The Pentester Blueprint: A Guide to Becoming a Pentester

Show transcript [en]
thanks for the introduction welcome everyone i hope everyone's having a good time at this virtual conference today uh kudos and thanks to the staff and uh stephen for putting this together and running this uh really great encouraging to see all these these uh conferences that have continued even though virtual so this is awesome and another great uh side effect is the fact that people that normally couldn't attend these are able to attend people that geographically distanced that could make it so this is an awesome deal so it's really been great this year be able to have so much access to so many great conferences online so uh so you heard a little bit about me so just
a little more detail on my background i like to share this background because um it kind of gives you an idea of how i got into pen testing and so you you know you can relate your own path where you're at and how that can relate into becoming a pentester if that's something you're interested in so i've been in iit and infosec for over 22 years i've been in infosec specifically since 2004 started out doing network security did that for about a year and a half moved into application security and application security is where i learned that i wanted to be a pen tester i was using web application vulnerability scanners started you know attending some different little
uh vendor talks on different tools and really got interested in in pen testing so in 2012 i got laid off from my job and i went to work as a pen tester so i've been pen testing for a little over eight years the first five years was spinning consulting if you ever get the chance to consult that's a great way to get a lot of experience really quick get you know exposure to a lot of different environments than you would in just one place so that's really molded and helped my career a lot i'm also the co-host of the uncommon journey podcast and this is a podcast on becoming you know we're getting into information security and
i co-host this podcast with alyssa miller and chloe mustaghi it's a little more to my background just to kind of show if you're doubting that you or don't think you can do this you know i was a former meat head you know power lifter pro wrestler and never thought i'd ever be paid to use my mind to think so i started i was a pro wrestler after high school and then i had to find a more stable career because i got married so i went to trade school to become a dread cad draftsman and during my drafting career i found out about sysadmin work i was working for a company and we were billed like
out at they were built out twice of our hourly rate and then i noticed the sysadmin was making about 10 would have worked out to be about ten dollars an hour or more than what we were making and what they were doing seemed a lot more interesting so i became a cis admin did that for a little over six years moved into information security and then pen testing and so this is a this is a slide i share each semester with my ethical hacking class my web app pin testing class with great power comes great responsibility only hack if you have permission and even better written permission hacking without permission is illegal if you get into legal
problems then that makes it hard to get any kind of job development i t security in general so you want to really be careful when you're doing any kind of hacking make sure you have permission uh this can be done practice wise through ctfs or bug bounties but make sure you have permission you don't want it's not worth getting in trouble what is pen testing so pen testing is assessing security from an adversarial perspective attempting to exploit vulnerabilities to get unauthorized access to systems and sensitive data also known as hacking and some of the things i like to do here too is people new to the community people just getting started you know make sure you differentiate between
hacker and cyber criminal there's a lot of people in the industry that are in that are offended by that and you know starting off on the wrong foot by labeling them negatively is is a bad thing so just remember that so and keeping that in mind you know be able to assess security from what an adversary or a cyber criminal would would view is a way to uncover vulnerabilities that may not otherwise be detected you may run a vulnerability scan but unless you're able to get on that system you really don't truly understand how vulnerable that system is and exploitable vulnerabilities are higher risk at a higher priority for remediation sometimes remediation these security flaws
can be very expensive it could mean replacing firewalls or adding new software possibly adding new security roles to the company so this could be expensive and an exploitable vulnerability is a higher risk and more of a priority to remediate and so this a lot of times go into the justification for budgeting new new equipment and staff too so this is why this is really important also regulatory compliance pci dss the payment card industry data security standard has driven a lot of pen testing over the past several years i used to work for a bank and we had like a 13 person pen test team and all of our pen testing was focused on pci that was the reason in the what
drove the pen test and the budgeting for the staff for that size to perform pentest it's a fun job and there's a lot of opportunities as pen testing when i got started in 2012 most of the pentest jobs were either contract or consulting jobs and so as pci and other industry needs and compliance has come along then there's been more opportunity for jobs if you have like 500 applications you need tested for a company and you go through a consulting company you're going to spend a lot of money so if you have your own internal staff then that makes it a little more affordable in pen testing jobs when you're looking for a pen testing job
you know the more professional terms you know you've heard you've heard pentester but penetration testers in the long long-term uh form of the name security consultants analysts and engineers so a lot of times you have to kind of dig down into the description dot job description sometimes to see if it's a pen testing job because a lot of times you're going to see consultant or engineer so other terms synonymous with pen testing is ethical hackers offensive security adversarial security and threatened vulnerability management is a popular department where some of these type of functions reside under there's other skills that pen testing is important in so you may not be pen testing may not be your goal maybe
