Threat Hunting In Practice - Michael-Angelo Zummo
Show original YouTube description
Show transcript [en]
awesome so first off thanks for coming to my talk I know there's a couple others going on right now so I appreciate you all coming to this one hope I can leave you with something with something ply right even right after this talk so a lot of students in here no couple there we go don't be shy raise your hands uh yeah you know pay attention in this talk again there's a lot of Concepts I'm going to show you tools things like that that you can actually apply I know some security conferences could be a little bit higher level but besides is great uh so take everything in and you know try these things apply them at your home if you're
able to um but today I'm going to talk to you about how to level up your threat hunting using threat intelligence and we're going to start off going through a few slides just based on some requirements that you guys should have when building an effective threat hunting program but then towards the end we're going to actually walk through a threat hunt that I've conducted in the past with a partner of mine and we'll look at real live examples and show you how to find them yourselves so a little bit about me first I am Michelangelo Zumo I just go by Zumo you can find me on Discord my Discord ID is up there I'm also probably the only
Michelangelo Zumo on LinkedIn so you don't need to memorize that URL you could probably just search me and find me there but I started my career out in the Marine Corps Marine Corps oh God put that here a bark apologies everyone take cover um but I started out Marine Corps intelligence I was a Korean linguist doing National Security worked at the NSA for a few years and then transitioned into cyber when I did my masters in cyber crime investigations and cyber security did a lot of digital forensics and law enforcement I'm from Tampa originally from New Jersey but I I've relocated to Tampa now it's just that besides St Pete last week where I did the same uh demonstration so
again thank you all for for joining so first let's define what threat hunting is and to me I learned this a few years ago threat hunting is honestly just a constant game of cat and mouse it's finding the threats the evidence of the threats the threat actors before they find you or your organization which could be pretty challenging if you don't really know what you're looking for so we're going to go through some of the steps in how to conduct a threat hunt and identify some of the key requirements that you need and the evidence that you're going to be looking for so one of the first prerequisite prerequisites when building your thread Hunt is identifying your critical assets
and your critical assets can be anything that's important to your organization but identifying them what they are where they're located who has access to them and what type of data is accessible or hosted on those assets is going to be really important to understand when you're trying to identify your critical assets every organization has you know you know large organizations have big fingerprints Footprints out there and there's probably tons of assets that they can be monitoring for but identifying those priority ones is going to allow your threat hunting to be more effective and and focused on the types of threats that you guys should be monitoring for foreign these assets there's a few things that
you want to going to keep note of I apologize for the size of the font here but I'll I'll highlight some of the the main ones you definitely want to be taking note of your assets make model OS versions uh because threat actors are constantly looking for vulnerabilities into the different devices applications that you're trying to protect so understanding all those different details for each of your assets is going to allow your Fred hunting team to focus in on again specific threats and identify any active exploits targeting those assets and allow you to better defend them other things again I mentioned earlier you're going to want to take note of is what types of data and who has access to
those assets you know in in today's world pre-post and during covid uh you know we're largely a remote Workforce Now across many different Industries so understanding where your assets are located who has access to them who needs you know what permissions and privileges do they have on those assets are all things you're going to want to understand so you're trying to tell your thread Intel team or your threat hunting team knows how to better defend against active threats and also when inventory you know it could be pretty difficult to understand what assets are out there that threat actors can get their hands on we're going to go through some of the ways that threat actors do Recon on your
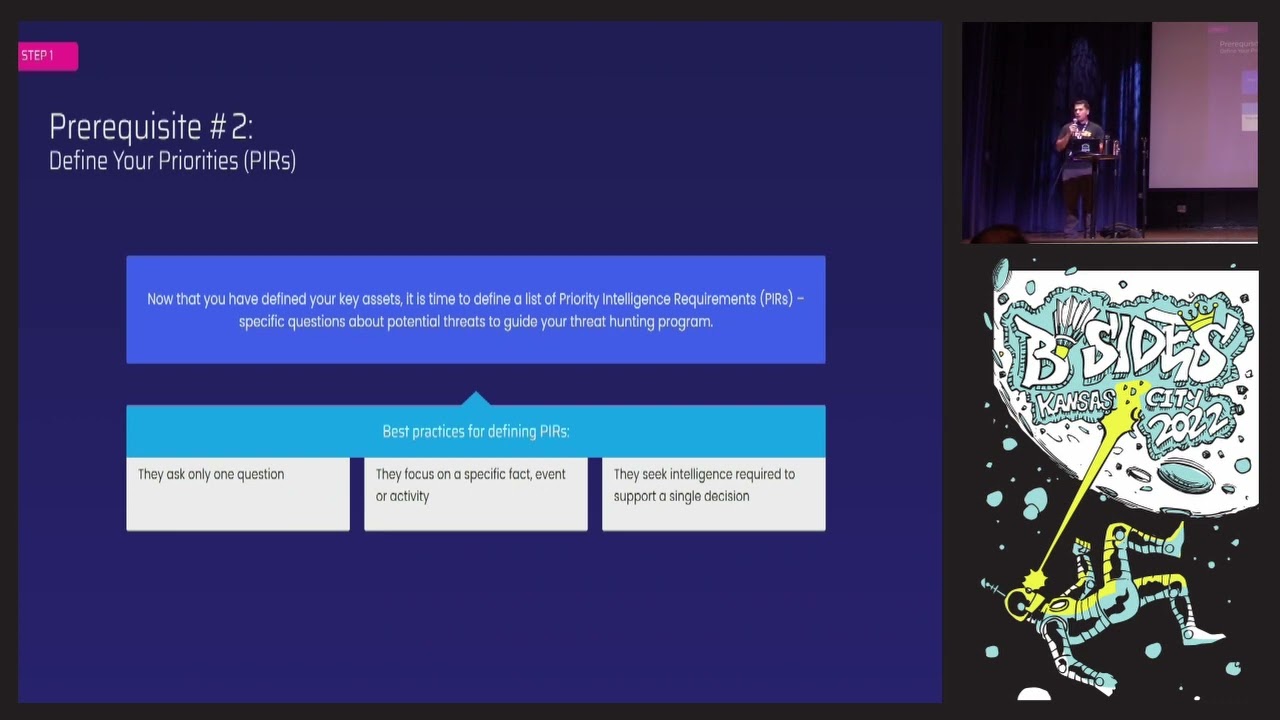
organization and these are all open source tools and I'll show you guys those but using tools like that is going to allow you to understand you know if somebody in HR department on the other side of the country is setting up some website where they're putting your organization's IP or any information on that might cause a breach so you want to again understand where these assets are located and who has access to them prerequisite number two is really up to your threat intelligence teams the analysts the threat Hunters to identify the priority Intel requirements your pirs and these are going to be created once you've identified identified the critical assets that you guys want to
protect and this is going to really allow them to stay focused Michael James was talking earlier in one of the rooms on Ocean open source intelligence and one of the issues he brought up was setting a too wide of a scope because there's a ton of things that you can be investigating out there when it's open source intelligence deep and dark web intelligence you know cyber intelligence and if you set too wide of a scope you're going to be collecting so much data you're not even know what you're not even going to know what you're looking at so setting those priority Intel requirements for example if you have a remote Workforce you've got people logging in from their homes you want to
