Reverse-Shell Fallacy: An introduction into defence evasion techniques
Show transcript [en]
[Music] so lunchtime is pretty soon and I don't want to keep you guys waiting and um my talk isn't very long uh so I thought I'd start off with a little joke um so the dog walks into the bar um sits down and asks the bartender for a drink the bartender pours him a drink and asks hey buddy how was your day the dog looks at the bartend and says
rough okay um yeah it's uh considering a comedian as a career path if this doesn't work out okay so uh starting off with the reverse shell fallacy introduction to uh defense evasion and why a reverse shell doesn't always mean success um so I had the idea of doing this talk after seeing on what is now the best source of information AKA LinkedIn um people posting reverse shells bypassing like certain uh vendors and so on and um them getting like millions of likes while other people post actual like useful information and they not even getting like a share um yeah those people know who they are so this is just a little bit about me um
I'm on Discord a lot sharing memes uh you can try and reach out to X I don't know if the messages will go through cuz I don't have premium um I like sharing memes I like making my way and tools and talking about [ __ ] like that and then I also just like General like Windows based stuff um today's on the agenda uh please forgive the basic slides um yeah I literally worked on this for like two nights and I was like okay well [ __ ] it it's good enough um so we'll be covering the past and the present uh what defenses were what they were uh what they were and what they are now uh some things that
Microsoft helps us out with MC AV Next Generation AV uh EDR and then we'll just cover some takeaways so past versus the present I'll start off with the past the past had the uh static detections it sucked at fatherless uh it was brittle it was easy by easily bypassable you could use like the Met spting coding change it up a little bit and Bobs your uncle um before MC came out I'm sure uh that was before my time I'm sure attackers ran rampid um yeah but even when with MC and organizations that only have MC and like a basic like antivirus well yeah it's pretty much it's really easy to get around and uh cobal trike metal met
sploit is everywhere I'm sure you guys have heard of those tools tools um today the cracked Cobalt strike is everywhere um MC a lot of like Security Solutions have their own I want to say like they hook into the uh MCD or they um basically like bring their own like sysmon so that they can actually just monitor the PO Show event so even if you bypass MC great you try and run a militia script you still get blocked uh virtual arloc um yeah I don't know who uses just plain virtual aloc anymore except for like just like demonstration purposes um today's Security Solutions focus on um visibility and hunting it focuses on the um actually like
collecting events so that it can integrate with other Solutions such as your seam such as your xdr such as your what other like thousand um uh terms there are uh Ai and machine learning machine learning is everywhere um um and for good reason not just as a marketing thing but uh well it works well if it's just not a b bunch of like FL statements um I'm not a AI machine learning expert obviously um you don't see me with like the ponytail and like the glasses I'm more of just a guy who shares memes and talks about how I byass it and then um yeah uh back then it was uh static detection so it would scan the
files and today it's more static and behavioral and correlation and all those other things um for DS wanting to get into defens EV asion um not just being like Oh I'm a pentester um cool let me see if I can get a show uh gets blocked you know people like you like you don't want to bother the client you don't want to tell the client Hey listen can you please just put my thing on detect only mode um you want to actually like let them do your their job and you do your job and you just try and like find as many um vulnerabilities and do your whatever you need to do the client will
get the alerts but you will still be able to just run past so this isn't a like a red team like oh I'm going to like sneak under your nose and steal over your [ __ ] this is just like a if you're a penti or somebody in the security industry and you're just looking for some tips to bypass your Security Solutions um many organizations have multiple Solutions in place so um you not only have the EDR these days but you have something that monitors the network you have a seam coming in you have a saw you have all these other things and if it was just the EDR or if it was just this one thing it's like easy to like
get around but like with all these other things um you can for example buy pass uh like an EDR but then perform password boot uh uh password spraying on the Network um you know xdr picks that up or something else picks that up because you're being a cowboy and you're just making a lot of noise on the network uh training and research for both attack and defense is becoming more available we can see it with everybody launching courses these days um everybody with more than 5 years experience sometimes um and yeah like that's becoming more available for the attack and defense um it's expensive as well but that's a story for another day um and then the
