Simple Data Exfiltration in a Secure Industry Environment

Show original YouTube description
Show transcript [en]
this is my my my third b sides and uh i i just want to thank you know dan and all the other folks that have put these b-sides on because this this session has been better than the last one and which was better than the one before i'm just so impressed at how good these b-sides uh conferences are so so really you know thanks thanks to to the folks that put in all the work hey so um uh my colleagues wanted me to to to uh title this uh presentation differently they wanted me to call it uh data exfiltration for dummies but uh i i thought that may not be uh very good with my uh professional
standing so i gave it an innocuous name a name that you'll you'll you'll never remember but the premise of the talk is is is that there's lots and lots of ways that you can exfiltrate data even significant amounts of data from from relatively uh uh secure networks uh i'm gonna be talking about uh you know our our top 12. um and what i find is that when i first go to a a client uh six eight of these top 12 will will always work so it's it's pretty common the these these things can be carried out by non-technical users with no elevated privileges i'm not even talking about local admin privileges it's it's very very simple to to be done
uh importantly it's unlikely to be detected by the organization uh in in real time or even in in kind of the the event monitoring stuff um they're it it's it's widely effective across uh virtually all of the networks that i'm going to be in it's it's not zero day or any of the heady stuff that you you know you've been hearing about today the reason for the talk actually my motivation is that there's very very little awareness of these susceptibilities that's probably not a word i want to use i can't say it among the i.t practitioners and what's clear to me is that if you're not aware of these susceptibilities they're not going to be fixed it's not
just that the next rollout of of some of the systems is going to uh uh happen to uh uh pick this up okay so so it's really kind of a bold premise on my part to say that it's so easy to be done uh i mean what makes me say that um just a quick background on me i'm an i.t auditor uh no bullying please and uh i've been running with with my colleagues you know a boutique type of i.t uh audit firm we do some direct uh audits but most of us most of the work that we do is is is outsourced by to cpa firms and and some other firms so in the in the last two years i've
done about uh a hundred uh i uh uh audits that's one a week and boy it feels like one a week uh it's it's predominantly in in regulated industries because those are the the only people that are gonna pay for audit so it's financial institutions banks and credit unions health care hospitals uh health centers and to a much lesser degree these these other areas i have never been to a defense uh network so i'm i'm sure that those are much better off than the financial stuff yeah okay so so the the assumptions um again i'm talking about uh uh an environment in which security is is is mandated meaning that they have requirements to protect the data on
their network so they're supposed to be taking it seriously um the user that that i'm looking at that's going to be exfiltrating the data has no technical training no elevated privileges the data set size could be you know megabytes up to gigabytes per you know i'm not addressing how the the user the malicious user is getting the data i'm assuming that they have some sort of privileges on applications and some harder that they can get to the data set and once they have that data set there they're just trying to figure out how to get it out and do something with it um it organizational detection and what i mean by here is is that it's detection
by the organization via via their routine systems their routine alerting systems or even their event monitoring which which might take place you know a day or two or even up to a week later i'm not talking about the situation that after the data breach occurs that 18 months later their customers find out and it hits the press and then mandiant and verizon are all in there doing their forensics and so i'm i'm talking about a detection by the organization using their normal methods not not forensics the forensic guys can you know do some amazing stuff so okay the uh typical typical environment windows 7 workstations in a windows 7 networking environment pushing typical policies i've already talked about you know the
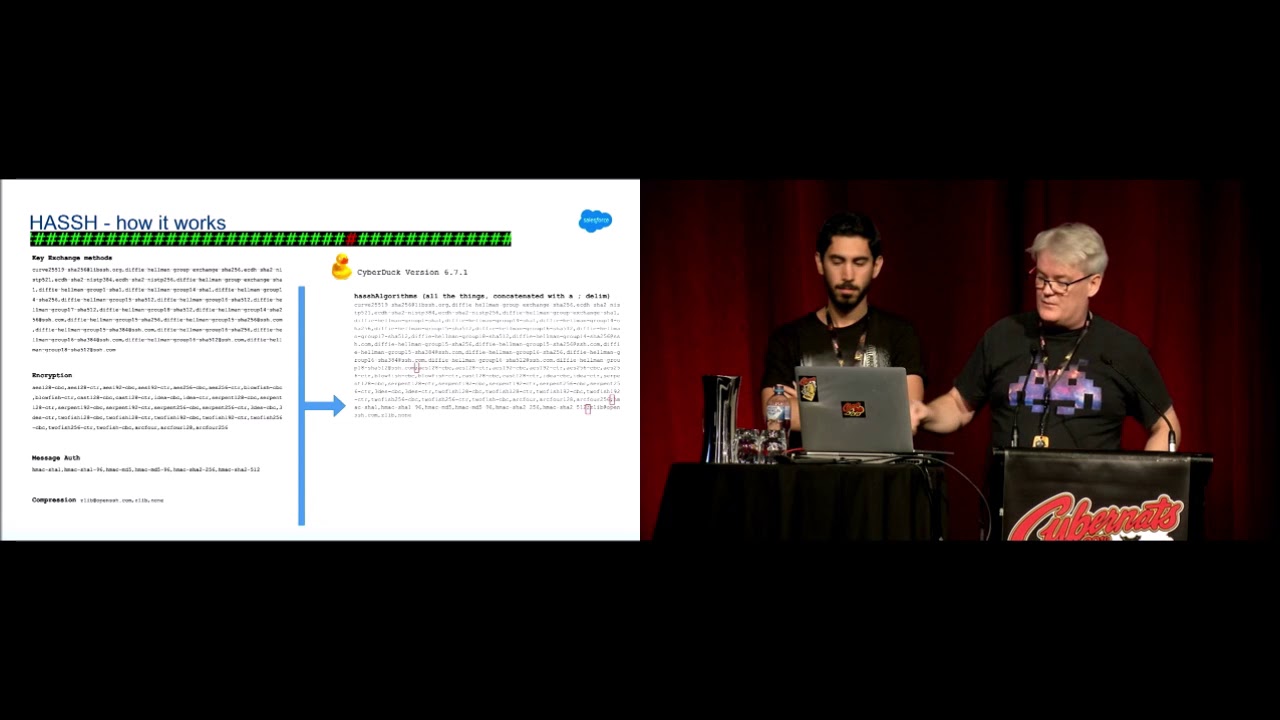
standard user level web content filtering and i've i've i've seen them all endpoint protection systems that are going to be restricting uh read and writes on usb storage devices and cds antivirus system you know operational uh patching systems for windows and third-party apps and i'm assuming that that's all up to date centralized security event monitoring and and alerting frameworks i'm i'm not addressing data exfiltration by by email or or you know someone using an ssl vpn or you know their mobile phone or you know getting doing a bypass on an mdm okay so the the the top 12 that i'm talking about i've categorized into into um bypass methods the the first one is is
