Tokens & Takeovers: Cloud-Powered Supply Chain Attacks
Show transcript [en]
[Music] hello everyone uh it feels great to be back at bides uh aabad again um so today I'll be talking about uh some interesting findings from the past one year around like cloud-based supply chain attacks and yeah and that have been fixed as of now so uh please note that the vendors that are mentioned in this stock uh aren't the only ones affected and yeah so let's say you are a developer learning a new cloud service you go to some official Cloud documentation and it references a GitHub repository uh you think that hey it's official documentation nothing to worry about go through the steps the scripts and then you just follow whatever process that they have mentioned and you
don't think twice or maybe a friend sends you a website which is like an official uh Microsoft website uh about like talking about a tool which basically helps you down load Ram or something basically speeds up your system and you're like okay it's microsoft.com what there's nothing to really worry about right so there's a common thing between both the scenarios that I just described briefly and we'll take a look at what are the shenanigans that can happen in the back end when these services are powered by cloud services so my name is NES I'm from a beautiful state of Sikkim uh I work at Tren micro in the cloud threat research team so my focus has been around cloud
services since 2022 and I've been in the top 100 researchers for Microsoft twice now um and you can find my work on this uh single cute little web page so in the next uh 35 to 40 minutes I'll go through a brief background so that we can understand what we're talking about and we'll go through some of the in the wild findings that I have divided into different scenes and we'll wrap up with some takeaways so the scenario that I mentioned uh right at the start of this talk about a legitimate subdomain of microsoft.com or some official Azure documentation right would you trust stuff that is present there probably yes probably no it depends you have an implicit trust
which is built from the uh reputation of that organization that you are you know working on so implicit trust is something that we will kind of explore uh in the next uh 39 minutes maybe so let's take a brief look at how software supply chain attacks have happened in the past so polyfill is a is a popular JavaScript library for browser compatibility so its domain was actually compromised I mean someone else took over it and around 100,000 plus websites were compromised because uh it was being mentioned in the JavaScript references and there were no SRI checks as well and this happened because of a dangling domain takeover and even npm packages were affected in this
case C cleaner back in 2018 uh this this is a simple cleaner tool which helps you you know optimize your systems and it had it was back doored and it and it had around like 2.3 million pieces that were compromised so it would it would actually stole uh it was actually compromised from a from a developers Workstation and the credentials were stolen and then they were used and when we talking about supply chain attacks we really cannot forget uh the stuff that happened with solar winds so the Orion updates contained malicious code it was also compromised and it was able to propagate to like 18,000 plus customers with some really big names and a lot of uh us already know
about the Cod supply chain attacks where there were some instances wherein wherein attackers were able to basically exfiltrate the giup token and then they were able to uh like move laterally within the environment itself it had typo squatting officiation npn packages being affected and whatnot and when we are talking about uh supply chain attacks open source is very much leveraged in a very different way as well as we can see in this icon burst one where it talks about uh Gathering data from apps and websites and definitely we cannot forget this awesome research done from uh done by Alex Bon which talks about dependency confusion and how he was able to uh basically gain some initial foothold in in a lot of
organizations out there and I'd like to mention this uh one more U interesting bit about supply chain attacks it can basically affect literally everything that you know that works on software so be it genkins be it uh any of those cicd tools GitHub actions everything that you know can be used can be abused as well and retrospecting on how these uh supply chain attacks have happened there's a simple pattern to it you compromise that one single component on which systems uh systems are dependent it can be because of weak passwords unpatched uh systems vulnerabilities zero days domain takeovers domain hijacking CI specific attacks uh and a lot so they can Target any of your applications and this is how