captain m game continues as always um so recently Cobalt strike um Cobalt strike 4.10 came out uh crediting um a lot of their like design and a lot of like what they are doing uh they crediting to elastics um like in memory detections and all that which is a game changer I mean if Cobalt strike and brood Rattle and some of the other like big names out there in the offensive to world created like a single company to say Hey listen we had to design our stuff this way because of what you're doing like there's that and I'm not just saying that because they're sponsor and they gave me like free [ __ ] at the booth but
um it is actually a good product and then today we also have a small team of what today's landscape looks like we have a small team of nerds versus these big multi-million dollar dollar uh Corporation so you have a bypass you blog about it you say how you did it um 10 10 days later an EDR comes and it's like oh we wrote detections for it like okay cool can we have access to your platform or access to some of your research and they just say no um this is the effort my little graph it's not as nice as the one in the previous in the previous talk but it's something um it's a little like effort
versus defense and as you can see the blue is the effort and yeah the more the more advanced the solution is the harder and the more effort it takes and this doesn't even take in all the other stuff plus having a like a full on like sock te monitoring supposedly um monitoring monitoring everything like it just gets like exponentially harder for you as an attacker um I thought I'd sh another form of spy way other than the Windows operating system um if yeah if you know you know um so Microsoft has all these other things on their operating system that helps Defenders take advantage or that helps defenders in like that helps Defenders out and you as an attacker it makes your
life harder individually they are pretty easy to circumvent but um if you you comb like if you as an attacker you drop onto a really well configured box you know like yeah that sis admin is eating your or drinking your tears all day um so yeah you have stuff like UAC to make sure that you don't run like that you can't just get access to like administrator and then to system because Microsoft doesn't consider administrator to system as security vulnerability um you have PPL which is process is protection light I think uh so that's just like that trusted processes can um open handles and open threads and inject into like certain processes like Elsa's you have smart
screen that thing that asks are you sure you want to run this um you have the browser soundbox if you download something if you download an exe or something like that or an unencrypted zip file um it would normally like scan it before it uh before it um puts it in your downloads folder Mark of the web I mean we've all heard that story with the office macros and ASR which is like your attack surface reduction that's just like a weird little thing but it just like if you set up the rules you can say like oh if a Word document is opening cmd.exe then it's you know it's kind of sus um and that forces us as attackers
to actually start thinking creatively we saw it recently with uh elastic making the blog post about the Grim resource the MSE files um the link files have been known and like blogged about for a long time being able to like get around like Mark of the web but you as an attacker you kind of like the whole thing of this is to make this possible um just having this like layer defenses and knowing you can't just like send somebody an Exe on email and say hey bro open it like that like that won't fly um additional Security checks again and it's all about limiting that attack surface it takes it makes us makes our job
harder um but it doesn't always mean that the user is safe at the end of the day um just like for example if you're doing like uh adversary simulation or something like that and you need to do something like that to get um execution on an endpoint one thing you might do is I don't know do something like this for an example but you also need to make sure that you don't have the user click on 10 things because users after like three clicks are like done they're just like no I don't trust this um so you kind of have to get creative with your thing have the user like click once or twice at most
and then being able while also evading all the other like Security Solutions on place that being said if you are a attacker you don't know what's on the endpoint it's like casting your little thing your little perfect package that you've worked on for a while and just like throwing it into like a black box and saying you know like call back to me um most of the time it doesn't work but if it does work it's very nice um so yeah till this part it's been pretty like pretty much boring and pretty much like text and that like the pictures are coming soon um yeah so with MC it was the stop designed to stop the scrip based attacks I think
it was Bor out in 2014 uh spes on your Powershell sessions so if you try and download and run something in memory then it will say like you know like we detected as malicious content um a lot of antiviruses do work closely with MC AKA just like integrating with it and they also rely too heavily on this so I won't get into the netty gritt of what MC is but most of the time it's the MC scan buffer and the MC scan string that monitors your stuff for malicious like content um so okay wa I think I forgot something to say yeah so a lot of the times here with vendors um depending too much on this uh