is bypassing the endpoint protection system uh so that you can get to rogue storage device the next one is bypassing perimeter protection so you can get direct access to the internet the third one is bypassing web content filtering systems so that you can get to websites that that would allow you to exfiltrate data bypassing firewalls and then bypassing the total network control fully okay so starting off this is the first two this is bypassing endpoint protection systems over on the right i i have a little threat index so the frequency of occurrence is how often i see it and the organizational detection is how often when i'm testing i get caught okay because i test these
things these are all things that i've actually done on on on real networks it's not like my home network that i'm doing this i get to go in as an auditor and do things that other people aren't allowed to do so i'm really talking about then if something is very common and very unlikely to be detected i consider that a high risk so the first the first one is is probably the simplest one and and this one almost always works that is you take your android phone this is not going to work with your your iphone you plug you plug it in and it and it shows up as a network adapter okay you double click on
it and that network adapter magically turns yeah magically see that i love it when people say that you know they already know about this yeah it magically turns into a a usb device okay so what's what what's what's fascinating about that is is that this this bypass works even in the presence of endpoint protection systems which have al which have intentionally or or tried to lock down usb storage devices okay so i'm not saying this isn't like a home network where where you're actually just you know just plugging into your home this is where people are consciously have already tried to to to shut this down so why does it work well part of the reason that it works is is
because it shows up as a as a media device first and then importantly the drivers are already loaded it's not as if you need it's not as if you need drivers for for this these particular usb devices as a matter of fact it'll try to update the drivers if you if you try to if you allow it to update it'll block it because you don't have a local administrative control but the point is is is that when you plug it in it works now you have to be patient because it's going to try to index the phone and if you're using large you know cards it's going to be um it's going to take a while to index it
but this one works almost all the time it's it's just it's just such a such a a simple one and in terms of detection again i get the chance to play with this stuff i have never been caught i just haven't been it's it's it's it and and as an auditor i actually look through the what they are doing to see whether or not they're actually doing the the types of alerting and inspections of their logs that they're supposed to be doing now i find it in the logs obviously because i'm looking for it but in terms of their the types of alerting that they are normally doing it's it doesn't show up so um and even
even you know when they do their their their their reviews a couple and why because there's not there's nothing that's getting blocked here so um to stop this one it's actually pretty tough um so even if you're using you know the lamentions or you know gfi or semantic or whatever you have to you have to make sure that you're stopping this but you often have to push out policies uh you know by way of gpos in order in order to it's like a belt and suspenders you know it's it's not easy to it's not easy to just to stop this one this next one this next one i i find really amusing because um i've never really figured out i've never
been able to use a bluetooth file transfer for for anything useful other than data x filtration so here you plug you plug you plug a legacy bluetooth device in why legacy because the drivers are loaded why all right well because you don't need local admin privileges and and then all of a sudden this thing you know pops up and it says yeah i'm a bluetooth device let me pair to well what of course you pair to your phone now it's secure because you have to put the pin in so that the transfer from the workstation to your phone is going to be very very very secure um but but it it again it works very very well
very rarely do i see that there's even an attempt to block bluetooth devices because usb devices you know they they're all identified differently i mean the storage devices hid devices bluetooth devices network adapters they all show up differently right no one thinks about stopping a a bluetooth device because they're useless right except if you want to exfiltrate data in terms of the detection again as they say i have the opportunity to play i've never been i've never been uh um picked up on it uh and there's no perimeter record here so it's not going out through a um it's not going out through a um a firewall or whatever now forensically i'm not trying to say that that this
couldn't be detected because i mean it's going to show up in in in some windows event logs that there was something inserted i'm not saying that but these are not the type of events they're gonna that are going to go to the network operating center and someone's saying you know someone just did something that that you know i'm gonna go down to their desk and find out what the is going on so okay all right so so um this next one is is uh bypassing the perimeter protections all together and again you can see my thread index over here this one is again extremely common and i've never been picked up on it and and
