Next Stop: The Cybersecurity Zone by Jeremy Rasmussen & Michael Mallen

Show transcript [en]
So yeah, here's our uh AI augmented uh pictures. Hope you like those. Um we've never looked so good, but uh yeah, we this will be different a little bit than other talks we've given in past years. I think this is my eighth besides Tampa talk. Um, some have been on, you know, postquantum cryptography or hacking AI. This one's more of a thought experiment. We were like, what are some horror scenarios of supply chain disruption that we could conceive? And so, we're going to have today three little episodes, but before we get to that, a little disclaimer. Yeah. Yeah. And we wanted to put this disclaimer up there just because everything that we're going to kind of put together situationally,
it's just going to be all hypothetical. We will name some companies in these situations. We're not calling anybody out or or doing anything crazy like that. Just want to put that up there. Nothing against Microsoft and CrowdStrike and all the other people. You guys are doing a great job. So, just so you know, you know, Michael, not all monsters are otherworldly, but might dwell in the hearts of man. You're not going to do that the entire talk, are you? The whole try to channel my early my inner Rod Serling, but no. Yeah, I'm not going to do that the whole time. Um, yeah. So what we're going to do is um talk to you about what is where
do we find ourselves these days in terms of software supply chain hardware supply chain. Um we're going to look over an archive of the last five years. There's essentially been a massive supply chain disruption each of the last five years. So this is certain to continue in the future. And then we're going to give you three nightmare scenarios. But we're not going to leave you hopeless. We're going to hopefully like give you some ideas about how that maybe we can avoid these things and then some wrap up with some final thoughts. Yeah. So, we'll start with kind of uh setting up the new normal, right? I mean, everybody's enterprise, every every place you work at, we're going to
have some form of a a supply chain uh you know element to that, right? So imagine your your global enterprise, whatever company you're working for, it's humming along smoothly. Um, but it's powered by code that it didn't write and dependencies that it didn't go through and properly vet. Um, and you know, firmware that it's not even thought about. It's not even categorized. Now imagine what happens when that trust is shattered, right? So think about the supply chain and uh what a vulnerability that can potentially be. You know that where all this comes from, right? um we don't want to keep reinventing the wheel. As Marcus said, he g he just gave a prompt to an AI
engine and it spit out code for him. So that's one scenario is you don't even know the the provenence or where that code came from. Another one is we have code that we don't want to keep writing. So we create these libraries and there's these people out there who have um you've seen this XKCD comic before. They're are keepers of this code. So, a group of developers got together and some guy in Nebraska has been has been uh the open- source lead on that code for that library since 2003. Um, he's getting ready to retire next year and we don't know what's going to happen after that. But guess what? Um, his like compression library for Linux is the one
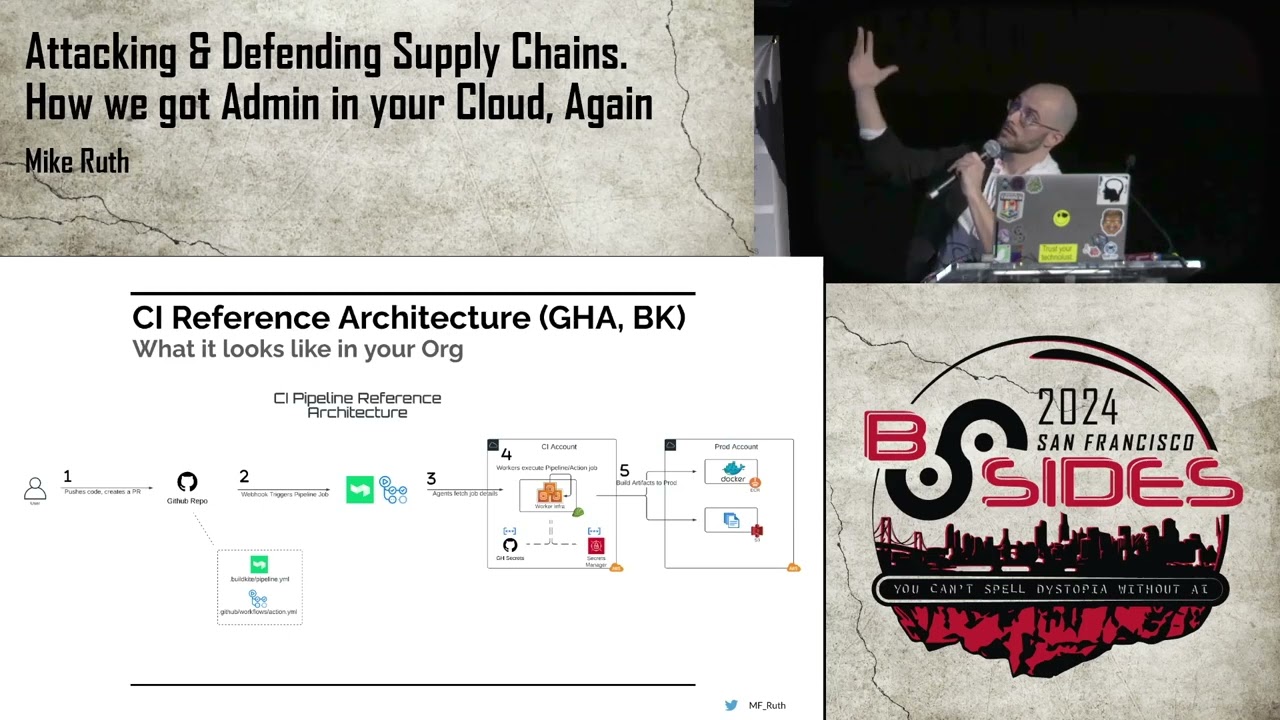
everybody in the world uses. And so, um, yeah, we've got this issue. Yeah. And I mean the supply chain is is many many moving parts right I mean your software components right so that's everything like you mentioned like your open source packages uh npm github libraries that people are pulling off the internet uh all your proprietary code from your vendors right so everybody kind of interfaces with vendors for different things um your anti virus edr whatever all your enterprise apps are uh technically thirdparty and then you know your APIs SDKs all these things you have to kind of categorize right and of course like your devops dev secc ops departments, your build and delivery infrastructure,
um CI/CD pipelines, um things like this, uh compilers, libraries, uh all the different tools that you're using to build your software in your company, um can come from an external third party. Um you know, your package repositories and all those different things. What happens every time you rebuild something? What right? And what happens always? It breaks. Why does it break? Dependencies. Uh you are using some legacy library. It's no longer compatible with the new one. So you got to put in a patch and then that patch has to work and then it has to be regression tested, right? So every single time you're even putting out a build, you're at risk for a disruption. But what if we're we could come up with
some scenarios at the global scale? Yeah. So each of these elements um you know we're talking about the supply chain. It introduces a uh inherited trust, right? You're going to rely on them. Your entire company, your production is all going to rely on them being secure even though you weren't involved with uh building that software or whatever uh vendor materials directly, right? or or you also don't control them right from a security uh standard, right? So any breach in any part of that supply chain is going to have cascading effects, right? your development environments, production systems, and not only your organization if there's a compromise, but like let's say all of your downstream c customers