it works and it actually abuses implicit trust so when it comes to cloud and how and and if you think about Cloud power supply chain attacks how do they look like um well it may be raining everywhere but that that's a very bad joke so I'll just move on to some background with uh with a brief background of how these have happened in the past and now we'll take a quick look at Azure storage accounts so so that we can we can get a fair understanding of what is going to happen next so Azure storage accounts a quick 101 it's Microsoft's cloud storage solution it's scalable durable available secure as well different flavors for different use cases you can access your
uh stuff that you have stored in a storage account via rest API SMB NFS it's similar to a S3 as well so there are different types of storages so blobs files skes tables these are the most popular types of storages that are used um this is just some basic introduction so that we can understand uh what we going to talk about so the usage when we think of the usage of cloud storage uh Services it's very uh you know obvious like you can use it to share your web resources and these Script image tags uh sharing files uh backups hosting static sites and you know a lot more actually so these blob stores can be accessed via
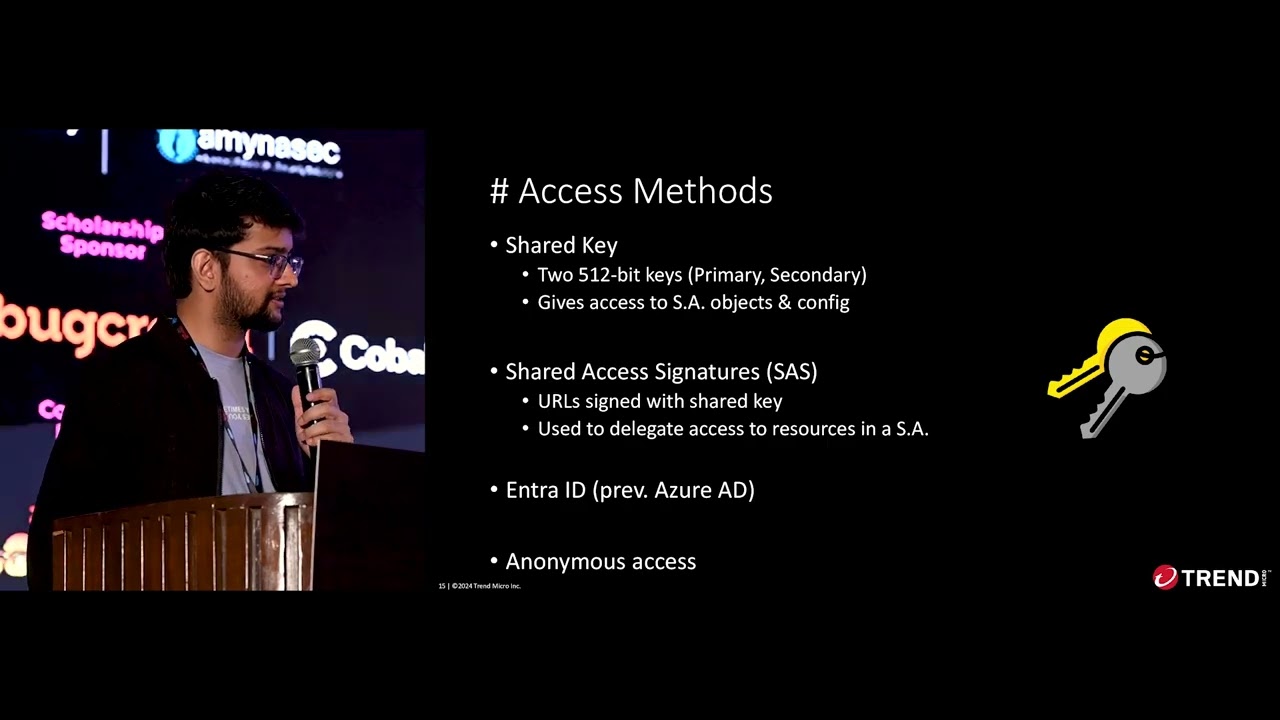
rest or https as well so in this example the name of the storage account is Sally followed by a container that is named pictures which is which is like the directory or the folder that you can think of which is followed by the blog uh which contains the image which is image 001 similarly uh there's a file type storage as well where again the name is the account name is Sally and the file share name is pictures followed by the folder or the blob which is image001 jpeg so there are various ways to access or you know delegate access to a storage account one is via a shared key which are basically two 512-bit uh keys there
are two because there are there's a primary and a secondary one so if you want to change one then you can use the other and it gives access to the storage account objects and the configuration as well um and then you have shared access signatures which are basically URLs that are signed using the shared key and it's used to delegate uh access access to resources in a storage account and you have enter ID and obviously the worst one that is the anonymous access so particularly for today's session uh we'll focus on shared access signatures so there's this tool called Azure storage Explorer it's from Microsoft it's an official tool um and you can use these keys or these SAS
tokens to basically browse or uh work with the Azure storage account that you have found or if you're brave enough you can use Cur or the rest API like bare hands so here's an example of a shared access signature so everything that you see in yellow is the shared access token and so there are specific URL parameters like SV SS SRT SP and all these things right so these URL parameters are actually well defined and documented as well so we'll particularly focus on these four URL parameters SS SRT SP and SE so basically SS is uh implying that the SAS token applies to blob file q and table Services the SRT variable in this case it applies to
service level container level and object level operations SP is basically the permissions of this SAS token which uh enables it to read write delete list add create and all these other uh roles and then you have the expiry of this SAS token which is set to sometime in 2051 which is way farther so now coming back to the example uh we'll just describe how this entire string looks like so we have the storage account name followed by the service host followed by uh the public data sets is the container name and the tar EZ file is the blob name followed by the accessible Services uh the apis that are accessible so service container and object level
apis the SAS permissions the expiry of this SAS token and yeah so SAS tokens are of three types uh account SAS tokens uh which can allow for access to multiple storage services so it can be blog file q and table uh the maximum validity that you can set is to uh d99 years and it's secured with a shared key it's similar to service SAS token but the service s token is specific to one single service and yeah so particularly we'll focus on the account and Service as tokens for uh this session as they are easy to misconfigure and you can set the uh maximum validity to 99 years cool so there's this one thing about SAS tokens that it is Created from
the shared key or the user delegation key what this also means is that the SAS token generation is not an Azure activity what this means is there are no logs generated if you create a SAS token from a storage account credential and there are no logs so you cannot track and if you want to invalidate any SAS token that you have leaked out you have to rotate the storage account key itself so we have some sort of background on what we are going to uh take a look at we took a look at the storage accounts we took a look at different Services some ways of authentication authorization and now we'll do some Reflections Reflections on
