Catch Me if You Can

Show original YouTube description
Show transcript [en]
yes I wanna see your manager it's yours risky our vendors their businesses are all cash means nothing [Music] the idea of this caucus came about from the test I'm gonna pass their sister was on the other some other testers yeah we go go on-site do a test it's almost too easy at times yeah we buy lunch perfect you're the main potentials move around a little bit escalate privileges give the main animated get Buddhism so that's kind of where this talk is a spear the North Ward you guys are out there to resist headbands and lose numerous right crazy blisters out there I guess it's really groundbreaking or the hopefully you guys are already getting chance to use these
evenings this we all get little deuce coupe sometimes which mrs. I'll say of it hopefully hopefully together getting them to be cool type of attacks that a lot of amateurs out there using right so over and over day covering common action area walkthrough credential harvesting for our purposes we're going to help our responders to comment we do a lot of this Christmas mr. you're using quite frankly easy but when you're on the networks talk about that will talk about privilege escalation gas Andrews policy purposes those are kind of things we're also using direct his attention for also need to move as well and then we'll talk a little bit about those accounts my password yeah this is all to me it's common sense
minute basic security - but again doing about successful attacks outside their discipline excellent varieties it's not it's not we're not where we need to be your security posture she was Walter Becker lead contact area listening that mission reached most hotly at one from facial in the spirit vision from other means with that most likely Avenue reading that thing that's it once we get attention cologne rock you're gonna start compromising subsistent we've got me the absence of any use everything else we're gonna start parsing other potential to move it around looking for system says that means once we find those guys it's pretty easy to dislike losses that once again Moses awesome it's literally there's the main idea for lunch right
that so much easier mmm they got a little drawl ancestor data as the loud movement there's even a lot I really want focusing on here you know we have a days he'll once we started native identified and wiring it was likely as a bad guy everybody's goal was for us is usually just hopping for all that we do get so engagements for they want Strether seething established would be there they out my only focus on a discrete vision or in an initial breach that's part of the problem they were focused on the perimeter and protecting the forest these little areas that's really where to meet you guys at that point there's a rival had continued
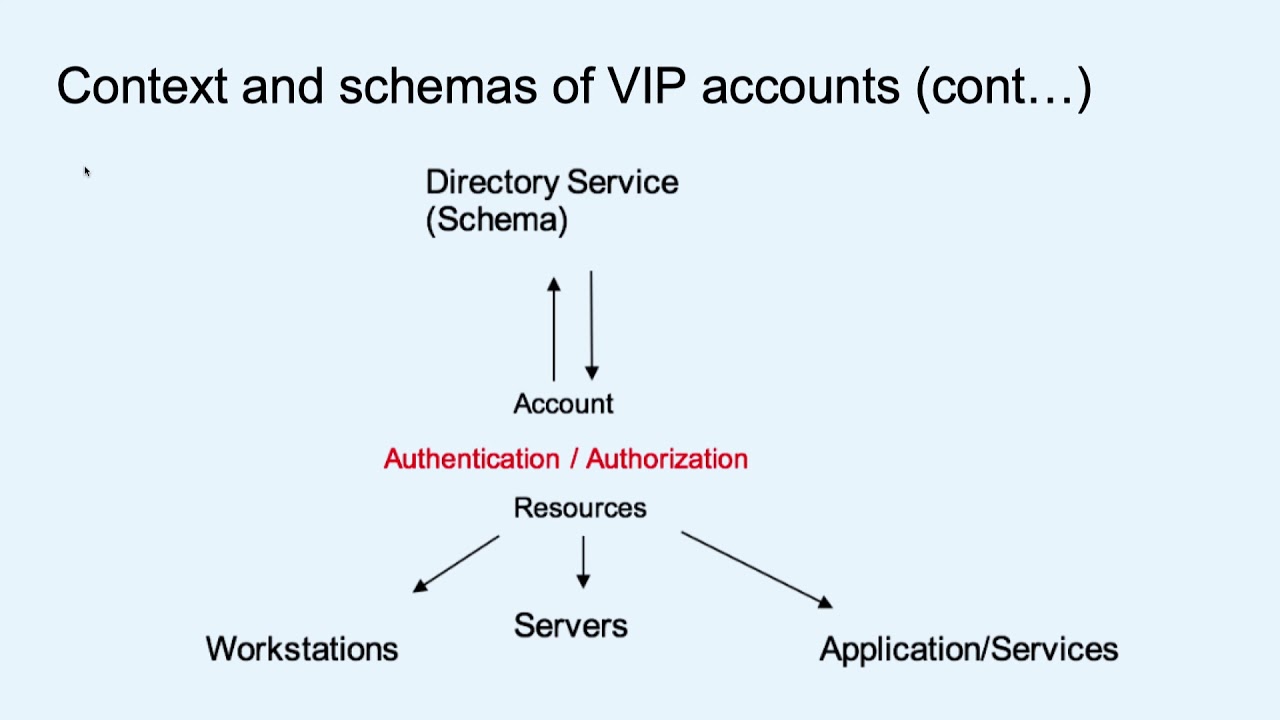
breach they've been kind of yes all right up so I got new this so Sam and it walks through that from start to finish Ali how you gain additional access which actually looking serious in that case with those references that's a lot of common ways to get access it gives through value at the initial credentials outlets other down the system it means obviously build is it's very rare that you get to see an adversary rather out of how to take it dolly down it's good read out everything you take it out alright so talk about digital heart for meeting the most adversaries we're gonna start out with the main user gets all them little careless user say gorillas they're
almost all the girls but we get the main user credentials use those a good clip do queries use the main controller find out who the man is are you need to target that go after next you know any service accounts or institutions once we find that and we're gonna do after visits to the main admin is a lot of times they they're a little more careful in password you're always a little bit more secure than the average user but with some of our tools we see a little later it doesn't really matter strong that word or we password so are using a free little say regardless so responder grants like I said earlier easily you guys are you just longer give it
often how many traditions [Music] pragmatism so sometimes I get lucky next to you the man is smart not often but the house so when we're spoiling our legs really doing for it so it's driven by the guy's inspired apps so first way when is really doing is providing us the ability to go after a couple sequences if I change service and then dubbing that so the element in our link-local multicast name resolution I meant by whose neighbors of the name service both do basically the same thing link-local multicast name resolution was a replacement for integers what it does is allow mobile computers on the same network to divide advisor with the WPF piece is basically
the mobility there is with variants for yeah all right let's go proxy turned on all right it's basically going to wear you out as I started with you know is there a proxy to find W guys out that did I could go do we get this information or browsing if not isn't where it ends if it doesn't get that as we go out say hey we might know the person I've seen so responder we basically did basis as they are a little answer to those requests so you can either answer them separately if they don't want your party most I understand and now look at group all you know what happens always so user to be on network that make this type of