as well, which you know we've seen that in the news recently and AI only exacerbates the problem because some like right now something like 30% of all code is automatically generated and nobody even is even laying eyes on it. Back in the day, we used to have something called extreme programming or parish programming where like there would be two people really at a keyboard side by side, one writing and one like peer reviewing. It's kind of the new normal that you have a a generative AI solution doing that and um writing that code. But the per the only thing is the humans not really even looking at the code. So it's just getting generated but
with no review. So what does it really do? Yeah. So, as I said, the archive of oops here, um, it kind of started a few years back with, um, December of 2020 when you had the Solar Winds attack. This is, um, came to light when Mandant and Fire Eye figured out that somebody had invaded their system. When they were doing the forensic analysis, they tried to figure out how it happened and they realized it was through an actual signed update for the Orion software from Solar Winds. Solar Winds being a network health and status monitoring software software that was used by like some 80,000 customers around the world. 18,500 of the customers had downloaded this signed,
you know, seemingly authentic and trustworthy um update, but it contained a remote access Trojan back door. Uh we think the Russians are probably the ones who did it. It was pretty pretty uh boss how they got in there. They actually invaded the DevOps environment. They were able to insert their code. What was some of the things they did like uh even suppressed compiler warnings. They they were they had a a trigger whenever like Visual Studio launched, they would they would go, you know, go dormant. Yeah. And they also had uh they did a test run in October uh the year prior. They just put benign code in there just to see if anybody would detect it during their
build process and it went completely undetected, you know, so they knew they had a method there for that for their big um implant deployment. And why like even today they don't really know exactly how the what the initial infection vector was or how it spread. Why don't they know? Anybody have a guess on that? Because the attackers deleted all the logs. So they have no they have no audit trail of of exactly what happened. So that was the first that's uh right that's red teaming 101 counter forensics cover your tracks. Um in 2021 uh CASSA um I think was it was it Reval R Evil? I think it's R Evil. Yeah. Took over um their uh remote
access software which is used to by MSPs managed service providers to uh manage the IT of other companies. So you can imagine the widespread attack here where your trusted service provider is now compromised and then they're using its tools to get into all of its customers. So that was a bad one. in 2022 um somebody I think uh what are they social engineer the service desk for uh octa and were able to get um access and I remember octa downplaying this quite a bit at the time but they later admitted that the devel that the uh attackers had ex um access to their entire GitHub like software repository so that was a bad one um move it you anybody heard of that
one and you're still going to hear about it for years to come. By the way, 2023, a lot of government organizations, a lot of companies were using Move It, which is a large file transfer facility. That was backward. Who was the ransomware group or the attacker group on that one? Uh Move It was KOP with a zero. And like I said, we're still hearing the fallout from that. Um last year there was a guy uh an independent contractor doing some testing with a compression utility in Linux called XZ utles and he found it was it was there's a lot of latency. Something was happening. It was taking longer to do its work than it should
have been. when he started looking into it, he realized there was this back door where it was like trying to create an SSH, you know, shell and um maybe move something off to China. And upon further investigation, they realized somebody had joined the open-source development group, had established trust with the developer group, and had inserted this uh improperly into the build. Pretty crazy. And then I brought a prop for this one. Anybody know what this is? Yeah. So, two days ago I was in London trying to buy a sandwich at M&S Marks and Stern, which is like their Publix, and I couldn't get one um because uh they've been down since Easter. No food on the shelves. Um no no online
orders. It's like the biggest grocery store. Now, now you're not just talking, you know, a computer outage. You're talking no food. Okay, so this is this stuff is crazy. It's real and it's just going to continue in the future. I lost my clicker. Thank you. So, let's look into some of these terrifying scenarios. This is this is a Twilight Zone uh what do they call it? Limited miniseries of three episodes. The first one is well before we get into that let me set set the stage by saying every system we have now has like kind of pre-installed trust um young young people in the audience. How do you get that little gold lock on your browser?