identify the types of threats that they're prone to and then start investigating the types of evidence you might find detective threats that you might find that are targeting those types of users and then Focus your your intelligence gathering and investigations on those threats rather than just saying hey today I'm going to go find some threats because you could find plenty of them but they might not actually line up with your priority Intel requirements then we're gonna plan the hunt so again the purpose what are we looking for why are we about to conduct this this hunt and for many organizations it's easy well we want to better defend ourselves we want to be we want to get ready
prepare ourselves for the next potential attack we want to see what other organizations in our industry are being targeted by and what kinds of indicators compromisers compromise what kinds of risk can we find in our threat hunt to better defend ourselves setting that scope again setting too wide the scope is going to make it very hard for you to come up with quick results quick results that you could take action on so picking one thread at a time investigating analyzing those threats and then moving on to the next one it's okay to conduct multiple thread hunts but you don't want to conduct one giant one and then understanding your limitations and there could be a lot of different
limitations you come across one of the main ones for me is what tools do we have access to and again we're going to go in a few slides here we're going to talk about some of the open source tools that you can use we're going to talk about premium tools that you can use as well but limitations and the types of tools that you have access to May determine how quickly you can conduct a threat hunt and how efficient it can be and when you're determining these tools you're also going to want to identify any of the potential gaps uh because of the lack of tools that you have or the lack of visibility that you might come
across so let's equip the hunt for many of you that are already in security roles uh or if you're a student learning about these there are a ton of different resources out there that you can get your hands on to help you start hunting you know just create a foundation of places where you can start hunting and identifying these threats even if they're not targeting your organization but things like open source intelligence feeds uh ISAC feeds for whatever industry that you might be in there's going to be a good place to start so you can just start consuming intelligence around indicators compromise and what other organizations what other security Personnel are observing out there uh in
in the attack field also Google is a great it's a great tool I'll show you in a couple of slides some Advanced searches that you could do to help you one do some Discovery and seeing what assets of yours might actually be out there excessively accessible on the internet but also to just do research on what is everybody else talking about uh in cyber security what types of threats are common right now things like you know Twitter feeds for example it's it's a it's a great place to go I wouldn't spend all your time there but you know people are constantly tweeting out the latest vulnerability the latest exploit case or the latest indicator or compromise for
whatever attack it might be Web spiders you can build your own of course uh and you could just start scraping you know the clear web you could try and do the deep and dark web uh and and other types of sources as well uh but what spider is going to come in with a lot of your premium tools where they're collecting data sources from all over the Internet and giving you sort of a central location where you can simply just search and analyze for any potential threats which is going to be useful for especially those that are just starting out that might not understand or know where these threats typically exist or where they're being
discussed that could be one of the biggest barriers that you come across when getting into threat hunting is not knowing where to look especially from the next external perspective and then we talk about some of these other ones again security blogs I like I like reading the Talos blog um crowdstrike has a great blog as well those are great places to just see what is trending out there what new attacks are coming up uh and and they often are identifying indicators to compromise that you can use to defend uh yourselves now we're going to execute the hunt the first step of executing the Hunt is in my opinion the worst one it's the collection um this was you know as an early and
early on in my career uh when I was basically just a data analyst uh was you know I was responsible for collecting everything putting it putting it in spreadsheets uh trying to extract whatever analysis I can out of it uh the collection though can be the the most taxing portion of your threat hunt uh and it also could be the end of your thread hunt right at the beginning because you don't know where to collect from as I mentioned earlier so it's going to be important to identify the different data sources that you want to collect for youth right on so that you can minimize as many gaps as possible where evidence of these threats might
exist when you're conducting your thread on processing the data is also a difficult portion but there's many tools out there that will process data for you both structured and unstructured data and this is going to be important to process data so that you can again quickly extract uh any types of data sets that you want from the data that you've collected but then also to apply playbooks in your different systems that you might already be using and also to allow your analysts to analyze it that's my favorite portion uh Beyond you know after the collection step is the analysis and you know there was talks earlier about Automation and a lot of these things being done uh just through
machines but I firmly believe that you're always going to require an analyst to review data or threats uh because I mean if we get to a point where machines can make decisions for us then I guess that's great but ultimately it's going to be up to the the analysts to again understand what are the pirs that we have set and once we've received a threat is this something that really matches up with what we're trying to protect ourselves against uh and what types of actions can we take lots of threats are unique uh so you you know you can have to come up with different playbooks every once in a while so being able to review those threats uh rather
