BlindSQLi Falls on Deaf Ears
Show original YouTube description
Show transcript [en]
[Music]
okay thank you everyone for coming to my talk uh I'm talking as you might have seen about blind sqli so I discovered uh sqli injection in a website yeah it exists in 2023 surpris uh so um a bit about me uh who am I started programming when I was 12 if you can't copying other people's code off the internet and uploading it to microcontroller as programming uh not an expert I'm just curious and I'm unemployed so I have a lot of time on my hands um uh during my first and only year at fits uh I learned about the sand and CSC as you might have heard hello talking about in the other conference room and uh that started my
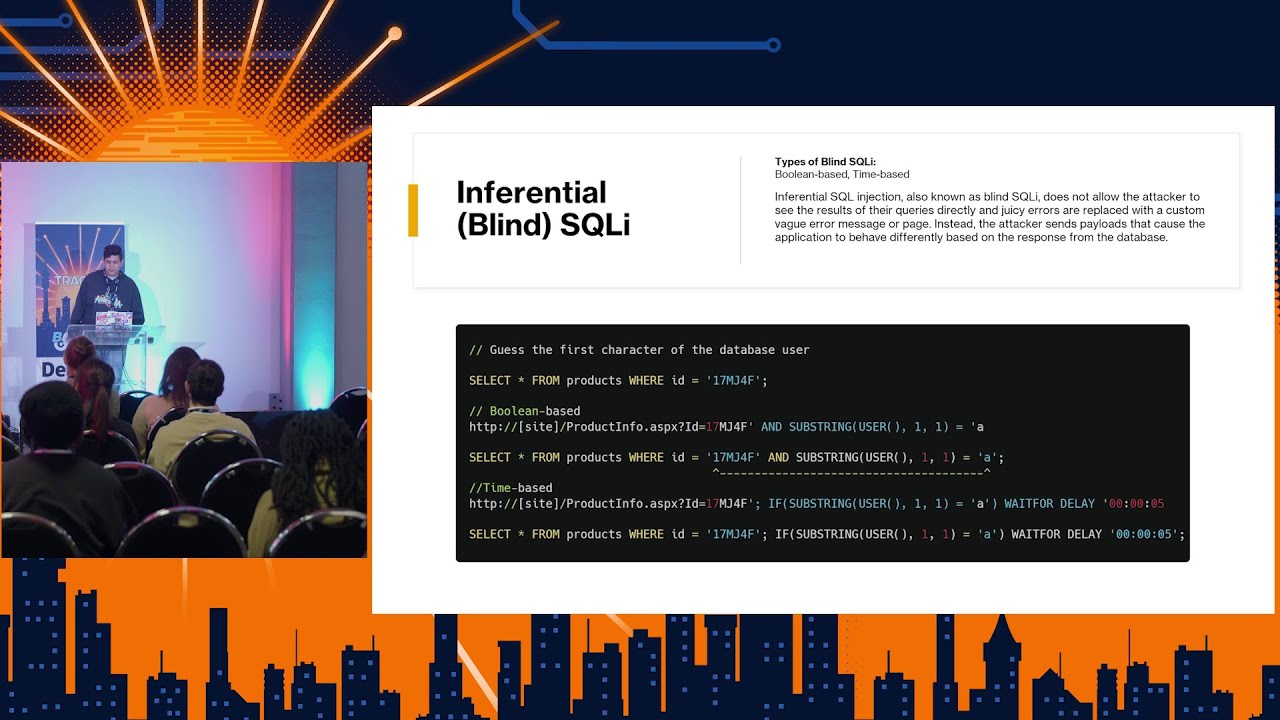
cyber security journey I came second with my with my team retired for first place in the Jeopardy challenge but somehow we came second I don't know uh tried for first place but um so anyone who doesn't know already there's three main classes of sqli there's inband that's where you send the request on the web page your data comes back right on the same web page so in the same channel you send your your query the data comes right back easiest type to identify an exploit uh inferential that's where you send a query but you can't see the exact output you can't see error messages uh all you can see is um some kind of vague error
message at least uh you can infer what that means yourself and you have outof band that's where you uh get the data back through a different Channel like for example HTTP or DNS requests you get the database to actually make htttp or DNS requests maybe even over email back to you so that's a different Channel that's how you maybe would export trate data if you have a blind sqli so inband um we have different types of inband sqli we have stacked we have add-on erab based uh you might have seen this the most common way to test is with a little quotes and you can also try a quotes or 1 equals 1 that will
tell the database uh if it's checking um any products with the name Hammer it'll say is there any product with the name hammer or is one equal one so the statement will always be true and you'll get every single product and um with inband of course you'll get all the data out right back in that same web page so you can say hey uh can you select all the products where the name is Alice and also give me the username and passwords from the user table thank you completely unrelated like random yeah so it'll just added Union joins two dat data sets together you have your products uh table and then right underneath it as if it
was part of the products you'll have your username and passwords just nicely there for you to to see and use non- maliciously um out of band you as I said before you can get your data back in DNS requests so uh this is a screenshot from a medium article I was too lazy to fire up Bub suet everyone knows it takes like three years to open um so uh this is a SQL um statement that has been injected into a query on a website that sends a DNS request with the version of um uh of the database which you can see at the bottom show up yeah so uh you can see it's 10.3 16 Maria DB and that is a DNS
request but that domain obviously does not exist it's just for exfiltration purposes uh inferential sqli so if you see this kind of error message on any website that you use you should probably stop using that that website it's uh not going to be very secure for long unexpected error hasn't occurred if the problem persists please contact Web Master um so uh this is not necessarily a website that I got into this is just the error message that I that I found is uh generally a blanket statement so you might have your try and accept and your website your whole entire website will be in that try and you'll have an accept just in case some someone does something
you didn't think about and it'll give you that 404 error page just the devs uh don't have to do much work um so if the database returns a nice error message for you and says hey uh you're missing a parentheses in your statement or something it's quite easy for you to figure out how to fix your uh sqli statement to inject properly you can figure out what the statement looks in the back end of the website but if there's no error messages directly from the database like like in this case you can't actually see what is wrong on the backend side it's a little bit more difficult to figure out what the query looks like but it's still possible to
inject statements so this is an example of what a blind sqli would look like uh you have your select all from products where ID equals 17 m j4f and a Boolean based blind sqli would look like uh that's this right here so in this case this website is accepting user input and is passing it through to the the website's back end through a get request so you can see this is what it should normally look like and it should end over here but if I add a little quotes and I add my own little command um and you see there's no quotes on this side because the website Auto completes that for me uh it ends up being select all
