Hacking The Airwaves
Show transcript [en]
[Music]
Okay. Hello everyone. My name is Robin and welcome to my talk hacking the airwaves. So today I want to sort of take all of you through my journey as to how I started looking at radio frequency hacking and sort of giving you some insight as to what it means to look at radio signals from a security perspective. This talk is then also hopefully going to raise some security awareness around the topic. So who am I? As I mentioned, my name is Robin. I'm a cyber security consultant at MWR Cyers and my main focus is actually application security where I started looking at radio frequency hacking as a hobby in my very first year. But then where did this actually all
start? Because signals is kind of a esoteric type of uh concept. And I do think that it sort of started when um in my university years where we had a lot of exposure to signals and signal processing things like that. And in my final year project I have I was tasked to build a synthetic aperture radar. This allowed me to really dive into the fundamentals of signal processing. Now, taking that information to a cyber security consultancy, I thought to myself, well, they taught me how to think like an attacker. So, what if I look at radio frequencies as an attacker? With that said, I immediately went to my mom's Mazda and started hacking straight away.
So, for this talk, we're going to look at the following agenda. Starting with tooling, some automotive cyber attacks, more RF attacks, and then closing remarks. Tooling. So, when you're looking at radio frequency hacking, these are some of the tools you might come across. We've got the Hacker Hacker F1, Flipper Zero, Proxmark RD4, um, RTL SDL, and there's much more. But at the end of the day, all of these tools are essentially just radio receivers and radio transmitters. nothing real special about them. And all of these are tuned in into a specific radio frequency that you can operate on. And when we're talking about radio frequency hacking, it's essentially anything between 20 kHz and 300 GHz. And
in that range, there's a wider range of applications. For example, we've got RFID, NFC, key fobs and remotes, um, Wi-Fi, GSM, and GPS. For my research specifically, I looked at um the communication between the key fob and then the actual car. The problem I ran into is I had no idea how any of this works and I had no idea how the key actually does its thing. So then I took the key fob to a spectrum analyzer where I literally just used the hacker F1 and pressed the button a few times of which I saw signals that looks like that. And at this stage well I also didn't really know what this meant. So I
saw two distinct peaks in the actual signal that I was capturing. And just to note this is sort of literally the raw signal displayed in the frequency domain. So the bar, the horizontal graph bar here would be the frequencies. And we can see we've captured this key fob at 433 MGHertz. But now, of course, I needed to dive a little bit deeper in terms of what does the signal actually mean. Well, turns out that signals makes use of digital modulation. And digital modulation is essentially a technique that allows you to represent binary data in the actual structure of a signal. For example, we've got there the top part being the digital data being sent through. And then let's say we're
talking about amplitude shift keying. If the amplitude of the signal is higher or larger, that's going to represent all of the ones in the signal. And when it's lower, it's going to represent all of the zeros. However, if we look at frequency shift keying where it's FSK here, the higher frequency part of the signal is going to represent the ones and then the lower frequency parts of the signal is going to represent the zeros. Taking this information back to the actual signal, we can see here that looking at the two peaks, this signal might have been using FSK because if we can look at the sort of right hand side of the signal, we can see the higher
frequency portion of the signal and then the left peak would have been the lower frequency portion of the signal. At this point, I was feeling extremely confident because I now know everything about key fob communication because I was able to understand this is a one and this is a zero. So I thought to myself, okay, I want to attack my mom's Mazda. How can I do that? I thought about, okay, if I were to capture a key fob signal, what happens if I replay that signal? Will I now be able to unlock the car? Maybe have a permanent key to it. This didn't work. And I was sort of back at step one. Okay, I don't know what I'm