than just you know blanketing A playbook for any type of threat it comes in is why an analyst role is so important and then conclusion this one is the this one uh I like the most because I remember being in roles where people before me conducted investigations whether I was in military law enforcement cyber security uh and I've seen you know the results of those investigations but I didn't know how they conducted it so we're going to talk about making sure that whatever threat on you conduct make sure it's as repeatable as possible for yourselves and for everybody that follows you afterwards uh I believe in karma so document your threat hunts so that the
next person in line has an easier time conducting their Throwdown because you don't know what pouring and Cur of their career that they're in uh and it might be a Brand New Concept for them uh and hopefully if you document it then your next role might be easier and hopefully somebody that you replace or uh you know take over responsibilities for has documented as well make your lives a little bit easier and then evaluating the hunt so once we've conducted our hunt you should have you should reflect on it and see how efficient was it were there any gaps that we identified during our threat hunt which delayed uh our our results um you know did we identify anything
that we were lacking which prevented us from seeing specific types of threats that we should be investigating and that's going to be again looking at did we collect from the right data sources and did we have the right Tools in place to allow us to collect or analyze that data so ensuring that you're evaluating your thread hunts every time you conduct them to make it uh and to improve upon them for your next run Hunt is a very important part of the process don't skip this process and then concluding them as well um sharing that I can find I was going to jump ahead there for a second but in this field uh and it's it's the same
in the military and and in law enforcement the government as well pretty much everywhere I guess um it's very easy to go unnoticed and when uh when you are noticed it's usually for bad things a breach happened or you messed something up you shut down a database by accident or you ran a tool that you weren't supposed to so when you conduct these thread hunts you've documented them and you've come up with an action plan because of that threat hunt make sure you report it show your bosses show your manager managers so show your executive leadership uh and get the credit that you deserve this is not an easy field and again uh oftentimes there's not enough people
that are promoting their employees uh showing the work that you have done communicating it up to Executive management so make sure that you are doing those for yourselves so that the hard work that you're conducting is is is seen uh by the right people so how does this work in practice this is gonna be the fun part I got through all the slides all the words these are probably all the words that uh that I was able to type are done with pretty much but now everything else is going to be pretty pictures and screenshots um but uh the next several slides are going to be an actual threat hunt that I've conducted with a partner and I
actually just inserted a couple new slides from a recent breach that we'll talk about the Uber breach I'm sure you've all heard about it I'm still taking Uber though um but I included a couple new slides in there since my last talk at St Pete but when we start our threat hunt again uh assume that I already have pirs I'm working with a partner so I collect their pirs uh and it allows me to understand all right what are you trying to protect what types of threats do you want to find uh and and see if there's any evidence within your environment uh that we need to take action on so in this case again remote Workforce
uh one of the most common types of threats that we see targeting Partners today organizations today are those that are gained through initial access fishing supply chain compromise trust relationships valid accounts for the new people the students that may not have gone dived into threat intelligence or threat hunting yet the minor framework is going to be one of your best friends when trying to understand what types of threats are out there what types of threats are you prone to and what types of evidence might you might you find for those threats this is a great starting place for your thread hunts and it allows you to create that scope to stay very focused on your threat hunts and
not kind of go down some of those rapid holes that you can easily go down in this field so familiar familiarize yourself with the minor framework uh it's a great resource and they they build their their framework in a very convenient way to read and explore so I highly encourage you to you know even log in right now to to take a look at it and one of the most common places that we see threats like initial access uh valid accounts compromised third parties and vendors and things like that are dark web marketplaces marketplaces like the one you see on the screen Russian Market too easy Genesis Jamia if that's how you pronounce it I don't know it's just what
I call it uh there are several others like it they pop up it seems like every single day and there's also plenty of different forms both clear deep and dark forums where threat actors are auctioning off accounts that are that are captured the very same way these marketplaces are capturing them and what these marketplaces do is they use programs like azero Redline Steeler not the mandiant redline Vidar raccoon info Steeler there's a ton of these tools out there both paid and free or cracked uh that threat actors are can get their hands on very easily and deploy just with basically pointing it at uh a URL or trying to infect a victim's machine and then they can start
harvesting credentials for that victim's accounts very quickly it's basically just a point of a push of a button once they download it we'll we'll show you later how how easy it is to find tools like this uh but again a lot of them are paid some of them are free and they're very accessible and the Uber breach Uber acknowledges themselves they announced it as you can see the in the Uber Newsroom here uh acknowledge that the contractor that was compromised in this attack uh likely had their information stolen by one of those programs that I had on that previous slide uh and then sold on a dark web Marketplace so I forget when this was I think it was