this is interesting you want to learn the skill and maybe you you know you aspire to be a pen tester but these skills will help you as you're learning along the way if you're a sock analyst you're able to understand malicious traffic better same same with a security analyst network security analyst and engineers understanding that malicious traffic digital forensics and incident response this is important that you're able to identify malicious traffic and it helps you to to investigate your your cases better if you understand the hacker mindset understand these attacks purple teams this is beginning to be something pretty popular where the red team offense and defense are working together to improve the defenses during pen tests
you can monitor the activity see if that it's being detected and then you know once you're finished go back in and run some of these types of attacks and tune your systems to make sure they're actually detecting that malicious behavior on the network also you know you're testing the people that are defending the network in application security this is another popular area and one of the areas if you're wanting to do pen testing the through bug bounties it's a quick way to get experience through working in production applications in different types of pentest targets it's not all just cutting dry network you have your wireless networks and then when you're testing networks you want to test it internally as well
as external external is not only a threat sometimes internal there was there's been stats thrown around over the years and i've seen sometimes threats there are actually internal can be up to 60 to 70 percent of the time not sure on the exact stats on that but there are insider threats you know there are people that will try to steal intellectual property that are actually hired that'll get a job within the company to go into the company to steal the intellectual property so the uh adversaries are internal as well as external and then wireless and external this is you know outside facing you know someone doesn't have to be inside your building to attack your
your network so these are very important applications are very important because you know a lot of the applications before used to be thick clients sitting on your desktop while you still have your microsoft office and those sort of tools a lot of the applications have gone to web-based because web-based is more mobile you can run it on mobile devices different operating systems and some you know kiosks and all sorts of things so it's a lot more flexible application that people are using so those are there's a big need for testing that as well as cloud and mobile applications hardware testing the routers and switches testing products you know right hard you know network hardware products you know when they
create new routers and switches they need to test the security on those that way that any bugs can be remediated before they're released out into the public iot is another popular area medical devices pacemakers and insulin pumps are connected by bluetooth even wi-fi i've done wireless pen tests before where for hospitals that i was going through there doing my scans and i saw you know medical devices showing up on the wireless network as well as i've done pen tests for for manufacturers of medical devices and just seeing those devices attached to a network kind of gives you a little you know kind of wears you a little bit look kind of scares you of what the
possibilities could be you know these are devices that if taking down it can harm someone so it's really important that they're secured as well as transportation with the self-driving vehicles on the horizon and soon to be out we need to make sure those are secure because if someone was able to take control over a self-driving vehicle you know they could cause a lot of harm so we need to make sure that those are secure uh people in buildings you know you have to make sure that the people that are doing the job of protecting your company whether they're security or just people that are just employees in different areas you have to make sure you need to make sure
that they're not letting people in the building without proper access and protecting your company so the way you test that is the social engineering you also test the building security like through physical security testing so these are a lot of times part of red teaming activities but these are all important areas that need to be tested and based on where you may start out is based on the experience you have if you have experience in networking then network pen testing may be the area for you to go into if you're a developer then application pen testing is going to come more easy for you as well as if you have experience working with hardware you
know firmware and that kind of stuff so work look in these different areas maybe if the the spot that you may want to focus on where you want to start your career as a pen tester in types of pen testing knowledge when you're doing a pen test there's a amount of knowledge that the tester has you know the black box pen test is going to be more similar to what an attacker is going to try to perform and it's important to do this while the white box or crystal box pen test is is important as well maybe that exterior is really tough to get into but if someone was able to find some someone's password
or you know brute force the password to get into it then you need to be able to test all the other security controls so with application pen tests you want to use a account level for each level of access thoroughly test that system and a lot of these are based on the amount of time you have if you have a lot of time then uh you can do black box that record requires more reconnaissance more time to test whereas the white box of crystal blocks test requires less time because you have more knowledge of the system you can have anything from like on top of a couch you can have diagrams of the network as well as documentation