what you do here is you plug the device in then you put your phone into tethering mode well all of a sudden your phone then shows up as a nic adapter okay and guess what the nic adapters have already been pre-loaded in into into windows seven so no administrative uh privileges are necessary in order to make this work if it asks you to update the the drivers don't do it because then you'll get blocked but you don't have to update the drivers because the ones that are installed work beautifully so um again as a as a nick device this is going to work even in the presence of endpoint control where you're where you're blocking say
usb storage devices okay the next one um the next one is is similar um but it's it's a it's a little bit different and and this is my favorite d-link uh uh usb neck device um and again why did i choose this one it's because it's legacy the drivers are already there and uh this one is is is even better i i don't think i've ever been stopped using this one until the you know i mean i've go back the next year sometimes they stopped me but you know but i've never been stopped on first try on on using this thing so you know 20 bucks data exfiltration to your heart's content the only problem there is you have to
use your phone as a as a as a wi-fi hotspot right so so that you can you know take you know bypass the perimeter uh and go directly out to your uh um you know to to the internet directly the only thing that i would say here that sometimes happens and this is about 50 50 of the time that is when you have both nics uh active sometimes one of them won't be active so you have to the the you might actually have to unplug the the rj45 cable to deactivate the network and then that makes this one active on the workstation all that means is if you're going to do the data exfiltration you'd have to take your
data set that you want to exfiltrate put it on the c drive and then exfiltrate it it's one more step but if you're trying to exfiltrate data you've probably got the time right so so again uh uh endpoint protection systems are unlikely to to to uh alert under was a question oh sorry uh on an allowed event uh again the the the the event is going to be logged but it's not going to raise anybody's concern because it's it's it's it's an okay event and here there's no perimeter protection detection whatsoever a record okay so i've already showed you pictures oh i forgot i forgot this the built-in adapter hey so a couple a couple of
years ago people were going crazy uh updating their workstations from from xp uh to to windows 7. i mean everybody everybody waited to the last month or two to get it done i don't know why but but um a lot of folks bought these uh cheap lenovo um uh think center things i mean i i see them all the time they're about this big they stand on the desk it's it's it's a it's a really nice little package it's got i think it's an i1 with like a gig of ram and it comes equipped with with the cds and that was a joke incidentally um it comes equipped with with a dvd rider and a built-in wi-fi uh nic card
well in the rush to to push all these things out they never disabled the the built-in uh uh wi-fi nick so i find that if if those little things are sitting there they often have the nic cards and then what you do is you just you just enable them you don't even have to do anything you don't have to plug anything they're already there you just use your your phone as as a uh as a hotspot okay so that's what that picture was there in the middle one that's the okay um bypassing uh web content filtering systems um and again i there's a lot of web content filtering systems i've i've gotten to probably see
most of them uh one of the most common bypasses that that i i see is is that the web content filtering system is set up to allow things like bomgar or log me in or go to my pc or our team viewer uh because there's a bit of a mistaken belief that's you know it might it might be necessary so what you do is is you you go to one of these sites uh you there's a free account if you want to you you set it up and then uh you can exfiltrate data using these these remote control devices i i assume everybody's familiar with these things um this isn't working quite as well as
it used to because there's some activex stuff that's now needs to be installed to do the transfer so i think i think uh bomgar and teamviewer are working the best but usually i'm finding now sometimes the activex controls are still getting installed even without local admin privileges i don't quite get it i know there's some weird stuff going on with the enterprise versions but at any rate that that's still a a good one if you want it this next one is new and and that is i i'm seeing i'm seeing uh customers going out to to use office 365 for for their email so that means that they they they use the browser and they have to
