Going into the Underground by Michael-Angelo Zummo from Cybersixgill
Show transcript [en]
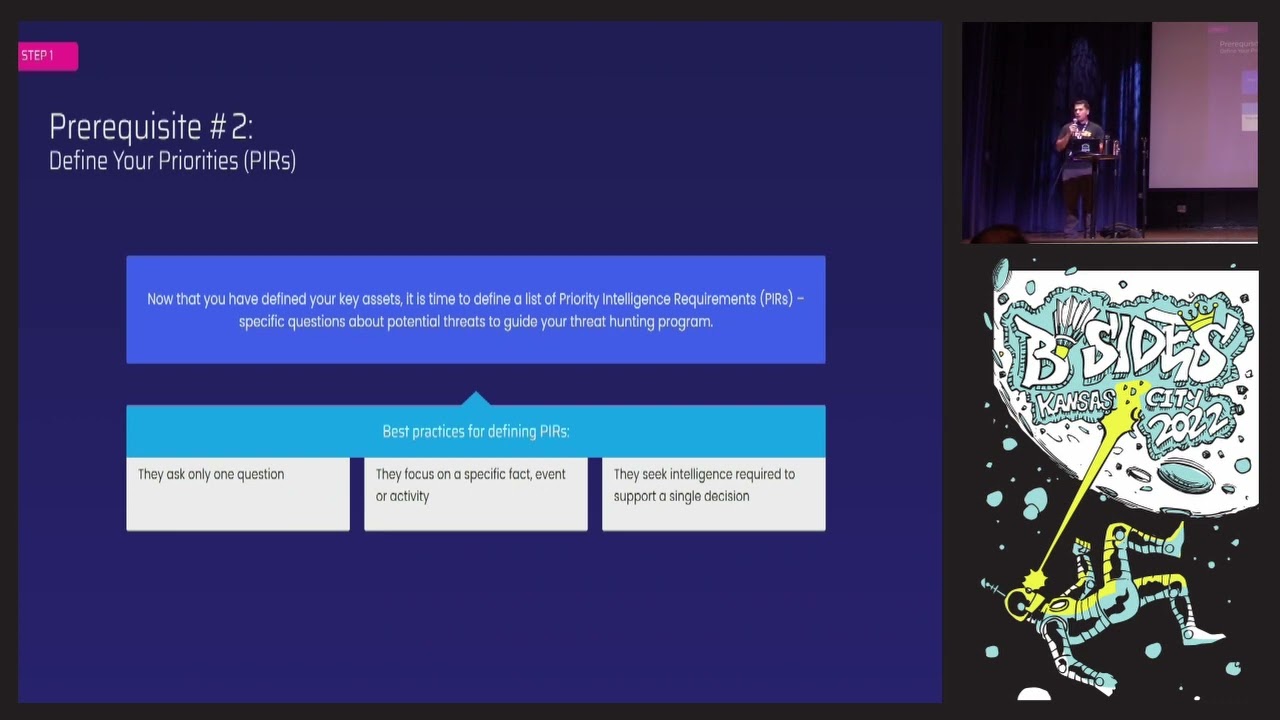
okay kept like switching up here um thank you yeah I'm so glad thank you that's all they've changed awesome yeah um I'm excited to introduce our next speaker Michelangelo Zumo Michelangelo is a um he'll be giving his presentation titled going undercover in the underground practical guide on how to safely infiltrate and engage um you're welcome to ask questions throughout and without further Ado thinking what thank you hey thanks for everybody for coming I'm Sumo I know there's a lot of talks that go on right now so I really appreciate all of you that have decided to come to my talk my talk is very practical so I plan to leave you with something that you can actually do on your own that's just a dark web talk I don't encourage you to do so but I am going to provide you some tips on how to protect yourselves and then for the Enterprise Enterprises and the companies in the room I'll show you how you could automate this and make your team's lives a lot easier when trying to extract threats that we're commonly coming across in the underground so I'm Zumo uh I presented at B-side St P last year I'm pretty new to Florida I've recognized a few faces I think some of you were at my talk uh in Saint Pete if you were raise your hand I thought I saw a couple people someone over here maybe but maybe I'm wrong uh but my talk last year was all about threat hunting and one of the questions that I got out of all the conferences I went to last year was well how do you even start how do you get access to these underground sources and how do you extract intelligence from them too to actually perform the threat hunting that I was teaching about last year so that's where this talk this talks about I am going to show you a little bit of threat hunting still so that again you can apply some of this to your own work in your daily activities but this is mostly going to be about how do we get started so the agenda and and based on your questions we might even talk about more than just what's on here but I'm going to show you how to set up your dark web environment or your underground environment using tools like tails for example OS system uh you can also use Virtual machines my go-to is Tails we're going to talk about how to find those sources we're going to talk about how to get access to those different sources and then creating your own Persona safely by disassociating it from yourself protecting yourselves while you're online and engaging with these type of threat actors how to communicate with them and basically we're just going to model our Persona based on what threat actors are already doing and then we're going to just do some thread hunting and if we have time he's going to give me a a hands up at 30 minutes if we have some time I got something very cool at the end for you so first what is the dark web I know like dark web is one of those terms almost where like when you hear AI or ml you're like oh okay but really the dark web is just anything that is not indexed by your search engines sources that require a special browser to get access to tools like Tor i2p or zero net when we talk about the dark web we're really talking about the underground because all of you some of you might be familiar with like response Bridge forms just went down there's a new forearm call that thing is called like poem forums now or something that's kind of taking its place it looks exactly like breached and breach looked exactly like grade forms those weren't dark web forms those are clear that you could access that with Google you know it's very easy to get access to but they're underground uh because the types of threat actors you're dealing with on those sources types of data that's on there types of threats that we're extracting every single day every single minute from those types of places so when we talk about dark web we'll really talk about the underground which includes those clear web sources it of course includes the deep and the dark web and it also includes messaging platforms like telegram QQ Discord even you see a lot of fraud on those types of platforms where threat actors are selling credit cards vulnerabilities zero days things like that so we when we're today you're going to hear me say the underground a lot and that's what I'm referring to again I'm trying to leave you with something practical something you guys could actually do on your own so because of that I have to give you some precautions um these sources are inherently bad now there are some sources that are hosted on tour that are no criminal activity on but the source I'm talking about are malicious you have threat actors that are on there trying to exploit you trying to exploit your companies trying to exploit anybody that's on there that's stupid enough to click on a link that they don't want to work so because of that I need to cost you all if you do try this on