about how the application is reading written even source code you know these are helpful in testing so that provides a more thorough test and grey box testing is kind of more common of what you're going to see as a pen tester it's kind of a cross between the two methods they give you enough information to be able to test the application or network well without giving you too much or too little so it's kind of a happy medium between the two and that can vary not everything is set in stone there's not just those three identical you know types of knowledge you could do you know it could be more defined or less defined so there's a lot of
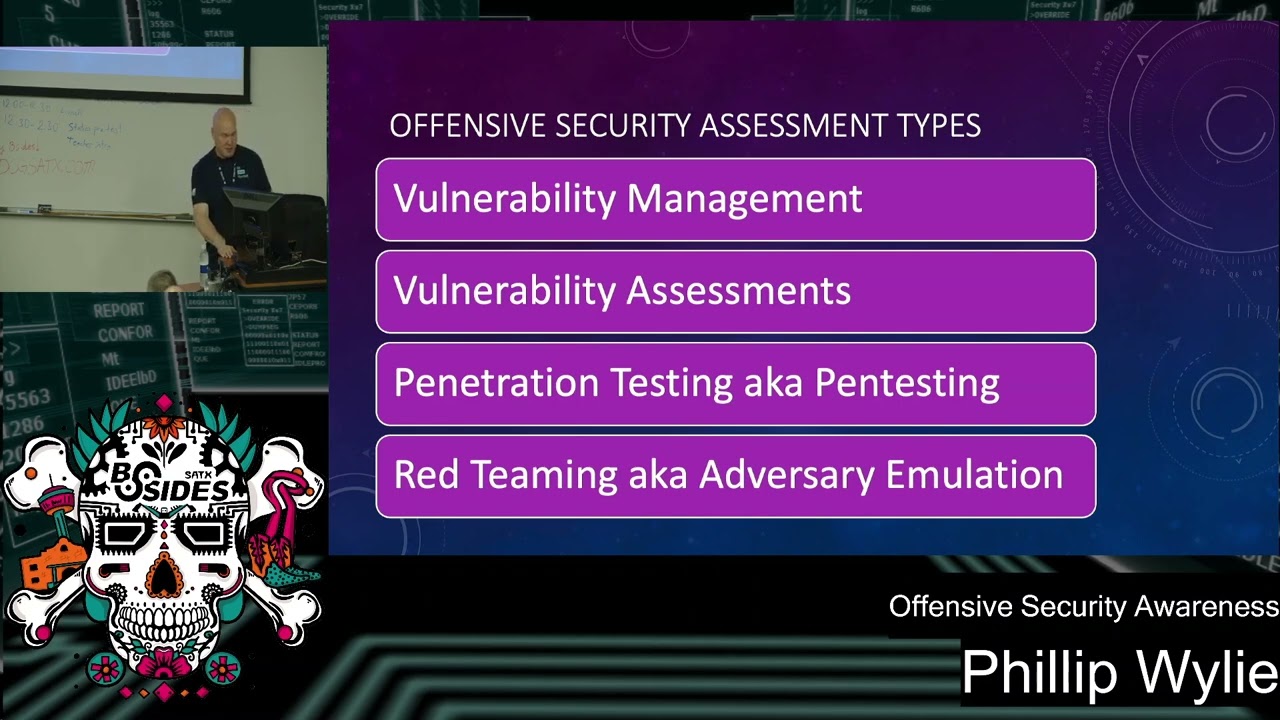
variance in there and it's going to depend on the time and different types of pen test steps now these first two as you see the red text it's not a pen test vulnerability scans is not a pen test this is running a scanner to look for vulnerabilities and this is actually part of a pen test is running vulnerability scans and then your vulnerability assessments is the next step above you run your vulnerability scans and then you validate those vulnerabilities to make sure they're not false positives and you can also run other tools during this process to detect vulnerabilities that maybe the vulnerability scanner might have missed and so the next step of these methods is pin testing so basically you've done
your vulnerability scans we've validated any of the vulnerabilities found any extra vulnerabilities with other tools so now we're going to go in and try to exploit or hack any of the vulnerabilities that we found that are not false positives once you get in that system you can see if you can go further and then you get into your red teaming or adversarial tests this is where you're testing the blue team it's an attack simulation less restrictive in scope usually so that way you're able to go in and test the reactions so you want to make sure that the ir team is seeing this activity that your ips ids is detecting this so you can shut down any of those kind of
activities so it's a good way a good exercise to test the test the blue team and different specializations so we kind of covered some of the different targets so some of these specializations there are in in pen testing most people are going to start out as a generalist this is the way i started out i did network pen testing and eventually moved in shortly after into wi-fi pin testing and then some light web application so even though it's a network pen test you're going to find web-based clients web-based servers and in admin portals for different administrative consoles so there's so sometimes that may be your only way in as a pen tester into the network is through the web application
layer and so there's applications web app mobile thick client and cloud and then social engineering a lot of people there's some people that will specialize in social engineering dealing with you know physical and security and and social engineering people i've known people who got their start that had no technical background but they were really good at talking to people had really good people skills and were good at social engineering so that was a way for them to start so that's a place for someone to start a lot of people just seem to be drawn to that area it seems more fun a little more thrilling to do so that's kind of an interesting area and
gets a lot of interest from people wanting to break in and then transportation there's companies a lot of the automobile industries they've got people to test their their vehicles and then red team the adversarial simulation and sometimes people just don't jump right into this it may be someone that's worked in social engineering have worked as a generalist this some light web application is good here but a lot of your skills there is going to be more focused on your your network pen testing as well as your social engineering and how to become a pen tester this is usually the reason people attend this talk they're wanting to get into pen testing so you need to understand the technology
before you can secure it or break into it so you really need to know networking operating systems at a sysadmin level meaning you can go into windows you can disable the network adapter connect to networks make configuration changes because if you get access to the system as a pen tester you want to see what else you can do if you've only got like a shell or command line access if you know the command line of that operating system you can shut down firewalls or services depending on your level of access to that system so you really need to know those operating systems otherwise you'll spend a lot of time on google trying to figure that as you
go and you need that base knowledge so you can utilize your time better and then understanding security because understanding security makes it easier to break into and then application and hardware other helpful areas to know as a pen tester and so you're so if you have your technology knowledge then the next thing you got to do is you got to learn to hack and this is kind of where the point i was at when i became a pen tester i had done vulnerability scans network as well as web application so i needed to learn how to hack so i started my job and i signed up for the oscp certification course and that's one of the courses
i've learned the most about pentesting because you really learned how to hack in that course and so it really helped help me in my career and conferences classes you know like these conferences you know we have workshops here in different talks on the subject going to meetings and meetups your local defcon groups your your hacker associations and stuff that's a good way to get in and learn about the different types of techniques and the more views and ideas of pen testing you get and hacking the better because everyone does it a little bit different and so someone may explain something that clicks with you better sometimes it's a matter of seeing this topic more than once to really get it
self-study home labs are great everyone should have a home lab there's a lot of good videos out there on youtube there's different tutorials that you can follow for self-study blogs articles and twitter and towards the end of this we're gonna we'll cover some different resources in these areas that'll help you and your your studies to become a pen tester but twitter is a great place to get information you're gonna find out about all the latest conferences where you can learn hacking techniques and pen testing so that's a really good great resource a lot of good people to follow there too and so to become a pen tester you really need the hacker mindset and so the hacker mindset is the ability