doing. How does this work? And it turns out there's something called rolling codes. I'm sure all of you have heard that with um your like garage remotes these days and your key fobs, there are rolling codes being sent along with it. And these rolling codes are meant to prevent replay attacks. So how do rolling codes prevent replay attacks? Rolling codes are essentially randomly generated values that's sent along with each signal to ensure that the signal being sent is unique. Because each signal is unique, it allows the car to actually determine which rolling codes it has already seen and which it hasn't with that is allow is what allows it to actually prevent replay attacks. But the rolling codes
itself, how does that communication between the key fob and the car now work? So if we take the car and the key fob, the car is going to have a pseudo random number generator and the key as well where both of them is going to have the same seed. This is what we mean by the car and the key fob is in sync. So the car is going to have a list of valid rolling codes. That's what we can see over there in the right hand side. That's going to be your list of valid rolling codes. And that's stored inside of the cars. It's called a rolling window. And whenever the key fob generates a random number, it's going to
send it to the car. And because they have the same seat value, the car can actually expect that the correct value is going to be sent through and the car will unlock. But why is there a rolling window? So, when you're out of range and you press the button a few times, the car isn't going to hear the signal or receive it. And if you didn't have a rolling window or a list of valid answers, you're going to doss your car. An example of this is um I'm sure it happened to me at least when uh your parents would give you some of the car keys to play with. You maybe press the button a few times and that's actually
the biggest concern as to why you might do your car. And if you come back into range, you can see there that the key has generated the value or the rolling code value 8. And the car is going to see, do I have eight in my rolling window? Yes, I do. So, it's going to unlock the car. Now, of course, it's in real life, it's not going to be these integers. It's going to be randomly random uhly generated numbers. Um, now the big note here, because we have a rolling window of valid answers, this is basically having a list of valid passwords for your car. You can't make that list too large. Otherwise, the attacker would have a higher likelihood
of actually guessing the correct answer to your car. So, that's why the rolling window can't actually be too big. But now, what happens when we go beyond the actual rolling window? Well, if you do that, that's going to desync the key in the car and then you're going to cause a denial of service. So we can see here for the key fobs generating the rolling code 15 and that 15 value is not inside of the rolling window. Therefore the car didn't unlock. This unfortunately happened to me. Um I doSed a principal consultant's car in my very first year at the company which made me extremely scared. I think this was literally just after I passed
probation. So it was a very stressful time for me. Uh basically what happened was I was really getting into this um radio frequency hacking and I asked everyone hey can I hack your car and they basically said no apart from this one principal consultant um he said yes of course and sort of just a little bit of context he would park in the basement so the basement cars are obviously out of range of the actual key fobs. So I was sitting there in the office playing around with the key, pressing the button, trying to sort of analyze the signal structure and afterwards I asked them, "Hey, can we maybe go down? Just want to test one of the attacks." We
went down and a lot of people were interested. So we actually brought a group down to the basement and uh we attempted the attack and it didn't work and we were like, "Oh, okay. Nothing happened. Cool." Um and then Christo just wanted to make sure that the car is actually still locked. pressed the button, nothing happened. So, at that stage, my heart sank because I broke a PC's car and I'm just barely out of probation. Um, uh, luckily there is something we can do to actually reync the key fob and the car. So, here's some of the things that we looked into. And the first one was essentially performing something akin to a mechanical ritual.
