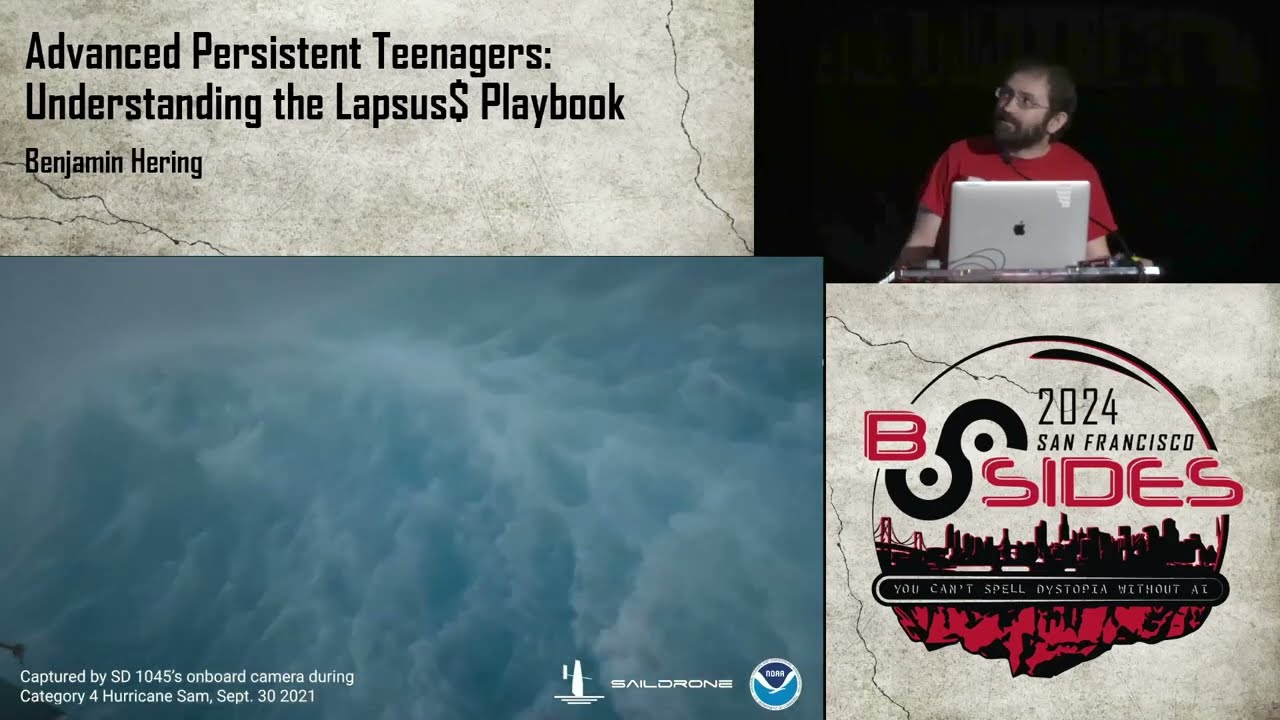
Pentesting: Tips, Tricks and Stories

Show original YouTube description
Show transcript [en]
all right so thank you again everyone for coming and staying and obviously we have a lot of prizes at the end and and giveaways so be sure to stay till the end but but I would like to introduce these two guys I found outside the hall here to present last second just kidding Patrick and Erin they're from rapid7 they have a great presentation so thank you well thanks everybody for sticking around I'm really gonna have a tough time with this kind of thing so I'm used to running around when I give presentations but I got a stay near the microphone because we're recording and all that so if you seen you start wandering over I already told Erin to
make sure to chain me back down here oh yeah well I guess we'll yeah so just tell me to get back or whatever so who are these guys we'll start off my name is Erin or a Ron as I get called all the freaking time can't go anywhere without it so I just have a shirt and I accept it now it's Who I am so I previously was a Knicks administrator I guess kind of doing like SEC DevOps stuff before the second DevOps movement but it was they just called me a Knicks admin I get a fancy title and then I worked as a security admin financial sector and now I pentest over at rapid7 during the financial
sector I did a lot of Blue Team and Red Team type stuff and that kind of transition into my pentest consulting career so it's been fun so far my name is Patrick and I'm a pen tester I previously worked at the Akamai cert but been doing web dev as anybody watched security weekly ever ooh so sometimes Paul lets me be on that whenever Larry has to travel I got a Def Con 401 group up there and I'm also the one that if you follow the layer eight conference Twitter account I spam the heck out of you with messages constantly and if you've been following that as well we're gonna give away a free ticket to the lair a conference at the very end
I get a special person that's gonna throw one of our little swag balls out at the end so we'll do that for anybody else that is interested in that kind of thing but first before we start let's give a round of applause to the organizers and the volunteers of this conference stock up putting on a conference like this is a crap ton of work I sometimes help out it another b-sides that's a little bit north of here at some small town and they're just kind of a lot of work so those are the people that do it so make sure you thank them what else we're gonna be talking about today let's see type of pen test that we do at
rapid7 these are all the different types that we can sometimes do web apps mobile apps internal external network testing all types of social engineering code reviews red team engagements IOT lots of fun stuff but there's only a couple that we're going to be talking about because we're gonna be kind of telling stories tell you different ways that we've done some of these types of tests as well as mitigations as well so you can kind of take these things back and fix them so yeah well kind of tell some stories with them starting with the external so like patrick said we'll have stories and just basic bones you know there's nothing rocket science here it's all super super
basic that's why you know the title is easy ways to make our job harder really easy things to fix really easy ways we get in you know I'd like my job to be more than 30 minutes on a Monday to getting into your network because I'd like to actually you know do challenging attacks and yeah but you find boring ways all the time so we're gonna go over the boring ways please fix those yeah if you work on that side of the house so favorite methods we have like week domain passwords week egress filtering lack of multi-factor authentication and exposed web admin panels we're gonna get over those get into each of those but you know this is very external network
so weak domain passwords the downfall of pretty much every company who has to use passwords as their sole form of authentication will get to multi-factor or later but we usually discover this through a password spraying or a lack of network egress controls so passwords bringing type stuff before we can password spray a portal we have to somehow get usernames and Thank You handy tools like websites like linkedin where everyone wants to say where they work in their names and then you can do Osen and other ways you know the harvester recon ng mal ta go pastebin dumb census data Google you know if they have no sessions they're internally can ask the domain controller one of the other kind of fun
things with this I remember one of the stories I guess a little bit already real quick couple weeks ago had a university and one of the nice things about universities is they have the address books so one of the first things that I wanted to do was to get names because that's the first step that we're actually trying to get here is user names so the way we get user names is through names and the way that we kind of get names is through all these kinds of sources if you're not really familiar with these kinds of things like the harvester is a tool that's in Cali it's pretty awesome recon ng Tim tomes built that it's also
pretty awesome with modules in there as well but one of my favorites is the company address book does anybody have a company address book don't raise your hand because I loved it when they have these kind of things because let's see if you work for like Acme comm one of the things that we love to do is we'll just go to your address book and put in at Acme calm and guess what most address books do they're gonna output everything maybe you got to put in like a wild card or something like that in front of it but it was super easy just kind of dumped the entire company first name last name kind of thing from there it
was just going to be a matter of figuring out what was the actual username format it's very very common I mean especially if you work in a government type organization when you're doing pen tests for cities or anything where you have to have that data publicly exposed because they're you know working in the public sector pretty common to go out there and look up and be able to find an employee directory and sometimes it'll be like the web page is slash hey show me everyone who starts with a slash B and so you just write a quick bash grip you know curl go grab all those pages parse it all grab the user names with some said a knock foo
and next thing you know you have a list of usernames that your spring against something huh I'll get the domain controller on the internal later yeah I know so he bring up ask the domain controller we'll talk about that a little bit no sessions later on we get to the internal side but if you expose your domain controller to the internet one well that's a problem too you should fix that to start - once you're on an internal network sometimes you can just be like hey domain controller give me a list of all users movie through sessions where it doesn't require a username and password except anonymous login like you guys know maybe the net user command and the
Windows domain same thing it's basically that's all it's doing it's asking the domain controller st. give me all your user names you can do the same thing or if you've compromised credentials that's a great way to get all the other user names and service accounts and start password spurring them another option some companies think they're you know stealthy and they go oh well if we don't use first name last name or first initial last name something like that people can't guess our user name so here there's an example the company uses AI UHT 18 what does that mean I have no clue but we were able to use Foca which is an open-source intelligence gathering
