Offensive Security Awareness - Phillip Wylie
Show transcript [en]
special guest today he is a bestselling author of The pentest Blueprint starting a career in as an ethical hackers he is also the host of two podcasts the hacker Factory podcast and the Phil the W podcast uh please welcome all the way from Carolton Texas Mr Philip Wy thank you thank you and thanks everyone for for joining uh kind of the the inspiration for this talk came from my time as a red team lead at the a large Global consumer product company because when we do things you kind of you're working a cyber security you kind of expect this is something everyone would know but one of the things I I kind of discovered when I was there pretty early on is
people in uh the security department didn't know the difference between a vulner ility scan a pen test uh a red team operation they didn't really know the difference of that so I created a single slide PowerPoint slide with the different different types of Assessments and uh vulnerability scanning and vulnerability management showing the differences between those and it's kind of funny that I really didn't dawn on me until probably a couple times back not couple months back or a couple times recently that I've given this talk that it kind of dawned on me that I think the ciso of that company didn't realize what a red team was CU he brought me in to build a red team and we'll get into
differences between that but I got in there and uh some of the assessments and stuff I did was kind of evident they really didn't know what a red team was and it's kind of interesting because uh red teaming is more we're getting into more details but it's more adversary emulation and I had a director while I was there that wanted adversary emulation done against an sap app and you don't do red team operations against applications but it was kind of interesting that I just recently thought about that that was the misunderstanding was at the very top of the security organization it wasn't just uh you know the practitioners and and management types so he got he uh shared all the
information with you but at the end I will share some uh links and stuff from my YouTube and all that as well as uh my LinkedIn so feel free to connect with me we will have question and answer at the end of this session but if you can't think of a question right away then later on you can send me send me those questions later on so the agenda we're going to talk about offensive security the different assessment types methodologies and standards and some of the tools used in security assessments so offensive security is assessing the security posture of Technology from a thread actor perspective and this also can be people this also can be physical security but
you know we think about our environments you're always hearing in the news hackers breach this company or that so if you're going to defend your environment what a better way than to assess your environment from a thread actor perspective and so one of the things about pen testing and other types of events of security it also helps uh justify the need for budget for remediation because you may have you may have a vulnerability that maybe it's not exploitable but if it's exploitable then you definitely need to remediate it because uh threat actors could exploit it and uh and that you know that would be bad you know it cause the company damage and stuff but not only financial
loss sometimes reputation loss but it's a good way to to uh justify that budget because a lot of times you see one of the biggest frustrations pentesters go through is you go pentest an organization they file risk acceptance instead of fixing things sometimes a risk acceptance is warranted maybe it's because you're not going to be able to remediate in a timely manner maybe it's because it's going to require staff new hardware software to do this may not be a fast task so there's needs for it but some compan kind of use that as a reason to not do that and a good example of why you should remediate quickly uh one of the companies I
consulted for we were doing a pen test for a company it was an external pentest they had a 90-day retest and a lot of companies are only doing one pen test a year PCI is requiring twice a year some companies may do twice at the most but this company also paid for a 90-day retest to test the remediation so they had some criticals highs and and mediums so we came back to do the F test they remediated 90 days later they remediated the highs mediums and criticals there were just a few lows left but between the time we came back and did the retest a security researcher had figured out how to exploit that vulnerability so now
that low level low risk vulnerability was now like critical or high it was exploitable and so by the time we come back we retested it 90 days later if they hadn't had the retest then it would have been open for a year until the next pentest giving plenty of opportunity for a thread actor to to exploit it and another example of a bad decision on not remediating something I did a pin test once where I was doing a web app pen test only the application was in scope no network but during that pen test through a a sequel injection vulnerability I was able to get command line access to that system and once I got access to that system I was able to
dump the password hash crack the password hash fairly quickly uh the password was like password all lowercase and the number one and since it was only in scope for this uh particular system this this web app I couldn't go any further than that I couldn't try to Pivot into other uh systems do lateral movement or or privilege escalation because it was out of scope sometimes it's kind of limited what you can do on web apps but they filed a risk acceptance because it was a development system and mind you it may be a development system but I am sure it's on a production VLAN so if you're able to get in that system you could
