Optimal Offensive Security Programs
Show transcript [en]
we're good cool good morning morning good to see this nice big crowd this is a big beat size this is quite a bit larger than ones we do in uh in Dallas World work besides DW everything's supposed to be bigger in Texas but you guys got to beat so so awesome to be here thanks to besides Billy for inviting me to be the keynote it's an honor to be here and you know it's going to be a good time when you see Rando so so this presentation was based off of my experience working in a company uh as a red team lead and it was kind of interesting because I end up creating this single
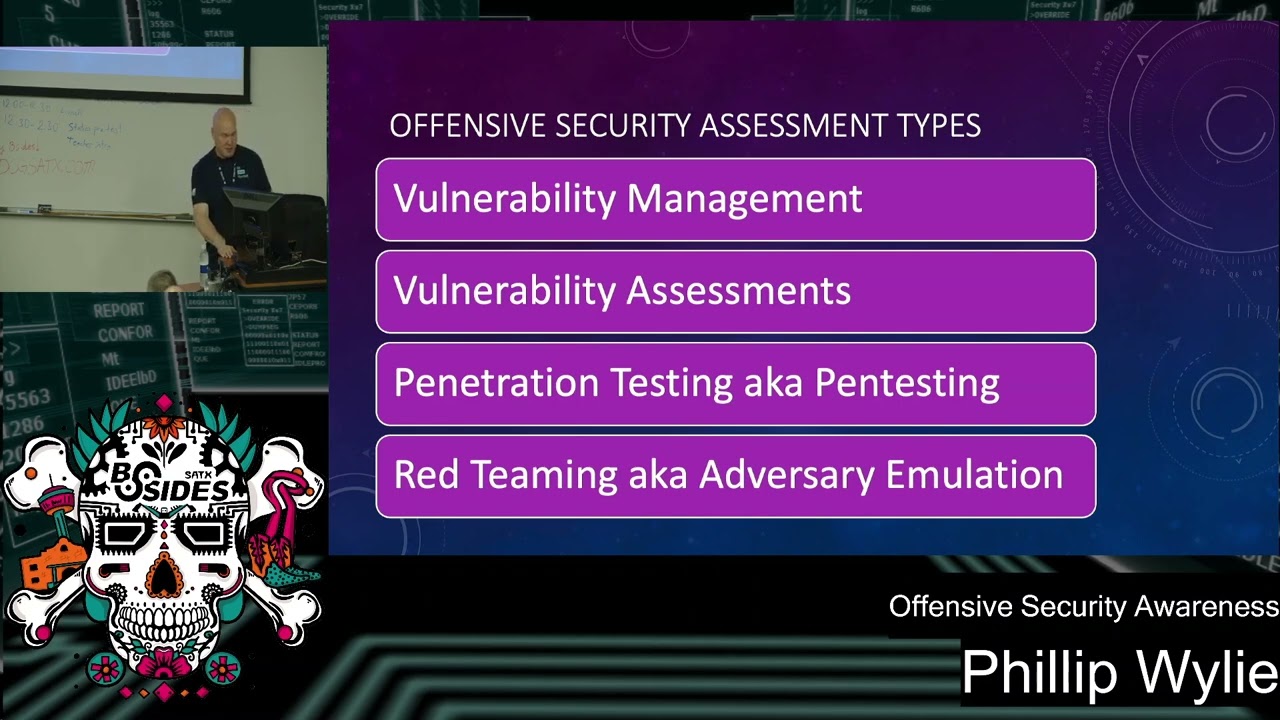
slide because people in the organization you know when you work in a certain area sometimes you take for granted and think everyone should understand the area you're in cyber security you should understand offensive security but that's not the case so in the organization we had people that were you know on The Blue Team uh people in project management different areas within cyber security didn't know the difference between uh red teaming pentesting vulnerability assessments vulnerability scanning we had a director there that actually wanted a red teaming operation done against the sap app and so I created this single slide that showed the difference between the different types of offensive security assessments including like vulnerability management and so forth so we'll
actually have have that slide in this presentation but that's where it was where the inspiration came from uh this was originally I did a talk called offensive security awareness and then kind of saw the need to show some of the gaps that we see in in traditional pentesting and areas to improve so that is something new to the presentation uh but that's kind of the updates to that so kind of a little bit about my background I've been in offensive security for uh over 12 years cyber security for for 20 January make 21 years and I was a assist admin for the first 6 years and for anyone that's wanting to get into cyber security uh if
you can't get a security job starting out I recommend something like being a CIS adman the best experience I had helping me become a pentester was the time I spent as a sis admin because you ever get shell to a system and you don't understand the operating system you're going to be doing a lot of Googling and not doing very much so also I'm an offensive security instructor and former adjunct instructor here I used to teach at Dallas College I taught pentesting we about pentesting there for almost uh 4 years and that's really what got me interested to speaking because I like to share information and before I would just share information for anyone that wanted
to become ocp certified to become a pentester and then the opportunity came around in 2018 to be an adun instructor at Dallas college so I had the uh pleasure of building out that program there running it for almost four years and during that time uh I had had a lecture I gave my class on pentesting careers uh first time I gave that lecture was in January 2018 by November 2018 I turned into a conference talk titled the pentester blueprint and then later on made a book out of it because I saw that this was good information because there's tons of good books out there on pentesting but none of them were really showing you where to start
out what you needed to know before uh becoming it or train to become a pentester coach and so I'm also a podcaster so I host the Philip Wy show previously hosted the hacker Factory I went independent last year so you got to check it out I have all my guests share their hacker origin story kind of how they got started my most recent episode was with Jason Street next week is John Hammond I've got an 0 from Dual Corp coming out in a couple weeks and so I'm also a part of the Cyber circus Network so we're going to be presenting later on today we're doing a live podcast episode so I hope you're able to attend that
and so some fun facts about me so I usually only include this in my uh career talks but I figured this would be worth sharing so before I ever decided to get into it or any of that uh when I graduated high school I didn't know what I wanted to do for a living so I was a power off my friends say hey you're a big guy you should become a pro wrestler so I went to wrestling school and I wrestled for a couple years uh so and this is actually me wrestling in where the picture of the yellow t-shirtt this is me wrestling a 750 lb here it was a nightclub I worked at so uh working as a
pro wrestler I was lucky to wrestle once a week and it wasn't enough to make a living so my main job was working as a bouncer and the organization that the uh nightclub I worked at they had special events on on Sundays because it wasn't worth the expense of paying a band so they'd have special events like this and they had wrestling bear come in which was open to anyone to wrestle and so the other other one is at the same nightclub I didn't have any good decent resolution pictures from my wrestling day but this was a match we put on there but I wrestled in WCW and wccw went to wrestling school with the Undertaker uh