to think like a hacker be able to find ways and vulnerabilities into the system the hacker mindset is is kind of a combination of creativity and analytical thinking and so this is like one of the areas there's other areas in i.t and security that are creative but this is one area that really calls upon your your creativity and so developing the hacker mindset is similar to troubleshooting you know the first time you install windows or linux and if it goes perfect that's fine but then once you start having problems connecting the network or you install linux or windows another time and it doesn't go just right then you have to troubleshoot it and you learn so much from troubleshooting
and just kind of like hacking you when you try something that doesn't work then you know other directions to go other things to try and continue your research and continue to enumerate the system performing more recon so and then along the way you'll learn different hacks and so you'll identify okay this this is a java server you're able to upload uh a shell to it you know a malicious file to create a shell and get access to system so you kind of learn the different types of attacks and put those together and the best way to develop this is the repetition and hands-on hands-on hacking experience ctfs bug bounties home labs just practicing that and you just kind of build this
base level of knowledge that after a while there's just things that you just built you're able to know how to do without referring to your notes it's good to keep notes but you once you like any area of i t you know you know how to connect to the network you know how to set up apache web server these different things once you know those a little better then you're able to get your testing better you're building up that base knowledge and able to function better as a pen tester and so the pen tester blueprint formula is technology knowledge plus security knowledge plus the hacker mindset so these are the items that you need to be
successful as a pen tester and this takes time and one of the things i want to tell anyone getting into this be patient give yourself time hacking wasn't easy for me to learn it took some time to learn it so it takes time so give yourself you know time and be patient don't try to rush it and take your time as you learn you'll better absorb and remember things if you take your time don't try to rush through it so where do you start so you want to div you need to develop a plan so you kind of you're going to do a gap analysis on what you know and what you need to know so we've discussed that you need
technology knowledge you need to understand the technologies the security as well as the hacker mindset so we need to fill in those gaps some examples here if you have no i.t experience then start learning the basics the operating systems hardware and networking a good place to start here is look at like your a plus certification type material not saying that you have to get the a plus certification but there's videos out there like professor messer that you can go through learn the operating systems learn basic networking and then progress into like network plus type materials or even like the ccna learn your networking and then you know if you're you've got it experienced fill in those gaps of things that you're
you don't have experience with if you're a a help desk person you may not be dealing with linux much so learn linux learn security and networking so just fill in those gaps that you don't that you don't know an infosec experience same there you you may be to a level that you're understanding linux understanding networking but you got to get the hacking down so ctfs and bug bounties and labs and my my advice for everyone is build a home lab even if you're an experienced pen tester i t person security analyst having a home lab is good even as a pen tester we have labs set up that we can test our proof of concept codes
if we have some exploit we want to perform on a vulnerability we found on the network or something new comes out we want to test that ahead of time because sometimes exploits can have adverse reaction effects on a network so you can crash a system so you want to test it first and work out any kind of bug so this is good and it's way to learn techniques because you may not run across all these scenarios in a pen test so having a lab you're able to test all the newest latest attacks in your home lab and then your labs so i kind of categorize this and this can vary the minimalist lab is one of my favorites
and this is just having virtualized hosts on your your laptop or your desktop computer so you're running a virtual machine with uh kali linux or and then your attack platforms the vulnerable vms that you want to attack and then you have your dedicated labs where you can have like separate systems you can have like a one computer with just your vulnerable vms on it and you can get more advanced you can have separate servers you know you can hook up some raspberry pi's to your network for your like client computers or little servers uh you can set up routers and switches even wireless networks so you can build it as complex as you want to and
that's a good way to learn learn these uh technologies but keep in mind also too the more complex you build it the more troubleshooting you may have to spend when you're working your lab if something doesn't work right then you have to go back and and fix that so keep that in mind as you're building your lab and i personally have a small server that i built with vms on it as well as i run some vulnerable vms on my laptop and so your home tech lab attack platform so you have to have something that your tools are on that you're hacking with and so kali linux is my my top choice and parrot os is a good uh