Right? Anybody know where that comes from? What does that represent? Theoretically it represents that you have this secure communications channel between the uh client and the server. But where how do we get there? Well, the ser the web server had to serve up a uh certificate to the client who had a pre-installed certificate in this browser, a way to trust through that a certificate authority that issued the certificate to sign that communication. Well, how did you decide if it if you trusted or not? You didn't have any choice. It just came that way. The browser came that way. Your software came that way. You bought the operating system. You have inherited trust. And so imagine if somebody
assales that trust. Yeah. So this is the first one and and again we're trying to go worst case worst case scenario here on all these like what's the worst supply chain thing that could happen and again just kind of as a thought experiment. The first one here we'll call it the trusted route of all evil. Right? So what if uh Microsoft's code signing uh infrastructure got compromised? Right? What if it fell into the hands of an AP? You know, the most most trusted seal on earth, Microsoft's code signature. What if they uh back doorored that and were able to control it? You didn't install malware. You installed a sign driver from Microsoft. At least that's what
your system believed. Yeah. So um for years now they've been trying to shore up security around say uh kernel zero or you know root root level drivers by having them signed by Microsoft. So now they just go in basically no questions asked. You don't even get a prompt you know complete bypass. So if somebody got access to that root level certificate all hell's going to break loose. Here's what's going to happen. Yeah. So kind of what's the fallout look like realistically with that right? So if that happened let's say hypothetically Microsoft's digital digital signatures are universally trusted right they own the market share of the entire of the entire world basically right um you know
if an attacker can produce authentic Microsoft signed binaries then edrs all your anti virus Windows updates um office updates are just going to sail in with no checking and they're going to contain back doors and malware yeah zero warnings right So all of your um things that rely on signature validation, right? Your smart screen, app locker, device guard, all of that, all of that uh layer of control um it's going to be bypassed, right? Essentially, and you know, malware signed with Microsoft certificates. We've seen kind of instances of this in the past where someone's trying to forge a certificate, but they can masquerade as legitimate Windows updates like you said or or Office patches, right? And again the
reason why this one is is really bad because of how widespread Microsoft is as far as like the market share right that's a de facto office solution application for the whole world right yeah so imagine if u in visual studio in the software development kit somebody backd doorors that then every application you make with visual studio is then backdoored as well it's uh I think was it Ken Thompson it was a Thompson issue that he brought up in a uh ACM M talk from 1980 where he said if somebody actually like um inserted code or a bug into a compiler then every single application that was ever compiled off that code could be backdoored and you wouldn't be able to
know it because you didn't have you know you don't have access to the compiler code and it's this the same situation a Thompson issue. So there this is going to affect us not only at the enterprise level but at the national security level and even the global level right. Yeah. And and again looking at re some of the real world example examples that we did here like what would actually happen there from you know some of the primary things uh as far as like uh you know impact right so enterprise every enterprise all their defenses are kind of out the window right um like you mentioned all those payloads would just get past EDR no
problem. Incident response teams would just be uh I mean 247, right? John Hammond would be working late that night. Um widespread supply chain uh infections, right? Uh developers don't really know who to trust. Um all of the uh signed malware is just getting redistributed because it's coming from a trusted source. from a national security perspective and again realistically if you wanted to try to look at this in a threat modeling perspective is like somebody would do this to get into the government or or national security uh targets right government systems using those Microsoft uh signed drivers that are compromised um they're going to be breached silently right and that's what they're trying to aim to do is is
persist in the networks undetected does anybody remember code red nimda sad find confficker. What are those worms? Okay, how does a worm work? A worm finds a common vulnerability uh across all systems and then uses that to exploit and and propagate, right? So now they have root root trust. Guess how widespread and how worldwide that worm is going to be. It's nightmarish, right? Yeah. As soon as you get to like a warmable situation, think like Stuckset or or Want to Cry. Um, anything with that, that's going to be a just shut everything down sort of situation. And trust in Microsoft is going to erode too. And we've got some other examples we'll go over here later in the talk,