probably gain access ACC to other systems good possibility they were using that reusing that same password it was the admin account for that system and they were using it like as a system count they were running XP command shell and you know for those you that know it's like a command line utility to uh administer Microsoft SQL servers and they had dis enabled but they filed a risk acceptance so this is kind of why you need to make sure you're testing frequently you need to remediate the things that need to be remediated if it's actually been exploited during a penetration test you need to to remediate it it's kind of uncommon to actually get system level access through
a web app pinest because anyone that's done web app pinest will see you can see some critical things maybe data exposure usually at the most but you really need to make sure that you're remediating those items and and testing frequently so there's different types of targets when you're doing a pent test and so this is growing by the year we got new technologies you know computers networks apps Cloud Transportation physical security and actually even people because you know you see the people part sometimes companies can have really good inpoint detection they can have everything set up really complex passwords but if someone is sent uh malware through an email and you're able to compromise that system that opens it
it doesn't matter how secure your your environment is someone's able to get access as that user same thing with the physical security someone's able to walk into a data center or gain access to a desktop or laptop that's connected and logged in then someone already has access it doesn't take a lot of hacking skills to get into that so you really want to make sure you're testing the people and the physical security because sometimes these are often overlooked a lot of companies are doing just the basics they're doing their testing required for compliance and that's it so really need to test the physical part and one of the things as a pentester one of the things I'd always note is we
because when you're doing the report you always list things that are opportunities as well as things that're they're doing good because you give a pentest report to people sometimes it's a lot of bad news and you want to have something that document that's showing them they are doing some some of the right things so some of the things I've documented is companies that were really doing good with physical security and make sure to document those things or if he's in organization and they've got really weak uh physical security controls people are tailgating and all this then that's something to report to them to to uh recommend social engineering or physical pentest but these keeps keeps growing because one of
the things now you're seeing now with AI uh the OAS project is offering some LM uh resources for testing uh AI for the large learning models as well as there's companies out there providing security there's actually a platform called Hunter that's a bug Bounty for uh AI so if you ever want to get into AI bug Bounty that's a good resource but as technology grows we're going to get more and more targets when I started uh pin testing in 2012 you know you weren't see you wasn't seeing Cloud as much uh you know we got so much more Technologies iot is becoming more prevalent a lot of more work from home stuff that are bringing in these different uh reasons
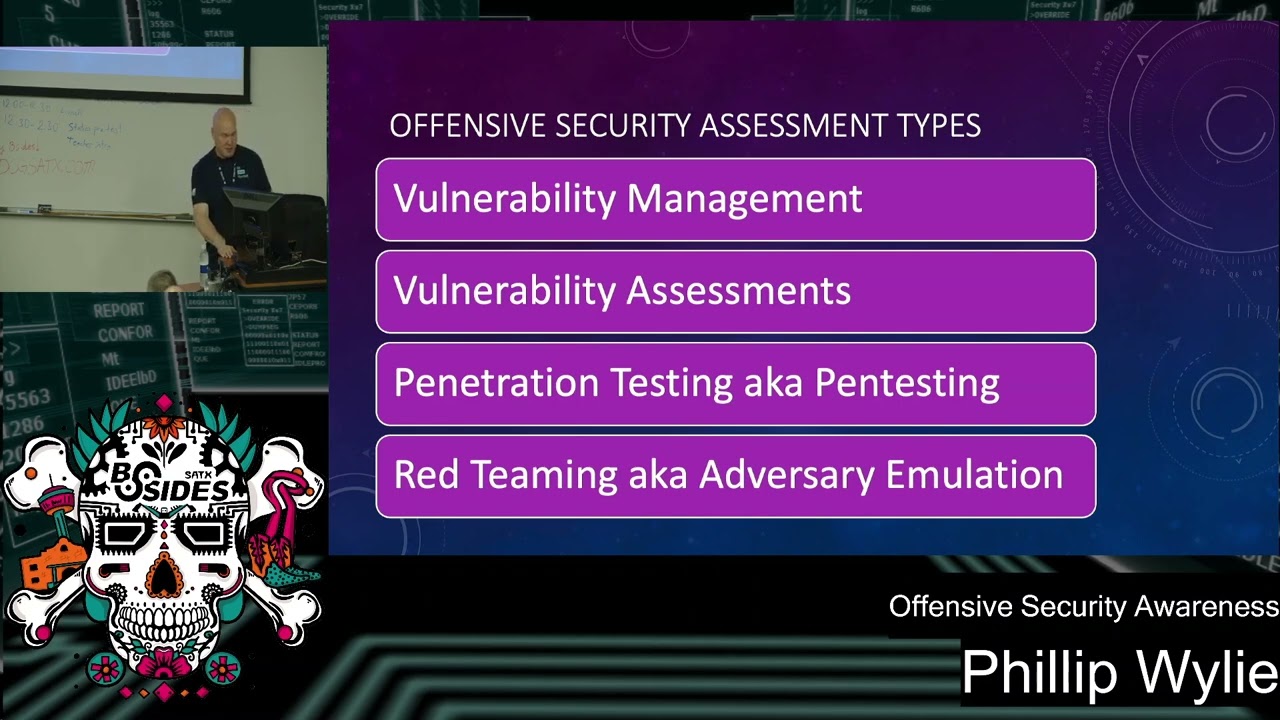
to perform pin tests so the different assessment types so which while the first two are not really offensive security assessment types so you have vulnerability management this is your vulnerability scans we'll get into the details that vulnerability assessments because one of the things you'll see if you ever see the the description for jobs you'll see VAP which is vulnerability assessment pentest and so also uh red teaming and what I'm St talking about red teaming I'm talking more about adversary emulation and we'll get into the differences between that the industry is really kind of confused a lot of that because they call everything red teaming that they're generalizing offensive security so one of the things is is it's
getting to be where I don't know that you can say it's really incorrect terminology but something you need to dive into and do a better job of describing so if you're a company you want a red teaming operation done you need to to you know give more detail actually what you're wanting and stuff so vulnerability management this is the cyclical practice of identifying classifying and remediating vulnerabilities and this is kind of even part of your uh patching program is part of your vulnerability management so this is where you're doing your uh reoccurring vulnerability scans and what you're doing here is really checking for those cves and some of those configuration errors between pentests because it gets kind of difficult to
constantly be a pen testing which that is an an option and really a good option if you if you have uh you know the budget to bring people in our internal team to continuously be pentesting or use some of the automated platforms that that do that so vulnerability management one of the things that people don't think about sometimes is your asset Discovery and inventory because if you don't know uh you know if you don't know what you have then you don't know what to test or protect or what to defend there and you know back in my days when I was in it from when I started out in '97 you had Shadow it but this was
someone buil a server and putting in a cubicle now with Cloud it's easy for people to spin things up and you don't have to really uh be that highly skilled it brings things to spend stuff it may not be secure but it's just a little bit easier to be able to go into uh you know a browser go in and configure things compared to the way it used to be I worked for a mortgage company we had a lot of uh these different units business units within the company we're having people come in and build access databases but so now you have the cloud stuff you have a lot of companies that are creating microservices for for
marketing campaigns they spin these up they don't always take them down when they're when they're done another good example of the testing things and having a good act inventory is I one of my friends was doing a pinest for a university and they were doing this pin test because they had like a web design and uh web development courses there so all the students got their own website and so you've had this school for 20 years or more teaching these classes and so all these web servers or websites haven't been decommissioned so you don't know if they're being properly tested so uh they were going back to test all these find all these systems so they