I wrestled the road warar M ey Express rock and roll Express fabulous free birds so I just figur that'd be something fun to share and one of the reasons I like to share this in career talks and sometimes people don't think they can do certain things I never thought I'd use my mind for a living I always thought it would be something physical and then over the years you know I had to find a better career went to CAD school that's where I got exposed to computers got into it from that as a CIS admin so just something I like to share with folks especially you know the aspiring Security Professionals and and this is something for if you if you to
help people remember me by so the agenda so we're going to do an introduction to offensive security uh the different types of offensive security approaches identifying the gaps in offensive Security Programs and strategies for optimizing and overcoming gaps in offensive security so offensive security is basically assessing the security from the threat actor perspective you're always seeing in the news these companies being breached by threat actors uh you know nation states you know whatever level a threat actor but there's no better way to assess your security than from a threat actor perspective you can run a vulnerability scanner and find vulnerabilities but in some cases it may be vulnerable to the certain cve but maybe there's mitigating
controls that would not allow someone to uh exploit that system so this is why you want to do a pentest against system so you're you're using different techniques like computer hacking which is is the the most understood part of it or most realized and then also some physical uh testing as well as social engineering a lot of these different ransomware attacks and breaches people get the foothold in from uh social engineering and so offensive security is an important complement to vulnerability management so this is kind of testing how well your vulnerability Management program is working so after you know you're doing your your uh vulnerability Management Programs but you're not really sure how well it's work working
are any of those uh vulnerabilities actually exploitable what can be H what can be done past that vulnerability that's exploitable can someone Exel data get access to data so doing V doing the uh pentest is a good way to validate your offensive Securities uh your vulnerability Management program so different assessment targets so this is kind of changing over time it's uh you know computers networks hosts you know laptops iot devices Cloud a lot of things shifted to Cloud since I've started in pentesting in 2012 you know there's been a big push to the cloud and we're seeing a lot of that so uh Hardware devices even like some of the medical devices are starting to
require uh that pent test be done because you know one time you know the thing you have to we've got great innovators in the world in our country but people don't always think about security so you build these devices medical devices and you're not expecting anyone to try to hack into those devices so now that they're starting to require that because you know if you're able to exploit an insulin pump or a pacemaker you could kill or harm someone so it's important that these are tested iot and IC this is becoming very critical because you know our critical infrastructure people trying to uh attack water treatment plants electrical facilities so it's very important physical security is one area that gets
overlooked a lot and we'll get into some of the the gap and stuff around that area further in his presentation so different uh offensive security types so one one of the things that we got listed here the first one is vulnerability management it's not truly an offensive security approach or or type of test but it needs to be included because you should have vulnerability Management in your program so the next step is vulnerability assessments penetration testing red teaming also known as adversary emulation and we'll get into details and show the differences between red teaming and P testing because a lot of times there's a lot of overlap and through this presentation uh one of the things
to keep in mind is you don't necessarily have to use that same terminology but it's important if you were going to have a red team operation conducted make sure that you know you're on the right page that you're using the same terminology because some vendors there's a lot of vendor products out there they we call it red team I've seen some bug Bounty platforms that refer to their platform or their team is red team which truly not it's really pentesting but just as long as you know the difference that's going to be helpful and that's one of the also The Inspirations to this presentation is you just need to understand enough of this to be able to work with the defensive
security teams and understand to help be a better consumer and and decide on what type of uh assessment that you need so vulnerability management is the cyclical practice of uh identifying classifying prioritizing remediating and mitigating vulnerabilities vulnerability management is an integral uh integral to computer security and network security must not be confused with vulnerability assessment and we kind of see the steps here so you got the you're doing the asset inventory uh an asset Discovery one of the important things that we need to make sure is we have a a complete inventory because if you don't know what you have you're not able to protect it or assess it so you need to make sure