operating system as well for linux i recently used that for the first time i did a wireless pen test cali linux wasn't working out so well with the drivers for some of my network cards that i was using and some of the tools just with the newer version of kali linux some of the updates trying to use some of the wireless tools just didn't work right and paired os everything worked like a champ and i was able to install other tools pretty easily and ubuntu is another route to go you can use the pentester framework scripts from trustedsec and install all the pen testing tools on there and run it from that perspective and then there's also your windows
option windows 10 with the commando vm scripts it runs some automated scripts similar to what the pen tester framework does but this installs the pen testing and hacking tools on windows and it also sets up security so windows defender doesn't go in and delete your pen testing tools and exploit code from your system so it sets the security up for free there so that's a nice added feature as your pen testing platform i recommend even like from a professional perspective i like to have like either a a intel based system that i'm running ubuntu as my host os or mac os with vms on that or windows and i will run like a a windows vm for the windows tools
as well as a linux vm so it's good to get the experience with the windows tools linux i mean the experience with windows tools because the linux stuff is very popular but it's good to learn the windows stuff because there's some tools there that can that are very helpful on a pen test and home lab targets so you can create virtual machines there's a lot of targets on vault hub that you can download a lot of ctfs will will upload their their the vms of their ctfs so you have those to play around with as well as there's metasploitable two and three these are two vms i highly recommend starting out with they're really dense with
vulnerabilities that you can exploit to get the same similar benefits from other vms you may have to install multiple vms or vulnerable applications to get the same amount of targets but with metasploitable 2 you have a lot of vulnerability so one of those vms can keep you busy for a while and there's a lot of walkthroughs on those two vms that you can go through and learn how to pen test you can look at the different walkthroughs and compare how other people are doing it differently and pick up some helpful techniques and then a wasp web goat as well as uh juice shop and several other vulnerable vms that you can find on owasp.org's website are great and you
can build your own vm targets go to exploitdb download the vulnerable software build your own targets at home just like testing your proof of concept code some new vulnerability comes out and maybe it's been patched then you can go back and get vulnerable versions of the software and set that up in your home lab to test it then of course like your your different vulnerable vms like hack the box and try hack me are good options as well and some recommended reading here so uh the first semester of or actually the first year i taught the ethical hacking class i used the book penetration testing a hands-on introduction to hacking by georgia whitman this is a great book
for anyone starting out it takes you through setting up your own home lab so you can go through and set up your lab this was really great book for anyone's going through the oscp they cover a lot of topics there that are helpful in preparing for the oscp and the next book i'd recommend or the next books would be the hacker playbook two and three and don't skip version two because version three gets more into red teaming which is good but you don't want to miss out on the items in the hacker playbook too so the hack the first book the penetration testing hands-on introduction to hacking will help you build a base and the hacker's playbooks will help you
you hone your skills and and improve your your pen testing skills with that then the hacker's playbook exploiting discovering exploiting flaws security flaws is a great book created by one of the creators of burp suite so this is a really good book for web application pen testing and the red team field manual that's that's another good book that's filled with a lot of different command lines for linux windows powershell a lot of different admin related functions and there's another book out that i didn't put on i forgot to update this slide but another book that i recommend getting this is good for anyone blue team or red team uh pen testers but the the operation operator handbook this is
a good book uh it's a lot thicker than the red team field manual this covers anything from like kubernetes uh gets into a lot of advanced networking stuff so this is a really great resource to have and it's available in ebook format whereas the red team field manual is only in a printed format and here's some learning resources so i've got these divided out by paid and free resources and if you look at the top section i start these by from most expensive to least expensive sans institute if you're these are usually courses that if your company's paying for your training that's great there's 7 200 courses typically for a six day course they've got some other ones that are
like two days long like the red team course that are like thirty eight hundred dollars they're less expensive but then you get to your elearn security these are like from a thousand to like thirteen fourteen hundred dollars per club per class it's really good defensive security they have a lot of advanced pen testing related uh courses there like the oscp that's a good one and then virtual hacking labs that's like 750 for a year's worth of access to this hacking lab and it has an online course with it that's a good one to prep for the oscp and then you have pentester academy pentester academy has a large library of pen testing videos covering anything from
mobile to wireless to javascript for pen testers python for pen testers different uh topics related to wireshark t-shark some light forensic stuff active directory security and hacking and then there's pentester lab this one focuses more on web application pen testing but where they differ from some of the other the other resources are that they go into types of exploits that will get you command line access that you're able to actually hack the system and not just discovered vulnerabilities and that one's pretty pretty cost effective in a really good course you can build a lot of linux security skills from that course they teach you how you can exploit the different uh unix linux vulnerabilities and then