could decommission and and find any kind of vulnerabilities so the asset Discovery is really important you see a lot of tools out there that are taking advantage of this you can do uh if you have like a vulnerability scanner like the tenable products in nessus they actually have a host Discovery feature in there so you need a good inventory and and keep up with that inventory because not always it is not always going to update what new systems they brought online when someone gets a new laptop or a new desktop those aren't always being documented so the next phase is the vulnerability scan so you're running nexos tenable uh qualus whatever vulnerability scanner your organization has and then you're doing
the remediation this also includes patching so patching is part of the the remediation or part of your uh vulnerability management plan so you you want to make sure that you're doing that with your program and then repeating you want to make sure that you're you're consistently repeating this because you know every you know Patch Tuesday there's you're opening up more vulnerabilities out there and the threat actors and security researchers are looking for those patch Tuesdays and trying to figure out how you can get around the the remediation for those items so vulnerability scaners is a piece of software like open boss nessus and nexos and nuclei is a good command line one but if you're wanting to if
you're getting into security and you're wanting to learn about vulnerability management and a good step a learning step is to learn how to use something like nessus because you know you see the ocp and they're not really using vulnerability scanners in it but you know one of the things some of these these uh education products Overlook is the fact that you're a pentester you're going to be running vulnerability scanners and if you know how to run a vulnerability scanner then you could be on a vulnerability management team it's kind of like a step towards pentesting if you're wanting to be a pentester so this automates the process of detecting vulnerabilities and one time you didn't
have vulnerability scanners so you were dealing with things like using important service scanners like inmap trying to manually discover these vulnerabilities and so fortunately they got vulnerability scanners to be able to scale to do what we need to do because if you've got thousands of servers to test in your environment doing this manually just doesn't make sense you have to have some kind of Automation and vulnerability scanning is just one of those things that's kind of helped uh automate what we're doing even other uh pieces of software that's helped helped uh further the scalability is like your your exploit Frameworks like met exploit and then you see some people are starting to do more automation around
these things which are making helping scale people more scale more there's some people that are purest hackers that think vulnerability scanners are cheating or these other tools but you really have to do it because when you're talking about assessments or pent tests it's referred to as a time box test you're only got a limited amount of time to test and you need to be able to do as much as you can so vulnerability assessments so vulnerability assessments is is kind of the next step above your vulnerability scanning and your vulnerability Management program with this you're looking for the vulnerabilities you're not only finding the vulnerabilities you're also validating these vulnerabilities because a lot of your
vulnerability scanners will find false positives and so using a secondary vulnerability scanner you can help find those vulnerabilities as well as doing different uh manual techniques and using other tools metas sploit is good about finding and remediating some of these are are actually validating some of these vulnerabilities and one I use a lot to validate is nmap usually nmap has an NSE script that you're able to go through and find some of these vulnerabilities because any of these critical uh vulnerabilities come out they usually write an NSE script so you can quickly scan your environment to see if you can find any of these vulnerabilities and so it's interesting too because you along the lines of the
false positives you also can find some false negatives things that have been missed so if you're using other uh vulnerability scanners and manual techniques you might find something otherwise that you didn't find so this step is going to be a lot better at finding true vulnerabilities than vulnerability management doing your vulnerability scans but it's definitely something necessary so pretty much like this uh you follow a lot of the same similar steps Al although you're validating and doing some manual testing so penetration test the next vulnerability type so this is similar to vulnerability assessments uh but you're also not only validating the vulnerabilities if those vulnerabilities are exploitable you you do your your uh analysis across those
vulnerabilities and see you know nessus or whatever vulnerability scanner you're using will tell you typically if it's exploitable what it's exploitable with if it's not then you do you know go to exploit DB and look up these particular versions and see if they're exploitable then you attempt to exploit those vulnerabilities and one of the things about this phase that it may show up and this is one of the reasons you want to do uh pentest because you may do a nessus scan there may be a mitigating control you this cve may be showing you it's exploitable but maybe there's something a mitigating control the W is configured a certain way maybe there's a firewall or sometime but mitigating
