it's the target all target and everyone else and I've dude us it's going to take place drop tank aquarium today taking we look it's big yeah
yeah so AWS have some really cool ways and how they can rearrange traffic and also how they move about servers as well so they have instances that kind of koto Kate between the servers so that if they do see attacks i think really take this instance put over here so that it's only the target is getting attacked and that's one of the ways that they mitigate it if ass given that you've got mitigation companies you know Sandra product or anything else and different levels figurations varies how do you know it's been working so that's always it is there is a big note that you know is a stand with the people working to all so it's over standards no and that
always kind of printed the passion Heidi testing because Tom bill is due any less attached as such you can always build it in a test that environment and see if it holds out and but otherwise you know no company in their right mind is gonna quite happily go along but it's not a size bigger size been yet approval spawn you know source to destination and actually form the dogs just in case anything does happen and I suppose tried interested manufacturers techniques is putting them in your best bet in terms of appliances there be easy to test or cloud-based it's all going to be I'd staying home down to the reputation provider do they have a stronghold who
they're supporting why especially telling with how much battery do they have those kind of questions that'd be my response
so yeah rather than waiting for the absolute acts Wilkie probably kind of tips their backgrounds I've head what are they indicate some potential attack and off the top of their heads in two minds but you knows we could attack you can detect or stop the Tappan Zee taking place then you basically want I suppose that pendant position to threaten telligence where if you know where potential clock masters are they work out with bass are and then from that potentially then protect or drop a traffic a high level 4 eva me today but as far as I'm aware there's not huge and is being done in under these be cited a husband and basically supposed to be
protecting yourselves and paying our fortune for it should
your website this is our network we're going to protect it moving traffic you actually say so Darren no it's not my I'm not bitter and the terms of in terms of ISPs obviously there's are not kind of met and and so the damn top state they're going to have their customers and obviously for obvious reasons they are going to want to kind of be a part of the kind of mitigation you know if they can stop the this traffic from existed on their networks it's much cheaper for them particularly for the kind of t2 t3 networks that have to pay for the bandwidth and I'd probably same kind of more towards your the larger ISPs and in terms of the vendors it's a
money making thing for them then they can make money off this this issue and I suppose that they could solve the problem completely then the bed isn't kind of the opera job so putting not in their best interests fits it I don't think it's ever going to go away though not would be the internet asset is just have to say else
you
you