you've got a good asset inventory and with Shadow it this is can be a real problem you know back in my say admin days it was a little more difficult to just build infrastructure you have to bring someone in it was Tech will build a server and install the apps and so on but now with the cloud it's easy for people to spend stuff up fairly quickly maybe marketing team need to to uh spin up some microservices to do some ads for marketing and stuff so it's really important that we're doing this asset uh discovering inventory then you do your vulnerability scanning and then vulnerability remediation including patching you want to make sure that you're doing your ongoing patching as
you know Patch Tuesday comes out you get these new vulnerabilities you need to make sure that you're going going through patching and then kind of testing after that to make sure that that didn't open up any holes and then repeat the process cuz in traditionally vulnerability management is what goes on kind of between your pen tests because a lot of times companies May to have a budget to do continual pen tests or frequent pentest so vulnerability management is something that's kind of in between that helps you out between pentest so vulnerability assessments are kind of similar although we go a step further with a vulnerability assessment we're doing not only vulnerability scanning we're valid the vulnerabilities
to make sure they're not false positives and this could be done by using a secondary vulnerability scanner because there's times vulnerability scanners may find something the other one doesn't I had an example where I was back in one of my consulting jobs I was doing a pent test for this company they're using rapid 7 nexos and I found something with nessus that rapid 7 nexos wasn't discovering and there's cases where it may be the other around other way around some vendors will get the cves into their platform sooner than the others and so just different types of manual Discovery and and different manual testing tools metlo has a a lot of good auxiliary modules you can use to look
for uh vulnerabilities and do uh Discovery with so using a lot of the different type of tools you use in pen testing but you're not exploiting so what you you're doing is validating the vulnerabilities uh a step you can go a little further to make your vulnerability assessment a little more effective is to see if any of the vulnerabilities are exploitable but not exploit the vulnerabilities then then document that report look up any poc's and list that in your report so that way they know and this may be kind of uh a way to show them that they need to perform a pen test that a vulnerability assessment wasn't enough and there's cases when you want to do a
vulnerability assessment I was doing a pentest for a hospital chain and this wi-fi pentest and I got in the hospital and I was starting to do my scans and I was starting to discover medical devices hooked up to the Wi-Fi network in the emergency room and operating rooms and so that's one of the cases you really don't want to be uh doing things that could like running a ness's bability scanner may not be the best idea for you know trying to hack any of these systems so what I did is I went back to the ceso we changed up the way we're doing the assessment so we changed it to a vulnerability assessment but I did a uh
a wireless access point and wireless controller configuration review to look for any vulnerabilities there combined with a vulnerability assessment to reduce any risk or of injury or taking out any kind of U critical medical devices and there's some cases with OT and ICS environements that you may want to do a vulnerability assessment and have to be really careful in your approach so penetration tests or pen test for short or similar to a vulnerability assessment we how the vulnerability assessment we did the vulnerability scans the discovery and all this validating the vulnerabilities we're testing to see if they're exploitable and then would go in and actually actually exploit the vulnerability see what we can do past
that are you able to do any kind of post exploitation sometimes you know when you're you're new to pet testing which I was guilty of you're more focused on getting domain admin uh admin or route to the system but your your your your data is your crown jewels your information because this is why thread actors are using ransomware to encrypt your data to be able to find a way to monetize what they're gaining access to and so uh doing you know you can test data EX exfiltration is one of the ways to take this a step further other post exploitation uh methods like lateral movement and prival escalation and so the different types of testing so the main you mainly hear