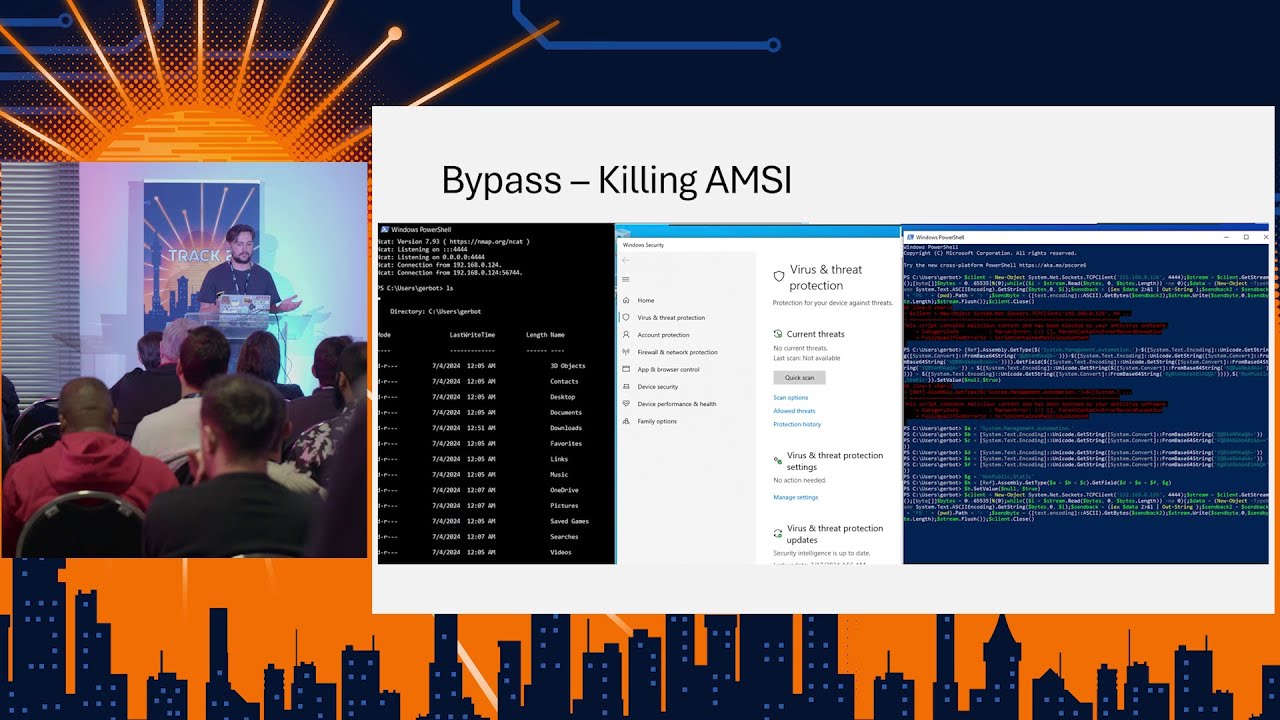
think of MC as like The Bodyguard for Fess attacks on um normal antivirus machines like you will go and download something run it in memory MC will scan it it will tell the it will tell the antivirus that's normally only for your like PE files it will say you know this guy is good to go or chase this guy out of the ball um so so that's basically what MC does on like a like a very high level um so there are many ways to bypass MC as you can see there I don't know how clear the text is but the uh very first on the top right there I just tried a normal reverse sh calling back
to my beacon there's my IP address on the right hand or on the left hand side if you guys want to hack me Good Luck um and obviously it didn't work because uh the script contained malicious content which is the reversal uh used a MC bypass that I've been using on many engagements over the years it got triggered and caught so it was kind of like a sadge moment for me um cuz it's like my little baby has now been like yeah has now been detected so I had to like work around I basically disabled MC and ran the same ran the same command as I did in the first block and yeah got the call back cuz you basically just
tell MC to like error out and then it's like okay cool like I don't know what to do now and then the antiviruses it's like okay I trust you even though you don't know what you're doing and that results in the reverse show um so without killing MC uh this is just an example I think I messed up the slide somewhere but I wanted to show you that you can you don't have to disable MC like a lot of the times if you are like a um on your newer machines whenever you bypass MC or you patch MC in some way um your newer like your newer edrs or your newer like next Generation AVS will actually detect that
you are trying to like um trying to patch it or trying to kill it and then it will uh set up an alert and kill your Powershell session so this was just me playing around um with some string obfuscation and on the right hand side you guys can see that this is the exact same one that was found here that got triggered first and and then on the left hand side is actually the one that's hiding and peeking around in that uh peeking at you from that Powershell session um so this is kind of like because it's still scans for malicious strings if you can hide or offis skate those strings in some way you can still
get around uh just normal like Amy without having to like without having to patch it or without having to do whatever but yeah these are normally like you shouldn't get attached to them because they will like MC will eventually like pick up that you are trying to do something and then you know like flag you and kill your session um and these are just some tips if you want to look at like some MC bypasses uh so string Kung Fu obviously like one thing you can do um and I've actually like done it here is you just take this normal string pop it into like Chad GPT and say like obis skate this I challenge
you to obis skate this as best as you can and you know well it obviously worked because I was able to get a call back to my sh so yeah very very minimal effort actually um yeah so if you want to like the first two there are many like bypasses there are many blogs there are many repos going around these type of like bypasses and that uh string kung fu is a a great one and then also just like you can mix those like two things like you could see in the like the first slide is the first one the first patching session got detected modified a little bit and uh you know you're good
to go um yeah to keep your alerts low um so these are environments that have power sh execution I've seen a lot of like people saying like oh yeah like move away from po shell Powers shell is dead well I don't know how many environments that you guys have been on that do have Powershell disabled um not many and even then like there's a way to like go around it but yeah um so learn how to use Powershell without the third party tools like if you need to do domain enumeration don't just like load in power viiew and say get net computer and get net user and get domain user and do all that like just learn how to do it
manually and normally like that's enough to like fly under the radar um you'll see later in the thing that or later in the slide why um Power store is pretty cool and um yeah it's uh enough to like bypass some EDR as well and I mean xdr as well and then um yeah like like Lin's living of the land is still a great thing uh been able to like identify like sey to or using like SE to to do a couple of things um using like Ms bold for instance if Powell is disabled and you have Ms bold on the system you can actually bring your own version of Powershell on there and that is pretty
awesome as well and you can use like you know like the like link files and do all like do all those type of things to like just get creative if uh if if the opportunity is there um so next one is antivirus and next gen antivirus uh antivirus scans for bad uh strings inside of a file and your next gen antivirus will monitor the PE and use Ai and machine learning and do all this like fancy marketing keywords to actually like watch for like bad things um this creates a lot of false positives as you can see on the thing there somebody called their Wi-Fi name invoke mimik cats and um yeah uh that happened um so with your more