We looked at the car's manual and it gave us like a 20step list of how to put your car in debug mode and then you put the key near the ignition and that's going to resync the car somehow. We tried that. Lights started flickering in the car and it didn't work unfortunately. Luckily, the um PC still had a manual key so he could open up the car, start the car, and drive home. Of course, he was a little bit frustrated, but he's one of the kindest people, so he didn't show it. um because that would have meant that he might have had to go to the dealership where they do the ritual for you for a fee. And that's the
problem that sort of stressed me out. Um so luckily when he went home he started playing around with the car itself to try and you know get it back in working condition. He used the spare key and then that unlocked the car. So that worked. Okay. And then he used the original key again and now the original key started working again. That meant that there's some type of built-in feature that allows you to reync the key fob and the actual car. That sounds awesome right? But wait, rolling codes were designed to prevent an attacker from replaying older rolling codes. And rolling codes were also built so that attacker can't guess future rolling codes. That's a rolling
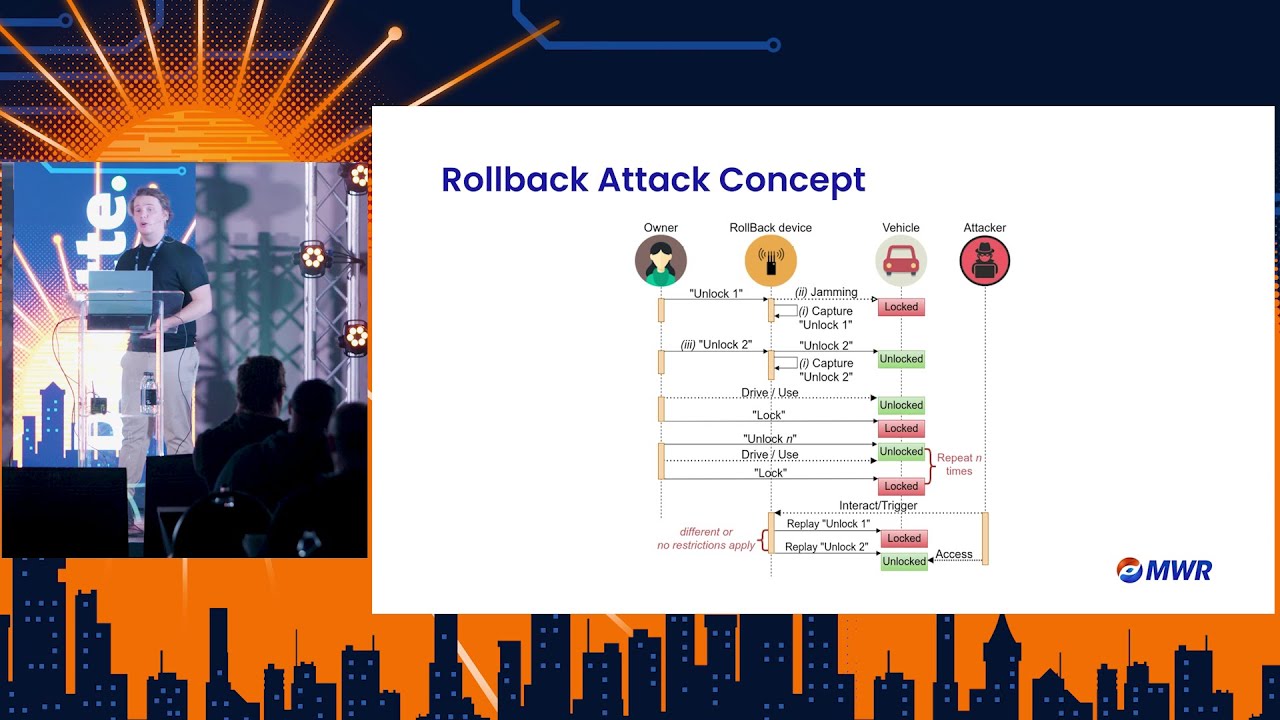
window. But now we have a built-in feature that allows us to reync the car to a specific rolling code. Can't we use this built-in features to reync to an older rolling code? In comes the roll back. So the rollback attack concept is essentially you would intercept or capture consecutive rolling code signals and then replay that to the car. Once the car recognizes the consecutive signals, the car is going to see, ah, okay, you gave me two consecutive signals, for example, and I'm going to unlock them. So, if you can look at how that might look from an attacker perspective, let's say we have um the attacker waiting in a parking lot in a bush or, you know, something like that
and the owner is coming back to their car um wanting to unlock and drive away. The owner is going to unlock their car, but then the attacker is going to jam the vehicle from hearing the signal, but then also capturing the owner's um key fob signal. Then the owner is of course just going to press the button again thinking maybe the battery is a little bit flat. And then after that, the attacker captures another signal. So this is their second consecutive signal. And this time they don't jam the car and let the user um unlock the car and drive away. At this stage, the attacker would have two consecutive rolling codes with them and whenever they replay it, it's actually
going to unlock the car. So for my PC, I'm going to show you here is um the same vulnerability isn't associated with all cars um but unfortunately my mom's Mazda is. So, although was I guess lucky for my perspective because it allowed me to do a little bit more research and essentially with the Mazda CX-5, you have to capture three consecutive signals. So, in this case, we have three rolling codes consecutively. And when I replay that signal to the car, the car is going to see, okay, you gave me three consecutive rolling codes. I'm going to perform the very last action you gave me, which is an unlock action. Just note that these signals were
actually captured in 2022 and the demo I'm showing you was I think um videoed last weekend. So here you can see laptop on the car. One 2 3 and the car unlocks. Just another one. One 2 3 car unlocks. So that's sort of the idea of a roll back attack. Now, of course, you need to trick the victim into actually capturing those three signals, but as I mentioned earlier, some of the cars actually only make use of two consecutive signals for this um roll back attack to work. Looking at some of the mysteries of the roll back itself is do does the signals um have to be consecutive the consecutive signals? Um not always. No.