last week or I forget what date we are at but it was either last week or the week before that and again they said that the count for this contractor was likely sold on a dark web Marketplace well if you're familiar with these marketplaces that showed on that previous slide then you would be able to log into one of those and find an account for example the one here on the left-hand side of the screen I apologize it's kind of hard to see it on that screen there so let me highlight that on 9 15 2022 we could see that someone's account to uber.onelogin.com was listed for sale for ten dollars on this Marketplace it's an interesting thing interesting
about these threat actors that sell these accounts on these marketplaces is they're not actually vetting the data that they capture through their Steeler programs and they don't even know that they have access like in this case this uberonelogin.com because they capture so many of these every single day they sell them for as little as a dollar in some cases and there's so many threat actors buying these things up that it doesn't matter to them what what types of access that they can have uh through the accounts that they capture they're gonna make money anyway but what we see is ransomware threat actors sophisticated apt groups things like that they know that these groups these vendors are
getting access like in this Uber instance and they're scrolling these marketplaces purchasing these initial access these compromised accounts for just a few dollars and then they're able to wreak a lot of damage on these organizations as we've seen in fact with the Uber one if you search a little bit more on these on these marketplaces there was actually five accounts with uber.onelogin.com in that same week that that breach happened so it's very likely that whatever contractor was compromised had several other employees that were compromised as well which I'm sure by now Uber has taken I hope has uh has fixed that and has identified uh what I was able to surface through my investigation but Uber's not
the the partner that I work with in the threat hunt that we're going to keep going through here it just happens to be a recent example that I want to show you uh you know based on the types of threats that we see out there so when you're conducting your thread hunt again you want to understand what your critical assets are and some for some people they might have difficulty in identifying these assets so you want to then perform reconnaissance on yourselves because this is what threat actors are doing this is this is how their footprint your organization to identify where are we going to start our attack well we're going to at least try
to get in and a lot of them use open source tools like like you see here it's a little hard to see it up there but DNS dumpster search DNS recon who is even Google these are all tools that they're using to perform open source Intelligence on your organizations to identify the assets that they're going to start targeting there's a few screenshots here and for this particular partner because it is a pretty high value Target I did redact their name uh but I assure you you all know who it is and you might be able to identify it based on some of the screenshots you'll see in the next few slides but in this case I've redacted
their their name and I just made up my own Zumo bank that will be used as the victim in this case but we can see here again we can do some who is searches we could do some search searches to look for any type of sub domains that are registered by the same organization same thing these threat actors are doing to identify your assets DNS dumpster if you're not old school like I'm not old school I like I like a fresh gooey uh I hate going into the terminal so DNS dumpster is one of my best friends uh if you're like me I recommend it uh or even just Google um and you can see two of those slot uh
two of those images here one of DNS dumpster or you can identify some of those publicly exposed domain self domains and then even Google is very useful to do some Advanced searches on and kind of help through the process of elimination just help you identify what assets are publicly available or accessible uh in this case here I I use twitch as a different example but you can see that I removed www.twitchtv from my results and then I looked for any other subdomain with Twitch TV and then you can see we're able to identify a status dot Twitch TV which basically just tells your Twitch is up or not uh and then there's even a developer.twishtv so again dread actors
are performing these same types of reconnaissance steps to footprint your organization and look for the tax vectors and besides Saint Pete last week uh there was a keynote speaker Dr stunning Ware she's the uh ciso at FIS down in Florida and she started her career out similar to how I started my career out but she was more on the pen testing side uh and co-development and she had this funny example where she talked about where she was so eager and so uh anxious to get started where you know she'd download Cali and used you know just started playing around with all of the tools that come pre-installed on Cali Linux I had a similar story oh well so the
result of that was she was playing around with all the tools and she she shut down a lot of her own organizations databases which got her in a lot of trouble she still she's so today so she she made it okay but I have a similar story where I was playing around with DNS Recon and uh and I you know just went ahead I thought I knew what the tool does and hit the play button on it pointed it at I think at that time I pointed at something you know uh maybe something like active site or something like that um but uh if you don't read the documentation or if you didn't read the
documentation once the program starts you're you know all of a sudden in brick red bold letters comes up you know brute forcing initiated or something like that I was like oh crap um so make sure when you play around with some of these open source tools that you read the documentation read demand Pages uh read The Help files because you don't want to just point a tool at some domain and then hit play you might get yourself blocked by an organization that you might not want to be blocked by or worse so we've done our reconnaissance and now we're looking for some easy ways in into that organization and one of those easiest way easy ways