traditional antivirus uh it's like the biggest the biggest challenge I had for making these slides of finding pictures that like like like that everybody can understand and that I don't don't have to spend hours making so I did link the credits but yeah that's not in here but yeah so um your more traditional antivirus comes free with some uh Windows installations we've all seen like Norton and maafe and like I think those are the two main um one semantic maybe um but yeah like they normally come free and you normally you normally uninstall them because they say Hey you have 90 days free and then you're just like ah just get off my system um also block malitia sites like
I know like maffy does that uh your up your signatures that scans for or that gets matched to like files that it that the antivirus scans get stored in like a signature database which then gets updated on a regular basis like you can go onto your windows and say like oh update update like signatures or whatever and it will like yeah it will just have the latest so it like scans for certain things or scans with certain files takes a hash of it uh looks in the signature uh in the database file and then it's just like okay cool then it determines if it's malicious or not um many organ organizations still have them because I think they like cheap
um and you know who doesn't love cheap up until they get hacked um but yeah like we've been on or I've been on engagements where we had this like had this like um more traditional AVS you run a PO shelf session you bypass MC and you basically do whatever you want as long as you don't do like certain well okay with your traditional it's like you do whatever you want uh Next Generation uh AV thanks to Microsoft for the picture um and yeah so BAS basically it does the checks but it what it will also do is it will take some data send it to the cloud analyze it using different models different like just think of it
basically as instead of the database sitting on your computer the database sits in the cloud and then it sends it through to the cloud analyzes it and then it's like okay cool you're good to go or no we think this is bad um and then yeah it also offers some sort of like centralized management for organization so you you as the sweaty it guide doesn't have to like run to 700 computers and update everything like you can just sit in your seat and do it and basically it's just like a traditional antivirus but just with add-ons if they're like oh you know marketing will say oh we detect fers attacks we do do we do this we do this we do this like
okay yeah like a lot of the times it's your traditional thing that has like a few things like stuck on and um it basically like if if there is a vulnerability in your or if there's like a weakness in your like normal antivirus and they make a new nextg antivirus um the vulnerability sometimes is still there uh with Windows Defender it is like that I can't like really speak about the RIS cuz I was too lazy to go and download um all the other like antiviruses and that to like to test it but I know with Windows it is um this was a just a simple reverse um if I put this on LinkedIn I would
have been famous um but yeah I decided to share it with you guys instead so basically what I did here was just like a simple like rust uh TCP shell that calls on Port 80 and that bypasses like um Windows Defender like nextg antivirus in Commerce and um basically how I did this was just uh using an exotic programming language so it bypass like the static detection and like because there's no like known malicious like shell like this and then for the behavioral all I did was like a simple like 2 minute sleep and um basically just like called out on on this I don't use any like fancy windows apis I actually just use like the um
like rust this like Tokyo framework just to like establish like a HTTP session your whole idea to bypass your next Generation a uh antivirus is basically just to like blend in like uh like a sheep and wolves clothing you want to make you want to make us think that oh yeah I'm just like a little like innocent little file sending on the system you know meanwhile you're getting you're getting a reverse shell and starting your uh malicious activities um here's your tips uh little sandbox evasion goes a whole way uh again just want reiterate what I said like your whole thing is just to like blend in a little bit uh if you can bypass static detection bypass the uh
your sandbox evasion attacks uh sandbox evasion checks like don't go and just like throw everything you know in there because it's going to look sus um don't use the Comm common one apis like a couple of years ago when I first started out on this I used virtual aloc and a colleague of mine laughed at me I ran it and Windows Defender laughed at me so yeah like don't use your common stuff with Windows Defender you can uh just go and use the um the N NT apis um because somehow it doesn't detect that so use your more exotic programming languages like I see there uh like you guys can see on the right C versus rust