but we've seen vendors uh trust just be completely kind of washed out because they made a mistake whether it's security related or not. Um, you know, and they've they've caused a lot of people a lot of issues, right? There's always that catch 22 like Microsoft will sell you everything you want in your license, right? They'll they'll be your SIM, your EDR, your uh identity and access management, everything. But then you're all you're also putting all your eggs in that single basket. So you can imagine the fallout from this is, you know, a revocation storm, a tsunami, I guess, a revocation tsunami of certificates, right? Every single certificate is going to have to be revoked. They're going to have to
regenerate those certificate authorities. All the intermediate ones that that that are based on uh trust up to the root are going to have to be completely rebuilt. Um as you mentioned, massive incident response, probably years worth. Yep. Um and then downtime. What does that mean? Well, Splunk just put out a report that says even like a slight disruption in service level agreements, SLAs's or customer experience is downtime. And a single downtime event can make your your stock go down by like 4%. Oh, by the way, the uh the M&S uh food store in in uh London, their stock went down by a billion dollars. Uh and only a billion. Yeah. And and they also had a hund00 million insurance
claim so far on the thing. Um so across glo global enterprises, they're saying the annual cost of downtime is over $400 billion already. And imagine what it would be with with this. Yeah, it uh people start listening when you start talking about billions of dollars uh you know as as the outcome of some of these things. But um you know when we were trying to develop this talk I was kind of talking to different people about like these these scenarios. I'm like yeah that would absolutely never happen. Well right we've got too many safeguards in place there. There's no way. There's really no way that could you know logistically happen. Well, we've seen kind of good examples of this uh
throughout history, right? I don't think we've seen the big one yet. Um Stuckset, they've used stolen certificates for their stuff. Um Microsoft's, not Microsoft, but but Real Tech uh and J Microns. Um the Shadow Pad and C Cleaner one, there was an incident with them where they had legitimate certificates used to sign malware, remember where, you know, CER was completely off the table uh for usage for a while. the Solar Winds incident is always going to come up when we're talking about supply chains, right? Um they use back doors to get in undetected. Um and and Microsoft again they had signing keys stolen very recent. The Chinese Yeah. took their Azure signing keys which were inter
intermediate level but still it showed kind of maybe a proof of concept of what could be. So this stuff is real. Don't think it's not real. It could happen. The good news is we're not just going to leave you there to languish like we've got some ideas. um you've seen what could be. What can we do now do to prevent it? Obviously software build materials um is anybody familiar with that term? Anybody building software? You're understanding the uh the software supply chain who's depending on what where the um where the libraries coming from, what versions are they? Making sure you're not using vulnerable libraries that you're not using outofdate libraries. um making sure that you have kind of a like whenever we do
any kind of assessment on any system what's the first thing you need to do is understand what the system is right under understanding all the hardware and software of that system imagine in the past the not too re you know not too distant past that we didn't nobody even knew what was in their software right they didn't have a sbomb and so having your arms around the of what's in your actual build is super important to be able to protect it what's other isolation, right? Uh part of zero trust is um segmenting off your important things from each other. You guys have heard of zero trust architecture, right? So um identity and access management everywhere, continuous monitoring
everywhere and isolating your important stuff. So even if somebody can get into one thing, they can't get into the other. I've seen you've pinested a lot of systems. How many systems is dev and prod the same system? They're almost integrated everywhere and they're they're always overprivileged because sorry dev guys, you know, they they need admin. It makes it easier. Yeah. So you pivot in through the dev environment and you can you have a one-way path over the prods. Third party vendor risk management is another thing. Are you making sure that your suppliers are doing everything they're supposed to be doing just like you're like you're doing it. You're holding yourself up to a standard. How can you hold their feet to
the fire too to make sure that they have lower risk? So there's methods you can do to get surveys from them, questionnaires, do risk analysis, um do external, you know, scans. Uh it would be great if you could actually put a like some kind of agent on their environment to be able to monitor what's going on. That would be that would be a deep level of trust. I don't know if they're going to allow that, but that would be the ideal, right? And of course, frequent threat modeling. Uh has anybody heard of Stride, the Stride model? Go look up Adam Shawstack and Stride. It's a threat modeling approach. Anybody that's trying to do um an
