Going Undercover in the Underground - A Guide on How to Infiltrate and Engage - Michael-Angelo Zummo

Show transcript [en]
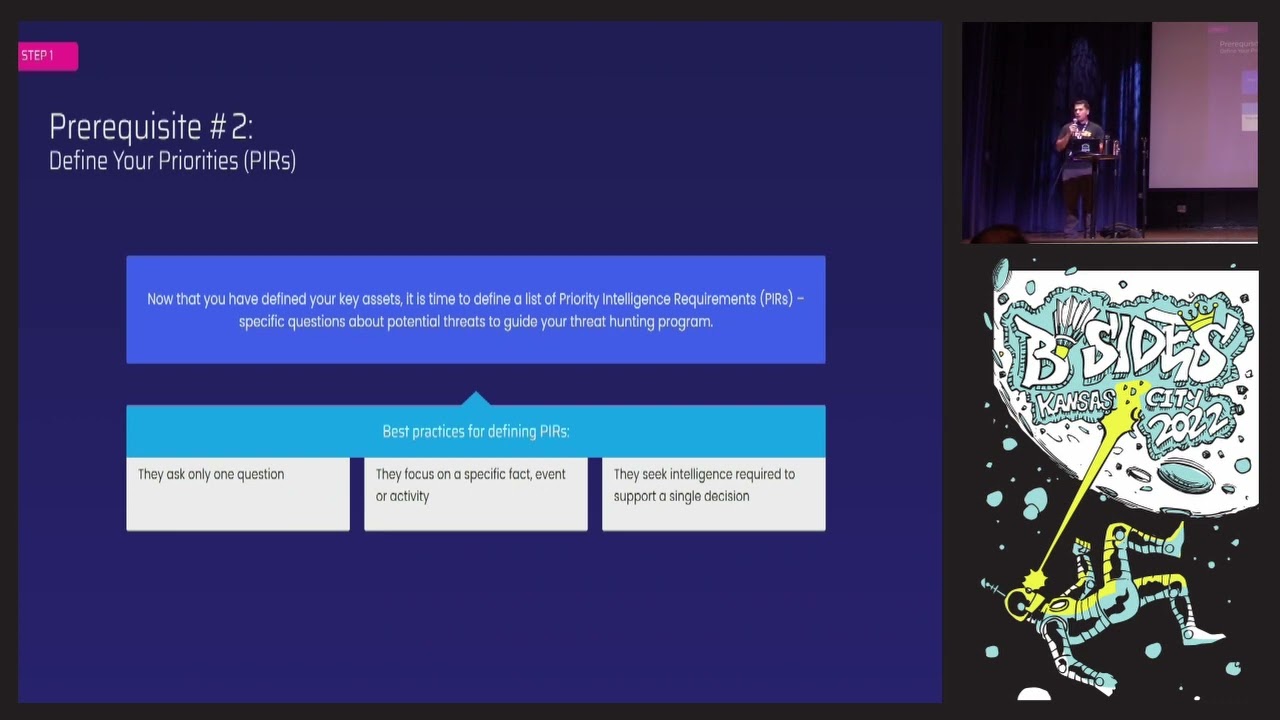
hey everybody thanks for having me back anyone who attend my talk last year here obviously Brad I got to thank Brad for introducing me to this great Community here other people there as well awesome thank you again for coming back uh I am Zumo uh I just go by Zumo I am the North America thread Intel manager at Cyber 6 Gill and last year I talked uh about threat hunting at this conference and how to uh Implement a thread hunting program a CTI program within your organization and one of the most common questions I got when we got into the dark web and stuff like that was well how do you get started in the dark web how do you safely access it and how do you engage with thread actors and start extracting Intel from there so that's what this talks about we're going to talk about everything from setting up your own dirty machine your own secured environment to start exploring the dark web and then of course we're going to talk about how to find sources on the dark web uh and as you'll see I actually just call the underground um and then once we've developed some sources that we we have interest in we're going to actually create our own Persona together and my goal is to give you all the steps today so that you could actually do this yourselves afterwards um but we're going to do so in a safe Manner and I have two rules is one don't become a perpetrator and two do not become a victim I have to say that or else the FBI might come knock to my door later so um and then once we create our personas we're going to actually show some examples of communicating with thread actors and some of the methods that we use and then we'll of course just like last year we'll do a little bit of a thread hunt at the end together so this is probably the only time I'm going to say dark web or the the last time I'll say dark web throughout this presentation I think everyone here probably has a good understanding of what the dark web is but basically anything that's not indexed by Google um you need a special browser to get access to it things like tour which is the onion on the bottom left for you i2p and then zeronet which is a little less popular these days but there are still some sources that are hosted there um but really I like to refer to it as the underground because many of you if you're in thread Intel or you do your own ENT knows that many of these sources aren't just exclusive to the dark web you can get to plenty sources just using Google you can get to you know find Intel on Reddit on Twitter ppins things like that um and then there's also messaging platforms like telegram which is ex you know huge platform now for threat actors for any type of use case uh for fraud terrorism narcotics even you could pretty much find a channel for anything on telegram because it's easy to use it's very accessible For Thread actors of all levels of sophistication no matter what kind of experience they have um so for the rest of this we're going to just talk about it as the underground places where threat actors engage with each other where they plan play and profit uh from their attacks and again my two rules are do not become a perpetrator and definitely do not become a victim that's part of the goal of this is to help you set up a secure environment so that you can actually do some of the activities that I engage in safely yourselves um as you'll see here as an example uh this forum might actually look familiar to some of you um if you know what it is just call it out um but many of the programs that you can click on or you know files that you can download from these sources are malicious so you might think you're downloading one thing for your research or for you know uh engineering or whatever and in fact you're downloading a hour into your own machine uh because thread actors are looking to take advantage of anybody they're not like friends with others on The Forum they will take advantage of anyone that's silly enough to you know click on links like this uh with their own machine so always set up a a dirty machine before you're going to explore some of these sources and definitely before you start clicking around on these sources now one of my preferred methods of exploring the dark web or the underground is by using a Tails machine Tails OS is a very lightweight that you could just flash onto a drive uh alls you need is like 8 gig 8 gigabyt of um storage and you can plug that drive into pretty much any machine and then boot up the Tails OS which is uh has Amnesia so every time you terminate that machine it's going to erase everything off of that drive uh it's not magic you still can't be logging into your Facebook or your bank accounts on it because if you're connecting that whatever your activity on that drive to your personal life then you know whatever activity you're engaging in it can be traced back to you so