survey a more Eastern a that's worth a if I think service is why not go to the leg responder I'm in it you kindly in the username pepper patch and then it's a matter of going back - which you know oftentimes is fairly sure do those users ways what we've always told users never the savings are as a character passwords or later so basically with responder we can we can take advantage of these weaknesses again like I said it's almost right right away the first thing I'd be model size for a child is if there's not switch matters what's that if there's not switch networks right yeah yeah you're gonna get to do it although I did read it
wasn't last year it's always there we just kind of their bed server system on my new blank dubbing pad that's my dress is long didn't want some special because it on your own servers it's about I wouldn't take it off okay it's not usually deranged condition it's not any badges I'm gonna start with and actually that writing so one thing I wanted to say about the responder is I don't know if adversaries that they're using similar taking some tools for all the obligations Father's Day I do know that they invited a public apathy users father now I load it never explicitly said he would go with all network they actually you to capture edges I'll kick
off this monitor and then Wireshark or TCP dump and then watch to see if anyone else is trying to respond to this information smooth you can tell if you're overriding two other pastors when Alonzo basically thought out a lot certain hangings yes sir so what can we do to mitigate respond or one of these weaknesses right so those in our advising service really got to say look interested disabled users the problem is it's probably not likely those services in violence so looks like that you're not going to do that all same thing with restrict their then benign communications you can limit that have communication between those this really in this responder on your desk is
usually focus on living let me of your privilege right reducing the amount of good those account users you have network I see the best way to take care of this I think there are some either a be your first five protections that identified with large runny but one side it was that I just changed something that only borders you there do you nice right there and we'll do it if every variations you know I'm taking that box instead of on back with the text things for proxy figured that double bad DNS injury so they didn't go out and just yell to the for the network it's really difficult difficult to take listen so you have to use other other means of
calculating that weakness our next tool we like to use a desert devil uses maybe dance you know it basically allows us to get clear text that's worse those village and his billion hashes as well as allows entry golden years of unfettered access to your network but that changed overnight basically the problem is Windows 3 2008 4 3 2 2012 r2 as well as where there's a one my default in stores passwords and reversible format different new you ask allows you to go out there like those scribbles so again like I was saying there's no it be a strong password to be with password so that actually the right up for hacking thing again rose yeah the
guy was truly need I guess the order that nothing funny certainly deadly backwards and what I really bitty pointed there is pretty good I was laughing at the guy I make fun of it in reality would be a gassy longing all our Google so so that you know it's the one one thing about it it requires local admin for another new des again you know when we get to talk about cripples cows holla at words that's right we've seen environments where we visit a louse is 411 across the bottom
so mitigation context and strategies in me that's it's sort of easy to tip and then so you were out of the box me guess to easily detect a lot of Athenian problem lies in it I'll get to do is compile it contains some different okay time to not may begin sort changer something else right and maybe suddenly very flies and go we're not going to touch this that's right yeah my favorite thing is usually I'm using a PowerShell so maybe dance so there's a discontinuity there are there are some rules that wolves out there awesome protections that occasionally at but it's a lot harder than here everyday bars one thing you can do that started
with 2012 r2 here you still protected you to true so they'll come back against me just straightening the words by a lot of non configurable protections I'm gonna Isaiah rebooting good friend hope happens they also released a accent to basically or that over to the older versions of support when those so that was just sort of delving that's at most now does even if you have a 2012 r2 domain controller which you have these other over one though there's over seventy nine zeros you guys probably don't wonder what is there in your mother if you haven't patched it under seven dozen our hands located user groups they don't get it either Fuji sees have to do so
and then windows 8 one greater by the fault will not still work credentials and their discipline or you can see that all older versions of limits which are mainly without of all is not it's not saying it unfortunately because again maybe dance requires eleven looking pretty sure he's not a problem plane house going there to change it this time use your rocket individuals so it gives you the protector user groups probably a people if you want to go to college with richer said yes another good way to mitigate them cats its she proved end-users for meaningless processes but dealer religious writers richer and users probably never need to be able to do and then the cat speeds that to do its
business so that's a real good just general