get out to office365.com okay i get it so they you open that up but microsoft in order for that to work also requires you to open up the dot live and the dot office i don't get why but they do now everybody probably has a dot live in a dot office account because if you're running windows 10 right it's like i mean they nag you to to do one of these microsoft accounts and that that gives you you know one of these accounts so the whole point here is you've already got a free account that that you're going to be able to use now you're not going to be able to exfiltrate lots of data all at once but
you know 10 meg at a time or 20 meg at a time or whatever it is is you know you can get some get some real stuff and further you could have an office 365 account yourself like like i do so when i'm at my customers i can just log on to my own account and exfiltrate that if i wish um this next one is is is is really insidious and and that is web content filtering systems often default to allowing uncategorized uh or unrated sites and the reason for that is because people complain that if they go to one of these aggregate sites like the new york times or whatever if you if you block uncategorized sites all
that crap that comes from the from the the uh um advertises it all gets blocks and it makes it makes the website look really really really ugly so so it puts this stuff back well what does this mean what this means is is is that if you register a new site for like five bucks or whatever it costs you a godaddy you can you can bypass this or let's say let's say if you um you know want to find a new file sharing system a file sharing site i mean how many of those are are coming on the market now i mean there's a new one every week all you have to do is go out
to the new one it's not going to be categorized it's a file sharing site it probably is going to give you a free account just to test it so that you can you know exfiltrate your data from from from from your secure network uh to a free account and there you go so actually this one's really insidious when we do social engineering we always get a new account right we you know get a new five dollar account we send that we send that link and in the email boom they click on the link there's no controls that link is wide open because they don't they don't block it it's uncapped so i mean this this actually is is a
really serious uh uh control weakness okay so um here the the the the possibilities of organizational detection is a little bit higher because you're going to be you're going to be in in there in the the logs in terms of where you went to and um uh and and [Music] what you saw but again unless you abuse it and show up as is hitting a lot of uh improper sites you're probably going to not get caught again i do this all the time and i've never had anybody come to the desk where i'm auditing okay um bypassing firewalls and you know if this was two or three years ago i probably wouldn't have included this
slide because it would not have been consistent with that this has to be a non-technical user okay so um so in terms of setting up an ftp ftp server to exfiltrate data to a couple of years ago i would say that that's in the realm of the more technically sophisticated no longer right because i mean i don't know last year i went out and i i think i dropped 50 bucks i got one of these netgear cheapo routers you plug your usb device into it and and all of a sudden that usb device pops up on on on the external net as a as an ftp server right it required you know it was maybe two points two
point clicks in order for me with this fifty dollar server to all of a sudden have a um an ftp server that i i could have and it even gave me dynamic dns right so i didn't even have to remember what the ip address if i didn't have a have a static so i consider now ftp in the in the realm of of a of an ftp server in the realm of a [Music] a non-technical user so what i again what i find is is that ftp is is often not blocked uh and sometimes it's not restricted by a source and destination address so if you happen to be on a workstation where it's not
not properly locked down golden and again if if if the firewall is allowing it yeah there'll be a record but again no no alerts rdp again i'd say is is is now in the realm of the non-technical user and what do i mean by that that same fifty dollar netgear thing allowed me to do port forwarding okay holy smokes so for two clicks i was able to to to forward 33.89 to my crappy laptop well i also forwarded 80 as you know to the crappy laptop to the you know 33.89 so that i could connect to rdp on its normal you know port 33.89 or if if they did some outbound filtering which they often don't do anyways
because they're very poor at outbound filtering i could i could always use the universal bypass port right 80 and and it's not like ftp where you need multiple ports which is a much more complex thing so i mean i don't even try to you know put you know ftp you know over port 80 or something like that so this works beautifully it works beautifully and rdp right all you have to do is drag and drop onto onto the the remote rdd you know desktop so i don't know i think everybody knows that windows explorers is a a full ftp client allowing uploading and downloading so you have to use windows explorer if you want to do the ftp thing