So for most cars, yes, they do actually have to be consecutive, but some of the car models allow you to just have two rolling codes. Doesn't even matter when you've actually captured them. Then you can unlock them. That's relating to the first column or first row, sorry, of that table where the rollback attack is called loose and you only need two signals to actually do it. This is terrifying because now the attacker just have to capture um two signals. Doesn't even have to be consecutive. Whereas the more common one is going to be the third row where the rollback attack requires you to capture three consecutive signals like the Mazda CX5. Um, another one that's quite common for
um, or I guess a car that's vulnerable to the second column one is the uh, Hyundai i20. And this is kind of horrific because this is a common car for a lot of people to have. And another thing to emphasize with these type of vulnerabilities, you can't do a patch. You can't just send an update to the car and it's not going to happen anymore. So that's one thing that I'd want to highlight with sort of all the auto security automotive security um concerns that I'm um highlighting here. Then um how many consecutive signals do I need? I did mention sometimes it's two to five. And then is this just for unlock and lock? No, it's not. So, if your car
has the feature to actually start the engine through the remote, as long as you captured or as long as the last signal you've captured has the start engine um action inside of it, it's going to start the actual car. Uh something that I've seen before is attackers basically showing a PC where they would um roll down the windows, open the door, start the car, and we'll of course drive away. So the rollback attack is quite an awesome attack for attacking the car's actual rolling codes. And this made me a little bit more interested because what other type of attack vectors are there? And then I noticed that wait, the signals aren't actually encrypted. I had an initial
assumption that all these signals that I'm viewing is encrypted and there's not even a need for me to look at at this stage because I'm still starting. Turns out no, definitely not. Most of the signals aren't encrypted. So far, ironically, the Mazda key fob that I've tested, that's the only key fob that I've seen so far that is encrypted. Not saying, of course, there's a lot of key fobs that aren't, but everything that I've tested so far hasn't been encrypted. Now, because it's not encrypted, it of course allowed me to look into the actual signal struct the actual signal structure a lot more in depth. Here we can see an act an extract of an
actual key fob's um signal and we can see its data structure sort of just giving us all the information there. It's built out of the um header one frame off time subheader and two frame and I can see it's 380 milliseconds. That's how long the signal is and how long it takes to actually transmit. But after looking a little bit more into the actual structure of the signal, I noticed that we only need half of the signal to perform the action. This is because the key fob actually sends the signal twice. And I've seen this with um quite a lot of key fobs where instead of sending it um once being a long signal, it basic basically sends it twice. And
this allows us to reduce the transmitting time to half of the original value. So this is going to be in this case 190 milliseconds. This is going to become more evident a little bit later. Now since I only need half of the signal, I'm going to look at the data structure being sent from header and then the one frame. So the header is basically a constant value that's sort of just telling the car, hey, wake up. Um, I'm sending you a signal. The user code is the actual key fob ID. So with each key fob, you're going to have a specific ID. And this might be related to your spare key and your main key.