the basics so it's very interesting to note that these SAS tokens are basically just a bunch of URL parameters and uh so many bug bounty hunters are there researchers are there right so URLs are often logged everywhere like a lot of places like server side any referal headers browsers and if there are any inline proxies um yeah and there's a cwe as well so it's very much well-known it's not like something that we don't know and this was also observed uh in my session last year that we had actually observed the um users JWT being logged in enginex Access logs on Azure ml compute instances and this is a well-known thing on Jupiter server so you can specify
your token as a header or as a URL parameter or in the password field itself so now we start uh with the beginning but we need to take a look at some of the history so SAS tokens uh this is one of the blogs that I found that have that talk about how SAS tokens can be abused so it's from uh Sunil yadav not so secure and there was this recent news as well I mean it's not very recent but it's kind of recent given my age it's September 2023 where a SAS token was actually abused um used by researchers at Wiz to access 38 terab of data that was accidentally exposed in a storage
account and so the storage account contained a lot of other things as well like employee backups of some former Microsoft employees um the machine learning models the data sets and all and then Microsoft actually re released U their end of the story like hey we have actually we had actually found that but it was DET I mean marked as a false positive but now the system is fixed uh they have getup secret scanning in place and uh they are already reporting on the overly overly permissive SAS tokens and that's the end of the story um so if there are any questions uh we can take that now thank you okay I think that was not a good one so
uh we just starting now so we'll take a look at Microsoft documentation first so how do you learn something other than YouTube or those one minute engineering videos through the documentation so Microsoft documentation is there on GitHub it's it contains the howto of azure services and it's also open to user contributions as well so during uh while during during some uh searches that I was performing for EXP SAS tokens I came across this one documentation reference which talks about Azure SQL managed instance which is like a scalable Cloud database service so you can you know create your DBS and all on a managed instance which is on Azure and you can work on that and
here's a tutorial to basically restore a sample database and these documentation uh instances they are actually mapped to GitHub repositories so if you notice in the GitHub repository they have an SQL statement which says it creates a credential with a specific identity where they have specified a secret as well so the secret actually contains an overly permissive SAS token if you notice uh the secret is the SAS token and it has uh the services set to blob file q and table the apis that are accessible for service container and object level apis the permissions are read write delete list update and all these uh other permissions and the expiry of this SAS token is 2028 so this means that this s
token is valid I can use it to possibly Mount or maybe access the storage account and also write on the storage account and this is an account SAS token so using the Azure uh storage Explorer we were able to access the storage account and if you noticed there's a file called NS was here so that was me I was able to upload files on these storage accounts with right permissions and implicit trust was kind of broken so as I'm able to upload a file or um manipulator file on that official storage account that is used in Microsoft tutorials and is also mentioned on their uh subdomain I was curious to to see whether if I could um
uh perform some sort of code execution if there are any instances out there so the way for that was to use stor stored procedures so in this case I create a stored procedure uh which basically enables XP CMD shell and then I'm able to execute command if you are uh running any of the procedures that are in this database so as you can see I'm able to run who am I and I can view the PC file as well so the impact here was that we could achieve code execution via back door stored procedures uh this was reported to msrc and they had already like they fixed it basically so this is one the other is uh kernel CI so kernel
CI is basically an automation or a test system for testing Upstream Linux kernel um systems and it helps basically ensuring the quality and the stability and the long-term maintenance as well so Colonel CI also standardizes the hardware uh testing for the Linux kernel across all the possible widely used Hardwares and they have certain dashboards and a GitHub repository as well so what we found was that it it provides some sort of Early Access to users for testing the Linux kernels and the way it does is it gives them access to a file share that is owned by them and the file share contains I mean to access the file share you need a SAS token and the SAS token looked something