so group policy purposes is a hacker always like to check right away once I get their domain credentials you know I believe you need domain users and queries the group possibilities and getting access that all the big thing is obviously if your administrator live in big cities and push out things across your environment very easily including setting the local administrator down all those various causes a problem with that is basically the password will never enter sugar camp while it's sorted in encrypted format very efficient energy E is pumped available instead from Microsoft say so it's trivial once your eyes yes there's an example screenshot I had where I haven't made that kind of like that was a main user we consist of
all that one script it gives out does that see where they actually retained the administrator name do something else and then you see the password to see pants were there there is water you can see the the other scripts here below where I'm at there's Mario that were personal use it yeah once you get there things that might not be a you may have man right width:70px for information another accounts you go out Friday servers yeah that just event or
so mitigation strategies liveness what you know dubab which does what you say variety basically said basically does not allow you all use right you can no longer no longer michelle this very the problem though with that patch is it's not backward compatible so then all your requirement is you ever use it in that fashion as follows with their error so most likely your certify this bachelor flower with microsoft released some posters didn't dumpling that a lot of them actually goes out and the surgeon thing up all those days no house with it that it writes located another one that will manage to lose Jeremy did you move through you know I didn't donate them all here I don't yeah
why I can do that why provide the slides out are you talking about that's yeah a little bit straighter that well that's nothing that's that's yeah that's like that's not amended the very day I experience these are specific aster liver for the last half of the tablet market for tomorrow right hey not to ensure that it think it's pretty compatible across so somehow privileged sounds a little bit you know a lot of our problems stem from the misuse of overabundance of privileged accounts in the environment this is a sample the main group
so I think that's a little more interesting accounts that were a little bit of a administrative law administrator big fail that's a when you use in every service at Yale when you finally been the trigger group responder that means is being interactively long time yeah this is a no-no the first place so I'm not sure everyone with responder if you find administrator sending you happy it means that administrator isn't a campus that's being interactively logged into another system way which which is a note other II's these privileged to have administrative rights provided through for group memberships so you can track who's doing what in administrative level so that's always an additional finding of a tech mom whenever I see that yeah
it was interesting on that like that yeah there's a password for the service whip sense okay yeah so you rim brought you that step in there go to we're listening on loud trying to sleep outside drop you in that there so that word was 63% of all data breaches certified hospice investments that's also a privileged accounts this is that one out anything your compliance people are probably beaten every day with you with it give your force then desert probably beat you up with a limit local administrator though it's easy to fix things you're my little egg even worse than that any device where everybody's little a being on a resolution that's also for me I'm
kind of for them and so you know eliminate shared little anything else you know to the engagements where I like Backup Exec this cross little word you do you guess that and also it's like overlapping everywhere and it's like just like spread you're gonna Kitchener wait a minute it's over
that means it logging and alerting all the manatee vision I want him everything's I mean that's gonna do Mike I wanted was created when they're lying in out in there like out in the saline it Bob's working with 85 gazing on Downton I'm gonna do if you launch an agreed wanted nobody actually go ask mom what's going on right as she replied with reality most organizations if they have monitoring they're probably focusing on Brunner there's most likely not by using our monitoring group steps and again they look like the missionary loose I'm saying that you get them up there twice because feel like a killer hy Swiss do it so like I said that's no rocket
science a right we passwords is full full some random passwords out of the they the main floor thought I had run cracks actually got 26,000 that word of it you see these they all meet when there's a bunch of clients you know three to this board there's a lot more about the yeah for sure at least it's nearly
but yeah these are go right the biggest the biggest offender here is just dictionary words Patrick racket using any sort of word dictionary probably for us might happen because they dictated that we're tracking Bob's like those orders everybody's dozen or more you need a characterless at work let's now doesn't matter is how we're going to get less you move up to nine characters these errors strong password exact number that somewhere around there some days work that goat in start with up two years our mafia these GPUs my father you infect a pairs it low through whose route loves with accent really so I think we need to reevaluate what all the telling users that word where's
my identity with a PCI or with or other compliance requirements right here here's that's do the other thing I'm certainly is how can be filled users just use s reuse best oh yeah so we can continue to try to educate our users but it only takes one