Then the ID code, that's your car ID. So each car is going to have its own ID. Because for example, let's say um you're a manufacturer and you have um 10 cars there. How does the car know which key belongs to him? And that's through this type of method where each car is going to have its own car ID. Then we have the function code. And this is the code that tells the car what type of action to perform. Usually, of course, you have your unlock and lock, but if you have a little bit more fancy car, you can do the boot open or start the engine, rolling down the windows, those type of things. Now, rolling code we have
already discussed. Um, this is a randomized value that's sent along the signal to make each signal unique. And then the par code is something that's just calculated based on the actual signal that you're sending. With this said, I was thinking if I'm able to plan a brute force attack on this actual key fob signal, I would be able to unlock all of the cars of the specific model. So I tried to think, okay, what's the feasibility of a brute force attack? And I found, okay, we've got the header, function code, and the parity code, which we can determine already. So for example, the function code is usually um a four. In this case, it was I think four bits or so. And then
that's something you can determine beforehand. Now, looking at the rest of the bits, I need to try and brute force. Looking at the amount of combinations it's going to take me um in company with the amount of combinations times it the time it takes to send the actual signal. So, it's 380 milliseconds divided by two because we only need half of the signal. it's going to take me I can't say that number that many seconds and that's not feasible of course. So then I thought to myself but the signals are unencrypted. So what if I perform a targeted brute force? So in this case I'm going to intercept the victim's signal of which I can capture their user code and ID code.
Now I only need to determine or I guess brute force the rolling code value which is only 12 bits. In this case I can do it under 13 minutes. From the this point on I was like okay um this is already some good results but can I do better? So I looked at the rolling code trying to find any type of um predictability or things like that looking at the patterns and I noticed that this specific key fob increments their rolling code with two each time. So that's of course not random and not what you're supposed to do. And in this case, once I intercepted or captured uh the victim signal, I just plus two by
the rolling code, make sure I calculate the parity code correct, and I can instantly unlock the car. Now, this specific vulnerability is of course literally going against the whole spec of what is meant to be a rolling code. just sort of as a summary of the things that we've already discussed with the um attack surface in key fob communication talking about replay attacks but this is mostly mitigated by the um rolling codes then you can just use the rollback attack to bypass all the rolling code security controls then because the key fobs are unencrypted it allows attackers to actually analyze the signal to try and find patterns with it. Um then looking at the rolling code itself the
rolling codes are a lot like your OTPs if you want to take it to application security right so all of the OTP type vulnerabilities is going to be applicable to the actual rolling code being sent what's the brute forceability around the rolling code and what's the predictability about the rolling code and if we talk about replay attacks that um is the rolling code being invalidated or not those type of things. So after looking at all of the rolling codes, I was suddenly stopped in my research and was asked to investigate an incident. So no, this isn't really, you know, for client or cyber incident, whatever. Just someone asking me, "Hey, I found some CCTV footage of um a few
criminals stealing a car. Can I figure out how it happened?" Because it seemed a little bit strange. looking into the actual video. Um, just to sort of set the scene, I'm not sorry I wasn't allowed to actually share that video um, with everyone today, but explaining it at least I can. Um, what happened was the victim parked at a parking lot and there were shops in front of him, climbed up the car, made sure his car actually was locked. This is, I guess, the horrible thing of it. He even did the pool check and then went into the shop. We noticed that um a car stopped behind them. Um one guy um climbed out of the car, followed him
into the shop and then another guy stood at the actual car door. Suddenly the car door opens. Guy climbs in and then the the guy drove away. Shortly after the person following the victim inside of the shop also ran out and then of course they just sort of drove away together. And I thought to myself, how is this possible? So I started looking into the actual car, noticed that the car is making use of keyless entry and keyless start. So trying to look at that technology and I found out the type of attack that we're doing is called a relay attack. Now the concept of a relay attack is essentially what we can see here on the
diagram. We have one attacker standing at the actual car. When they pull that car door, the car is going to prompt a signal asking, "Is the key fob nearby?" The attacker then takes that signal and essentially um relays it to the other attacker, extending the range of communication. And then the second attacker grabs that signal and throws it to the key fob. The key fob's going to respond, of which the second attacker then grabs it and throws it back to the first attacker. In this case, the car is going to think as if the key fob is nearby. The same thing or same technology is used in keyless start. So they did the same attack twice just by following the