tool to go scan the internet for documents and pull metadata so focus best light specializes and getting metadata from documents so if you publish like Word documents to the internet PDFs they have metadata they usually have authors and then if you can find the username format you know since they were so brilliant and decided that we're gonna hide our user names and use these really obscure user names they incrementing them so AI UHT 19 20 21 22 so instead of me having to go search all these user names I was pretty much able to incrementally go through them and find them and then oh so then you can start password spraying at that point and user name enumeration will let him
take that over so a couple of the other ways that we often find what's the valid user name format a lot of times it's just whatever's in front of the @ sign in your email so that's one of the first places first things that I'll try is just kind of go look to see what the email addresses and see what's in front of there another website that you can take a look at hunter IO is kind of nice where they tell you what a lot of different username formats are for companies so that kind of works as well so once we get user names we're trying to actually get access into the company we're trying to log in and get
authentication so we got user names that's half the equation the other half that we need is passwords so what we're gonna try to do now is just kind of guess at passwords but instead of doing brute forcing we're gonna do password spring and there's actually a difference because one of the things that people will often say when we say that we're gonna try to guess password it's like well I get a count lockout so I don't really worry about that it's like okay those account lockout sir those are nice but it's really not gonna stop against this kind of thing so much because what we're doing when you think of the brute forcing and what the lock outs are going
to do is you start thinking that we're just going to go get the top 1000 passwords off of the LinkedIn dump or something like that and throw it at users that's not what we're gonna do that wouldn't work too well so what we do is we have a pretty good idea of what passwords your people like to use and we're gonna show some passwords that I can guarantee are in your network or might even be some people in those rooms passwords I've given this presentation similar presentation before usually to non security people and they come up to me after and go I could have changed my password now okay that's good good to know what was your password by the way
they didn't tell me so what we were what we're going to do is since we know what common passwords are so we're gonna go get all those usernames and try one password is that gonna lock out that's not gonna that's one guess that's not gonna lock out and if we have a pretty good idea of what these pretty weak passwords are eventually we're gonna guess them and one of the things that I've kind of noticed is once you start getting up over three hundred four hundred users accounts we're probably gonna get at least one once you start getting up in the thousands we sometimes get dozens with these weak passwords so there's three that I try to tell people
do not let anybody in your network use these passwords because these are the ones we're going to guess and these work 100% of the time at least one of them usually all three what's one of them okay some variation of password we always see that how is that still there once in a great while I do see literally all lowercase password and that person's just not even trying anymore they just gave up but we do see some of these really secure ones like P at signed dollar sign dollar sign knowing that's like super secure I guess because somebody told them that yeah that's leet stuff so that's one password is virtually always in there what's next good shut it
out there we go a variation of company name it'll take that for 200 so yeah something about the company name that's one of the next things that I'm always gonna throw in there whatever your company name is then maybe the year maybe an exclamation point something like that is always going to be there what's next there we go these guys are on top of this season year why does season year work and that's because of our password policies think of what your password policy is your password policy is generally going to be you need three out of four uppercase lowercase special number right and then we also require that they change their password once every three months makes sense right
because for security so once every three month what else happens every three months seasons change and if you just put the year at the end you're gonna get something new every time so if we do Summer 2018 fall 2018 with an uppercase F for an uppercase s we have our uppercase lowercase in our number and if we really want to be secure we'll put an exclamation point at the end so we get all four okay so yeah those kinds of things are virtually always going to be there so the next thing where do we spray these kind of things where are we going to try them well login portals is certainly a great place VPN is one of my
favorite places because once that works we're in you know a VPN gives you an access to the internal network and another one is your outlook web access your Ola and Ola is pretty awesome because there's Metasploit modules for it that lets you do these kind of things as well there's a Metasploit module called auxilary scanner HTTP oh login where all you got to do is just point it at the IP address for OA with a whole big file of these usernames that we just scavenged up from somewhere and put in one password and say go and it's gonna tell us which ones are valid even better is it kind of does user name enumeration for us we kind of see up there where it
is showing us you know a failed login isn't any good but even better there's another one says failed login but username is valid so it's doing that user name enumeration for us so sometimes when I'm trying to figure out what is the proper username format I'll just throw it into this module and it'll tell me I just use that this week and I did my little happy dance when I guessed right but even better is it'll also tell us when we have a successful login ok so this is again going to be that that same Metasploit module and it probably looks pretty bad and I know a lot of times when we do our presentations we create these little
contrived models to put up here so that we don't actually show customer data this is customer data this was on a pen test that I did he kind of get an idea by the username admin admin that was probably something higher level so most people have an idea of how these levels kind of go you have your regular domain user that's not what this is then sometimes you have a local administrator that's not what this is then you have a domain administrator right that's not what this is then you have an enterprise administrator that's what this is I put this through and because I had this access I was able to see all the groups
in the domain controller and looked up what groups is admin admin in and it was in the enterprise admins group I went over to my person I was working with I was like did you know that the password for your enterprise administrator is one two three four five he said that's the password for my luggage okay anyway all right so yet that's kind of some of the ways that we are able to do these kind of things as far as the the password guessing and of course you know worrying about our getting our best summer ever as well so I guess that's some stories but this is one I can't remember if this is where we want to tell that kind of
fun story anyway like we'll go for it so I was doing this password guessing on this one test and sure enough best summer ever it worked I had you know all my users I start throwing it out and one gets me in so I was spraying against the VPN and I see that I got access and I see that the password was just Summer 2018 I'm like okay this is pretty cool but sure enough it's just about always going to work so just by chance I was like well let's make sure now that I'm in because I you know got my you know inside shell and all that I'm kind of zipping around the network like let me just kind of check