are lead credentials if you go on to paste bin if you go on Reddit if you go on a deep and dark web Forum if you go on telegram or uh you know QQ or even Discord you're going to find files with just lead credentials in it username email password combinations and this is one of the ways that threat actors you know maybe the less sophisticated ones but even the elite groups the APT groups and Ranch run groups are trying to get ways into your organization they're just using what others might have already exposed whether it's through your own organization's breach or through a third party breach that you use your employee login for uh and then reuse the password
these threat actors can collect these credentials from all those different dumps put them in their own sheet and then use some whatever available credential stuffing tool is out there pointed at your URL and just see if they get any hits uh it's it's that simple a lot of these tools again are automated and you can download off of GitHub or some Forum uh and and deploy it as simply as that and in this case for again I've replaced a name with sumo Bank we see that David my co-worker on 228 2022 uh was exposed through a third-party breach and their password was my dictionary password not very difficult to to uh to crack we also saw on that same day that an
account was for sale for safemail1.zumobank.com very similar to that Uber breach uh the Uber account that we saw on the previous slide and in this case was available first for ten dollars so already we identified two uh potential access compromised access for this organization where threat actors can get access bless you in fact if we looked a little further back over the past year using that same safemail.zumobank.com we saw that there was 337 instances for this particular partner where that's very same access was compromised and listed for sale for very cheap on these marketplaces with proactive starting fret hunting we could have identified that previously uh and potentially blocked any impacts or threats uh that would occur from this
but as you can see in this case we weren't doing this proactively yet oh good you can see it up there so with this partner we actually purchased one of these accounts from these dark web marketplaces this is one of my responsibilities I maintain uh all my personas across these different sources and in this case we purchased one of these accounts again I removed the actual information from it but when you buy these accounts from these marketplaces you could see the types of information reveals now in this particular account there was way more accounts for this particular victim uh that like their Facebook their coinbase account was all compromised uh by one of these uh uh
malicious feelers in this case was Redline Steeler uh but we see that username zuma1234 and that same password my dictionary password was compromised through the red line scale program and had I not purchased it a threat actor would have came in here purchased it themselves and and see uh exactly what I can see right now and then use it to log into that organization Network so keep Redline in mind because we're going to implement this into our threat hunt as well it's you know we we know that this in this case this is the threat for the the tool that was used to compromise the counselor for our threat hunting we want to identify well how do we defend against this type
of program and with so many accounts listed for sale over the past year we want to see well did we have any data leaks that we didn't know about and in this case they did uh back in January January 30th 2022 the threat actor Christina if you could see that up there on a very popular form that is no longer active uh thanks to law enforcement uh Forum rate forms posted a SQL database for the Zumo Bank listed it for sale on raid forms for actually pretty cheap uh and I blurted out the actual evidence here but Christina he or she I'm not sure but a very well-known threat actor actually he's posted screenshots of the
leak which allowed us to quickly validate oh crap this is ours uh we need to figure out if any threat actors purchased this from Christina uh and we need to now monitor Christina uh moving forward to see if she's going to continue targeting us what you're able to do again through analysis tools tools that are collecting intelligence for you and giving you a central location to sort through that intelligence in this example um I don't want to talk too much about vendors but this is from our platform where we're able to see that Christina is very active across the deep and dark web very active on telegram uh we're able to see that she was selling
databases and services across a variety of different sources we could see all the different threat actors that she was communicating with pretty much on a daily basis so these are threat actors that she was potentially collaborating with or possibly selling the data to and when we were trying to understand her capabilities we saw that okay based on her previous activity right around this time when we searched she also had a outbrokers database she was selling and even a CSV file to the U.S Air Force that she was selling at that time so we didn't think that this was just a you know case where she got lucky and you know or maybe took the data from another
threat actor who was reselling it we we believed that she was very capable of getting this access herself um and potentially targeting us again I'm not picking on the Air Force either all the other military branches have been breached in the past as well even the Marine Corps we've probably been breached several times but there was further ever evidence that Christina uh was very capable because we see that she was even selling basically pet testing services footprinting services for organizations uh across those different forums where threat actors could pay a hundred bucks and she would build a footprint for whatever Target you wanted and she would sell this across these different forums and if you
looked at her post she would have hundreds of threat actors replying to her her service with targets uh for she would then you know DM and you know conduct whatever whatever transaction uh that they were going to do from that point so in this case Christina wasn't just some script Kitty uh we don't think at the time we didn't think she was part of like an apt group or a government group or anything like that but was a very capable threat actor and so we want to now monitor her and proactively uh uh analyze her activity in our future threadlines so how can we now be more proactive and defend against some of the threats that