Black Box and white box mentioned black box is also known as a blind pentest white white box pentest is also referred to as a crystal crystal box or assume breach so the black box is more of an attacker approach this is limited information and and this get varied because really one of the things you want to make sure when you're doing these kind of test that you have the full scope that you want tested because if you lean specifically on a black box test you're dependent on reconnaissance to discover all these systems that need to be tested and you're not given a full scope then there's a good chance they may get missed so you really want to
include that scope with the white box you get a little more detailed so white box you've got the fully defined scope if it's an application then you've got source code to do static source code analysis against that to thoroughly test it uh for an application you want to test authenticated on every level of access to that system to make sure if you're a user you can't access information that a administrator can access and if you're just uh if you're an administrator there's certain information that you don't need to be accessing so you want to test these different levels and over the years something interesting's kind of happened and and what brought this about in infrastructure is doing an assume breach
doing a pentest for credentials is the fact that a lot of times pentest companies were going out they couldn't get that foothold cuz they didn't have credentials maybe it was hard to haveen that system and they couldn't make get a foothold unless they were doing something like uh social engineering doing some type of fishing campaign so a way to overcome that is with credentials because we have Insider threats so you have cases where no before had was infiltrated by uh people from North Korea and then you see instances where I talked to one the company back in 20 2019 that we got our uh threat intelligence from and they were talking about a hardware company where a nation
state implant was within this organization so they had access to the system it makes it easier some of the stuff that they would want to get intellectual property wise everyone may have access to so they're able to steal this data as a legitimate employee so The Insider threat is always been an issue I mean I'm sure some of us in the room that's been around for a while you've heard the story of the developer that worked at the bank that set the uh deposit application to take like a fraction of a set and deposit another account and then having hundreds of thousand thousands of customers over time it adds up to a significant amount of money so Insider threats also disg
employees uh Insider threads also taking consideration ransomware so what the level access you have if you click on uh a link that has ransomware in it then whoever the the attacker is has that level of access so there a lot of reasons to do that you want to thoroughly test it some people that are hardcore hackers think this is cheating but really you need to thoroughly test your systems and doing that with an authenticated approach is the way to go and you can start out with a blackbox approach see if you can get a foo hole see if you can hack in and then if you can't go to the assume breach that way you're thoroughly testing cuz like I
said before companies will come in they couldn't get a foothold they write up on write up the report and it look good the company thought they were secure but they didn't take in effect uh you know Insider threats then there's also a great box this is kind of in the middle this is typically what more pen tests fall under you're taking a blackbox approach that you're trying to hack into it there's no credentials but the ray box you've got a full scope it's got all the IPS that way you're not missing anything out in the scope and so red teaming so this one uh before we mention what Sher red teaming is a pentest you're looking for all the
vulnerabilities that are exploitable and exploit them with a red team operation you're not doing that with a pentest you're let people know that the pentest is going on so that way they see malicious activity or anything it's broken it can be fixed it can be addressed but with a red team operation you have a control group and it's usually like the ciso maybe some management usually they don't let the blue team in because they really don't want them to realize what's going on because you're also testing the reaction of your Defenders seeing if they're able to detect the malicious activity are they able to contain it and uh so red team you're really trying to emulate a
AP group using a certain TTP to get into that environment and so this is a type of method that relies heavily on fishing and social engineering and like I said you're going in undetected one of the best outcomes I've seen from a red team operation is this company had an incident response company on retainer they were having this red team operation going on the Defenders detect something odd so they bring in the instant Response Team they're investigating they call the ciso to let him know what's going on and he let him know this is this is authorized activity but the fact is that they discovered it they reached out to their consulting company come in