from products where ID equals this product and substring user 1 one equals a so what is that mean that's asking the database uh does the first letter of well is the first letter of the database user the letter a is a small character a and also tell me the product page so if it is uh a letter A for the first letter of the database user it'll give me that product page back because if it wasn't then there would exist no item in the database where that query is true so what you can do with this is you can see okay when my statement is true for the database or when I get an item back um
it gives me uh sorry when when my extra little statement at the end there is true and I have a valid item in that ID column it gives me the product back but if there is no uh product it won't give me any product and if this little query at the end here is incorrect then I won't get anything back I'll most likely get a 4 or4 error message because the website is expecting some kind of product back from the database um and with this you can get yes and no questions onet from the database you can say hey is the first letter of the database user an a yes it is oh cool I got a product if it's not
you'll get an eror page so this way you can get every single letter of the of the database user one at a time painfully or you can script it and there's other ways to do this you don't have to just rely on true or false if your website is fast enough if it's efficient and it's not really bad you can use a wait for so if your statement is true the website will well the database will get your information it'll wait 5 seconds and it return back to you so if your website returns really quickly like you ask it for something instantly get the response um and you and you pait this and then suddenly you
have to wait and you see that little circle loading for 5 seconds then it paes it back to you you know it's actually executing that command so something over there is is working um okay okay bypassing filters so as you've probably seen in all of these slides I've used a single quote to exit out from that little uh inputs that string input so why don't we just why don't we just filter out all quotes we just say Okay use a positive code remove it from the input we sort it no more SQL injection right no so if we use a numerical field uh if we're using a numerical field for our uh SQL query we don't need
a quote because you don't need to have quoted strings for numbers everybody knows that and we can use a union statement in this case with no quotes to dump all of the users if it's um in band so this is where my Journey Begins I was learning about SQL injection and some Advanced Techniques because nobody sees inband injections anymore that's really 2000s if you have an inband uh vulnerability on your side you probably fix your [ __ ] right now so um I was learning about blind SQL injection and I found this website that I used to use a lot it's was a aspx.cs everything looked really really uh not well put together so I noticed some
weird Behavior about the website when I would put a quotes in some areas or if if I just did something that um would give me an error page and in a regular like modern website should not give me an ER like a blanket error page it should just not you know behave badly it'll just if you search for products and you put a quote it'll just return either no products or do something normal um but I didn't know and looking at the SES for the first time um with this knowledge that I would go on a journey that would take me through ense um trying to find it which sounds e than it actually is uh a a company that is
quite quite large um and I tried to disclose this vulnerability multiple times with no success so let's start this um firstly there were a couple pages on this website there was a login. aspx as the name suggests it's a login page and uh it posts the credentials that you enter into these text boxes to the to the back end so you'll say Okay um username password you'll say maybe admin sends a post request with that and a bunch of other stuff like session ID whatnot uh and that didn't seem very vulnerable I tried injecting quotes I tried a bunch of things and either it's extremely secure and um uh that that's just like one section of the site that
people really focused on security or maybe I'm just not skilled enough yet to get through that that part of the website so I focused on other things I looked at the stock site and I sent some um some queries through it's used a get request so I could literally just change the url at the top sorry I don't have a lot of pictures I had to finish this up yesterday uh so I tried an all1 equals one semicolon Das Dash that comments out the rest of the the query because otherwise it'll just break so the website actually did break and it didn't give me everything I couldn't see what it was what it was doing because it just
giv me that blanket statement I couldn't use a um uh inband SQL injection if I could that would be a lot easier to export trate data so you'll see later so uh I'm just going to ignore that cuz I'm running a little on time so product info that's where it really got very interesting there were it sent a get request with apparently no sanitization single quote breaks the query and gives me that custom error page from before looked delicious because it was just a single quote this time unlike the last page uh and when I tried single quote or one equals 1 semicolon dash dash I got every single product all the images like it actually had I don't understand how