like this so it had like again the readed write permissions it was expiring at a much later date and these SAS tokens could be then used to basically access the storage account again and I could again write files and this actually mean that I could have possibly modified other users test kernel builds uh achieved potential code execution on colel Ci's test build system uh alter testing results for other users obviously because we can write to any any of the files there and potentially abuse this uh storage account for unauthorized storage as well so the fix here was that they removed the SAS token that was mentioned in the GitHub repository they probably also rotated the storage account key so that
the key was in uh the token was invalidated and yeah so this was about Colonel CI then when you think of these URL parameters one of the most common things is to maybe you know just go haywire and scan the internet and let's see what we found on the internet out there so storage accounts uh talk about scalability and durability as well and availability as well so let's say there is a storage account where you have mentioned or where you have kept your JavaScript files images other web resources that you have referenced elsewhere like in your Android apps websites uh Mac OS apps and all those so these resources are all stored in one storage account and they have been
referenced in other places so we did a quick scan of domains containing references to SAS tokens and here we see a mention of a Javascript file that is being referenced using an account SAS token and the SAS token has redri permissions and we found the same SAS token on seven more websites so total eight websites and if you see where this is going basically the sash token is over permissive and I can upload I mean I can basically override this Javascript file and there were no SRI checks so sub resource Integrity checks were missing as well um so the impact was that I could maliciously modify the Javascript file that I found from one of those
websites which was referenced in seven other websites and I could have possibly compromised the entire other other other websites as well so total eight websites with readit as tokens the Javascript file could be modified and the endless possibilities obviously like credentials harvesting uh browser based crypto mining as well so do you know browser based crypto mining I did not know that so there's this cool talk uh which talks about hijacking a JavaScript library that was being used in a bunch of uh government websites and they were being abused to mind cryptocurrency on users end that was pretty cool um yeah so now we move on to Microsoft PC manager so Microsoft PC manager is a tool uh that we as kids
maybe 10 12 years ago would like to have it would help us basically download Ram from the internet like basically make our systems a little more speed speeded up so you can speed up your windows devices uh you can clean your applications clean storage optimize your startup file utilities it's it's similar to C cleaner in a lot of ways so to install uh PC manager there's this tool called winget winget is basically a package manager for Windows 10 or Windows 11 and it has a CLI as well so you can Define these uh package um package information as manifests so these manifests are basically yaml files and you can Source them from two different sources so from Microsoft
store which is apps. microsoft.com or winget which also has a community authored uh GitHub repository as well which is mentioned in this GitHub repository so this is how the yaml file looks like uh for a wiet package package and if you notice there is this thing called installer URL and installer Shard 256 which which basically contains the path to download the installation file which can be an MSI installer.exe noft nullsoft installer and all and the installer shop which is basically calculated uh by the wiet CLI uh from the installer that we are working on so okay this is okay cool yeah so in one of these manifests what was found that that there was a SAS token which
had like read write permissions um and this was kind of interesting because it was mentioned on Microsoft's PC manager uh yaml file itself and if you want to install any package this is how you can install it like B get install you specify the ID of that U tool that you want to get on and this is how it works so if you notice the URL the SAS tokens is like read write delete and list permissions so let's see where we can what we can do with this but first the domain looks a little different it looks like PC manager. office plus. CN a Chinese domain so I was just playing around with this uh
domain and I was just trying to see what are the other things that I can get out of it and I found that we could get the underlying domain to which uh the storage account to which this domain was mapped to it's not really a sensitive information disclosure but it helps me connect easily and directly now so turns out that we could browse the container named like the directory named MVP in in this storage account using Azure storage Explorer and we had right permissions as well there were around 20 gigs of internal um debug builds as well so the impact here was that we had RR delete list U permissions on around 358 GB of