and try to contain and remove the threat so this is kind of one of the things you do and you think a lot of times about you're doing Disaster Recovery exercises and business continuity to see if you're able to you know uh come back from a dis disaster or any kind of outage or something be a recover from that but when we do red teaming as kind of a way to test your instant response plan people actually detecting what's going on and that's really what you want to do you know maybe not all all the time the technology can catch it but if your your people can catch it that's a good thing and just kind of an example of a pentest
I did once was more of a adversary emulation but we got down to the last last eight hours of the pentest and we came on site to test physical security we were in a conference room and we were really down to the point where we really couldn't be quiet anymore we had run ness's vulnerability scanners responder and I was able to get a footo hole with the environment I was able to uh create a uh an account on the system we gained access to those systems and we're on site one of the things while I was there the guy was doing the pentest fors was kind of a side hustle that I was doing so he decides to call his cell phone
from one of the the telephones to see you know the outbound number so maybe he could do some uh you know social engineering do some fishing and so uh he did that so they actually later on had the record of this but the interesting thing was this was a very educated ciso that the guy could perform pin tests himself they regularly had uh ctfs to educate the team they were going through training they were you know highly skilled and they had all the the software and everything that you would need to secure environment but the problem was there's so much noise they didn't hear anything we were there and they didn't detect it until 12 hours
later we were gone 12 hours as it's been a threat actor we could have had whatever data took it and was gone and one of the main reasons they found us was because when they started looking in the suspicious activity they found his cell phone number and the funny thing was is that uh they kind of figured out because I created a user account under my name because with pentesting you want to make it easy to clean up if you've been a threat actor you're going to create an account that's not easy to figure out so I use Phil and so he knew that you know we're both part of the Dallas for security community so they
figured out was me but like I said 12 hours later so they didn't have those end points really tuned in to uh kind of sort through all the noise so also to Red teaming is referred to as adversary emulation so anytime you're trying to get one of these type of uh tests done make sure that you're on the same page because back to that director he was wanting to get a red team operation done against sap app really he wanted a pen test done so being on the same page some people use terminology different so just know to ask you know if you're if you're wanting a red team operation done make sure you're saying adversary emulation
most Consulting companies are going to know what that is but some vendors uh some other vendors with products really don't know the difference and so here's the example that slide that I created that showed the different types of Assessments and compared those so if you see one thing that's common across all those is your reconnaissance whereas in your vulnerability management this is your asset discovery and inventory so you have to collect information on the targets the next step is your vulnerability scanning which you do vulnerability scanning across uh vulnerability management uh vulnerability assessments and Pen tests pretty similarly running a vulnerability scanner but when you get into red team operations you have to do more manual
testing to try to go undetected I mean there are cases like the one I shared where I was running vulnerability scanner and they didn't know anything was going on but a lot of cases are going to detect that and so with the the next step is your manual testing and vulnerability assessments so you're looking using different manual testing tools to find vulnerabilities and a vulnerability scanner we have missed and then the vulnerability validation and then like I said you can take that a step further and see if there's any types of uh poc's for exploitable vulnerabilities and document that your report and then pentest you're taking a step further so you're doing pretty much everything you did in vulnerability
assessment but now you're trying to exploit those vulnerabilities and then do Post exploitation and with the red teaming you're just trying to find with red team you're trying to find one way in that would be you know equivalent to a breach you may find another alternate way to maintain persistance but with a pen test you're looking for all the vulnerabilities to be exploited and exploit those and with red teaming you're just looking for one way in and one of these things too is with the red team operations this is something you want to do when your your organization is more mature so after you've been through several cycles of pentest and Remediation that's when you add