environment uh security scenario has to use Stride to address confidentiality, integrity availability authentication access control, non-repudiation, all the things you need to go into a secure build. All right, let's get some more horror stories out of the way. Yeah. So, this one um the idea for this one came from an incident that happened last year, which we'll cover a little bit during this July 19th. I remember well, PSD day. I think the collective community was just like, "Oh that could have been a lot worse." But, uh, this one, um, so we're talking about CrowdStrike. Everybody's heard of Crowd Strike. Probably one of the best, uh, EDR, XDR kind of product out there. Um, I do a lot of red teaming. I do a lot of
pen testing and you know they always give us a lot of trouble on the endpoint, right? Um so we did we did a talk on the Conti ransomware group about three or four years ago and we found out that they were trying to buy CrowdStrike through a a third party, right? Because we were like either they're trying to test it to see if they could bypass it, but more likely it's the only one they trusted to actually work to secure their stuff. Yeah. So yeah, it's very good. But uh let's say in this scenario that CrowdStrike's internal systems, more specifically their management, like their cloud infrastructure, uh are compromised by an AP, right? This would
have to be a pretty uh sophisticated group to do this. Um but let's say they've got a multi-stage campaign put together. They get in there and they they set up shop. Uh and that attacker gains access to basically what is a command and control infrastructure. If anybody's ever managed an EDR or anything like that, it's basically just a C2. Um, you know, so you can execute code from CrowdStrike in the in the management console. You can um, you know, potentially shut down machines. You can do a lot of different things. Um, so again, the idea for this one came from that incident and then as well as, okay, if I was a real, you know, let's
say Russian SVR operator, what would I want to hit in America to get, you know, uh, on that level? Um, so imagine at the very eye that watches over millions of endpoints suddenly turned inward and blinked very Twilight Zone. So with kernel mode access, they obviously can inject uh commands, exfiltrate data. The scariest part of this one is um you think somebody's watching, but they're not, right? Because the EDR is falsifying information that's going to the sock to the security operations center. So any kind of telemetry and log forwarding has been disabled. Um any kind of indicators of compromise. I know as a red teamer you you've probably done this before, right Mike? Uh if you want
your code to execute you put it in the execution path of the EDR because EDR always excludes itself. So just drop your app your application malware in there. So in the same it would be just like that because now the uh the EDR itself is compromised. So, it's not going to, you know, report anything bad that it's doing. Or we've gotten into SIMs before in some organizations where, yeah, we've compromised your SIM. All of this initial access uh box that we're working off of, we're just going to go ahead and mute those alerts for a little while so your team won't see them. Does it does remind me of a story of a prominent hospital system that we
redteamed where um they were using a secrets vault, right? a privilege access management vault, but they didn't have multiffactor authentication on that PAM. Yep. And so you were able to crack the password and then get into their secrets vault and then they were literally sitting inside of the SIM watching everything that the SIM watchers were supposed to be watching them do. But run that command and then go check the SIM, make sure it didn't alert. So that's what can happen. Same situation definitely. All right. So with bad falcon, dirty falcon, um yeah, again, massive global incident response effort, um potentially maintaining access for years undetected. Um unless somebody like a, you know, a mandatory or whatever figures this out quickly
and, you know, eradicates it, there's going to be like global, legal, and geopolitical ramifications, right? It's going to be cyber war 100%. And and the one thing that we do see, especially with that incident that happened last year with them, not security related, it was patch related, but they they kind of lost a little bit of trust in the market share, self-imposed DOS. Yeah. And you saw the news that came out with that. Um I I got on the plane to come here uh a couple days ago and I saw one of the Delta computers and it had the little Sentinel One icon on the bottom. So they switched off a crowd talk after that. So
yeah, Delta has a $500 million lawsuit pending against Crowdstrike. I believe only that only that much. Yeah. Could this happen? For sure. Yeah. Like we were saying, um, it did happen in a way like it wasn't an attack per se, but a lot of people at that time were asking, hey, does does Crowd Strike really need Ring Zero access? And because of because of that level of access, you could insert a kernel mode rootkit which would be undetectable forever because the operating system it could just forge results going back to the OS and like say it didn't exist or that this, you know, if the operating system were expecting this file to be a certain size, it would just forge the
results back saying it's it is that size even though it had a Trojan in it. We've seen it before, right? All the time. And um Kasperski, he actually told me this yesterday. Uh you want to talk about shadow brokers and Kasperski? You didn't you didn't believe me on that one? I did not. But um here's how I understand the whole shadow brokers thing having fall having shaken out is that there was an NSA contractor who took some of their proprietary pin testing tools home, had them on his or her laptop, and they were running Kasperski antivirus or EDR. And that thing popped um an Eternal Blue alert for the CVE, you know, for eternal blue that went back to the mother ship