controls certain permissions to prevent the exploit so you really have to attempt to exploit it to see if it's truly exploitable and so uh this is kind of one step within that process once you validate those vulnerabilities and one of the things with pen testing because we'll get into red teaming next with pen testing you're looking for all the vulnerabilities that are exploited exploitable exploit those and document them and also you're going to do steps after that like lateral movement privileg escalation data exfiltration just seeing if you can get access to certain types of data so the uh different pentest types are blackbox also known as blind pentest this is more of a thread actor approach
this is more of what a hacker would do they don't have you know they don't have a statement of work and a scope for the pentest test it's up for them to find all the targets and do the reconnaissance so this phase is going to require a lot more reconnaissance to uncover the details of those systems just like you're doing the pin test you're doing your your vulnerability scans your reconnaissance you're looking for vulnerabilities seeing if they're exploitable to see if you can get get a foothold in there so this type of testing is going to take a lot more reconnaissance and a lot more effort gray box is kind of the next level down
this is a detailed scope so this is IP addresses domain names your for the applications and this this type of testing you've got everything that's there so you know everything that should be tested in scope so it gets tested some things could get get uh missed on the Blind pinest and so white box also known as C crystal box or assum breach this is detailed information so this could be uh diagrams on the environment this could be source code because when you're doing a web application pinest or application pinest you should really do static code analysis and source code review because that's one area where you can find V abilities so you need to be
testing that and you also want to test authenticated because there may be maybe no one can break in from a thread actor approach but what happens is someone has authorized access because some applications that are open to the internet if you you like a social media account you're able to register for that get that account there doesn't have to be any approval so you got access to the system you might not be able to broke break in from a a blackbox perspective but once you gain access there may be things you can do so this is where the uh assume breach and authenticated pin test to helpful so applications you want to do all different levels of access so
just something from a basic user up to admin because there's some information that admins don't need to see like credit card information uh pii Social Security numbers that stuff doesn't need to be exposed so getting in and testing that so out of the three of these methods this one tests more thoroughly so I'd even recommend if you're doing this approach try to see if you can break in and get a foothold you know at the beginning and then continue on with this more thorough method but they're very important this is like when the hardcore hackers think it's cheating but you really want to thoroughly test the system so red teaming so red teaming this is uh using techniques tactics and
procedures to emulate real world threed actors so this is actually more this is actually adversary emulation so with a red team uh you're doing your reconnaissance trying to gain a foothold in but you're trying to be quiet because uh you always hear people talking about paint on the pent test trying to go undetected you may do that as part of the pentester for a short time but typically that's not the goal because as I mentioned pentest is a time box test so you're limited on time with the red team operation thread actors have months years to try to get into environments and sometimes that's how long it takes them to get in and so emulating a thread
actor you need more time and especially one of the reasons is you're trying to be quiet another thing about this with the pentest people know the pentest is going on it groups security groups know that's going on on so they know it's not malicious activity something breaks they can report it with a red team operation you have a control group and the control group is like the ceso maybe a few others because you really some cases you don't tell the blue team manager because or the IR team because then all of a sudden they've got a heads up they don't want to look bad they may tell Pop their team and so you don't let them know and
one of the the things about this one of my favorite descriptions of red teaming was from from wifall the founder Dallas hackers Association and this quote was the the red team tests The Blue Team so you're not only testing the technology with the pentest we're testing the technology although when you get into social engineering you're testing people but with red teaming you're testing the people the process and the technology are people following their instant response plan is there instant response plan in place and one of the best results I ever heard of a red team operation is this company had an IR firm on retainer so if they ever got breached had something suspicious they would
reach out to the IR firm they would come in and investigate so by the time the ceso found out about this during this red team operation the IR team had already been brought on site investigating and he's the ceso said no this is a plan activity but that's perfect outcome even if they got a foothold in environment it was seen in responded to and blocked because there's some cases you can't block for every scenario but you want to make sure that you're responding and so this is like the perfect thing to do and it's if you think about this is almost like some of your you think of uh Disaster Recovery in business continuity uh plans
where you run these exercises to test to make sure your your plan's working just like with your backups you periodically test backups to make sure you have good data this you're also testing the uh the teams to make sure they're doing things right and this is a good thing to to do afterwards to go back and review it and see where there are opportunities for improvement some cases some company may not have an instant response plan so creating instate response plans so here's kind of a comparison of the different assessment types so you can kind of see over here they they pretty much all have some kind of asset Discovery uh which Vil manager call Asset Discovery but it's really