this with crack map exact that's another tool that we like to use against a domain controller one of the nice things about crack map exec when you use it to log into a host it'll tell you if it's a local administrator on that host by saying pwned you know you you own this machine so I took that user that I guessed summer 2018 to get through the VPN and used crack map exec on a domain controller it said pwned I'm like you gotta be kidding me this user with summer 2018 is a domain admin and sure enough because of some other privileges the person was actually just like an accountant or something but for some reason the
accountants had full local administrator rights on a domain controller which I didn't understand and I think they didn't either so we kind of worked our way through that one as well what our remediation well we know that we want stronger better passwords it's probably not a good idea to make people be changing I think NIST also just updated their guidelines recently to tell you don't make people change their their passwords because of that summer 20:18 fall 2018 kind of problem that people are creating weaker passwords the only time that you really want them to be changing their passwords is if there's any kind of indication of compromised if you have a reason to believe that you've
been compromised change the password if there's no reason to believe that there's a compromise going on just let them stick with it as is yeah of course we don't really want to just worry about the security of usernames and passwords so let's put that MFA on things if you can get people to use password managers that's great too I know some people say well that's scary having all your passwords in one place well what's the alternative I guess we can kind of discuss at some point but anytime that we're up against multi-factor authentication it makes our life much harder and that was kind of the title of this make our lives harder so that's one of the ways with that as
well so I think Aaron's going to talk to you about yeah real quick before jumping to that to actually want to back up just a little bit yeah now the story I want to throw a couple things in there so first you have your own login that Patrick was talking about before we don't have a slide in here for it but it was worth a shout out how many of you using outlook 365 instead of like you know oh your own local instance got a few of you in the crowd right how many of you are using Active Directory Federation services in front of that all right we got we got a couple okay it's a fun fact for you if
you're not using a DFS and using 365 all in the cloud it takes your domain the past or the NTDs date file basically which has all the ntlm hashes of user names passwords syncs that up to the cloud and then authentication happens against that up in your o 365 instance it never communicates back to your Active Directory server because of that Microsoft you know feature not bug doesn't want to count lock out it doesn't actually enforce the account lock outs for o 365 so passwords throwing up there is awesome here's another thing passwords bring in o 365 the activities logs that they give you they suck I'll throw that out there people have been saying you know you
need a better way to correlate passwords so there's these giant logs of all these failed logins and you can look up failed logins by IP but you can't look up ok did the same IP login to try a failed login across multiple accounts and so you can't detect that password spray without actually dumping all the logs and writing your own parsing tool to do that we I wrote a PowerShell script with a buddy recently to kind of do that and then look for wherever successful logins happen from an IP doing password spraying we wrote it into the activities API earlier this summer two days before we released the two old mark software the activities API is evil people are
using it for bad and they took it away so it came back about a month later after they fixed some things in it but they took away a lot of the functionality we were using to do that correlation so now you have to export it to an Excel spreadsheet to do that unless you're feeding everything to assume or you're using Active Directory Federation services that's why I brought that up at the start a TFS is basically you log in through there and it relays the communication back to oh and it works directly with your domain controller so you can enforce lock outs you can for stricter access controls and you can you know get those logs to
your sim a lot easier anyway I just want to give a shout out on that moving yeah
yeah so secondary physical device as a key let's say you're you know using a Yubikey something like that to you basically you plug it in and then you have to have that key you plugged into your laptop when you log in with the password so it's something you have like something you own and something you know yeah it's like not SMS you know you're not using your phone at that point you could use the phone as well but some people prefer to use maybe an RSA token you have a you know physical token that generates your key a lot of banks like to use those I've seen that being pretty common until employees leave them in
their desk with a little wafer locks that take point to seconds to pick and that's another rant for another time yeah anything else on the slide awesome so SMB egress we want to talk a little bit here about okay I couldn't guess the password or maybe I guessed a couple accounts but they don't have VPN access they don't have email access externally not much to do there so another way we like to capture passwords is we'd like to send emails with HTML image tags and them or put on an Internet Explorer or sorry a web page a image tag in it but it's not a normal image tag it's an image tag that's making a file reference
so instead of like HTTP website name dot jpg for our file its file colon slash slash and then the path to our server and what that tries to do is windows alt is awesome by the way it tries to authenticate everything for you like seamless integration tell me to go here and I'm gonna you know send your creds along with it and so when Windows authenticates over SMB they use the hash called ntlm v2 or net ntlm v2 and whenever you connect to a file share or connect to something on pork for four or five if your windows and that file share says you need to authenticate the first thing Windows does is it takes the
logged in user password that's trying to get to that file share it takes the hash of that the net and the ntlm hash it does kind of a handshake and authentication attempt sends over the net ntlm v2 hash which you can crack offline we can crack passwords offline a lot quicker than we can guess them you know millions of attempts per second so we try to capture hashes and then we crack those you know more obscure passwords and we do that by putting in this image tag in an email because like I said Microsoft likes to authenticate to everything if you open it up and outlook when you open that image tag in Outlook since it's a Microsoft product
it tries to connect out to the Internet if four four five is allowed to egress from your internal network out to the Internet and you're running on windows opening in an Outlook it's gonna automatically try to authenticate to my rogue server so what do we do first things are exploiting it we stand up an SMB server and the SMB server is basically pretending to be a file share whenever something connects to it over SMB it says oh wait I need you to authenticate with this challenge hash goes back to the client the client goes okay let me take my Windows password hash it with your challenge you know we're gonna send it over and then they