something like rtin and this you're also U doing you know you're relying more on fishing and social engineering and do your physical assessments there as well so identifying the gaps so kind of to share a little history lesson of where we got to all these gaps uh so pentesting used to be less restrictive in scope more full scope pentest and really before uh any kind of compliance really companies that really knew security really well were the only ones that were having pentest done it wasn't a requirement so a lot of companies weren't spending money but then PCI DSS come along and then for compliance reasons people started having these pentests done people that were previously having these pen tests done
needed to focus that budget on PCI because they had to get through all this testing it was a requirement so other areas got neglected uh different types of testing got left out like social engineering efficient campaigns and so they left out a lot of areas so you know you can be PCI Compliant even your PCI environment secure but there's other critical uh systems and get sensitive data in your environments that have nothing to do with PCI intellectual property pii Phi so there's a lot of information that you want to protect and these were getting overlooked they the good thing about compliance pentesting it helped pentesting grow because a lot of people weren't doing pentests it was
interesting because when I kind of got started out in pentesting I would go to some of the different meetups and when I go to the different meetups and conferences local there might be only you know two or three other pentesters in the room now I go there's a lot of people see the need for it organizations are having their own pentest team so it's really grown but it's also addressed some gaps along the way so another one of the the gaps is the frequency so pen tests are are kind of a snapshot of your uh security posture also known as a time box test and so time between tests is kind of opportunities for threat actors and one
of the the cases for frequent pen testing was during one of my Consulting rols I was testing this company un fortunately they paid for a retest so 90 days later we were come back in and retest the environment so came back 90 days later they had when I did the pin test they had like a critical a high and some mediums when I came back did my vulnerability scanning during the initial phase of the pentest I noticed they remediated the criticals and the highs and the mediums so only thing left were the lows that were there from the previous pentest but one of the things that happened during that 90 days someone had figured out how to exploit
one of those low criticality vulnerabilities now if they hadn't had us come back in do the pentest that vulnerability would have been there for another year so this is one of the reasons you want to do frequent pen testing and this is one of the cases where you know at least having vulnerability management between pentests something to to do in between so if they would have just done been doing their vulnerability scanning if they would have did a vulnerability Scan they would see okay we got a critical vulnerability now this supposed to be exploitable and they would have known but a lot of cases companies would have waited until the next year to do another
pinest and so other limitations are Overlook methods like physical uh security controls testing your your controls your building uh see how people can tailgate to get in you know CU someone gets access to your data center gets access to a laptop that someone's logged into they've got whatever level access that person has so you can have the best inpoint protection you know say if you had a hack proof environment but I'm really not convinced that exists but if someone's able to get access to a system that's logged in they're already in the system they don't have to worry about getting the foothold so you need to test your physical security controls data centers are really critical and some of the things
look at too is said if you're were a utility company you have uh service vehicles trucks and vans you don't want anyone to get into those vehicles or or you know you could have expensive Broadband equipment in those you know people are stealing copper wire so you know maintaining those physical assets and even files because you know some companies have still have paper files and making sure that those are uh controlled securely and social engineering so social engineering is really important because you see a lot of the footholds uh from these breaches are through social engineering and then also red teaming this is not being utilized as much this is really kind of testing your ability
uh you know to detect things from you know like a nation state or so forth you're actually be able to to take your uh efforts a little further than assum breach assessments which I mentioned earlier where you're testing the systems with uh authenticated and then purple teaming also known as security controls validation this has been one of my favorite new uh assessment types that's been added so you're not familiar you're working taking the red team and a blue team and they're working together and see if they can execute different types of tools and they see if the employing detection systems are detecting blocking uh those type of activities and then you just kind of work through that to get to