your own as you can see here I have an example of a threat actor that was sharing a tool himself and it just said hey by the way you need to be careful when you're downloading tools from other threat actors cracking tools and things like that because threat actors are loading malicious programs into these tools and while you're trying to take advantage of others they're taking advantage of you my go-to tool when I'm accessing sources when I'm maintaining my PreSonus is using tails tails is a it's a very light OS it's uh has Amnesia so every time you power it down it erases itself um you can put it on a a small thumb drive eight gigabytes is all you need uh it provides you secure Computing anywhere so you can plug it into whatever device really and Boot It Up they have it for even mobile devices now uh and it's going to protect you it's going to protect your network it's going to protect all your other devices because as soon as you unplug that it wipes itself as long as you don't store any of the data any of your own data or connect it to real live data or real personas then you should be okay but it's not Magic you still need to be careful and not log into other sites when you're also like log into your official accounts when you're also logging into underground sources I have a video because I'm using their their device the videos aren't working but I have don't worry I have a backup so I want to show you of the startup you guys see that okay so this is just startup of tales it's again it's very simple it's very light lightweight and when you log in you can see I'm logging in here it's it's got very minimal resources on it and it's all about just maintaining uh your anime animated uh so that you can protect yourselves against these threat actors reporters use this when they're overseas when they're Behind Enemy Lines trying to communicate with the outside world some like when there's human rights issues going on and stuff like that this is what tails is for protects you when you're engaging in malicious activity or suspicious activities things like that so let's go back into my rotation here all right so finding sources finding sources especially on tour or or the dark web it's not exactly you can't exactly Google these sources there are some that are indexed and you can get quick links to again breach forums raid forms when that was around the new poem form same thing you can find those sources easier uh but finding source is really it requires you to have an end with threat actors to communicate with them and figure out what where are you guys going where are you guys selling data where you got Sharon malware exploits all that kind of stuff that's where you find the real sources where the real threats exist and I have a couple examples here of different types of sources we have forums this is cracks form this is this form excuse my language is a real pain in the ass uh because it's a high maintenance Forum where you need to be active to really kind of get the threats out of there uh but again you can access this on Google it's very simple you have credit card markets these come and go every single day seems like uh these are just marketplaces where threat actors are selling your compromise cards have sort of miscellaneous marketplaces where they're selling everything from fake IDs to narcotics by the way I was previously Marine Corps intelligent for National Security I also worked in law enforcement uh taking down dark web narcotics dealers things like that so there are a ton of these markets and they come and go all the time as the FBI and other agencies are taking them down but when they get taken down another one is in their place initial access Brokers for the Enterprises in the room you're probably very familiar with these this is one of those threats that is on everybody's Minds nowadays these are marketplaces that use Steeler programs to infect your users machines and as those users are logging into their accounts or they're just stealing them directly from the browser it captures their account details and then sells them for very cheap on these markets we call them initial access Brokers because it provides that initial access into your network for sometimes as low as a dollar so I have an example I'll show you later but think about like the Uber breach those breaches breaches like that started from marketplaces like this where any threat actor can go in put in a domain find Uber and account to Uber and buy it for a dollar and then they can see what kind of damage once they've accessed and then you have messaging platforms as I mentioned earlier telegram they said there's tens of thousands of these I mean more than that but tens of thousands that my own company's monitoring already where we have threat actors against selling zero day exploits selling fraudulent items uh credit cards things like that but again finding these sources is not it's not like you can just Google you need to stay up to date and it when it comes to dark