Microsoft PC manager that was being um distributed via vet which contained like 20 gigs of internal builds so we could infect users of Microsoft PC manager via winget and apps. microsoft.com as well and this is a PC that I crafted so basically I was able to upload a file on that storage account and who does not love a p come on and the impact here is that auto update is enabled by default in Microsoft PC manager so if I replace a file on that storage account and if there is no you know because there's this simplicit trust again that is in play and if I replace a file on the storage account that gets updated on all
the endpoints you know where this is going and you could uh potentially carry out a supply chain attack by replacing the MSI installer and propagate across Microsoft end users as well but the interesting bit was that wiet has its own defenses like the the installers are 256 so I was not able to bypass this um so the mismatch in the ca itself does not lead to a direct code execution so if I replace a file on the Manifest and I expect a code execution that's not going to happen and there are certain Flags to disable Integrity checks but they need admin privileges so not really uh my thing right now so these are so this is how
you can basically enable the uh hash override and then you can basically install the uh vet package that you want to install without validating the Sho 56 which is not cool enough which brings me to Microsoft PC manager scene 2 which is the director's cut and now this is the uh coolest part the presentation so if you know you can do better uh then do better it it sounds very simple right and compromise why wiet is fine I mean I don't even use wiet so how popular is PC manager like how popular is this tool and where else can we get this uh tool from is there a dedicated official website so I did some
searches on Google and it seems like it's kind of popular like there were a couple of blogs from PC World bleeping computer they all mentioned that hey you can use this PC manager to uh speeding up your system and all that this is just to show that this app had a lot of existence there and it had this particular subdomain mentioned which had PC manager. microsoft.com okay cool and it was also mentioned in the apps. Microsoft page for this uh for this tool on the publisher info itself so this is how the website used to look back then when I was working on it and you see this cute little download button there so when I click on download I get
redirected to this akms URL so akms is a URL shortener for from Microsoft and they own it right so this is again a trusted URL itself and this basically sent me to another domain which is a a storage account followed by a SAS token and folks if you if you can uh zoom in a little bit you can see the read write SAS token which was a service SAS token okay that should be fine and you can see that the expiry of this uh token is somewhere around 6th of March 2024 so akms URLs were also found on various other um various other places various other places on support forums left and right so you can see these akms
URLs so all of these URLs were actually using a SAS token that was that had the read write permissions and as you can see I was able to again uh get access to the storage account I was able to upload a file and this was here and it had around 118 gigs of releases that could be compromised via akms URLs and PC manager. microsoft.com so the impact was again redri delete list on 118 gigs um we could infect end users of PC manager through this official subdomain and this is how this is how I crafted a PC for this and here's a quick video so I go on Google and I search for PC manager so I hit on the first link
it's not a Google ads don't worry then I am headed to this page I click on inspect element because why not then I go to the network Tab and I click on download and I just save the file I copy this uh Link's URL and I head back to storage Explorer I connect to the storage account using the Azure storage Explorer itself click uh yep okay so I'll just reiterate that I have access to this exe file where the expiry is sometime in 6th of March I have read write delet list permissions and I click next and I hit connect
so once I'm connected uh it will be mounted as a uh blob container so the container name is mvp1 and I go a level up a level up and if I can see I have other files as well that can be
replaced and now I show you the SAS token that I have used this is the same SI
token I have already uploaded a file on this storage account this is just for the video I'll just scroll down to the bottom click next and you see this NSO here file so this was the file that I was able to upload this is just to show that I could replace any of the binaries as well
it takes a while to
open all right so these two issues uh were reported by the Zer initiative they both were assigned a CVSs of 10 uh last year so the impact here was that I could basically replace the uh PC manager tool that was mentioned on their official subdomain and Wing get as well so these were a couple of uh fix commits that were seen and it was first committed on GitHub on 5th of November 2022 with the SAS token which was reported on 20th September 2023 so the initial fix for this was uh they just uh changed the permissions created a new SAS token with just read permissions and this is is totally fine there's no issue with