um C being your the way it like decompiles like everything decompiles to C um so it's it's harder to hide stuff but it's also like yeah it's you really need to like if you want to just get like a fast and dirty like reverse shell just just use like a like just use rust um yeah sound like one of those Tech influences like just use rasb um but yeah one thing you can one thing you can also look at is C Shar uh that is a phenomenal language that doesn't get the attention that it deserves because you can a lot of tools are written in cop you can run cop in memory on a um in a Powershell session you can
I think you like B 64 it and then you like run the bytes in memory like stream it through which is pretty cool because of like the net run time um so yeah like if you want to like if you want to be if you want to like focus on like Windows stuff like UC shop uh if you want to focus on like like multiplatform use uh rust or use go or um I think even Nim but Nim has its like that has its quirks and then just hiding your ioc so one thing I did in my uh rust revers show was just like obious skate the IP address and the port number as well um
and yeah that was enough cuz like what the thing like what the antivirus does is like opens like like from like a basic point of view like it opens up your file it looks for like bad stuff and then if it's like to bypass static detection if the static detection doesn't like find anything then it's like okay cool like you can go on to the next stage so hiding like common ioc's is a great way of like bypassing like a both AV and like your next gen AV um so this picture is probably like the only picture I could find that really like indicates like how complex an EDR is and I had to go and buy the book to
get it um I did credit the author so please thenum me um but yeah just showing like I'm not going to go into detail of like what it is um or like I'm not going to go into detail of the design philosophy and like like the principles and all this like there's your picture read it if you want if you don't want like it's also fine doesn't hurt me um so they do differ a lot in operation like there are some antiviruses okay 16 minutes uh there are some antivir or edrs that have that are really strong in like um fers there are some edrs that are really strong in like binary there are some edrs that are
really even strong in network even though they sell themselves as an EDR um they have the cooler dashboards for the threat hunters and interent responders um there was another point in here but yeah um the cooler dashboards is one thing like anybody that has ever like try to like hunt something or respond to an incident know that like if you have to like do like 10 15 20 clicks just to like see where the like where the incident happened like it gets so frustrating um so a lot of them have these like cool dashboards that showed this like pretty pictures um of all the data they collected because an EDR collects a lot of data like you can see
they like collect stuff on the system it the static um the static it hooks into the do it collects the Network stuff like all that data needs to get sent to one place and then displayed for like for the Ed or for the incident response guys or the M the the threat Hunters to actually like correlate and understand what's going on like it won't be nice if you just see like 10,000 events happening every minute like yeah and then again like it monitors all this other stuff as well um some of them as have this like new feature where they do like threat intelligence as well where they uh scan for like militia sites um
you know like sites known or sites on IPS that are like known to host uh C2 servers and that and then um yeah but most of the time as well just like beaconing um like you as like an incident responder or like a threat Hunter like you can see if everything calls out 10 minutes every 10 minutes on the DOT like like like bro that that thing is beaconing um and then yeah also just checks for traffic uh clear Tex traffic if you're going to like go past like EDR in most more complex environments uh make sure that like stuff is encrypted because it will read the network traffic going to and well going to and from like
on the device and it becomes even more it becomes even more difficult once you start adding like an xdr on it and you want to start like doing lateral movement and all that like all that stuff like yeah it's yeah it's just too it it's too much to talk about in like with 14 minutes left um this is where we used mde because uh why not Microsoft um they have a fantastic product in terms of like detecting like um suspicious like Network traffic and that but they like actual like endpoint is really susceptible to like userland or like B like if you can bypass the userland hooks like you can pretty much like run around like Defender and uh
both MD it just goes on that previous thing where if there's like a weakness or like a design flaw in the antivirus then in the next gen antivirus and now in the um and now in the um EDR um that floor is still there doesn't matter how many like things they attach onto it um the was just yeah like a simple like little reverse shell um using like encoded Shell Code uh that's that's another thing if you want to like bypost your static detections is don't ever leave your shell code unencrypted like any any vendor will pick that up um and then just getting a call back to brute rattle uh we use brute rattle internally and