web sources you need an exact onion address to get access to that Source otherwise you're not going to be able to access you're not even going to be able to find it and because it's a dark web they're constantly changing these addresses so once you're in it's not like you're done you're good you're going to be able to collect intelligence from that Source all the time no you need to stay up to date as that site changes its address you need to be aware of it so that your collection uh remains constant as I mentioned some of those sources are actually indexed by other websites out there but when it comes to those it's really just about those narcotic sites uh child exploitation sites those are the ones that you can Google and you can find a place like hidden wiki the shadow Wiki or dark eye where they maintain links and tell you whether or not a source is up or down but those hacking sources somehow I'll show in a little bit places like ramp forms it's a very prominent Chinese and Russian hacking form you can't you're not gonna be able to Google that you need to be in with the threat actors to know how to get to that source and then you have to go through the step of actually getting access to it here's another example of um in a forum post where threat actors often share the links to the sources that they are active on and in this case you have a threat actor that shared the telegram Channel where they're often selling data leaks sharing tools things like that that's how we identify these sources and then we get in see what types of threats exist on there and then extract all that intelligence from those sources for sources this is just one of the many barriers of actually extracting the Intel from these sources again the first barrier is finding them now you actually have to register them this is where that Persona management is going to come into play but also you have to know threat actors to either invite you to a source give you an invite link sometimes you need to pay your way in the example here this is Genesis form oh I'm sorry Genesis Market this is another Marketplace uh initial access broker where they sell accounts uh I have a little bit of pride in this one because this is one that I gained an invite to through my personas I think like three years ago now this one has kind of dropped off a little bit Russian Market which we'll talk about is way more popular than this one is because they sell things for a bit cheaper but this is an example where threat actors had to invite me to the source and I had to provide that invite code to actually get access and then once it got to access we're able to duplicate start extracting Intel from there I've mentioned ramp forms there's another form you need to be verified by admins on the site or you need to pay a hefty fee to get access to it um I would never encourage you to pay a fee to get access to a source because you never know if they're actually going to give you that access online so if you're sponsored by your company you're spending their money that's okay as long as you're but don't spend any of your own money to get access to these City so pay a vendor or have your company do it for you uh because I've been burned plenty of times where I pay money and I don't ever hear from the threat actor again uh but again it wasn't my money so I didn't care um but there are sources like that that exist and these are the sources that everybody's trying to get access to because that's where the Intel exists that's where they're sharing these zero days and the the banking malware the cracking programs all that type of stuff that's where they're selling it and that's what we need to get in television I mentioned crack swarm it's a pain in the ass it's because this is a forum which is actually a good design where they require you to actually engage in the Forum to be able to get something out of the form so forearms again they're like ready think of it I've read it I'm sure everybody knows what Reddit is there's topics you click on a topic you can see the thread right most of those forms you can click on any top they can see what Fred actors are talking about but in the in the in uh for cracks you can only see them if you're actually participating or providing something to the community of that Forum so oftentimes I'm digging back into old like projects I did during my Master's I'm like you know breaking code and sharing that like oh here's how you hash something or something like that to make sure that I can maintain that access but it's a lot of work it takes a lot of work um to keep that status on the site and it's just another barrier that you actually you have to get around when you're dealing with these types of sources then you also have language barriers exploit form explains where many of you are familiar with that one it's a very popular one mostly Russian threat actors though some of them are actually kind and they also Post in English for you so you don't have to translate it or paste it