practical pentest labs is 64 for lifetime access it's mainly a linux based lab you access it through vpn and they've got like a short little pdf course showing you how to do port scans and stuff to get started so that's a very cost effective uh resource and i kind of played around with that it's a lot of fun and good to have and then you get into we're getting into our free resources uh bug crowd university and hacker one these are bug bug bounty resources uh they have videos as well as different tutorials and stuff hacker one has an online ctf and they actually you go through the ctf and the training modules to learn how to
do web application pen testing which helps you in turn be a bug bounty hunter and those skills can also be used as a pen tester sans has a really good blog the sans pen testing blog there's uh different cheat sheets on different tools and techniques out there so this is a really good resource and hackingtutorials.org this is from the creators of the virtual hacking labs that i mentioned on the above part of the slide and this is tutorials related to nmap metasploit different types of exploits out there so it's a really good free resource for learning and then cyborg.it has some free resources some paid but there's a lot of good uh free materials out there on pen
testing and then web security academy from the creators of the web application hackers handbook and burp suite the web web security academy out there in portswigger has a lot of learning materials they have learning content plus online labs that are completely free so it's a really good place to learn and then owasp the wasp website the creators of the owasp top 10. there's the owasp testing guide for web app pen testing as well as testing guides and recommendations for mobile and iot and then hack the box.eu is another good place there's some good vms on there tj null recommends some vms on there for preparing for the oscp and then over the wire ctf as well as
under the wire ctf over the wire is more linux based and then under the wire is more windows based and power and powershell based so those are really good and to find these resources if you go to my website the hackermaker.com learning dash resources there's a link to this page with links to the resources so you can check that out if you don't have the screenshot of the slide in different certifications this is a question i get a lot you know uh what got me into teaching and doing conference stuff workshops and all that was originally just sharing information with people i really like that teaching and conference is a way to do that on a bigger scale
so the question you always get is you know do i need certifications and which certifications do i need to get your foot in the door it's very helpful to have a certification because sometimes it can really be difficult to get that first interview if you really understand and know it then you could possibly get through the interview but just getting your foot in the door can be difficult so things like the ceh and pentest plus you know could possibly get you interviews because hr and hiring managers are really familiar with the the ceh but to get into your certifications that are going to help you from a standpoint of the knowledge you're gaining from that
and and looked at by a lot of hiring managers are your your sans g pin cert your oscp your gxpn by sans and the osce these are pretty similar certs between the sans and offensive security although with offensive security you actually have to perform pen test you actually have to hack into systems to pass the exam whereas the sans certifications are more question and answer they'll give you items to be able to say what is this nmap scan do or whatever that that type of stuff it's good information and uh and very helpful for getting employment but like my oscp i've gotten out of the hands-on portion technical portions of interviews before because the hiring manager or the person who
recommended me said you know he was able to pass the oscp he's able to do our lab so it's it's a the oscp is has given me a lot of mileage as far in my pen test career and that you know this and then the other one you know the difference between you know the we have the intermediate intermediate and advanced and these are these are all good to have one thing i'll say too is while you're preparing for these certifications learn the topics the ones like the you know your ceh or pentest plus where you're not actually having to do a pen test or stuff or hack things you need to make sure to learn it because
when you go through the interview you're going to need to be able to answer the questions so make sure to learn it don't just pass the certification test the information you learn is going to be helpful as a pen tester and helpful interview this is going to help you answer the questions as you go through your interviews and there's also some other good other certifications out there through elearn security although their their certifications are starting to gain more uh notoriety people are starting to become familiar with it it's really good and i can tell you as far as taking those certification courses to learn how to pen test they're really good you'll learn how to pen test
because you have to perform a pen test and write a report so those are very very valuable although not as quite sought out yet i think that'll change as popularity catches on and job hunting tips so if you're wanting to become a pen tester professional networking you know conferences like you're doing here different meetups go to the different meetup groups get to know people my last three permanent jobs full-time jobs have been through connections i had in the security community my second pen testing job was through the founder wirefall from dallas hackers association he referred me for a job i got my job at u.s bank from attending a san an actual wasp meeting local oas meeting one of the people
there presenting told me the u.s bank was hiring so i was able to get referred and get a job there from that referral and i referred people that i know from the community that were looking for pen test jobs you know you get out there and don't just show up get to know people network people talk to you they know you're interested then they can pass on your information and share jobs with you i've seen people get hired out of our local meetup groups a young college grad from ut arlington did a a discussion or did a presentation at our local defcon group on malware uh analysis and the hiring manager for a major financial company was there