that and the attacker basically in this case uses the SAS token to get into the storage account which contains the PC manager builds the releases that are mentioned across apps. microsoft.com PC manager. microsoft.com akms URLs and the wing get manifest as well so when we think of the takeaways and when we think of the hope that brings uh that is brought along we need to figure out who is able to use these SAS tokens to access a storage account so one of the initial ways to figure out could be by enabling logging and then you can take a look into the user agents but you can start off from the user agents you don't need to just
stop there when we think of any overly permissive SAS tokens being used so there are ways to detect that but you cannot find which particular SAS token is being used so the signature field is missing so you can leverage asure uh storage analytics logs but with caution because if your storage account is heavily used you will incur a lot of cost uh you can check if an overly permissive SAS token is being used and you can also check whether a SAS token is being used so when we think of hunting for uh SAS URLs there's this very simple GitHub code search query that I started off with where I'm looking for uh the content which
contains SP equal to RW like any of these two and the expiry sometime later and obviously you can add more filters like not is fork or you can scope it to a specific organization or a giup repository and you can expand based on experience like there are so much so many tools out there so many cool project Discovery tooling as well so you can leverage all of that so the takeaways start with the bare minimum Privileges and work your way upwards so this is for any of the tokens any of the credentials any of the permissions that you uh you know assign so so if you are having to use these SAS tokens or like such sort of
mechanisms like AWS presign URLs as well you can basically uh use shortlived SAS tokens or if you want to create a SAS token which is like valid for a longer period of time you can use stored stored access policies and you can obviously like inspect your network traffic for Rite SAS tokens and you can also scan your code for these SAS tokens so it's just not it does not only apply to SAS tokens but any other Cloud credential that you see elsewhere and probably it's time to also update your truffle hog or git leaks and most importantly GP um and and from the code perspective code basis IC files Docker files Docker compos kubernetes yls and all of these other
things and this is one image that I had to put because all modern Cloud infrastructure is all dependent on one single overly permissive cloud service credentials audit assess don't assume trust I don't like to use the word zero trust really but uh I think this is a case where you have to focus on that aspect as well you need to develop some sort of detection response mechanisms for anything that you are exposing publicly you need to vet everything that you're uh using and working Integrity checks and all malware checks and all and whatever you can log and work on please do it because there's no other way to figure things out and obviously please keep the cost in
mind and there's more so it's not just Microsoft there are other vendors as well that were affector that we found in our research we leveraged a lot of Open Source tools as well we found a lot of credentials on thread Intel platforms like virus total as well so it's all in the process a lot of them have not been fixed yet so coming back to this image that I had shown earlier it all starts with code it just Ventures it way to Cloud if your code has vulnerabilities if it has malware if it has back doors it will just propagate to cloud and you need to fix things right at the start it's I'm not saying something new but it's
something that kind of resonates with what we are finding in the wild and now when we come back to implicit Trust on official Microsoft subdomains it's not just Microsoft I'm just repeating that again and official documentation implicit trust is kind of broken so that was my session uh I'm open for any questions for any hard questions that you may have and okay let's [Music] wait yeah we have one two questions okay okay can you hear me now yeah uh as you know on the Windows there is a universal access control for download files so when you yeah are you able to understand or should I talk slow uh you need to be a little louder I
guess okay on Windows you know there's a universal access control for the downloaded files and you said you were able to upload any file or change contents of the already uploaded files on the PC manages Windows blob but were you able to bypass this CU if you don't have any valid signature on the file Windows it will uh just block the file and warn the user and uh from the what you showed on the slides I see you needed to change the permissions on the winget itself so I am wondering how were you able to bypass if you were able to bypass if you not how Windows traded this uh as a accept report or like in medium sity high sity