victim. So the second attacker followed the victim essentially into the shop with a relay device in their hand just stood near the person and the whole relay attack happened extremely quickly and they drove away. in this case or the diagram over here is an illustration of how it can be done if the key fob is inside of your house. Um, and here I actually have some CCTV footage. This I can show. It's just on YouTube. Um, and we'll see here how the whole attack is being performed under I think a minute and 20 seconds. So, we can see the attack has sort of stopped there and it's two of them climbing out. very nonstressful there. And the one
attacker, you can see they've got the devices in their hands. One attacker stands near the car and the other attacker goes near the house. And what they're doing is they are putting the devices one near the car and the one near the house so that they're relaying the signal of the keyless entry into the house. The key fob's going to respond and the car is going to unlock. This allows them to just go into the car. Now, funny enough, the second attacker forgot we need to hack the keyless start as well. And like, why aren't you driving away? He came back. Oh, yeah. Okay, we need to actually hack the keyless um start. Doing the same
type of thing. The attacker inside of the vehicle is currently pressing the brake, which signals the car to actually transmit the signal and then the car is going to start. See here there it starts and there the other guy runs away and both of them just simply drive away. So in this case this attack of course only works properly if the key fob is maybe near or um like near the actual wall because at that point the um relay device has to send the signal through a wall um hoping that the key fob is in range and the key fob has to respond back again. Another version of this attack I've seen is attacker instead of using a sophisticated relay
device, they simply took copper wires and made a very large circle and essentially hold that against the wall and it actually still worked. So the funny or I guess not funny but the very interesting part about the relay attack apart from how dangerous it is because we're not exploiting a vulnerability or we're exploiting the way the signals work with the car. So you're exploiting the actual technology because all they're doing is extending the range of communication. And when I I spoke to a few researchers um on LinkedIn talking about this attack and they were sort of living in Europe and the interesting part there is that there where they live there's not they don't like have walls like we saw in the
videos there's no fans there's no walls so the cars outside for everyone to see then the attackers resort to this type of attack where they relay the signal through a wall in South Africa that's a little bit less feasible because we usually have gates and walls and things like that it's a little bit more common. So in South Africa, the attackers had to resort to following the person um to perform this relay attack. So it's just very interesting um to think about how attackers has to adapt and evolve to different scenarios but still performing the same attack. So now we're going to look into the defense against relay attacks. And something that the manufacturers essentially said initially
is switch the feature off. I mean, yes, switching off the server does allow the attackers not to hack it, but in this case, you're switching a feature off that you've paid for. So, this doesn't make sense. The secondary point there is making use of a Faraday pouch, and we can see an image of it. It's essentially a pocket you can put your key fob in, and this is going to block all signals from um entering it. This isn't very useful if you do this um having it in your pocket if you're going to the shops because that's akin to switching off the feature, right? But this pocket would have helped the previous video of the attack because the
key is at rest, right? If you were to place your key fob inside of that pocket, putting that maybe on your coffee table, the attackers wouldn't have been able to perform the attack. We saw in the video. But now the problem comes in. What do we do when we're in motion and we want to keep the feature? And that's the last point over there. Key fob response time detection. And this is actually a sort of remedial action or mitigation that um I thought well I wouldn't say I thought of it but rather it's something I would pursue and recommend we sort of do a little bit more research on. The key fob response time detection what it does it's
literally working around the concepts of a radar where all we do is we look at the time it takes for the car to prompt is the key fob near me. The attack is going to relay that it's going to hit the key fob. The key fob's going to respond and then set the signal back. So all the car the car has to do is the car just needs to start essentially some um something like a timer when the car is prompting where is the key time the whole uh signal roundabout distance and time that it's going to take and then you can calculate that if it's taking too long then you can just reject the