for like our clients only because it already comes with like a lot of evasion features outside of the box it's yeah it's a really it's a it's a really vicious piece of um of malw uh this was just like a little bit with like Sentinel one doing Sentinel one's weakness that we picked up uh was that it really sucks at um like monitoring your MC or monitoring your PO shell sessions and fower stuff um there are obviously like ways that you can like strengthen this uh adding like a sysmon or something like that something that actually like monitors your what you actually like throw into your um Powershell sessions but just for like your normal outof the-box installation
um and you have like a little bit of configuration it's not really hardened but it is somewhat hardened um yeah you can like you can run around and you can see the in the first blurry line there um that was my MC bypass that got detected uh this was I ran that one after this one so I think Sentinel one snitched on me if I'm honest with you um maybe it was mad I don't know so yeah basically bypassed that and used my encoded uh encoded shell and it was able to get a call back um but this is super important because well it's important to know that like just because you get a shell now like that's only getting your
foot in the door right like you still need to do domain enumeration you still need to look for users vulnerable to kerbo roasting and as roasting and like all those other things you still like need to do that and just doing it in a single like Powershell session is incredibly unreliable cuz you you trip one snare and it's basically game over it kills your thing unless you have like multiple shells open um but I mean that that is an indicator as as well if there's like multiple applications or Services calling to your same like C2 domain then that's another you can you can look at proxies as well but it just becomes like it just becomes really
difficult at this point cuz now you got it you're like oh you know I have this like shell I have this like I'm in you know hackers be like I'm in um but then you still have to do all your the rest of your operation like if there's something that like detects like CBO roasting or detects lateral movement um you're kind of like you're kind of done for you don't know what the client has in the environment not always like there are ways to like enumerate it and do your recon and that but like yeah it will say Sentinel one like if this was the xdr or if it had like Microsoft Defender for endpoint which then
monitors like like suspicious like traffic even though it doesn't stop it you have a you have a good like MDR or a good like sock they look at it and it's like why is they been like why is somebody like just requesting like like um TGT tickets you know like what is the point of this like as soon as you like do something suspicious it's basically game over um this was uh bypassing uh coward strike with Powershell um and basically what we did here is we took um uh basically what we do what we did here is I took uh Power view uh because it's a pshell script I opened it up I took the the functions that I wanted to
use and I just encoded them instead so instead of running the whole file you run individual single functions one at a time um it does take longer but I mean it doesn't it doesn't like yeah your l suspect you're you're less suspect on the network at the end of the day and yeah like and you can do this with like any application if you use like C um you can put that thing into your loader and then you can create like an object file and you can actually just run this as uh you know like everybody anybody that's used like a modern C2 know that it's like a like a cough loader or like a buff loader you
can create those object files and you can run it uh you can run these functions as well and if you use something like C shop well then you can just like if yeah you can just like encode your thing within Powershell and then just run it in memory and get like a and get your result um what this doesn't show you is the probably like 15 failed attempts uh at the kPa roasting um because it got detected a lot and then I don't know maybe maybe crowd I got tired of detecting the same thing and it just let me through but yeah no it's actually a lot of hard work um and then yeah so in the previous session we
saw a bow graph I didn't understand what was going on there so I thought I'd share one for all the other people that didn't understand what was going on there and they didn't want to say anything a better B graph about um the whole like perception of Defense evasion and I think just like offensive Security in general so you know you have your like commercial tools and your open source repos uh people use that you have the stage where I think every like PST that goes into where that everything needs to be custom it needs to be written from scratch and then you have your moment of Enlightenment knowing that you can use your uh commercial
tools use the open source repos and just customize them a little bit um other things are you know your low entrophy uh encrypted traffic clean domains and jit callbacks Jitter on callbacks just means that you add like a like a little like buffer to when it when it does normally callback so if it's like if you have like a Jetter of 40% on 10 minutes it will call between six six and uh 14 minutes so it's just like that Randomness between the callbacks just so it makes it diffic it makes it hard hard for your blue team guys to pick up uh your stage loaders you one thing if you encrypt your shell code in inside of a