those systems to be able to identify and block those controls and then also uh overlooked environments so Wireless Cloud your iot environments uh IC environments you know iot cameras sometimes these uh Wi-Fi cameras you don't think about but you can see sensitive data through there there could be sensitive data in room someone's able to access that see that through a a video camera so to overcome these gaps uh pen testing frequency so this is like probably one of the top recommendations so uh increase the frequency Implement Auto autom automation or autonomous pin testing and so uh there's some some products out there so the company I work for Horizon 3 we have an autonomous pin
testing product so you're able to run these pen tests uh continuously without interaction from a human and one of the things some of the organizations I work with and we always had some level automation so you need automation to be able to scale and interesting thing is uh things like autonomous pen testing is kind of like the next evolution of pen testing because you know at one time we have V ability scanners or we didn't have meta sploit and you wouldn't think about doing a pen test these days without those tools and environments are growing because it would you know when I kind of got into pesting uh you know the Scopes weren't as big but there's just
more and more stuff being added uh AI environments iot devices so it's really growing and there's such a a vast amount of systems that need to be test tested so you need to use some kind of automation to help uh continuously test and test more fre frequently and Implement bug bounties responsible disclosure programs for your mobile applications your external web applications and apis so this way you've got like a pinest or someone constantly testing your external environment and one of the Beauties about uh Buck bounties is there's people that specialize in certain types of vulnerabilities and they will set up their automation to continually scan don't add different bug Bounty uh domains and stuff in there and let that
run and they'll go back and see what they found and test deeper so this is a good way to do that and then responsible disclosure that way people find bugs in your web app they can report it directly to you and so this is a lot better than waiting for you know to get exploited waiting to the ne for the next pentest to tocover those vulnerabilities and one of the things is pretty nice about when you consider web app pentest and you look at bug bounties bug bounty hunters there's things that they'll find that a web app pentest may not fine because with bug bounties it's crowdsource pentesting so one the the descript I I
like to make or analogies is you can compare it to a fisherman someone that fishes for sport if they don't catch anything they're going to go home and have a steak dinner but the person has the hunt or or fish to feed themselves they're not going to eat so they're going to get they're going to be better at it so that's one of the advantages to like bu compies is these people don't get paid unless they buy something and then over Overlook methods social engineering include fishing campaigns and one of the things to include with the fishing campaigns is we have the different products like no before proof Point have these fishing campaigns built in and these are good
for uh building security awareness in education but one of the things where they miss out is what happens if that link you sent out actually had a payload did they have malware or ransomware what would happen there there if you're just using these other just know these other programs about a payload then you're just basically seeing you're just testing security awareness and with using a payload you're able to test ransomware Readiness what are they able to you pass that you you know this is one of these things that you actually want if some no one clicks on it you want to go through and have someone click on that payload to see what's possible what can they they get to
through that and so this is a good way do that test you can see what vulnerabilities because you can take that that fish further through that malware and perform further pet testing then you can kind of eliminate any of those uh threats by remediation and kind of help you rant aware awareness and Readiness and the physical security control controls make sure you're having physical pent test done and Red Team operations also known as a culation so if you uh you're organizations with tour start adding that and then purple teaming to do security control validation you know doing your security control validation and uh vulnerability management between pen tests is a good way to kind of help the optimal is
continuous pen testing but these are ways to to help out in between and also overlooked environments Wireless cloud iot IC environments make sure you're you're you're testing these environments and that concludes my presentation if we have time for questions I'll be happy to answer questions and uh please feel free to connect with me on social media uh this QR code has my link tree to all of my URLs so if you don't want to just take a picture of the screen with the the URLs and stuff and also uh check out my podcast also the Cyber service network which we'll be doing our live podcast episode later today [Applause]
good y thanks everyone and if you have any questions I'll be around today so up Bill