yes right those are obviously fall down so for me well I've been telling clients basically a focus on the earth focus on reducing the amount of critters focus all there was that boulders right required in to have Streeters changers around absolutely it was really locking do some damage with locals users I can't get to those
foremost a month most of my desk where I called through these hips you know they just done one teeny little securely not the same I wouldn't optimize them but it blew my job so far yes about longer obviously a spurious 15 16 yeah longer marriages be Kara loo at a certain point having words and you're worthless is probably all right but it's usually like peppered for any bringer lose again he everybody on it there you were shocked by how well they did I little bit me go clear take back we're gonna get this all Network [Laughter]
you know mitigation might be saying passphrases but he did multi-factor authentication even inside right I did one engagement it was PCI Bateman thank one day we motored for inside the main afternoon access everything you need it there they have their government at Merton separated by firewall a good new crops rice get you jump basta chooses to get out of that Network the big pain so all my money on any more there's more alive than that and they were conveniently once I family access is this notion you can meet they completely use their active directory to that gate so then why would they say big that point I did it reveal to client that one goes right down the production while
still imperfect so you know that point I think there are regulations you have to bag on that wouldn't to stop me from ladies in or at least made little heart in that for maintenance tools for the main enemy minions if you kind of cool with I'll do it this is one where you like check out right order shorter it'll short it things like that
minimize ever serving on it working again for my family as a tester or a lot of how we're going in as a breach we're sitting Network yeah sure all of you have users and you know how to use a Facebook how successfully aren't that
the question detergent communist yes I just love the taste of in you mentioned the we tasted before that let's say people maybe camel group also and that right out this way to detail is a little different yeah and there's more information it shows kind of another another hat basically put how they see the look Emily injection of that but and totally because I saw the
[Music] bullets for those minor crashes don't new Gladius one season in that directory so basically pushing everybody over to Africa and then it cracks passwords without actually yeah yeah so it's kind of needed and another good offense for take responder is to just create something that which is out of occasional text like that's where that kind of was like how many know and people are lazy and stupid they try logging with that just long get less efficient that's the base on your fishing you know for sure that's Jones arrived yes okay and then logging mining in place and actually acting on those logs oh my god yeah me just where I said same one with
a powerful right so they got I think that isn't polluting it is powerful big hangover we're all working because I hate it just yet and clan member and I was like man if I really don't like I came back didn't inspire welcome to be but you know then stop thinking it was just sitting there like they will need cognizant alive Robbie they're honest that kind of smells really hard for an organization to see one set up and each product you have your cytolytic don't play nice together and some of the more advanced detection stuff unless you're a scientist it is really difficult sense you know setting an anomaly detection or whatever you're going to do from your
learning what so I mean it takes a lot of time resources right all those it's cool with requires a lot care and feeding and their forties that Mormons don't have I mean in the security field we have a negative employment rate right getting those skills people cost money it's hard for a lot more business to have a little staff and then you have the Sam's out there of the world and those are sometimes pricey but you still have to know that's the whole log and look at the rest else right there might focus gonna bring your hands yes from what I could round if you lose on projects for hours like a lot of us are
they with so much time right and you said there was responders as needed all days to get maybe there's so a good thing to do you want to get it quick is at that point kind of it was probably serving or whatever need much to do so they go some type of we do share that you want in all desk number and ask them to check that say and do the sheriff I asked me to do it and just make sure that it was a misspelling and it'll medially put their present their hash you're responders you'll see excited and you're leaving at the time you want to get the hashes and that's a that's one way that I did
it for yes is greedy fuckabish yeah I love all the dirty jokes responder driving is it's a sometimes I just feel like I get a shower that drone admit ignorance anemia Mississippi game I live in complete UNIX world like every time I touch this UNIX her knack so what is this responder thing that we write as beings right no windows yeah well I'm sorry right it's a juice take advantage of those vulnerabilities are five main servers will be made with twists the reduce boxes just constantly you cross network yes disputing the most common I think so yes I think it's probably my [Music] call you might want to hear all this is a time
[Music] any other question through it was all somebody else over here was my stop [Applause]