truly kind of reconnaissance so reconnaissance you're you're also doing across vulnerability assessments as well as pen tests you're doing reconnaissance across red team but you're trying to be a little more careful with that quiet with your vulnerability scans you're running vulnerability scans to find vulnerabilities in map uh any type of tools like that to do Discovery LI for vulnerabilities and you also do that pen test but you're using more quiet methods with with uh red teaming a lot of cases you're depending on uh fishing emails social engineering sending you know malicious payload to someone to gain access to that environment a lot of times you hear about maintaining persistence and this is one of the areas
that's more important to maintain persistence as a pentester if youve ran your met exploit uh exploit against a system you gain access you lose access sometimes it requires being rebooted but with it you know as a red team operation you're emulating a threat actor you can't go tell the s admin or whatever hey rub this Ser server for me so you're using c2s your command and controls to maintain that access and you know c2s really make it easier to get connection back because uh some of my experience with c2s I've had instances where I had to reboot my Linux server and then I was able to quickly reconnect whereas if it had been uh some other manual exploit or
met exploit you have to go back and exploit all over again and you're really wanting to be quiet and undetected and so these last two you actually have exploitation and post exploitation and post exploitation you can test data exfiltration uh privilege elevation escalation also uh accessing data because sometimes as pen testers and a lot of us all go through this you're more concerned with getting domain admin or root and not focusing on the crown jewels so one of the things that you want to focus on is making sure that you're you're doing that and just going through and looking through the data um is is very important so we got some someone here that uh that that's one of
their main hacking pieces or methods that they do is going through looking through shares and finding information and finding credentials of developers and and maybe make it easier to get in so on to the methodology so one of my favorite standards is the penetration testing execution standard and one of the reasons it's my favorite it's probably the most recently updated but is also created by people in the industry some of the experts some of the people that are writing to tools that run very well-known Boutique pentest firms like for instance Dave Kennedy from trusted SE Carlos Perez which is a trusted SEC but whenever he contributed to this he wasn't at trusted SEC uh John
strand from Black Hills information security group uh Joseph McCrae Chris Nickerson from L's Consulting another pentest Boutique pentesting firm so this is not just based on research because one of the areas you can do research on security or different items and it's kind of easier to figure out but unless you've done pen tests and working in defensive security area it's kind of really hard to guess what needs to be done there because one of the mistakes I see people outside of the the area of security trying to speak on pen testing that's never done it is they're saying you got to go undetected and some of the the recommendations are given are just really not in line with with how things
really done in the industry so this is this gives you all the different steps of a pentest the pre-engagement interactions intelligence gathering threat modeling vulnerability analysis exploitation in post exploitation and Reporting and so you can find this at this URL right there so highly recommend checking it out U it's kind of dated I think it last updated in 2014 but methodology and a lot of that stays the same there's a technology section that will show you the different types of tools to use for Wi-Fi pentest in the different pentest types as well as this the pre-engagement section is really good because it really it's even good for you if you're getting pentest done uh they talk about setting the goal for
the pentest because even though you're doing a pinest for compliance you should the overall goal should be to be secure work in compliance to that so post exploitation techniques uh this is like your lateral movement trying to go from one system to another a lot of times password reuse this is a way that threat actors and pentesters alike are able to gain access to other systems privilege escalation trying to elevate your privileges from you know a system account uh you know a lower a standard user account up to an system Authority domain admin or root if it's on a Linux or Windows Linux or uh Unix system or Mac and then data exfiltration and just and then accessing the data
just in general because sometimes you see these breaches in the news and they seem like these elaborate hacks and someone just found an open S3 bucket so it really didn't take any Elite hacking skills to do that so this is one of the things you need to test on on your pentest looking at the types of data that's in there and data exfiltration this is a kind of good exercise to test but make sure you're not using real data create data that's structured like a credit card number or pii without using actual data because then this is actually an incident in a breaches itself if you if you do that so web applic web application pen
testing so the best resources out there is the oasp so they have their testing guide uh also the OAS top 10 API top 10 as well as now they got stuff for llm iot so they're constantly coming up there's projects listen there for new tools and types of testing and the most popular vulnerabilities and when it comes to the top 10 on OAS one of the things to keep in mind when you're testing systems it's not about just testing the OAS top 10 the top 10 is basically what's popular at the moment the most common you want to make sure you're testing for other types of vulnerabilities and then far as far as the tools go port and service scanner so