saw his presentation and needed an incident response person asked for his resume and he got a job and linkedin you know linkedin make sure you fill that out this is your online resume this is going to get people to you unless you're getting resumes out there they're not going to find you but if you're on linkedin they see the keywords for pen testing they will look at your your profile and that's how you know to help you get your foot in the door help you get interviews and keep it professional make sure that when you're posting on linkedin treat it professionally it's not facebook so you want to make sure you keep it professional make sure you put the the you know the
information on courses you've taken you know the type of experience you have in your skills that way people can find that easier and interview tips so when you're getting ready for interview prepare for your interview even as an experienced infrastruct person and pen tester i find that i do better on interviews if i prepare for it there may be some thing that you're not touching or you haven't worked with in that in the current job you're in in a while so sometimes go back and review review those topics uh the oau's top 10 pen testers are always asked these questions their interviews cross-site scripting sql injection or two of the most popular items you're going to be
questioned on during a pen test interview so understanding those vulnerabilities not just memorizing understand the vulnerabilities the different variations and types like sql injection you want to make sure you understand blind sql injection time-based sql ejection cross-site scripting your stored and reflected cross-site scripting understand those and how to remediate those because those are the questions i'm going to answer you ask you so really go over to know that and knowing that oh watch top 10 is going to help you a lot in your career and then some of the stuff that's that you wouldn't expect to get asked like the basics like 3-way tcp handshake or osi model people that are more experienced in management that may have been away from
things for a while they don't they may not be as technical and may not ask some of the more current type questions so they're going to ask you stuff about the osi model in a three-way tcp handshake this is kind of you know basic stuff you know it101 that they expect you to know so kind of know those when you're going to the interview that'll go a long way one of my last job interviews i had the director asked me questions on the osi model and tcp handshake during my interview so not a lot of times those aren't technical interviews but they will throw in some some technical questions to get a better idea of you know your skill set
and your knowledge and uh this is my contact information uh there's the link for pawn school up here so we stream our talks each month as well as we have a youtube channel with recorded talks on there so please feel free to check that out we've got a meeting coming up wednesday and on the phone school website you can find links to our meetup page to get the links to be able to access the streams as well as the youtube channel with the recordings on there and we have a link to our slack channel so we have a lot of industry professionals on there that have pen testing background blue team background we've got people
thread hunting experience so it's a really good place to network and share ideas and get information and i i teach ethical hacking classes and web app testing classes originally college which recently rebranded the dallas community colleges are now dallas college and then i'm also check out the uncommon journey podcast on it sp magazine and here's my social media information my email address feel free to reach out to me because i'm always answering questions and happy to help people out this stuff is my hobby it's not only my job not only what i teach this is my hobby you know my ideal hobby is going to to defcon and black hat that's fun for me so
i live and breathe this stuff i like to talk about it all the time so feel free to reach out to me ask me questions i'm happy to help share any kind of learning uh materials if there is any specific thing you want to get into and you need more information i'm happy to help you so check those out and follow me on twitter i'm always posting about any free conferences and and trainings i'm doing so connect there and so if anyone has any questions i'll be happy to answer your questions bill we have a number of questions that are coming from the track three uh discord channel so if you don't if you don't mind i'd go ahead and just start
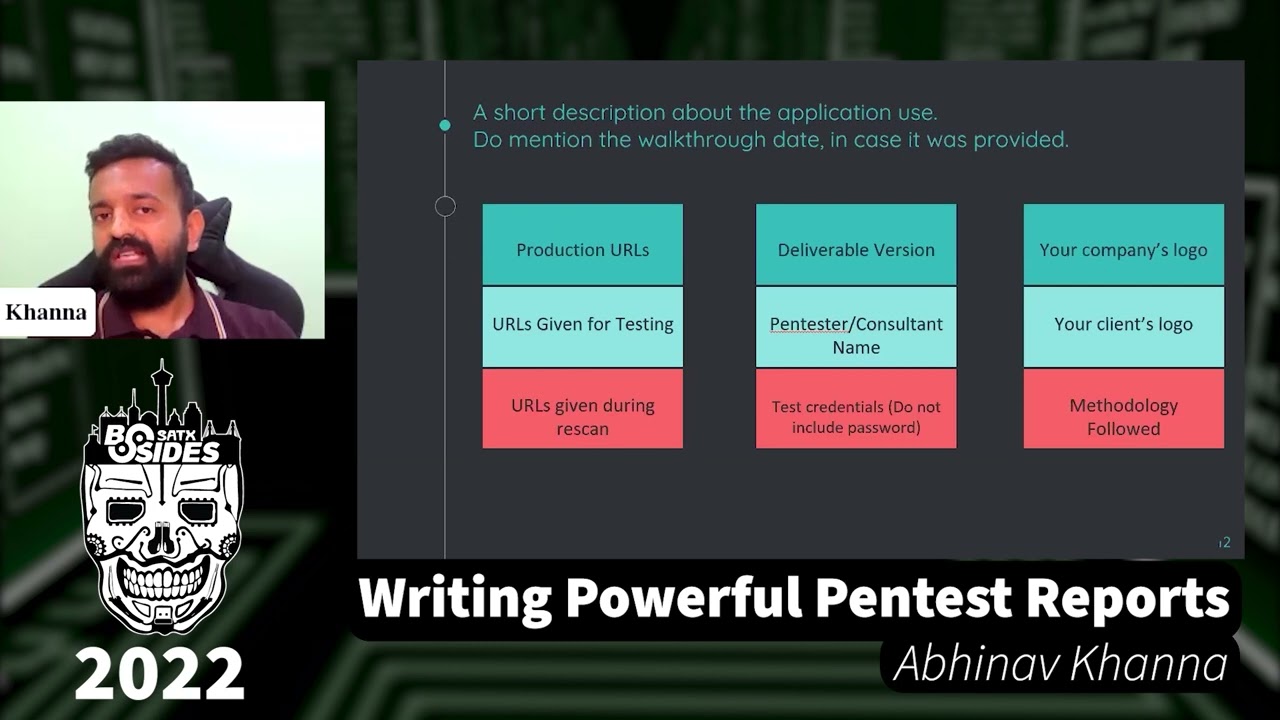
those off for you uh what about documentation during an event um the hardest part for me is writing the report is there a template that you find helpful to leverage maybe a punch list you use of all the things you cover yeah what what i recommend is looking at when you look at stuff like the p-test standard they kind of show you things that you need to do during your pen test and as far as documenting that a great resource is tradis they have dratis has a community edition of their software and it's a report writing and collaboration tool and i believe it's if it's not installed by default on kali linux it's in the the kali linux repository so
you just can do like an apt install uh dratis you know install that but what dredis does is not only does it collaborate it's a report generating tool and it also has like a checklist so you can define your pen testing methodology and it creates your checklist so i've used the pro version before and it works great and the community edition also has this checklist so you can choose the p-test standard for your typical pen test and you will select on what portion of the pen test and it'll show you different things to try for the type of pen test you're doing so it's kind of a good reminder and a checklist and aside from the report generating