we saw in those previous slides well Redline Steelers Red Line Steeler was the uh the obvious uh malicious program that we observed once we purchased that account from that dark web Marketplace the red line stamp was on there so we know that that that particular vendor used Redline in that case and we want to first see how accessible is Redline or I'm sorry we want to see what are the capabilities of Redline stealing and all those programs that we saw on that previous page uh where you saw Azeroth raccoon info Steeler Redline and things like that they all pretty much have the same capabilities and back in February of 2020 Redline Steeler which it was
relatively new back then a couple years ago we knew that the basic build features of this program was it collects from your browsers it captures your login and passwords cookies autocomplete Fields even your credit cards that you've saved in your browser so on and so forth now there are a variety of different versions of all these programs that threat actors put their own flavor on ADD their own capabilities to so when we identify the threats we want to understand well what capabilities they're to have because it might allow you to Branch off into another threat hunt and to you know identify other threats that you might might have to worry about foreign so trying to understand well how
accessible is this tool is this something that we're going to encounter again is this something that we really need to worry about and this again this is quite small but I hope you can see that okay uh a simple search across all these different sources that I'm familiar with deep and dark web a clear web different marketplaces threat actors can get their hands on these tools very easily if you do this simple search on raid forms on breach on exploit uh even on Reddit for a red line Steeler you're going to find some link where you can go download this program buy it from a Marketplace both clear indeed or at least find a vendor that says they have
access to it and they can help you out if you reach out to them very accessible tool along with all those other tools that we see compromising thousands of victims every single day so we want to then use tools to well how do we identify a red line uh and how can we see if any of our endpoints are infected with it well that's what virus total comes in buyers total uh is very useful because you'll have other analysts engineers in your field that have identified these threats and have uploaded the information the indicators for these threats to allow you to use them and block them from accessing your organization now again there's a variety of versions
for these tools because of how accessible it is and threat actor is able to put their flavors on it so something like a hash well for a file for that program is going to change as threat actors manipulate it but if you use virus gold there's enough people identifying these threats within their organization unfortunately that you can use that in that intelligence to better defend yourselves there's also a post down here in the bottom left that I have where it was really just a tutorial on a Russian Forum uh where a threat actor was basically telling you how to use the program and it's really just a download and click uh or push push to play
program that's how simple it was that the tutorial in that screenshot was basically like I don't know 300 words very easy to use foreign so now we know the types of assets that we've we want to protect we know the types of threat actors that are known to use those uh threats and we know the threats themselves or the programs that are used to Target or our organizations so moving forward because you want to proactively identify these threats through your threat hunting uh and and build a a a program that you can repeat every couple of weeks maybe once a week every two weeks every month whatever you want to set but you want to identify
once you've implemented new processes new security policies after you've conducted your first thread hunt you want to identify in future threat hunts have we done a good job at reducing our risk our threat actors targeting us more are they targeting us less are our assets more easily uh targeted so on and so forth and with a an effective program [Music] uh you can build a program where you can do this analysis again uh very easily and identify these threats and trends in this case when we conducted this threat this initial threat hunt for this partner we saw that in the past year there was over a million mentions and threats targeting their critical assets uh it wasn't just uh you know we weren't
just searching for one like in the Uber case we actually identified a dozen or so different assets and we there was over a Million results in the past year some of which might not have been you know imminent threats uh but threat actors were actively discussing and targeting this organization and looking to get access to them and if you have an organization that has a lot of money um then you're likely targeted as well but if you conduct these threats on threat hunts over time then you can see have we done a good job at implementing implementing new security policies new tools to defend ourselves because you'll see from time to time has those mentions
gone up have they gone down our threat actors saying anything different about our organization so on and so forth and this is a great these are great metrics to provide to your leadership to get that recognition for the work that you're doing are you guys doing a good job and showing a decline in uh in those mentions in those threats it hopefully shows that you are doing a good job but even if there's an increase it's going to allow you to conduct another investigation to figure out well why are why are threat actors targeting us even more now was there you know a recent business transaction that happened in the organization or news article about what something your