inmap is one of the more popular ones Mass scan is widely used it's a little faster uh but you have to be careful with it I actually was doing a pin test for an airline once and we were having to do segmentation testing for PCI so inmap just wasn't really going fast enough so I thought H I've never tried this Mass scan out so I'll try it so I thought well 10 5,000 is good 10,000 should be even better and so I end up rebooting a couple internal firewalls so that got me uh being Babys set the rest of the pentest they had someone set over my shoulder which I thought was be awful I don't mind I've had instances before I
worked at the company it we were having it problems and your managers over your over your back is it fixed yet is it fixed yet you just don't like that so I was really dreading it but got in there and the guy that was working with me really loved pentesting hacking loved going to Dacon so we really hit it off and made a friend so it made it a a good situation I thought was going to be bad but still run into him sometimes at black hat but uh you have to just kind of be careful with some of stuff but a lot of times that's a finding too you shouldn't you know reboot a firewall
because of uh you know a scan in some cases it gets documented in pentest reports as a vulnerability because it's vulnerable to denial of service and some of the scans that you do with nesis and even Med exploit they will show you where the systems are vulnerable To Deni a service so vulnerability scanner is an exploit tool so exploit tools cor impact was one that was very popular still around exploit pack is one of the newer ones but Metasploit is the one that does offer a free version so through my career I've actually had access to medit professional but it's interesting with Consulting companies they're making money off these tools but sometimes they don't spend a lot of money on tools and
I've worked for companies corporations as internal pentester where they had medit probe but I got so used to using uh met exploit framework that I just stuck with that but if you're going to learn one but it is a good way to learn things the more difficult way so then when you get the privilege to use the better commercial tools then it makes your life easier and so command and control you can use this in pin testing it's become more common sometimes people refer to Metasploit as a command and control but it's uh for me it's not I really don't really consider it so much it has some of the same functions but really it's more your your Cobalt strike
and and those type of tools that are and then vulnerability scanners so you have your network vulnerability scanners as far in web app vulnerability scanners the pro problem with the web app vulnerability scanners are Dash dynamically uh application security test tools uh one of the problems with them is they find a lot more false positive than your your typical vulnerability scanners so when I was working for a company Consulting we were using web inspect and got away from web inspect because sometimes you would spend more time trying to validate false positives because one of the things you run into especially like on uh Apache web servers they have this mod rewrite file so anytime the certain configurations may
be across other servers too anytime you send a a packet to it or you know trying to test something it'll respond back regardless so it'll sit there and keep running so your scans never stop so we went to uh using the vulnerability Scanner with the nessus which has less false positives but the interesting thing about trying to test the other things it's a lot easier to automate Network pin testing because people finally figured out how to automate pin testing but not web app pin testing there's still no one out there yet that's automated it so it' be interesting to see because with web apps you can have the same application Ser server same development language all
that could be identical it could be the same exact app doing the same function but it could be written totally different sometimes uh developers want to create their own authentication instead of using existing authentication mechanisms out there but it just makes it that much more difficult to to test and so this is my uh social media accounts and stuff and as well as my my podcast information so feel free to connect and we can open up to questions but if anyone has any questions afterwards feel free to connect with me on LinkedIn and and send any questions by yes so you mentioned a for and I was just wondering if you could talk a little bit more about any
that you've seen with red teaming or around llms or gen um just what have you because it's still you know companies are still building out AI every day be getting notifications like page that we're going to be using this type of gen using this language model can you just talk a little bit more about what we're seeing red teing and llm yes a lot of people are using it to create different scripts but one of the things when it comes to to using chat GPT or something like that you have to know something about the subject you may not have to be an expert but sometimes it can give you back information it's not correct so you have
to know something about it but more teams are starting to use uh generative AI to do that type of stuff so that's mainly where you're seeing it uh there are some tools out there for pen testing that is using it in their in their applications that's using uh chat GPT and there's some companies that are are creating their own llms to be more secure and training the models to be more specific towards uh you know towards offensive security what security type because part of the training is all the prompts to bypass the prevention so a lot of times it tries to prevent you from creating any scripts for hacking or anything like that so some people are building their
own uh chat systems llms and also it's interesting too because Jason hadex created a chat GPT for like red teaming and Pen testing so you can go to the chat GPT store and it's one of the the gpts you can get and it's more geared towards doing red teaming and Pen testing but there's also Cory ball the gentleman that wrote the API hacking book he created a chat g a a GPT that's available in a chat open API chat GPT store for API pen testing so Peete more people start create so the good thing is there's people once it become available people are starting to use it and just the mind the the spirit of a hacker in