and somehow the Russian intelligence agency FSB got involved and was able to come in and rip all those files which somehow which Right. Right. And now Kasperski obviously, you know, vehemently denies this, but the fallout is they they can't do business with the US government anymore ever. And so um yeah, this stuff can happen. Loss of trust. Yeah. And again, Solar Winds is always going to come up in these in these scenarios, right? I mean, a network monitoring solution like Solar Winds is going to give you all types of access to everything. And then uh Code CV and CircleCI, that was an interesting one. Those are what continuous uh integration, continuous deployment solutions, right? Yeah. Somebody uh
basically compromised their their Docker build infrastructure and was able to backdoor everything and you know get access to all their systems. So good news is we have some ideas. All right. So obviously building in automated security testing is important. I'm telling you when I was I I was teaching at USF for about 22 years. I could count on like one finger the number of software security like software testing classes they had. Now I think they do have some as part of their regular curriculum now. But teaching like first of all just teaching developers OASP top 10 and and and baking that stuff into your code is super important. But then also um you know doing this automated
testing every time you're you're checking in a build there's got to be that peer review both from you know human eyes and AI eyes on glass dependency audits we were already talking about that's part of the whole sbomb thing reproducible builds the idea there is if you have two what you consider to be identical builds and they compile they should be the identical uh binary but with the Solar Winds case you're saying the attacker was putting in benign code just to to test it and see if they could get past the filters, which they were able to. Yeah, that's that's a big kind of uh uh setback from them on that is they actually tried to
test it and they put in benign code to see if anybody would see it and this was directly after like the the compilation process before they pushed it. So you know so not only static code analysis but also dynamic and behavioral code analysis, fuzz testing, extremities testing, uh making sure that it's performing as uh as inspected. And then of course thread intelligence sharing. This is a hard one because you know obviously Microsoft and CrowdStrike and Sentinel One are not buddies but as frenemies they should be able to share threat intelligence information in a secure forum so they can try to help their customers overall. Speed up here a little bit I think. How are we doing on
time there Shanz? All right scenario number three hit it. So this one came from the idea which I think is brilliant. Uh, did anybody hear about the beepers from the MSAD that they sent to the Hamas guys? They put explosives and beepers at manu manufacturing allegedly. Allegedly. And uh, you know, they're able to kind of trigger those remotely and and blow stuff up. Um, thinking about that from like a hardware perspective, what happens if a breach occurs like at the manufacturing stage? We've seen a couple instances of this in the real world, but let's say an AP infiltrates the firmware supply chain of, you know, whatever a major hardware vendor and then the the motherboard manufacturer uh server
suppliers and OEM firmware um uh gets compromised, right? Um the silicon sleeper. Anyone here of Spectre and Meltdown? Those were uh chip level vulnerabilities that were discovered a few years ago where people figured out um so to to speed up everything on a chip, you prefetch instructions um and you have those uh cached but if somebody could glitch the circuit or or clear the cache um getting the instructions rewritten, they could infer what what the instruction was by this timing of it. So it's a side channel attack putting a a probe on a circuit and then watching how the circuit behaves. Well, silicon was thought to be the last bastion of secrets, right? You can hide, oh, I can hide our keys deep
in that silicon. Well, now not so much because people have this side channel attack and can read what's going on. That's just a a glimpse that was a feature, you know, a feature um from Intel and AMD. But you can imagine if somebody was a malicious actor and were able to insert themselves into the build process, what they could do. Yeah. And this is um kind of going through this research, this is probably the worst type of thing that can happen um from a detection standpoint. And then from a uh you know long-term capability for a thread actor, right? So they're going to be able to scrape uh encryption keys and passwords at boot. Um they're
going to be able to inject malware into memory before the the kernel even loads. um they're going to be able to man manipulate your entire trusted platform modules um you know at that level or uh at secure boot to fake system integrity. So this one's going to be this one's going to be pretty bad if this actually happens at scale