send it over as a net NT Lumbee to then you can start to crack it offline so we stand up our server now we gotta send that email to them I created an outlook plugin because putting HTML and outlook emails it's a little finicky you can only do it if you're using like an VB script so I created a nice little smiley face button plug-in and basically you click on it it you fill out your path here really hard to see in text wise but over here you'd fill out the IP address like file colon two backslashes your IP address or your server and then backslash again some random image signature JPEG whatever and then you
send it and it shows up as they failed to render image when someone opens it they have to click download HTML images that's the caveat unless it's automatically set to download HTML images but people like to click that when they see this little X they're like oh maybe that's something important download images and then cool we get a bite when someone opens it up we get their hash and then we have their hash to try and crack it offline and find other passwords you know this one was winter 2018 exclamation point I guess we could have guessed that as well but here's an example of kind of what the net ntlm v2 hash looks like we use
hash cat we put a word list at it and then we like mutate it with a bunch of different rules so we take all these common dictionary words and try every permutation of it using app signs or a symbols adding exclamation points to the end you know common user behavior rules that you see we modify our list with that and run it through hash cut and you know try and crack things so quick story on that flashback for a second when I talked about you had to click download images that's true you have to click download images and outlook however what if someone forwards that email internally when you send it from an external standpoint they have to click download
images because an untrusted sender it's an unknown sender but if you're inside an organization and you send that email to another employee and you know it becomes a trusted email and it automatically downloads the images you know my fake SMB images here and so I had a test and I had figured out the head for four four four four five egress enabled and I'm like okay how can I get there sock I want to start cracking everyone in the sock I'm like well what do users usually do when they get a phishing email what's the first thing they do with that phishing email anyone know okay send a security team a a smart process for that is to save it or have a
button that automatically does it for the user but if you're gonna train them then train them on the response of save the email to a message file attach that and send it over to you so you can analyze it and that preserves all the initial headers what a lot of users just go oh no bad email forward put an information security distro list we're good to go so that's what we did we sent an email and we just put like some Russian text in there and just made it look super fishy intentionally with our little you know image in there we thought I was sent it to the whole accounting team and one of them are
gonna freak out and send it over to security thinking they're savvy and so they did security gets it it's automatically trusted now it's forwarded from one of the users internally it hits the sock team and before they knew what was going on all they have to do is click an Outlook the preview button like you don't have to open the email just click preview there hashes are rolling in and then we start cracking them and you know sock elevated users they have access to everything go in you can and we'll talk about pass the hash later if four four five is open externally what yeah well talk about that a little bit but not pass the hash though not with
net ntlm be to you can do relaying the hash and so we'll talk about the differences when we get to the internal but yeah so we got that hash and we got a bunch of hashes flying in we start cracking the sock user hashes and someone had a password it was like um Splunk admin 29 or sorry 2018 something random like that maybe they just got done with flunked training they thought they were clever to do that you know and so they put it in there we cracked it in a few minutes we had access as then they had to factor enabled on everything except for their email setup well their VPN required a certificate that was the
first part you had to have a SSL cert to get on to the VPN SSL cert but they you know client certificate so it's kind of two factors something you have and something you know with your password but they also had it set up so that their Outlook externally they had the EWS path open and so EWS is kind of like how your phone authenticates it's also kind of for API calls and you can authenticate and dump an entire email INBOX bypassing two-factor you can't put two factor on EWS if you leave that endpoint open on outlook web access they left it open we use this password dumped all his emails and lo and behold he was
kind of a new hire and someone had sent him like Oh his or maybe it was a his cert that's what was his had expired the year before for his VPN and someone emailed him the new cert for the VPN access then you did for the Cisco buses that will be PN I'm like awesome I have your cert I have your password and I logged into VPN it's a sock employee and now we're internal so yeah SMB image tags great way to get hashes make sure you don't allow for four or five egress to the Internet you don't need it most ISPs block this intentionally under mediation but most ISPs block this from home users so it's hard to test this at
your home because your ISP is like you don't need file share access to the Internet over four four five that's a bad idea we're gonna block it for you but for companies they're like you do it your problem not mine so they leave all your ports open they have to for business use your cases but yeah make sure you restrict that alright you want to take over the exposed or oh no actually sorry I'm gonna continue in here yeah yeah cuz the next story so next one we like to look for is exposed administrative dashboards to the Internet so we get hashes we get login usernames all that sometimes we can't get them them or sometimes everything's too
factored there's no way we're getting in that way so we're gonna look for some kind of admin dashboard PHP myadmin is option WordPress admin printers web cameras Tomcat and JBoss the thing is when you have an admin dashboard for a web page admin dashboards usually that you deploy new web pages or deploy code for example Tomcat lets you deploy war files or you know you and war files can run retort or shellcode upload that PHP myadmin you can do a bunch of different sequel injection type commands you can also deploy modules out there and have it run things custom admin panels usually have some kind of feature and so a story of that is we were doing a pen
test and the devs had a admin panel out on the internet and no one was opening our SMB image tags or maybe egress wasn't allowed from client workstations that was all blocked but they had this admin server out on the internet that and they were working on this new dev website and there was no customer data on it so they thought okay who cares if we exposed the panel and the login for this panel was admin admin so great passwords again if you find a theme throughout our entire talk it's that people are terrible at making passwords so don't only rely on passwords but anyway so we find this admin panel we log in and very limited functionality so
maybe again that's why I didn't care at the time they had the ability to pretty much set a log file path location to change the username and password and I think it was to modify it use it modify like the index.html page so I guess you could you know inject some malicious JavaScript there but there wasn't any way to upload like a malicious page at all I couldn't upload like an ASP page but we noticed the whole thing was running on a Windows server and so we thought maybe the server can SMB egress to the Internet and there was a log file path well like I said before if you put in you know the URI path using a file