general that's anyone that's creative is building this stuff once you release it to the public to use for these different typ of uh methods you're going to see more Innovation coming out of that I met someone a while back the CEO of a company and one of his uh marketing folks for a company called Uno Ai and they created a co-pilot for blue team blue teamers so basically you put in there what you're want to do it kind of help gu helps guide you which is very important because any of us that have been in it a long time because anyone remember back you know in the late 90s you had to have access to Noel you had
to have a service an account with them or you know contract track or with Microsoft because you really just couldn't google and find a lot of information now we can we can find that with these uh gpts and stuff it's a way to to elevate that and help you know some lesser skilled individuals that's kind of like some of the automation like with our product our company we automate pentesting so it's able to take more junior level people and scale them up quicker but yeah it's really interesting one of the things I really look forward to seeing with AI just to see what it does on the defensive side because I think I see a lot of opportunity for
some really good enhancements to and new tools out there for the defensive side a great question I that fully answered what you're looking for I [Laughter] okay yes sir brought aut and I'm curious your opinion on how close it is to the real thing and um I'm just also curious about you know who who's really leading the charge in that space yeah as far as the ones leading the space I would say it's our the company I work for Horizon 3 we have a product called node zero and Penta Penta is like one of our biggest competitors before I went to work for Horizon 3 I didn't think it was this far Advanced so saying whether they could replace people
a certain level of pentester it could easily replace you take a junior level pentester this thing is doing things that they couldn't do a more SE seasoned senior uh professional you I don't you might not replace the yet but one of the things it is doing is it's helping them scale and we have to be able to automate because we're you know you look at the stuff all the these environments you figured 20 years ago there wasn't that much technology now it's getting ridiculous more and more stuff is being added and to be able to scale the capabilities and so with some of these automation tools you can take someone it doesn't it's someone with
some basic experience someone that's worked in it or help desk and train them how to use this tool so they can use it one of the things I'm not seeing them do yet is find OD days and so this is specific to actual practitioners that are finding the OD days but the good thing about that is is when you have researchers in the background so like for instance at our company we've had a couple of our Engineers find zero days actually create exploits and so this is something that we're not to with AI it's going to take the artificial general intelligence where it gets away from the training and it's figuring it out on its
own so I think it's a while before we're replac but I think with a lot of AI really what it does is it gives the end user the ability to be more creative because it's taking care of all these redundant boring tasks because as a pentester one of the things we dread is any time we find SSL related or TLS related vulnerabilities how to validate that stuff is just so boring and a lot of those some companies you work for may not require all of it be validated just to sampling but a lot of times you have to validate all this boring stuff and then you had had a lot of time to spend trying to actually exploit things and
one of the things is going to do too with this automation is give the pentesters more time to spend on these areas that haven't been automated so these companies uh you know they haven't really figured out how to automate the web app pentesting so now organizations can use this tool to leverage to give them more time to spend time pentesting applications if they're using AI in their environment to pinest that test testing their their web 3 Technologies and stuff like that so it's really interesting area and I know a lot of people that are uh using chat GPD and stuff to help personally but it's uh like I said I don't think it's replaced yet I don't know how long it would be
before but different levels because the interesting thing is is whenever before I joined the company and they were sitting there demoing the tool you know I was sitting there watching the command line seeing all the stuff it does yeah use that tool and okay this is cool because it's using this vulnerability scanner because it's quicker just to identify the host now it's going back and use inmap and digging deeper so it the way it doesn't it's not fully AI for the automation but it does some of the decision- making stuff is using AI but it hadn't replaced them yet but I think it's definitely needed to help scale especially with the continuous pentesting so we really need to be
pentesting continuous just like the example earlier where uh you know pentest the company came back 90 days later and they had exploitable vulnerability if they hadn't if they're not companies not testing frequently you don't know when they could be breached I mean because they're open like that so some companies are offering like manual continuous pentesting Bishop Fox and met spy or some that offer and you see Paz pentesting as a service so some of these companies are offering that on a more frequent basis because you really need to do that more often and using something like AI helps automate that so don't if that answer your question but it's really exciting area like I said the thing that gets