it worked but it had like a Next almost like it was designed to allow you to do this like maybe they used like a framework or some kind of like template but yeah that was very funny I thought um so it seemed like we had inband SQL injection unfortunately not of my union statement Works uh statements work and I got really bored and I almost gave up so uh yeah it's I I later concluded that they must have been using some kind of templating so when you send your query goes to the database the data database returns it to the front end um framework so something like flask obviously not this it's using asp.net and what it does
is what I'm guessing it does is it has an HTML template and it it expects a certain values a certain Fields so it maybe it expects uh price um item name minimum quantities Etc and uh it expects those values and if it gets any other values it just breaks so when I asked it for username and password when I asked it for other values it couldn't give me anything even though it was actually processing my statements um how did I know that it was processing my statement from before I could use uh weights for the delay sleep whatever you want to call it I could use that and see if it actually waited but unfortunately this slide was very
[ __ ] slow it was like extremely bad it was I don't know who wrote this but it seemed to get every single product no matter what query you used and then filtering afterwards something like that so I could not use this luckily for them this badly designed website actually prevented people from using this method of um figuring out if there was blind SQL injections so they got lucky um and another way is asking true or false statements that you know the answer to so you can ask a true statement you can say hey um give me this product information and also is one equal one one is always equal to one and it will
give me the product page but if I ask it hey give me this product uh product page product information n one is equal to two it is going to break no matter what because even if that product exists one is never equal to two so I knew that it was actually uh processing my query as commands and not just um a value for like a search so using blind SQL injection uh what can you do I can only ask yes or no questions like is the length of the database user string more than five characters uh is the data is the first letter of the database user an a is it a b uh and how is this useful to
me okay maybe I can get the name of the database user but what does that do right uh well we can script some things find out what databases exist what tables exist in those databases I found 25 databases I don't know why they had 25 that was super unnecessary uh and the tables things like um custom customer information um I didn't put this in the slides because they're going to be put online and a little bit of this is kind of illegal but it is being recorded so that's probably not very smart so anyway uh so um I'm just realizing that now uh okay so they did have 25 databases and they had a lot of tables like um
customer address customer names employee emails and that was very useful because I tried to contact the employees later and it was very difficult uh dumping the whole database yes I could do that through blind SQL injection but that would take years um and another very interesting thing that I found was what uh xcm CMD shell was enabled and in Ms mssql 2016 that was very useful especially on a 2022 Microsoft server um and the database user was privileged so uh that was very fun um so I could get interactive command shell and from there after a little bit of fiddling I could get uh reverse shell I mean I could didn't necessarily do that because that
would be illegal um responsible disclosure uh so on the website they had I'm running a little bit over time but hopefully the person that's supposed to speak next is late yeah oh thank you so um Web Master mentioned on the website surprised nobody answers that email uh contact contact us page had sales accounts web orders emails nothing um OS to harvest more emails I tried a bunch of different methods I learned some methods from uh what's his name Heath yeah from uh the PNP certification from uh TCM security he Heath Adams yeah so I learned a little bit of how to find emails for a certain domain um and I used that knowledge to find the CEO's
email to find a bunch of other people's emails nobody responded um LinkedIn found the CEO found the IT department found a bunch of people in the IT department um nobody answered the LinkedIn messages dumped the employee emails from the database and messaged everybody and said hey guys I have rce on your on your windows 22 server anybody care nope nobody cares uh so phon the head office three times first time nobody picked up uh second time receptionist picked up sent me to the ID department and the IT department didn't pick up third time I got through to the IT department and I went through a couple of levels of people uh finally got through to
somebody that said their supervisor is busy at the moment but they can take a message and I told him about what was wrong and he said hey we're actually looking for somebody to remake our asp.net website from scratch because it's we know it's pretty bad and I said okay cool asked me if I can help I said yeah uh I told him to send me an email and we can have a meeting um figure out what you needs requirements Etc never got back uh never got back from you um so unexpected outcomes lack of company response to every Communication channel it was quite surprising especially since when I got really tired after like a couple of months I started sending them