this is meant to disassociate everything from your personal machines from your personal profiles this is purely meant for your thread int tell investigations your dark web investigations stuff like that um I have a quick little video here for you to show you booting it up it's very lightweight and as you you can see here you can actually set persistent storage but if you set persistent storage you leaving more room for you to get compromised by thread actors in The Underground uh by the way you can get this from me afterwards so if you want to see these again I can send the slid so you can send me a message afterwards uh but that's it that's all it is there's a few programs on Tails uh it comes with uh tour installed so you can start navigating to those sources uh right from the beginning uh but again it's not magic you still need need to put in additional precautions in place and making sure that you're not connecting any of that activity you're you you're doing on tails with your personal uh self and we're going to go through those steps here now every time I do a video it the presentation messes up here we go all right so we have tail set up or you have a VM set up something like that some sort of secure environment where now you can go on tour and just start start looking around start trying to find sources start trying to follow thread actors and gain access to some of these sources um but there are a large variety of sources out there I come from military law enforcement background I spend a lot of my time developing my personas on narcotics forums marketplaces and things things like that taking down narcotics dealers you know serious ones like fentanyl dealers and things like that um but there are sources for whatever use case you're interested in for data leaks ransomware malware um again narcotics fraud anything like that you can find a source hosted on the dark web or again just a clear web Source or a chat group somewhere on Discord for example um I have some examples here of these sources cracks which we'll talk a little bit more uh in in the next few slides it's just a clear web Source you can it's cracks. proo or something like that um you can find it on Google and anybody could register for it it's not very difficult but there is very sensitive data on this type of source you can find leak data for major Enterprises you can find vulnerability information malicious programs people trying to hack their ex-girlfriend's Facebooks accounts whatever it is is you can find it on fors that all look relatively the same these look probably very similar to sources that you might uh go to for your own Hobbies like a biking form or something like that that's all this is then you have credit card markets fraud is one of the number one um use cases that we're extracting Intel from in all of our organizations uh especially in law enforcement uh but there are plenty of sources that are just dedicated fraud markets where you can purchase anybody's compromised payment card um these you know they're listing thousands of payment cards a day uh and you can buy somebody's account for as little as a dollar and start using their credit card information to commit fraud then we have your miscellaneous markets your drug markets which is again where I spent a lot of my time uh back in the Silk Road days uh but this one you can see here which is known as dark Fox is a source where you could buy anything from narcotics to pornography to even just legitimate stuff um it's a site like an Amazon where it just hosts vendors that could sell whatever they want anonymously um but but there are plenty of markets like this this is just one of those [Music] examples Russian Market H how how many people are familiar Russian Market couple of hands there this is what we call an initial access broker probably for anybody in Intel in this uh that is here today uh this is probably one of your biggest pains in the asses that you're hearing about every single day compromised access for sale on the dark web this is probably the notorious Market there was many others like it but this is definitely the most popular one where you can just simply go in and buy an account to pretty much any domain you can think of um they're they're available every single day for again as little as a dollar and we'll talk more about this when we get into the thread hunting later on and then lastly telegram as I mentioned earlier you can find a telegram channel for anything whether it's fraud uh narcotics leaks malicious programs gaming uh again whatever hobby fishing whatever you want you can connect with people around the world uh and it's so popular with thread actors because of how easy it is to use and how accessible it is um so this is one of those places that we're constantly finding access to and engaging with thread actors and communicating with them after we've connected with them on a forum somewhere now when it comes to dark web sources there's a bit of a challenge here one most sources you