functions because there's not a lot of it's hard to find a good report template out there but this will let you track your your pen test as you're going along you upload your nmap scans to it you upload your nessus scans burp suite and then you create a report out of it it takes all that information and generates a report for you so this is a way to keep track of your pen test and also note taking you use something like joplin evernote keep note onenote one of these note-taking tools and as you're pen testing go through and attach your ness's output or take screenshots take your screenshots as you're going along if you exploit a system it may not be
exploitable next time you may have ran it sometimes the exploits does something to the tcp ports that you're not able to do that exploit again so as you're going make sure you're taking notes so that way you remember how you exploited it take your screenshots your notes and populate that notebook that note taking tool create a node for each ip address or even group of ips that you run your map scans again take the output of each one of your tools that way you can refer back to it to look for you know exploits you can use against those vulnerabilities as well as when you write your report you've got screenshots there you've got output from
nmap all your evidence there so when you go to build your report you've got a nice neatly organized another question from our channel do you feel that the news and others have maligned the term hacker i noticed that you used the term cybercriminal appropriately and would like your thoughts on this yes it's it's exactly the media and that's where it came from so most people that know the story of hackers back when you know hacking at one time the hacker term was really people if you think about the hackerspace makerspace where people are building things or trying to modify technology to different different things that's where hacking came from in the media the news would refer to cyber criminals as
hackers so that's how it got coined is that way so we like to make sure you know because it's even locksmiths know how to break into a house but they do it ethically so as a security professionals we need to kind of help try to correct the mindset that way people separate it you know because it kind of gives us makes us look bad and and trying to build the trust you know media has made hackers sound bad so so definitely it's been the news that his coin that's where the where you know cyber criminals got the tag from um another uh post from inside of our channel uh one of the uh attendees is asking
uh the guy that has cea certification after the training he is the pressure for the job uh and he would not know where to fly and how to apply how can he enter into the field of cyber security if he is a newbie without much experience well one of the things i'd recommend is try is do bug bounties and and ctfs uh that way you're gonna get the experience network go to different meetups and connect with people online because people try to help you out there but uh is trying to get connect sometimes if you're you may have to take a job in i.t or security and then work your way into a pin testing role and there's nothing
wrong with that if you say you're just you you got a ceh cert or you just finished school nothing wrong with taking a sock analyst job you can learn a lot about that so i don't know if anyone here follows tinker sec from from twitter he's like a really great hacker and he never took any certification courses all self-study no certs and uh you know he's he's done well with without having the certifications and he just knowing you know knowing people in the community and he was a sock analyst so he worked as a sock analyst and someone heard him speak at dallas hackers and he got his foot in just you know you just have to get out
there and and network with people and you know and it doesn't have to be like a immediate meet up that's geared towards pen testing you're going to find a lot of your opportunities in more of the generic security type meetups your issa meetings because these are where the hiring managers are going to looking for people and just keep practicing and and working on it you know the bug bounty stuff i mean you could go to with the bug bounties you can get invited to do pen tests they a lot of these bug bounties companies also do pen test along with bug bounty so you can get invited to do pen tests and then once you're doing pen
test you've got this on your resume and you know working on projects working on scripts volunteers some of these open source projects is a good way to get that information good stuff on your resume okay philip we have uh one more question if you don't mind no i don't know what is your advice to a current help desk person who wants to become a pen tester red teamer i got the oscp in my pocket do they already have their scp or is that what they're focusing on that's uh i believe what they're trying to focus on yeah the oscp is going to help you is going to help you get your foot in the door there
and where you're at one thing's it's easier to sometimes get into a role if you already work somewhere so if your company has a security department you know just let them know you're interested in security because i uh expressed my interest of wanting to move into security back in like 2009 and 2000 when i worked at the company and it took me to 2004 to actually get to move into security they knew i had the interest at the time they didn't have the roles but yeah work on the oscp the information you get for that if you can land an interview and you you pass the oscp and really dig in and learn that stuff you're going to be able
to get through a technical interview well phil as always thank you for submitting your time and for your presentation today personally i could say this is one of the best presentations i've seen and that resonates across the discord channel that we're seeing so thank you for sharing all of this um immense information that you've gathered for us and thank you for your contribution to the cyber security community thank you for the opportunity i always love the chance to share and and educate so this is uh it's great like one of the things that's you know like they say it's better to give than receive and you know sometimes i think i get more than this than the people that
that are actually asking for the information so thank you thank you thanks phillip great content
you