share reference instead of like HTTP so he used two backslashes to a remote server it's gonna try and connect to it so we did two backslashes to a remote server which was our server on the Internet apparently this server was in their DMZ which he didn't allow or didn't have any four-45 egress restrictions and then we you know saved the log file location and next thing you know the server's trying to output log files to our server and we're replying back with authenticate to me first and so it authenticates and it's running as the domain administrator user for their company so it's just administrator with their domains we have that hash and that hatch was or we cracked it and it
was like Heinz ketchup 500 something like that I just cracked it pretty quick um and now we have the domain admin hash and that was pretty awesome you know from external straight to domain admin hash we still had to find another [ __ ] in the armor to get internal at that point but it's still another easy way to capture a password hash and then once we get internal access we'll kick it over to Patrick for that I'm gonna back up on him now so this is one of my favorite things to kind of do on the pen test as well and one of the ways that you can do this there's a tool called eyewitness
that will go ahead and screenshot whatever is at the web ports so one of the things you can do is you can kind of go through and find all your open web ports point eyewitness at it and it'll show you a screenshot of whatever is at that point and a lot of times what we do you know we'll also do this with the internal but it's fun to do with the externals as well to see what's there and sometimes when we get things like JBoss like Tomcat and these kind of things or some of the other administrative dashboards web cameras and these kind of fun things Google is your friend so one of my favorite things
to do at that point is what is the default password for whatever the service is and some - way too high percentage of the time whatever the default password is does get us in I remember being at one company one time and found a web camera that was wide open wasn't even a password on it and it was pointed what looked like you know I'm looking in there and I see like server racks and cages in front of it I'm like this looks an awful like a data center and you can kind of move the camera around you can see people walking around like this is wide open to the internet anybody can kind of see this
kind of thing so I'm doing the the debrief at the end of the week with the customer and kind of waiting I saved that one for the end because we're sitting in the room with all the c-level people and all the other managers and things like that and I'd popped that one up at the end and it was just a screenshot of the the web camera being wide open to the Internet they're all looking and it's like is that our data center and the guy the one that was in charge of the whole network was like yeah that's our data center open to the Internet and they were like why can you just get access to that and I'm looking
I'm like I have no idea why it's that way and he just kind of really got mad he's like next time we get a phone call at 3:00 a.m. from our NOC you can deal with that kind of thing I'm just like all I care about is that you password protect him and I don't I don't care if it's still available to the Internet kind of thing but yeah so those are some of the ways that you can do it I witness is a great tool to find these kind of things and then once you find these open dashboards on your own networks that you can play with test out some default passwords and see if they've been
changed all right so we get our internal access so fortunately about halfway through and halfway through our slide so that kind of works out pretty well here are some of the favorite ways and by favorite we mean like super easy because we're lazy we want the easiest way in so whatever is gonna be the easiest way in is kind of what we're gonna try first and these are some of the first ones that we are going to look for some of these things like the the black of least privilege we go for the LOA Minard like basically we just sit there listening saying can we have your hashes and sometimes network said yeah sure there
you go whether you have the SMB signing on so we can then start relaying hashes around the network of playing with things like mini cats looking to see if your clear text passwords are just kind of stored in memory yeah oh sit with the LM in r1 yeah all right so the question is are we sitting on the inside network with a sniffer we're sitting on the inside Network for some of these will use a sniffer but others it might be that we just plugged in so sometimes just being in a network tap is good enough kind of refrig it and another word too so yeah this is basically we showed some ways we get in externally
now we're internal so we got in from the external maybe we got on your VPN we broke out of Citrix and now we're internal we sent a phishing email we're internal whatever way we did to go from external to internal that's where this begins or you just hired us to plop down inside your network and start finding fun things well I am I don't want to speak for you but yeah and I remember one time going for a programmers job one time and I don't know if anybody else ever asks this question of programmers it's one of the best questions to ask somebody that's a developer programmer and to see if they really understand it just as a
programmer developer are you lazy I remember the first time thinking like are they asking this question for and the correct answers yes I'm lazy and the reason that you want a developer programmer to say yes they're lazy because you don't want them rewriting the same code over and over again you want a good developer that knows how to okay but we're not talking about that stuff today all right so the first thing we have our lack of principle of least privilege I think one of the the notes that I have in here is to make sure that your administrators are using their proper administrator accounts like they should be notice that your domain administrator privilege or account is
not called the check email or surf the Internet level of privilege so anybody that is a domain admin should only be using that account to do domain administration if they're doing anything else they're doing it wrong okay and they should certainly have different accounts for those kinds of things as well so make sure that we have the proper levels of privilege with these accounts because these are the kinds of accounts that we're looking for and when they get misused and they're using them in the wrong places there might be a pen tester coming by or somebody worse they just kind of scoop that kind of stuff up as well and one of the other kind of fun things to do as
well sometimes when they tell us that they have Network segregation right yeah separate networks that aren't really connected all that well okay so once we kind of get one domain admin account one of the first things that we're gonna try to do it can we log into the other one with that same account and all too often that answer is yes so we want to make sure that those kinds of things are separate as well this one isn't really going to be a principle of least privilege but more of a bad thing that I see a lot do you see anything in common with these two or if you don't really see it immediately how about now