file um a lot of like static detections will pick it up and it will say Hey listen we can see that this is a pack file like we can see there's another application within your application and we think that's uh suspect so have something that you drop onto the box and then afterwards you if you've done your like initial checks in that then you go and call your uh then you go and call the big guns and that also helps with your entropy entropy meaning like just like Randomness um randomness of characters within a file normally with shell code anybody who's seen Shell Code and pretended to uh know what's going on there would know that it's like it's
just just like random like digits and like [ __ ] like that so and if you encrypt it it becomes even more random so and if you have a High Randomness within your file uh that normally means that you are packing like you are having Shell Code or yeah it normally just means like encrypted Shell Code uh look for open source tooling manually modify it um and then having your um various techniques like there are many many many techniques out there that exist and that help you like circumvent edrs and bypass it like it's up to you to just like go and learn them and also just go and learn like the different like weaknesses
within an ed all um most of the time we have these like if we have an engagement we don't know what EDR they're running um or we find out what EDR they're running like a like a day or two before the time it's just this like rat race of just like researching vulnerabilities in it um I'm really lucky in the sense of like I work for a company that does MDR and we have a lot of like edrs available there that we can test in Labs um if you don't have that while any like need to do it on the flow you need to go and just go and like download like The the trial versions of stuff and just like
play around with it you can reverse it and that but I mean if you only have like um elastic that like only has like 14 days free trial like yeah it's it's it's not a lot of time um that you have to do a lot of research and then just like like legitimate third party administrative tools um I w't tell you which tools because yeah then my operation my next operation won't be a success but um yeah there are some there are a lot of like legitimate third party tools that can be converted into output formats of other tools um if you if you want to know um come and talk to me afterwards I'll tell you except if you
work for one of these two companies um so the takeaways is if your company has this capability for research use it um with the advancements in defense and that it's just going to be it's going to get a lot harder for just your standard pentest shop to be able to circumvent these things and with good reason it's like uh like companies spent millions of dollars of research some spend more in marketing and lawsuits but a lot of them spend a lot of um time and time and effort and um and and research so and you need to kind of like match that as well um so yeah if you guys have edrs and that in your company and you do have
like a private instance that you can use and you want to just like test around test what see sees what work like have the two screens the one where you like have the three screens the monitor your victim and then just your uh um you know like the console and then you can see like what picks up what doesn't um there are other techniques but that's that's basically like just seeing like what works what doesn't um good malware doesn't always um don't get attached to your work uh that's a really that's a super important one um because you can spend like a whole week maybe two weeks building this like perfect loader like that thing is like um you know fine fine
like Italian wine and yeah and then you use it on an engagement and next engagement you want to use it it it already got burned um gu I only have a minute left so good malware doesn't always mean a successful engagement again you can have the best malware the best loaders the best C2 whatever if you're going to be a cowboy on the network you're going to get caught if you're just going to like passw spray and do whatever and just like try and like Al has dump and just like go mad you are going to get get caught and then again I want to reiterate getting in is easy but staying in is super hard um especially if it's
like a longer term thing and the longer you are in the more stressful it becomes cuz you're like I did all this work please don't catch me um they often do catch me though and then yeah like this is just getting started uh learning a language I put python in here cuz they were um we were there at uh Zer I presented at Zer xcon and some of the guys came to me afterward and said like hey dude like you can do python as well so yeah you can just package it and it gets around mde and I tried it and sure [ __ ] it did so I threw python in here as well uh
learned the OS internals learn how to use a debugger because you'll be spending a lot of time in it I prefer uh x64 dbg um and then yeah just start learning the different techniques and start combining and experimenting with them and yeah thanks these are the links um I'll share the slides on uh on hack self so if anybody wants access to this you guys can just like check it on day okay thank you