overlooked people don't talk about much is the defensive side so I think defensive side's pretty exciting area to see what they do there anyone else yes this is kind a question but how do you feel about the I think it's I still think it's one of the best to have because it's more recognized I think there's other certifications out there that would do a good job of training you but it's the more recognized because like some of the TCM stuff are becoming more popular tenal actually looks for it net spy because I had a a former cooworker of mine from a company I used to consult with he got laid off and he didn't have
any certifications pen testing certifications so he was talking to them about a job and they told him to get you know his OSP or pnppt and come back so uh it's still kind of good it's more ocp is more universally recognized and it's even like a pathway to like the crest certification so this is one of the things some people over the years that kind of downplay it and talk negative about and some people it's because they got a competing product they want to make it look bad but the crest certifications over like in the UK this is like one of their top recommended or recognized certifications and even something some companies get Crest certified as well as with the
ocp uh back when it first came out all you had to do is I think take a written test and you had an ocp and you get their CR certification but when you have other uh certified bodies recognizing something that's a good sign but ocp is still probably one of the most most recognized uh you see a lot of the sand stuff that that are actually sometimes being recognized as well which I don't think the the gpen is an equivalent because on the OSP you actually have to go in and hack things but even back to like the TCM stuff it's pra it's uh practical you have to do a pentest and stuff so you're doing real world type stuff I
think they may be a little more realistic because they're not as limiting on some of the things you can do because in a real world in a pentest you can use Metasploit as many times as you want to and that type of thing so good question anyone else yes how long is a typical redam how much time yeah it just kind of depends that could be months or even a year sometimes people work on it for a year so it's just kind of depends on the type of red team sometimes you know you see more of the red teams taking over some of the fishing campaigns before when it was like uh pentesting more companies are starting to get red teams
but that could vary in in months or even a year you have a yearly ongoing operation you a question anyone else want also a shout out to one of my former students the very first class I taught at Dallas College Alvaro was one of my students so he was very first class so
[Applause] so if no one else has any questions I guess we oh yes another question you that yeah I think so it's just it's it seems like the coolest thing and I think it's probably the one area of uh pentesting that one of the areas of security that it just seems super cool but a lot of it is some of the stuff you get in there it's not as fun once you get in doing it I mean some people love it it is a lot of fun but it's not for everyone but it's also one of the first things people hear about when it comes to cyber security you talk to anyone they think about hacking they're not
really thinking about firewalls and stuff but one of the things I'd like to see and and I try to do myself is to bring awareness to the other areas of cyber security because we need those and there's a lot more opportunities so I mean you figure you know I worked at a large bank once and we had probably 13 pentesters our organization we had like a th Total Security Professionals so there's a lot more uh opportunities but I say if it's something you want to do you're passionate about it go for it and sometimes there may be opportunities to be like on the vulnerability management team where you're just doing bow scans and you eventually get to move over
that's one of the things that we had at the bank we had several people move over from other departments that was doing like vulnerability scanning or remediation and got to move over there so yeah there's a lot more people looking for those type of jobs but one of the things I say too that'll help you in this area if you want to do that is really work on your network and get out meet people because uh whenever I was teaching at Dallas College I had people always approaching me for junior pentesters and I would recommend other people from the community because I knew them and I knew they were looking for roles in pentesting so just get out make
sure you're networking the people that do the most networking have an easier time finding jobs because like for me I was in a toxic environment back in October and uh I resign I gave my two weeks notice so I started putting feelers out trying to find a job so I left on a Thursday and on Friday I had two offers and that's because I maximized the networking when you go on these conferences go out meet people because you don't know if they're you're not just the speakers because you don't know who sit next to you is a hiring manager of the company and don't even have to be the hiring manager they can get your resume to the hiring manager
and one of the things to keep in mind with this is with the referral thing a lot of companies pay referral bonuses so people are going to be more likely to refer you than what you think because they're they want the referral bonus you know cuz like the company where I'm at we get like a $3,000 referral bones and then going in that way networking it's easier to bypass those systems the HR firewall trying to upload a a resume which never may be seen because I the year I went to work at US Bank I met someone at OAS chapter meeting they worked there they were looking for pentesters i s in my resume two weeks later I had a job offer same
time I applied for Bank of America up loaded my resume I didn't hear back until a year later and I was highly qualified for the job so you can think of you're just getting started out or just not much experience G more difficult just trying to overcome the keywords and algorithms they use is near impossible but you can beat That by just going out beating people so I think that's
it thank you