organization did that all of a sudden spurred a lot of activity in the underground for your organization or is there an actual threat or vulnerability that you guys weren't aware of that you need to identify so building that repeatable threat hunting process will allow you to conduct analysis like this and provide those metrics to the people that aren't going to exactly understand you know maybe the steps that you've actually applied like we did in the last few slides and then other considerations again evaluating your threat hunts and understanding well what can we do now that we've identified these threats to better defend ourselves and some of the obvious ones for initial access type threats compromise accounts is
implementing 2fa MFA uh things like that to add another layer of security so that even if that initial access was compromised you're going to need a more sophisticated threat actor to come up with methods to get Beyond those other policies that you have in place they are out there there are threat actors can do that um there was a presenter at Beachside St Pete that was talking about um a organization I forget which one it was where the threat actor was constantly sending requests uh to their mobile phone to get access to their account they already had the log and a password but they couldn't get past the uh the secure login so they kept sending
uh the message to the user's phone the user would not click uh you know or approve that it was them making the request so the threat actor reached out to the victim over WhatsApp and said that they were the I.T Department which if your organization's I.T department is reaching out to you over WhatsApp you should probably not trust it you should probably get in touch with somebody else and figure out if this is a real request but they probably it's probably not a real request uh but anyway in this case the victim actually fell for that um and then the threat actor got access so educating your employees is also an important step to improving your
security and that's pretty much it again these talks that we like to do we try and like to provide you with something that you can actually apply on your own a lot of the slides that we showed or slides that I've you know that I've gathered from my own tool but these are things that you can do manually as well you can explore the deep and dark web you can explore these militia sources out in the open web and you can obviously explore places like Telegram and things like that um just a little advice especially for the students in the room deep and dark web I mean again it's it's like a mystery to a lot of people it's
not exactly hard to get access to all you need is a tour browser uh to get access to these sites um but I would caution you if navigating to those sites because there are threat actors on there that are looking to uh uh take advantage of uh you know beginners to those places uh people that aren't protecting their identity and are just clicking around willy-nilly a lot of the files a lot of the links that that are on there are malicious and you will expose yourself to pretty serious threats if you get if you navigate there so I recommend exploring the different ways that you can keep yourself safe by using premium tools like ours or
implementing a dirty machine using programs like uh like Tales OS Linux based program or Os that wipes itself every time you you log off of it and also has vpns installed to keep you Anonymous so because of my talk focused a lot on those types of sources if you are going to investigate them all just you know be cautious uh and try not to click on any links that where you don't know is not going to navigate to so that's pretty much it uh any questions [Music] don't be shy just no hard questions
and that's a great question so it depends on the threat actor there are plenty of threat actors on forums that will post a bunch of dumps uh and they'll repost it across a variety of places um and you never know if another threat actor has already used them or even if the credentials are valid but when it comes to these marketplaces like the ones that I showed on the slides these are threat actors that have a reputation to uphold and they want people to keep coming back to their Market to buy more uh and threat actors they communicate so if they were buying credentials that weren't valid they would or were resold they're going to let everybody else know
uh and in every case where I bought an account uh it was always valid uh the username and password was valid when we purchased it the account is taken off the market right away that being said that the machine that was infected which harvested those credentials um if you don't disinfect that machine it's likely that it's going to identify that once you've identified that that compromise and have changed the Account Details privileges passwords things like that that the program that is infected that machine is going to recognize that the credentials have changed so in that case they will sell it again once that program is communicated back to the vendor they identified okay there's a
new username password combination and they will list it for sale again but most of the time they don't resell them because again they're looking to uphold their reputation uh but again if you leave that machine infected you don't remediate it there's a good chance that the list of for sale again once they identified that the details have changed great question I have a coin for you by the way so don't don't leave go ahead [Music] of automated premium tools no so uh that's what our tool does um there are a lot of tools out there uh that use Web spiders to crawl these types of sources uh every single day continuously that's what we do we are
constantly crawling uh deep and dark web sources open sources messaging platforms and just collecting everything that we find out there so that threat Hunters like yourselves security Engineers can use tools like ours to find whatever threat uh your organization might be vulnerable to no matter the priority Intel requirements you have if you're a programmer and you can build your own spiders um then you can collect the data yourselves the challenge is going to be knowing what data sources to collect from uh and that's where we come in we just collect it all great question I missed at the beginning who do you work for what's your company oh yeah great question I work for cyber