04. Oh my golly. Yeah. So here's the thing. Uh when you're doing your patching cycle, most companies are looking at desktop software and Windows updates. They don't even think about stuff like virtualization software, network infrastructure, firewall updates, firmware updates, printers, phones, right? All that stuff. And so it's just not even on the list. And so all this stuff goes by undetected potentially for years. Oh, another place where you see um firmware like never updated. Anybody in healthcare, right? Your MRI machine, it costs, you know, $50,000 every time the tech sets foot on the property. And so a lot of times that that that firmware will just just sit around un undated for about 10 years. Even we could you can conceive of
something in a skiff, an airgapped system with an implant in it could just be sitting dormant for years. And as soon as it like gets decommissioned or somebody plugs it in, guess what? wakes up. You get a call back at your desk in the PLA in China. Yeah. So, this is going to be a heavy lift for everybody, right? Uh the the vendor must recall millions of devices if this ever gets discovered, right? Most important stuff, right? Data center, hospitals, uh SCADA systems, um all of that stuff has to scramble to get this done, right? Supply chains are going to completely halt, right? Um, you know, all of the major chip manufacturers uh Intel AMD Dell
Super Micro, you thought Huawei wasn't trusted. Huawei, Lenovo, all that stuff is all broken. All the trust is all broken. And, uh, basically it's going to get into kind of like a probably a cyber cold war scenario where, you know, we're going to try to do attribution. We're going to point to your, you know, your regular players, you know, China, Russia, North Korea. Another good reason to bring production back to the States. Yeah, this is not we're not just making this stuff up. This is uh real um so couple years ago, I say about eight years ago, I was at a conference and happened to have dinner with a guy who was CISO of RSA at the time. After a
couple bottles of wine, he loosened up to tell a few stories and I got the 411 on this. They were actually they're actually Chinese threat conference and happened to have dinner with the guy who was CISO of RSA at the time and after a couple of bottles of wine he loosened up to tell a few stories and I got the 411 on this. They were actually they're actually Chinese threat actors in their foundry in China trying to implant back doors in their secure RSID tokens. Okay. In addition to all the other stuff that they were going through. What else? Yeah, this one here, the NSA Ant. Um, so this kind of came out of the
shadow brokers thing. They called it DD bounce. Um, so basically you can do software application persistence on Dell Power Edge servers by exploiting the motherboard BIOS. Um, you know, system management mode. Um, so again, kind of that same sort of stealthy scenario that they were uh using for persistence. And again, disclaimer here because the the super micro one was never proven out, but it certainly did wake everybody up to the fact that these, you know, hardware supply chain issues could be an issue. Yeah, the the lowjax one um it was also a rootkit that's out there in the wild uh that could be loaded with uh UF UEFI firmware uh which then can touch disk,
right? So, it has the ability to write to system disk uh and you know and do all your normal tampering with the operating system. The good news is we have a few ways to try to guard against this. So, Intel created Bootguard, but just like with, you know, all systems that are doing security, you have the uh closed source versus open- source argument. Um, this is a proprietary solution. We don't really know how it works. And so, um, we don't know if it could be easily bypassed. You know, where's I'm sure Intel has decent peer review internal, but um, it would be nice, you know, if we all knew how it worked and then we could still say it
was secure. And in fact, um, what if those private keys were leaked? Oh gosh, I guess they have been. Yeah, there's been private keys already out there for about 40 different types of hardware that depend on Intel Bootguard. And so those are in the wild. So those will have, you know, all those keys have to be regenerated. Yeah.
It's a fair question. I I think I was going to go back to the whole thing of you know sovereign immunity. So I I you don't really see people coming after um just like in in war if there's collateral damage. Um, I guess you could come after the US government for damages. Um, but that's a question for the courts. I don't have a good answer for it. But yeah, you're right. If we develop the tools that are then used against the populace or against businesses and cause some of this issues like on the previous one with NSA, right? Uh, then who's who's culpable? Who's responsible? We'll chat later on that one. Just to finish up here, um, we
do have some good news like there's DevSec Ops tools for firmware developers. So, Chipsseack is a is a great anybody use that? That's uh you can get that off GitHub. It's a open source project for hardware security assessment. There's a couple of big players out there. Binaryly is one that does supply chain SBOM research, uh threat management, vulnerability scanning. Our own buddies, anybody from Opswat here, their local TM, you know, Tampa based company here that has a meta defender drive for testing binary. So, we do have some some hope there. I guess just kind of some final thoughts here is we've provided some nightmare scenarios, but hopefully we've given you some ideas for overcoming those.