actual signal. This is a nice way to allow the car not to be vulnerable to relay attacks. And then combining this with the Faraday pouch, your your car won't be vulnerable to the attack when your key fob is at rest at home and when you're in motion. One of the problems that we've seen with sort of looking into this type of remedial action is that key fobs don't respond um consistently enough to actually make this work. But at that point when we started looking at that we sort of um stopped for now because it's sort of like the key fob technology has to um get a little bit better in terms of the type of tech they're using in the key
fobs to allow this to work. So, we've spoken about quite a bit of um you know, automotive security and all of its attacks surrounding it, but let's talk about some of some of the more basic RF attacks out there to show you the attack surface or the remaining attack surface. Now, all of the attacks I'm going to show now just going to briefly talk about it. It's not something that I've um explicitly looked into or rather I haven't performed the attack. And some of the topics we're going to look into is RFID and NFC communication and more. So you'll notice already there's going to be similar sort of um attack surface points that we mentioned
earlier with the automotive security but of course for your normal RFID and NFC attacks as well. So we're going to look at for example replay attacks. This is the ability of an attacker to take the signal and then replay it. Let's look at your um building access control. If an attacker gets to a point where they can actually capture the signal. Now, of course, this is kind of hard because with access control, you have to be this close to capture it. Point is, it's still theoretically there where if they maybe put some type of receiver on top of the actual reader and you go and um access, you know, use your access control card to enter a door. Um they
would be able to intercept the signal and potentially replay it. Eavesdropping. So, this is literally performing um something like a man in a middle attack, but the nice thing about this attack is you're not sort of in the middle and passing the data through. You're just listening for all of the signals to come to you and then you can read the data. This is the very harsh thing if your signals aren't being encrypted because that means an attacker could read the signals and potentially read some sensitive data inside of it. A lot of the access control cards actually have um user information inside of the actual key card and that's going to send things related to that user which an
attacker could get. Also um this is related to your credit cards and banking cards. Um luckily they are making use of encryption so that's good but that's of course something to look at whenever you're looking at that sort of attack surface. Now with relay attacks, I think I sort of mixed the two over there. The first point on the relay attack is the one we just discussed where we extending the communication of the actual devices. Now this is going to affect anything that makes use of radio signals. You can do the same thing on Wi-Fi. You can do the same thing um for example um with your key fobs that we just discussed um with access control. Relay
tax is also possible. Let's say you have a device that can listen in on your access control um that sort of mimics the access control reader, right? You have one attacker standing at the server room that maybe takes um the access control card, another attacker having coffee with one of the employees. Now, with that, you're going to extend the actual communication from the RFID reader. And RFID readers basically pings every few seconds or actually almost um every half second to see if there is a card there or not. And then the attacker can just grab that signal, throw it to the guy having the coffee and then perform the relay attack again on access control cards. Now that's of course very
relevant to building um or office security as well. And now looking at maybe something with replay attacks. We spoke about key fobs, access control cards, but what about other things? What about ETOL? There was a bunch of attacks um that happened a few years ago where attackers would grab the ETOL signal coming from the boom gate. So that ETOL um device is going to send a signal back to your car and it's going to ask or essentially asking, hey, who is here? and the car's ETOL device is going to respond back to their with their specific information and with that information the um ETL gate is going to allow you go through and of course the
deductions is going to um happen on your account. But what an attacker could do is grabbing that RFID readers um signal and then replaying that to let's say you're going to a parking lot. If you know the RFID um or the E tag devices are sort of here in your um rearview mirror, then the attacker replays it to that device. The car is actually going to respond. Well, not the car, the actual device there. Then the attacker is going to grab these signals. They can do this for the whole parking lot essentially grabbing all the signals and then whenever they go to ETL boomgate, they can just replay your signal and the victim is paying for you. Of course,
that's some highlevel dedication just to not pay eel, right? Um then of course um card cloning and this is a little bit different from replay attacks because with a replay attack you are capturing the raw signal and replaying that signal. Whereas with card cloning, you are looking at how the card data has been read onto the actual card and mimicking the same process. So you can actually um write data to your own cards and you have your own physical access card that you can use with uh last thing I wanted to point out here with the relay attacks. Um I mentioned that some of these attacks are also related to banking cards and things like