six skill we are a threat intelligence provider uh using automation based out of Israel and uh there's um we're using complete automation to just collect data from those different sources we have very few analysts like myself all of which pretty much have military law enforcement or investigative uh Intel analysis backgrounds so we do maintain our own personas across these sources I can't tell you who my personas are I can't ask myself like that but we are on those sources getting access communicating with threat actors to find new sources and things like that so we get that access and then once we do we just suck it all out of there so great question oh we got more we got
more relatively large company
what would be the actual primary focus that you would look at if that that person's Cycles were very limited that's a great question so an organization with oh I'm sorry with uh limited resources limited tools I would start consuming fees did you get it you got it I would start consuming feeds tried and sell feeds uh you know there's open source platforms like like misp for example uh I think alien volts got their own open source one as well uh or free one at least where you can start ingesting indicators compromised from places like the ice hack feeds the government type fees there are other open source Feeds out there as well and that's at least going to get you started
uh and give you the ability to at least identify these types of threats um and and build uh playbooks to block these threats from entering your environment feeds are a tool that you can use that really an analyst should not be spending their time on anyway it's something that you can easily just consume and apply to Playbook to and automate it rather than spending your time looking at it all especially with limited resources abroad Spectrum it's rather difficult to mail something down yeah and with those feeds you can use it again you can use it to just automatically block threats but then do some internal threat hunting you know if you're consuming you have like a Sim
installed for example you're adjusting locks from all places you can easily correlate and see all right are any of these indicators combines that we're consuming from these feeds actually in our environment or have we ever observed them um again it's not as simple as I'm stating it but it at least provides you with a starting point um otherwise having a program like ours is you know not every member needs access to something like that because it's it's going to provide whoever's tasked with that responsibility with visibility into all these different types of external sources with just a few clicks of a button um so maybe considering a tool like that will will assist your team in uh getting
that visibility
a lot of questions oh that's a great question I'm gonna try and get this to you there you go uh so for so first off reporting law enforcement uh some cases we do actually report for law enforcement um uh again I used to work for them so we have contacts there but we actually have law enforcement using our tools um so that they get the visibility themselves and they can take whatever action they have they're using tools like ours to identify these sources and take down the sources like in the raid forms case whatever Credit Card Market is out there they're constantly taking them down and then more um you know different types of uh
criminal places like you know child exploitation human trafficking as well so law enforcement are using these tools themselves to identify these threats in alerting on them in general though um hour or you know uh the the doctor that the keynote speaker was talking about Ai and ml uh we're using our own as well to automatically correlate threats with your critical aspect critical assets that we've identified to alert you as soon as we collect it um which is the benefit of using a tool like ours rather than trying to manually do it alone great question hello with the marketplace is coming how are you identifying the marketplace great question I'm gonna try I hope I don't hit anybody
oh sorry about that that one there was no there was no spin to that one sorry about that if it went too far I'll get you another one
oh my God that one went real far so how do we identify these sources because they're constantly popping up new ones popping up um yeah these sources especially in the dark web are very volatile um and it takes one knowing where threat actors are navigating the most and communicating the most because you can monitor those sources to identify the links that they're sharing for a new Marketplace or new telegram group or whatever uh threat actors are sharing the places that they're going to and oftentimes these marketplaces or forums these new ones that pop up are promoting themselves on the sources that everybody's going to already um so that's how you would manually do it is by navigating it just kind of
trolling The Forum seeing where threat actors usually go into with our platform we actually which I'm grateful for because I don't have to do it anymore but we're actually automatically identifying those new sources we're able to identify the links that they share in these different places that threat actors and navigating to and actually deploy crawlers automatically to start collecting from it so we got that covered but you're able to do it yourself as well it just you know it takes timing and knowing where to to investigate over here
that's not an easy question to answer um but um you know I'm assuming uh you know you got multiple departments in Security in Telecom and whatever organization you are and you can kind of break it down by responsibilities for example the fraud team if you have a fraud team they can focus on uh threats that are targeting your customers um and identifying the types of threats that those customers are prone to and how they can better defend them whereas your your security team might focus on those internal assets the assets that your employees have access to and they just focus on those types of threats uh you have a vulnerability team they're responsible for identifying the
applications that you guys are running and the vulnerabilities that they might be prone to and then identifying what threat actors are actively targeting what new exploit kits are out there so breaking it up by section well I stay focused great question oh oh actually I hate I hate to be a Debbie down however it's it's the ghost of good questions present uh speakers take note apparently if you give out prizes you start getting questions let's get a round of applause for our speaker though