um the port forwarding you know point-and-click the detection no alerting is likely i mean you are going to have a record of the connection but it's not going to be um it's not going to have the you know the security guys uh knocking at your desk all right this next one this next one should not even be here this next one i i i think is is is one of the most ridiculous things that that continues to to plague our industry and and and that is um uh booting from from from a a a a live cd or or usb device and the reason that i have this one here is because this is no longer the you know
booting from a usb device or or creating a a bootable usb device is no longer just among the technical realm right because you can get windows 8 on a on a bootable device you can get windows 10 100 bucks iron key will sell you bootable windows 10. um you know the the use of you know linux mint or puppy or or whatever your favorite version is right i mean how difficult is it to make to make a a bootable linux device and some of those you know to to the non-technical user are going to feel very very very homey like like like like windows so um it's very rare that i i find that um
networks have actually locked their their um bios's down and further if they've locked their bioses down they they often don't lock their boot order correctly so they'll still allow booting to a live cd well because it's not a it's not a writable device right well you boot to a live cd and then you just plug in a usb device and you mount that and that's how you exfiltrate data so it's like okay well that's that's that's my dozen um you know it's funny as as an auditor you know i i i i i look at access control uh records all the time until i'm blue in the face one of the things that blows me away
absolutely blows me away is when i look at who has accounts on the network it's always more than you ever think that that that would be there you know especially if they're not totally on top of it and even then so so the who are the threats that that could could use these types of things well the threats are the obvious ones i mean employees the disgruntled you know the insider threat that's the obvious one but i think these other ones are are equally threats and you know the the vendors the contractors the contells consultants who often have elevated privileges and who often don't have any allegiance to to the people that they're serving and and and may have reasons to want to
get you know data off the network business partners uh visitors one of the things is is organizations will give a visitor network privilege to get out to the internet it's like are you kidding me they and you know it's ridiculous that they you know they don't have a fully segregated you know wi-fi network for for that foreign visitors um and i'm not to pick on that except i have i have personal experience knowing about significant intellectual property that was uh exfiltrated on by foreign visitors you know and then temps short-term employees interns summer students i mean even people who who you think oh geez these people can't hurt us well those are the people who who
probably are you know more sophisticated around this thing than a lot of the network matters and for crying out loud leaving auditors on your network you should never do that so all right closing comments um of these of these dozen uh methods uh half or more will work on any site that i've been to in in the last couple of years um the organizations are very very unlikely to to detect the the exfiltration um again in real time a forensic examination would show it but i'm not talking about that the awareness of these bypasses by by the i.t professionals the people who are setting it up is is almost zero um i'm sure that other people are aware of these right i
mean some of the folks i i saw smiling when i talked about that one it was probably your favorite one to exfiltrate that i i'm not the only one who knows about this but by a long shot the reason for the the reason for my presentation here is is is very simple without awareness of these bypasses um the preventative controls are are almost uh never going to be installed so um so that's it uh i would love to hear about your favorite bypass because i bet uh i bet you can take my dozen and more than double it so um any thoughts questions sir have your clients that you've audited that audit process which have had the
best success for mediating against those bypasses and why
so it really depends on the technical management uh for the network and how committed they are to meeting it and i'm not trying to give you one of these bsc answers but one of the things that um one of the things that i know is it depends upon how committed the organization is to closing holes so the simple answer is that when i come back the next year usually seven or eight of these controls are closed and then the year after that the rest get closed because i kind of hammer on them again so um but some of them as they say are more difficult to to to close like they you know this this thing
with the with the android phone because it's you know if if you're using uh i don't know semantic endpoint protection or gfi or whatever it's not simply clicking the button saying shut it off it doesn't you have to do something more you have to push the policy so that becomes a little bit more is do you have complex a suggested framework that you have clients look at or you basically just say you know this is what i did yeah yeah we we've been through it enough so that if they can't figure it out on them by themselves they'll give us a call and you know we can we can point them in the right directions or or connect them with