into Google or whatever but then you also have Chinese sources as well very difficult to extract Intel from and translation tools are great but if a threat actor has particularly bad grammar you're going to notice it you might still get the gist of things but you're going to miss that exact transition and then you have VIP sections within those forms themselves so sometimes getting access isn't all the access that you actually need you need to then prove your status you need to build a reputation to get access to the VIP sections where some of the top threat actors are actually communicating uh and sharing the Intel that you're looking for now we're going to create our first Persona and there's some guidelines here you have minimum requirements you need to set up an email a burner email I use protonmail uh protonmail is actually a big head and a little they're kind of a pain because they want you to start paying but it is a great email burner email to use it's also a great email just to use personal if you want to set up something where all your spam goes um password managers do not make the mistakes that I've made over the years where you use the same password for all of your dark web forums and one of those forms gets taken over and then they find out your credentials and they wipe everything on it or to take over all your accounts don't do that use a password manager uh your persona needs needs to be completely isolated from your real the real you cannot be logging into your Chase account at the same time you're logging into foreign you know build a new language style don't write the same way on a form that you would in an email to your co-workers say slang terms come up with a new style uh because you don't want a threat actor to come to a talk like mine and be like you know what that guy sounds familiar and then all of a sudden they're digging into your profiles and they're like I think this is him set up pgp open pgp um this is a good way of gaining a threat actor's trust because of some of the top threat actors still use pgp to verify each other to gain that trust uh and sometimes they'll only share the most sensitive information when it is encrypted and I got a tutorial for you because that's a little bit more of a challenge jabber is also a very common form of communication I'll show you that and then of course Telegram you've been on time so far so my first Persona this is me this is pitiful my proton address is pitiful at proton dot me like jabber's pitiful at xmpp.jp by on forums you'll see me as beautiful and this is real you'll actually see this uh my telegram is that pitiful here's my pgp fingerprint oh and that was it I thought I had another one this time but that's me this is my Persona you will actually see this Persona that's right actors know I have plenty of personas trust me but threat actors know that this is a security research they know this is not somebody that they Trust uh but if you went on to any of the forms I just showed you you will see my logo there uh and the stupid threads that I engage in how do I create them I model them also do is I use my own tool cyber six skills portal where we're collecting all this data every single day 10 million plus items a day tracking all these threat actors I use our own tool to quickly analyze and figure out what are threat actors doing today what communication methods are they using so I'm able to pick a threat actor like Jack Lowe here from a cardigan Forum a form that does a lot of different things but their focus is selling credit card dumps compromised cars things like that and you can see Jack Lowe uses an xmpb or a Jabber he uses Telegram he or she I don't know who it is um and then you can see all their different aliases across forums here maybe I could highlight a food but it's this right here aliases on the bottom right so I look for threat actors like that and I say okay this is how they're communicating I need to replicate that I need to look like that so I can gain the trust of threat actors and as you can see I'm able to to ensure that I am capturing as much information as possible I can search across all of those these different sources At Once by using their jabber using their telegram address to see all right where are where is the start actor using these communication methods and you see these are all different sources here alternate carvilla cracking Gap recacking these are all sources that this threat actor is active on using these different communication methods so that's how I model myself uh and when I'm building my own personas you can see here's an example of the same threat actor uh on a forum I forget what form this is but it's pretty recent back in May uh where they were using even using Gmail or Outlook which always kind of again I come from law enforcement space after the military so when I was dealing with narcotics dealers if I saw they were using the Gmail or an apple or something I would just subpoena that information to figure out who it