or crial sity cuz in these terms you are basically forcing user to enter comments which is not different than entering comment on the user compet itself so I'm wondering if you are able to bypass the signature because it is not it is just basic file upload so I'm wondering how windows I mean Microsoft itself traded this as a severity how they validated itself yeah that's a great question so the question is on bypassing the uh the signatures of the files if I had the permissions to upload or replace a file on the storage account so for the winget case we had the installer sh 256 that was mentioned in the yaml itself so we could not
bypass [Music] that I understand that one I'm not asking for that one you were showing the URLs you said uh on winget you were not able to do it because of the signature on the Sha 256 but on the next slide on the scene two you showed that uh there's some aka.ms URL uh which is forcing user to download file what I am asking let's forget the vet on the downed file itself were you able to force user to bypass universal access control because if it is not signed by the Microsoft itself uh windows will prevent user and saying it is uh from unknown source and how Windows trit is this is what I'm wondering so you're asking about UAC byp
pass yes cuz uh this is not different than uploading files on the Amazon's S3 buckets as long as you know you are not able to do anything that is not uh actually impactful for myself I'm experienced user for but for normal user you are just forcing them so the thing I'm wondering how windows I mean Microsoft itself uh classified the severity of the issue and Ted this because in uh let's say in back pantti perspective or and pent testing P perspective I would classify this as love impact don't get me wrong I I I understand you were able to upload files on the blob which is not different than any bucket on the AWS or Azure or let's
say gcp but the thing I'm wondering how Microsoft classified this so I think that's a commment that Microsoft can add to it right that's the first one and the other thing that you're talking about validating or you know bypassing the signature itself so the case here is that I'm not forcing a user to even you know click on a link the thing is if we talk about uh the auto update scenario um yeah the the thing I'm asking for the like uh like five slides ago I think from this one the aka.ms you show that aka.ms PC manager 500,000 yes uh I'm wondering for this stuff how it could be malicious for the user cuz you
are not able to bypass you the universal access control yes so okay now I understand your question took me some time so these akms URLs so these are all akms is basically a Microsoft owned URL shortener yeah I know so implicitly you will be trusting it if even if there is any sort of file that is not signed right you will be trusting it because on the based on the fact that it's an akms URL no it won't no I mean universal access control just doesn't trust the domain you are getting it wrong it will check the signature because it will say unknown source yes but the thing is uh that is what I'm wondering I understand your
point that is good uh vulnerability I'm not saying it's not it's not bad the thing I'm wondering how Microsoft handled this cuz for Microsoft itself this should be low impact CU you are not able to do anything to comp user computer cuz you are not able to bypass the universal access control cuz this file is not signant by the Microsoft or let's say windows itself so you will sh just let them download the file from The Blob of the windows.net but it will be showed as a unknown source when they try to run so I think that depends on the users uh awareness as well so if they're downloading a file from ANS URL yeah I
mean I I understand if we care for the users uh awareness then everything should be critical for us the thing I'm wondering not your one I'm wondering how Microsoft classified this so the process was like we reported it to Microsoft we showcased the uh PC as well yeah and they fixed it by replacing the SAS token with a read only SAS token so that was the fix and okay okay yeah no no no no the thing I am wondering is Microsoft traded this as low impact medium impact high impact or critical impact cuz if I was a Microsoft engineer who was going to Tre this I would classify this as low impact okay I think I can't I can't
comment on that as of now because we haven't you know seen any public statement from Microsoft on thisen just say they just pay the highest Bounty that that's the information okay on the bounties so zdi does not uh take any bounties from its venders that it reports to no no I mean the bonti let's forget bonti let's say they say this is very high critical issue for us that is what I am wondering I think I can take that offline or any other folks that can join in as well no problem because I'm running out of time here okay uh there was one more question I think at the back there we'll just okay I'll I'll
take the other questions offline I'm having some time cut here so uh that was all folks uh from my side for these SAS toen abusers and really thank you for your time U and let's connect so I'll be around as well so thank you