like uh stuff that you know would probably shock some people but from like emails that wouldn't dox me um different levels of security sanitization across the website login page seem to be a lot more secure than other Pages which means that whoever set up the database didn't realize that there's something called a union statement or like anything else where you can actually get uh like stacked um queries which is another thing that I used and I'm surprised they actually did encrypt the passwords in the database uh well hashed them and um they were md5 but still they were hashed so um and in conclusion uh I found out that you should probably not go directly
to the company and send them an email with your personal email um telling them about the vulnerabilities you found completely legally um yeah so you should probably go through a third party so if anybody here finds stuff on websites uh what I what I've been suggesting suggested is that you go to someone like my Broadband or go through a third party that can actually communicate on your behalf so you don't get yourself in jail um and all companies can have vulnerabilities regardless of the size or income of the company doesn't matter how big the company is bigger the company is the larger the attack office and you'd assume that they'd have better security but that's not always the case
um Q&A anybody have any questions no um thanks for that in terms of your SQL injection did you ever some stage try to utilize SQL map against it was an effective I did uh try and utilize SQL map but um because SQL map is such a general tool they uh they would get all the information so for example it would send a query like it would well it would have a lot of overhead firstly so it would send a lot of queries that it wanted for itself for its own purposes for making itself faster the F for the future but with my purposes a lot of that was really unnecessary and it made it take way longer than it needed to so
I did make like write some scripts but the way that I exfiltrated data um SQL map wasn't capable of that I had to Expo trade data by um well if I was going to Expo trate data from that website my bad uh I would have used uh a web hook and asked the database to send a Json packet to my web hook like with the HTTP request with all of the data so would say hey please dump this table send it an adjacent packet to my web hook because otherwise using SQL map would take like days you there's like hundreds of thousands of products in that website um yeah any yeah so my question was is
this hello can you hear me okay cool um my question was uh firstly the whole all of the es injection was blind es injection right there was no straight inband yeah I couldn't uh I couldn't find that they had that that blanket error page which really stop you sure for sure and my other question is did you use straight up character compa comparon in your blind disc injection well um I did when I was uh starting out like when I when I was just testing to see if it existed but when I wanted to find out a little bit more before I went to out of band I used kind of like a binary search where I used like more
than less than so instead of saying a b c d I'd say is the charact is the asky value of this character more than 100 is it uh more than 50 and I can get kind of like a general area and you know have you tried um so was this myql the database yeah MySQL 2016 so with my sorry mssql okay I suppose you can do this mssql but if you ever hit a mySQL database you can do what's called bitwise extraction you substring a character you get the bit value and you extract the bit string instead of the action instead of guessing the actual character okay I'll look into that thank you and then from there you can you can
create a lookup table so if you have multiple behaviors in the website you can have you can extract two bits at a time by saying look if it's uh a two then delay if it's uh one then produ or false if it's you know mean you can map it onto a behavioral table and extract two bits at I definitely talk to you afterwards about that for sure anyway anyone else great talk hello um I was just wondering if you have tried bug b hting um yeah sorry did I interrupt you that okay cool so um yeah I I mean I I should probably do that somehow all the all the vulnerabilities I found so far
those companies don't have BG bansy programs I just stumble across something that I find interesting and I go on to that B bonsy I feel like it's it's a bit specific so I'll have to like focus on a certain area and then you don't know if there's going to be anything there with with what I've been doing I've just like stumbled onto most of the things that I've like used curiosity to to drive me through um but I I definitely want to to start that because at least with bug Bounty programs I have the uh guarantee that I'm going to get P paid and uh just one more thing uh I would really recommend some sites
such as pser and bugy hunter.com just for reference thank you I look into that anybody else no okay thank you everybody sorry for taking up so much of your time uh