that. The relay attack once again extending the range of communication. It works on tap to pay. So if an attacker finds a way to maybe insert a device on a payment uh a POS device, they would be able to extend the communication so they are at the payment device and then another attacker is just following you. If your wallet maybe doesn't have one of those RFID or signal blocking um sheav inside of them, the attacker can take the signal from the actual POS device, throw it to the card. the card's going to respond back and the attacker relays that whole communication and actually make the payment go through. Um this all of this information is also on
like publicly resourced um places. So that's if you're interested, you know, you can take a look at that. But one thing I want to mention is of course I know a lot of these attacks are quite severe, especially with the relay attack I mentioned just now of making payments. Um we don't really condone um looking into or exploiting any of this. And some other type of attack surface that we can look at is in the radio frequency hacking realm. What is a a denial of service? And that's where jamming attacks would come in. Jamming attacks can affect any device that makes use of radio signals. So if the device is reliant on um receiving data through
radio communication, you would be able to jam that device. examples on the automotive security side. Um, attackers can jam your unlock or lock function. We all know this to be common at your garage stations where you would climb out of the car and you want to lock your car, but then attacker would jam it. And in terms of jamming it, you just need a device transmitting on the same frequency of the receiver. So, they can do it with a garage remote. sort of just hitting the button in and then jamming your car from listening to the key fob sending the signal. The same type of thing affects your keyless start as well. So, let's say you
get into your car and you want to like there's some criminals running up to you trying to rob you. You want to drive away. They can start jamming your car and disallow you from essentially driving away. This is of course only if you've forgotten that you can fall back to the manual start again, which in all fairness with my mom's Mazda, I have no idea how to do the manual start. I only know the brake pedal and pressing the button. So I would be extremely vulnerable to whoever tries this type of attack. Then with the same type of thing, your GPS trackers can also be affected by jamming attacks. So, an attacker could steal your car, perform a
jamming attack on the actual frequencies of that um GPS tracker, and then your tracking company won't be able to actually know where your car is. I want to note there that car trackers are actually trying to make their tech a little bit more sophisticated. So, they're using something um called frequency hopping where they don't transmit on just one frequency. They sort of hop between them. But if the attacker has enough equipment, they can just jam all the frequencies. Of course, Wi-Fi cameras will be affected as well. This was a big thing um in some of the restaurants in Ptoria where attackers would um steal cars or things out of cars in parking lots and the
attacker would essentially buy a jammer and just jam the cameras there because if you're using a Wi-Fi camera and not doing a wired connection whatsoever, the Wi-Fi camera is going to disrupt because the communication is going to disrupt and the feed will essentially shut down. So that this was a common attack vector that they used to steal cars or things out of cars. Same thing is going to apply to office Wi-Fi. Let's put you in a scenario that an attacker buys a bunch of um jamming devices and they throw it maybe onto your roof or they hide it in your office. How would you resolve that? How would you find the jammer? How would you know your Wi-Fi is being jammed?
We don't have anything to do that. We don't have jamming detectors in our offices, right? Of course, I haven't heard of anyone performing this type of attack. So, of course, terms of statistics, probably not the best way to invest in something like that, but this is the type of thing that can happen when we're looking at jamming attacks. Of course, same thing with the office access control. Let's say there's a sensitive door with room that you can go in and then the attacker would then jam the actual RFID reader and that's going to allow your whole IT um team not to access that door. And if maybe at that stage they have to resolve to a more
manual method. That's when the attacker could jump in and get into the sensitive room as well. So some of my final remarks here is the whole talk we mentioned a bunch of um attacks on radio frequency hacking but the idea was sort of to show you my journey as to how I went about it and uh things that I found some of the mistakes I made um and also to give you some insight as to what it means to look at radio signals hoping to actually give some security awareness that these signals that fly around everywhere are actually quite hackable and at this stage because they're not even using encryption that much sort of tells you
how far behind they could be. So, thank you. Um, this is going to be my last slide and thank you for listening to Robin Hacking Airwaves. The sweet over there is Airwaves. Thank you everyone.