other folks that we know would be willing to you know serve the community and help them so yeah yeah i mean the worst thing an auditor can do is dump a report on something on somebody that they you know can't fix yeah yeah no we we've been around this so many times that that we kind of know what has to be done i mean we know where to look so yeah so i'm getting sorry uh how often do you see techniques like this versus more sophisticated techniques like ssh or vpn tunnels or
well i i actually wanted to take out remote access sort of out of my my talk because i i think of you know the ability to do exfiltration using using uh facilities that have been provided or you know that's kind of a talk for maybe next year but um um so i i think i think there's a lot of opportunities for people to do you know remote remote type stuff yeah i was just trying to really really think about the absolute simplest ones you know there are more i mean people want if people wanted to certainly if technical people wanted to get data out i mean that's that's that that's possible i was just trying to think of
you know the simple people simple people i didn't mean that they're simple i'm sorry someone back here had had their hand up sir i was going to say if you're using ftp to exfiltrate sensitive data what are you doing to protect it while it's in transit um i will not i mean obviously what i'll do is i'll create you know text file or something like that i i'm not going to actually take my clients data and exfiltrate it i i'm i'm kind of crazy but i'm not that crazy so i i will i will take data that i put on their network and uh because i can because yeah because i can i can get it
on their network as easy as i can get it off to be honest so i'll i'll take something that will demonstrate that i can you know get a good chunk of data out um why why do you ask i'm curious um because what oh i oh yeah yeah yeah right right and certainly not the way i'm using it and and if you're if you want yeah right right oh you're absolutely you're right right your clients normally provide you with a standard workstation configured to their specs or you use your own machine excellent question as a one of the wonderful things about being an auditor is you can be a real jerk so you can go in and say this is
what i i want from you because because i'm i'm being paid by by the board okay so i i can so i get to pick i get to pick the workstation i want and i always use user credentials so i never make the mistake of taking a taking facilities that it gives me because they're always going to be different than the actual production um and i never use any credentials of someone other than someone who i have selected so what i'll do is i'll you know as an auditor i mean you wouldn't believe how lucky i am uh i can i can always kind of pick the right ones to look for you know it's always
you know it's always sally in in auditing that has the elevated credentials or i i mean i'm good at that so yeah but i i i get to choose that i i would never do it with my own i don't i i don't usually even connect connect my my stuff up to their network i don't want them to hose me so bam what if um your experience has been with companies using white listing applications some of your techniques utilize software that might not already be present yeah you know it's funny it's funny you say that because i i would have expected a lot more white listing i i don't see much white listing i i i just don't see it i i hear a lot
of people talking about it but it's when you do is it harder to accentuate it or it's just a different i think it's just a different method because the um the the applications uh that they would whitelist are not going to be problematic for me to use the drivers that i want so because the drivers would already be would already be installed um so i don't i don't think that would be a problem so yeah yeah what has what's made it the most difficult to exfiltrate data out of client networks or is it always easy um gee that's a good question i mean some endpoint protection systems are a little bit better than others for
example i mean a little bit um um but i i always get through i just always do it and and that's again that's the reason for the for the paper is because i i can i mean i've got a dozen you know when you have that many tools one of the tools is going to work um so yeah i i wouldn't say that there's any one particular thing that says geez if they have that you know it's going to be it's become problematic you know it's not like i can say you know semantic endpoint protection with the with the network aware stuff that they have is going to cause me problems causing problems when they scan but
that's that's a different problem so i can't say it yeah yeah so so i wish i could see what you know really sophisticated networks are you know i'd love to you know if anyone wanted to volunteer their network that you know where they work at uh you know fidelity or you know one of the you know bank of america or you know it's you know someone who's who's really i'd love to take the challenge on i'd do it for free actually [Laughter] but so well thank you thank you and and if and if you do want to talk with me privately about your favorite method i'm all yours thank you