okay oh I see this way too often it's one of my favorite things to do and it's one of those things that make administrators hate me is that I will go through and I will find the administrator password hash and your regular user password hash for the same person and compare them because guess what if the two hashes are the same the passwords the same so to me that's the same account if you have the same password on both so all too often this is the case in there once we start pulling out the hashes we see that kind of thing as well so yeah now we have our legacy broadcast we have our element our
NetBIOS kinds of things which is really just a way to that's the best way to describe eliminar not BIOS kinds of things all these workstations are talking on the network and they're constantly asking who is this and you know that person's supposed to reply or somebody's supposed to reply and say I know who that is but you know instead we reply and say I'm that person give me your hash and they authenticate to us because like I said Windows loves to just authenticate to everything I can authenticate to that's probably the best way down that's my that's kind of a good way that a machine might be looking for let's say a file share I mean it says
hey DNS where do I find this file share in DNS goes I don't know so it says okay well then how about by this IP address who is this IP address in the file share should say that's me but one of the things that we like to do is we kind of sit in between and we create this like race condition and say no that's me and since like Aaron said Windows loves to help and loves to authenticate once we say nope that's actually awesome say okay here's here's my password hash and we have tools that we kind of use that for as well so one of the best tools and this is usually like one of the first
things that I'll actually do when I am working inside the network even before I've done anything else at all I'll start up this tool called responder and what responder does is it just sits there and listens for this kind of traffic and one of the nice things is that if it if the network is going to be vulnerable to this then as soon as responder is able to detect that somebody one of the machines inside of the network is looking and can't find exactly what it's looking for responder will tell that that machine that's me give me your password hash and it immediately comes back once I see if there's any kind of traffic going on
there I kind of get a little bit excited and happy and it starts setting up other things I'm gonna be a little bit more fun to do with this well there's also a Metasploit module it does the same thing but when you have responder set up and it's as easy as just typing in responder - i eth0 off it goes it runs it's all kind of nice capturing hashes that way and responders gonna capture one of those ntlm v2 hashes so again we just have to crack that offline or what we can do is we can relay it which so coming back to the question you asked earlier can we pass an NT LMB to hash
the answer is no ntlm v2 is salted every single one is different that's what that challenge response code is that responder provides maybe in one of our slides for the Metasploit module actually you saw I was like a string of 1 1 2 2 3 4 going all the way to 8 at the end that's a challenge response hash and so Windows is actually going to take and create a unique hash salted with that response so every single time you get a hash for even the same user it's going to be different and you have to crack it and so it makes it a little slower to crack and that ntlm v2 hash simply because it's not like you can
take you know ten different ntlm v2 hashes and take each one of them compile it to an ntlm v2 without any kind of salt or anything and then compare them against those other ntlm v2 so it doesn't work so you can't do like rainbow table attacks instead you have to compute every single word in your dictionary when you're cracking to that ntlm - v2 with the specific salt to get the you know final hash that it should be to compare and see if they're the same so that means you also can't pass it because it's not something you can just say you know have my hash here it works as authentication if we were to
backup let me see many slides back it is yeah I'm just gonna fly back I'm sorry so if you see these hashes here these are ntlm hashes these are the hashes that are on your domain controller for all your users and that NTDs that file I was talking about these are passable you can take the ntlm hash and you can pass it as a form of authentication over port four or five and windows just accepts it because it's pretty much the equivalent of having the password unless you're logging in like a web panel that requires you know having the password instead of ntlm so yeah just reference that and so now we can talk about
replaying then so while we can't pass the hash with a net ntlm v2 which is what we're gonna capture with responder or SMB image tag or by you know standing up a rogue SMB server and somehow getting someone to authenticate to our server we can relay it and the relaying process is pretty simple there's one thing required though I don't know if we have it up there oh yeah so find SMB host without message signing required if you it's a default for Windows so Windows port 45 SMB if you were to scan your network with the ball and scanner and it comes back and it says you know you don't require or require SMB signing
you should pay attention to let that's bad because people can relay these hashes now so make sure all of your hosts require SMB signing oh if you don't require SMB signing we can do a very simple man and middle attack I apologize it might be hard to read some of the texts I'm gonna try and walk through right here though this if I can turn this so I can point more all right can you guys still hear me are we good okay away from mic just a little bit so we're gonna start with our attacker our attacker is gonna be running responder he's gonna be replying to people on the network trying to get people to
authenticate to it once you get someone to authenticate so in this case step one is the victim up top the green line there and the victims go into the attacker because the attacker got them to do it and they're saying hey can I have fun a cape to you the attacker over SMB and the attacker is like yeah hold on hold on I server over here this target without SMB signing can I have found a Kate over SMB and the server is like yeah but all's you have to do is encrypt this challenge I'm giving you with your password hash and then send it back to me and the attacker is like I hold on
server let's go back to the victim victim here's this challenge I got you just need to encrypt it with your you know password hash and send it back to me and the victims like okay cool here's my encrypted challenge and the attacker is like all right now I got the encrypted challenge hey target server you know here it all is I'm technically this victim over here can I authenticate to you and the server is like sure access granted authenticate over port 445 we're good to go the attackers like awesome execute this command you know four four five is great for Windows administration type stuff so you can use WMI the windows management instrumentation and implementation yeah
either way PS exec is another option you know be calm you have all these different options to go ahead and execute commands remotely over port four or five if they're a local admin on the server but not a local admin on the server you can still try and dump session information like if it's a domain controller you can dump all the users in the domain and all the groups that way so that's another option but usually we're trying to relay admin hashes at this point and then we go back to the victim at the very end and we're like a sorry access is denied but the attacker has already established a session with the target so that's how