know the popular ones you could probably find pretty easily these days um but most sources are pretty difficult to find and that there's a reason for that people are trying to remain anonymous right um and you actually need the whole onion link which is that link highlighted here a little difficult to see for you guys but again you can get these slides from me afterwards and I think it's being recorded as well um but you need the actual onion link or one of the mirrors to get to these sources you can't just Google you know CP BB uh and you know get a result where you could just log in you need that link there's different ways to find those links I'll show you one in a few slides um but there are some sources that will host links to these uh to these dark websites or these onion links typically though uh these sources are look normally listing drug sites it's one of the most popular reasons why threat actors or people in general are going to the dark web is to buy drugs uh it's very easy to buy drugs on the dark web that's why I had a job in law enforcement for so long um but there are sources like the hidden wiki Shadow Wiki dark eye Darkness live many others as well um constantly coming up and you know often times going down as well that will host these links where you can simply just click on it or you know see the mirrors for those sources uh and then start you know exploring these sources but again lar they're mostly for Narcotics sites or fraud sites you you'll often see those sites that we TP we typically use for threat Intel leak sites ransomware sites things like that usually it's a little bit more difficult to find those links but if you're going deep enough into Reddit or you go on Twitter or you're active on another source maybe not a dark web Source but some other Forum you'll have an easier time of finding these these links uh to these sources as you can see here this is an example where often times thread actors on just a normal clear web Source will advertise another source that they're active on or in this case this thread actor was adver ad vertising their own telegram Channel where they were uh posting uh data leaks and um combos for uh credential stuffers and things like that so oftentimes you just need to participate on some of these forums and stay up to date on the post to find links like this to find oh here's another source that thread actors are frequenting uh pretty often now often times finding the sour is not enough you have to register for them right and this is why Persona management is so important because we're not going to register for uh malicious source with our Gmail right we we can't be letting these threat actors know who we are one most of the time they don't care who you are uh but they will ban you uh if they don't think you're contributing to the source uh but you know worse they could actually Target you so registering the to to these sources can be pretty difficult especially because many of them require invites or access codes things like that Genesis was one of those competing initial access Brokers probably one of the first ones uh before Russian Market came online uh I was particularly proud of this one because I was one of the first people one of the first thread Intel people in this Source uh and this was a source where again you needed to know the admin to get an invite or you needed to pay a significant fee uh to get access too I uh having my all my personas from law enforcement got into this one pretty quickly and then was able to make a bunch of burner accounts just in case that one got uh banned Forum ramp which is a Chinese and Russian speaking form primarily although they mostly speak English on the source is another example of a dark web Forum where you need to again know the admin or in most cases actually just pay the fee uh quick note for any thread Intel analysts or thread Hunters that do this manually never use your own funds to pay to get access to these sources you will get burned we've been burned before I've been burned before uh where you pay a fee and then you never get your access or you know you get scammed or something like that so never use your own sources make your companies pay for that and then back to cracks Pro which uh is a pretty easy source to get registered for but in this the issue with this source is you need to actually participate or contribute to the Forum now again my first rule is do not become a perpetrator so we're not going to engage in criminal activity right um FBI has some pretty good guidelines of what you're allowed to do what are gray areas and what you should not do at all um but this Source you need to actually participate to be able to get access to everybody else's post um a cck quick little tip thread actors like to know what's going on in the world so an easy way to get around this is just share articles you can go on a source and you know ceso comes in you know screaming about some new vulnerability that's being reported on you could simply just