Somebody once asked me, "Hey, can't we make a foolproof system that you know is not subject to attacks?" The answer is no. As long as you have humans designing and operating the system, you're always going to have you're always going to have human error involved, right? If I mean, if you want to have a completely closed system and cut off all communications in and out and nobody can even pick up the phone or answer an email, but as long as you have those things, you're going to have those vulnerabilities. And as long as you're you have this inherent trust in the system, you're always going to have those weak links like like in the XKCD
cartoon. But I was just thinking it, you know, um I thought about this once. We we got paid to do a penetration test on a a university that had about 50,000 students. And with about within about four hours, we had gained complete access to the student record system, to the faculty account system, and to the entire financial system of the university. Every one of the records we came across was worth, you know, $150 on the open market. So do the math. That was like $7.5 million of value. I think we got paid like, you know, 50 grand or whatever for the for the pentest. So the point being, it sounds like those guys are, you know, they're driving around
Lamborghinis right now and, you know, it sounds like they're making it. What goes around comes around. Ultimately, they will be judged. But we as the White Hatters, as the, you know, the moral high ground, we're helping society become more secure and be a a safer place. And so in this twilight zone of horror scenarios, you know, we're stepping up as the heroes. And I'm challenging all of you here as well who are in in a role to make a difference in this world that, you know, we have that moral obligation and we have that that charge. So, I salute you for being part of that, being part of the good guys. Right. So, at this point, um, we'll be happy to
open it to any questions. We got a couple of minutes. Yes, sir.
Right. So he's saying um uh the uh the charge that Delta is making against CrowdStrike is that their EDR is a inicit back door. Yeah, we've seen this argument before. Do you remember when um Sony uh had a digital rights management on their CDs? So like if you ever loaded a CD, uh they they implanted a little uh rootkit that's that stayed persistent. That they got sued for that. So, my guess is uh if they have quality lawyers, they're going to get some money out of this. At least a settlement. Yes sir.
So you want you're Yeah. The question is is whether or not we should respond. Do you mean the if it hack hack back, right?
It's really going to just depend on the scope and scale of what it is we're looking at, right? And you know, we've there's policies in the government talking about hacking back and and reaching back for for some of these things. But it comes back down to the attribution thing as well. Um, which is always a challenge, but we we have to Yeah, I have an idea. So, I know exactly what you're talking about with that other government. If if I recall correctly, they weren't doing anything right. Like they they weren't even using like licensed copies of Microsoft Office. They had like um shareware version, you know, scare what do they call versions. Um so the answer is we I think
we have an opportunity now to be proactive and to put in those things that we need to do. If we put in zero trust, if we put in segmentation, if we put in sbomb control, if we put in, you know, vulnerability testing and all that stuff, we have the opportunity now to lessen the severity of these attacks so that that they won't be so devastating and widespread. But yeah, the show must go on. And so with any instant response plan, you have to have workarounds, right? You have to have there's got to be like a paper version of the ledger. If you can't get to the electronic ledger, there's got to be workarounds and that stuff has to be planned out
years ahead of time. One more question. Uh Jonah
Yeah. Yeah. So, I've seen this before. Um we were working with a uh um a smartarthome connected home software developer and they had they had built a couple of tools themselves but all the rest of them they had purchased through mergers and acquisitions and there was no uniform method of security. So I think it's incumbent on whether it's a private equity group rolling up, you know, software companies into one big entity or if it's, you know, a global software developer, um, you've got to, uh, impose a unified security stack across your entire development environment. If if there's things that are lacking in the things that you've acquired, you need to bring those all up to the same level and
standard. Um, does that always happen? No. You're absolutely right. It's usually just a a money play, right? It's um who is it? Tommo Bravo. I mean, not not I'm not disparaging them at all, but they'll they'll come in and take an old brand like that and they'll cut off the bottom 20% of the staff and try to make the thing profitable again and then, you know, sell it off and what's happening to the security at that point, right? It is definitely a concern. Many such cases. Well, hopefully uh you enjoyed this trip into the Twilight Zone. Have a great rest of your day and we'll see you around the con. Cheers.