relaying works remediation for both responder and for SME relaying the first is disabled ll M&R and NB TNS on your network these are legacy broadcast protocols they're not needed anymore but they're on by default in Windows so go ahead and disable them you can do it through group policy it's pretty simple follow a principle of least privilege because like I said we're looking for those admin hashes we're trying to use admin hashes to get them into a you know relay I'm do a server or crack them so we can just do all of our lateral movement over port 4 or 4 or 5 but if your users aren't running as a domain admin on their workstations then they're
not authenticating to our SMB server as domain admin and therefore we can't really use their hash to go do something bad so make sure users on their workstations when they log in they're not logging in as at a privileged user we'll get into that later when we talk about mimic at 2i it's another bad idea finally if you also require SMB signing this is going to prevent your relaying so we can't just relay hashes because it requires a special signing between the client and the server and so the attacker can't be in the center doing that man the middle attack and then another option for preventing well if you're doing principle of least privilege using laps as well might not
apply for the SMB type stuff there but if we're able to compromise a host and we have to dump that host so over port 4 4 5 we dumped the local admin hash on a server or we dumped the local admin hash on another workstation let's say we relay your hash back to our workstation and all users in the domain are also local admins on workstations domain users equals in local group we didn't dump the hashes off those workstations with that one relay if that local admin hashed that ntlm hash because when you dump those off of workstation there the ntlm we can pass it to all the other workstations and servers in the network and if you're
using the same password across all your servers and workstations for the local admin account we now have access to all of them so laps is basically it's a password solution inside Microsoft inside Windows that automatically randomizes at the local admin password across all of your workstations and your domain or your main servers and then you can take and get that by being a domain admin and pulling it from the Active Directory domain controller you can go into Active Directory and look up the local admin password for each workstation and server so we always recommend lamps that was a mouthful sorry let's have a story so I had this client and we've conducted pen test forum for three years and we beat them
to death with weak passwords and finally they said screw it 16 character passwords for is not sorry 12 character passwords for standard users they had complexity that dictionary checking and then any admin user had to have 24 character password and above that's strong I mean well if they're not using common dictionary words or if they're chaining them together in a random format I'm not going to crack them even if I get the ntlm BTU hash and so that's what I did I got the ntlm v2 hash and I couldn't crack it and my point of contact just had a smirky grin on his face like aha can't get into any of my stuff now because we had used his hash to the past
three years prior cracked it and then gotten anything so it's always great when you uncover you're pouring a contacts password they hate you for it and you love yourself for it uh-huh so he really challenged us was here it's like you're not gonna use my account for anything but the one thing they didn't do is they did not implement a principle of least privilege and we told them over and over but they're like no well every user needs to be a local admin on their workstation I give up like why don't you just have like a second account that when they need to do that local admin stuff they can privilege escalate to it briefly you know just it popped up the
prompt and so it Center you know username a password enter a user admin user and a password that there so it's not like you're logged in as that user anyway we were beaten the dead horse they're asking them and they kept saying no year-over-year so then we came in and we did SMB relaying and we sat down first thing we did was we sent him an email with an image tag and he thought he was gonna be cocky and so he immediately clicked download images because he's like you can't crack my hash ha I don't care if download images but what we had at doing was relaying back to his own workstation if you do it over one port and then like
we had him do it for like a cred is purely was like coming over port 80 or 443 for HTML off prompt like a basic auth prompt and then you can relay that back to 445 on his own host we knew he's a local admin on his own host so basically when he clicked download images we just relayed it back to his laptop and then dumped the local admin hash off his laptop and you know it's only for his laptop so we pwned his laptop in the first 10 minutes we were there once we did that we dumped his password from clear text in memory and that actually brings us to our next finding credentials cache in memory so
how many of you guys have you know I've heard about credentials being cached on Windows it's very common thing a lot all right awesome so here all aware of the dangers of LS ass and everything Windows tries to do to protect passwords and they fail at ahead you want actually take away else ass you know I'll keep talking on so for else ass stuff it else ass runs on every system this is the local system authentication authority I'm blanking on terms are in ours up to late drinking Oh security authority subsystem service thank you I was way off Wow anyway I just known as L SAS IC l SAS and I go for that process to dump creds
from memory anyway runs in every window system it's gonna cash the credentials in clear text in memory if you you know have it configured that way which any Windows host Windows 7 and below Windows Server 2008 and Windows 7 they're automatically set to cache credentials clear text in memory so if I become local admin on a workstation I can grab the L SAS process by elevating to the system user and once I grab that I can scan through it with like mini cats let's say it's a tool and mini cats will pull out all those clear text passwords that are cached and so you can have a super long password I'm still gonna grab it out of memory
windows 8.1 they're like alright you know what we can't can't they're all sorry backup windows 7 you can patch this there's a past you could apply for the new to have to set a registry key to say don't cash aw digest passwords in clear-text but it still caches the hash the ntlm hash that's good enough for me if I grab the hash I can pass it around the network so I can still get access to it Windows 8 Windows 10 they tried to create the L SAS process as a very elevated process which even system can't access anymore the system user should not be able to access else ass unless you've reboot the machine with a
registry key set to say bring it out of this privileged mode so that I can access it again I don't know why I see organizations without that set all the time so make sure that set at least that L SAS is running above system level so we can't access it and dump you know credentials from memory but yeah the whole goal of else s get clear text credentials or get hashes to pass so mini cats the tool I had mentioned there's plenty of ways to get this to run on a box you have to be local admin or sorry not local admin if you have to have admin rights on the box to be able
to grab the L SAS process you can run tools like crack map exec and say login over 4 or 5 with this hash and give me credentials for memory you know run this mini cats PowerShell script basically a PowerShell umpire has one reporter Metasploit has one powersport has one my personal favorite method if you're not trying to automate and do things very fast is just logging into the box with RDP or just getting onto it for 45 and get a command shell and then use proc dump so marks off sysinternals tool or just right-clicking taxman jerem proc dump you do a dump file of else ass to else a CMP is the default it goes to you