share the CNN link about that um vulnerability and uh that's usually good enough for these admins on these sources uh you have to post it in the right section they are pretty uh picky about where you post information they don't want you to be on like the leak girlfriend's Facebook Tab and you're posting vulnerability stuff um but it's usually good enough for you to get around these requirements so that you can actually see uh what other people are posting and trying to extract whatever Intel you're looking for the next obstacle which is becoming a bit of an easier obstacle to hurdle over uh are language barriers many of these sources um most some of the most sophisticated threat actors in the world are Russian Chinese uh but that's not it you know there's German Italian uh you know Arabic plenty of other languages out there that are using the underground to engage in malicious activity again I was a Korean linguist in the military unfortunately Koreans don't like to use the dark web at all so I don't really get to have any fun with that or practice Korean anymore um I have to do it legitimately but um you can find pretty much any language or dedicated source for that region of thread actor in the underground and that's one of the barriers that you're going to have to deal with or obstacles you're going to have to deal with because not everybody targeting your company speaks English right uh they are speaking many other languages and you need to be able to to see that to be able to identify the threats that uh your organization might have and then there's also VIP sections anyone familiar with raid forms one two couple rest in peace um raid forms went down was taken down by law enforcement I guess probably a year and a half ago now or something like that couple have taken its place um was a form that was around for a really long time um and I was sad because I had personas on that form that were just specific to that form that I can't really use anymore um but there was an example of a forum where just gaining access wasn't enough you need to also again particip in the form or no sophisticated threat actors on that site or significant threat actors to actually get access to the VIP section or you could just pay your way too um but there are many sources like this where they'll have VIP sections where the you know the most precious Intel for us is actually located um so when as you're exploring these sources is something to keep note of if there are locked areas of that form uh where it's just typically where you're trying to get your Intel from so we've set up our our dirty machine in this case I'm using Tails now again tails is very good for your just one-off investigations if it's something you're looking to automate then you're going to have to look into other methods like a VM uh a dedicated VM that you can set up um tails is not really meant for that it's you know it was really meant for journalists and people Behind Enemy Lines being able to communic what's going on without risking themselves um uh but whatever method you have as long as you have some sort of secure environment that you've set up and now you've identified some sources that you want to get access to we need to actually create our own Persona and for our Persona I actually modeled off of a thread actor I have many personas but for this example I created a brand new one just so that you guys can learn from this uh and you can learn from the requirements that I built here for this persona but you all you need to really do is model it after any other thread actor that you see on these sources you know the best ones aren't you know the most popular thread actors but the ones that are using the most uh forms of communication or are active on a multiple sources so that you can kind of blend in and model after them so some of the requirements that you're going to use are a burner email in this case I just use proton mail it's usually my go to uh you're definitely not going to use Gmail or anything like that that requires you to verify who you are um a password manager I almost hesitate telling you this because I believe the best way to learn things is through pain I still try and do that um but if you don't use a password manager you risk uh logging into a site that is no longer legitimate uh and then you lose access to all your other personas so don't do that use a password manager and do not reuse pass passwords um make sure your persona is completely isolated from the real you because we're again we're not going to become a victim right and then we're going to use other uh communication methods like pgp which I'll show you an example of jabber telegram uh and then one other which we'll go through so this is pitiful this is me you could find you can actually find pitiful uh and a challenge that you could do if you follow these steps afterwards is actually try and contact me you could contact me at proton at pitiful proton the L's in full are ones just uh FYI you can find me on jab