take that offline and then you analyze it offline with movie cats that way you're not running mini cats on a box which pretty much every antivirus solution knows what it is a lot of next-gen AVS see you touching the L SAS process and they freak out and they alert on it at least they might not be able to stop you they try to what they might not be able to and so they at least alert on L SAS being dumped so that's a good thing a positive of next-gen a B unless you're running one that can be bypassed by just moving the directory that it's running in I'm not gonna say the name cuz they
asked everyone to remove that from the internet censorship anyway so we have mini cats running in Metasploit so we have a shell on a host I know missus Empire I'm sorry we have an empire module running we're running as admin and we just type in mini cats it's as easy as that we got the ntlm password hash and then w digest is gonna cash it in clear-text and so we see justin has the password exclamation point J and then one two three four five six seven eight nine zero super secure Justin but it is lab so yeah that's you know you can use mini cats through multiple means to get hashes another option if you want to
just be rogue and be a bull in a china shop crack map exact with SMB once you've captured one account that can login everywhere so let's say I get that local admin hash you're not using laps everywhere and I want to try and get clear text passwords from all your users all your DA's so I can just have the clear text passwords to use elsewhere I can use crack meth exec pass in the local admin hash and spray it across the whole network or a port for four or five authenticates to all these machines and these machines run mini cats for me because crack map exec is telling them hey run this PowerShell mini cats
command and give me the output and so now I'm just dumping clear text passwords from tons of different targets and you know sometimes they might not be clear text because they could have W digests clear text disabled but at least I get their ntlm password hash and I can pass it anywhere after that so that's a really quick way to spray the whole network and just get way too many creds if you're using a tool to detect you know logins across the network rapidly like that then you know again detect this attack it's not very stealthy but a lot of people still don't do that they don't have logging to look for you know the same account just logged into a
thousand servers in one second like I think that's a red flag I don't know man maybe it's not maybe your admins do that all the time but yeah yes yes yep people take it out of that I don't know why so yeah sis admin life so yeah remediation like I was talking about you have Windows 7 Windows 8 2008 if you have these operating systems 8 actually I'm sorry 8 doesn't run in the privileged so you can still get the ntlm hashes it's well eight didn't 8.1 does so I misspoke earlier when I just said 8 blanket but yeah if you're running on the older and you haven't migrated up yet if you're still running Windows 7
because you know everyone knows it took 10 years to get off xp for people so it's gonna take 10 to 12 years for Windows 7 to 10 or above you can you're not you know you're not out of luck you can at least get rid of the clear text passwords by setting this registry key and installing that patch but the ntlm hashes can still be extracted so that's the risk you balance you should probably run laps and make sure that no one's logging in as local admin on their workstation or sorry domain admin on the workstation because then you can grab that hash Windows 8.1 you prevents access to LS ass a print 1 @ above you prevent access
to LS ass there's a less a registry key to prevent you from grabbing that so yeah make sure your reg key is set all right storytime so did you want to do the multi relay here yeah sure fly by I actually pulled this through a tldr basically there's another great way for cache credentials the central kaz server so central authentication server these are like a goldmine everyone in the year company authenticates to them if you can ever get to that and dump credentials and clear text and memory there you pretty much get everyone's credentials in clear text so the story was just basically you find a cache and SS admins like the name their cat server
like cazzo one domain com so you find it that way and then you target it and you dump everyone's credentials in clear-text and it's great test you or the password alright do you be password storage so another option is if you're not using laps if you're trying to set the same local admin password across all these workstations you might use group policy preferences which is Microsoft they released the option to do this where you could use group policy preferences enact group stuff XML file to store the local admin password and AES 256-bit encrypted string and then whenever your workstations got it they decree to date and they set their local admin password to this while Microsoft and
sometime before 2012 was amazing like they always are and they disclosed AES private key on MSDN and so that key meant we could decrypt that password and it was the same across all environments and so any user who has actually successful which is every domain user domain users gets to assist Paul because that's your login scripts that's everything was able to go and find the group's out XML file and then decrypt your local admin password which is used across your entire environment because you're setting it the same so the first thing we do when we get creds is well you know let's say we responder we crack a hash it's a local account we connect
to the domain controller or four four five look for groups that XML decrypt that password and you know get local admin to everything in the environment any user can do it and so Metasploit has a module SMB enum GPP super simple put in username put in password put in domain controller go search for that file and it decrypts it okay so real quick forgetting this is a quick story how we got the username we were doing a pen test one time and we have any user names passwords ring wasn't working but instead we were able to go to a printer a Xerox printer and that Xerox printer had their credentials to get to the address book from the domain controller
so we were able to go to the Xerox printer login as admin admin the default admin for their web page login changed the LDAP server that was authenticating to to say authenticate to me and Xerox instead of passing any kind of hash or anything fat with LDAP just straight up sends you the credentials and clear text so we open the netcat listener on our server change the LDAP server for Xerox it passes the domain username and password we logged in with that dump GPP credentials and we're domain admin within like the first 15 minutes of walking insight to this company it happens all the time remediation first apply a patch GPP is not valid anymore Microsoft doesn't
recommend it they say use laps big issue though once you apply this patch it doesn't delete groups out XML if you still have sis admins using groups out XML from ten years ago five years ago whatever it's still out there if they haven't deleted it and you can still go get that password hash and I'm willing to bet money that that password or sorry that not password hash but local password I'm willing about money it's reused somewhere else in your environment so we spray that same password and find other you know legacy accounts configured with that password and if you want to fly under this this is my father were taken so long I told
Aaron that we needed to talk for a longer and clearly we've done that so a couple more real quick ways does anybody remember eternal blue ms 17 not pet yet kind of stuff that was released in April of 2017 and Microsoft released this patch well it's all still going to be vulnerable and you also remember MSO 8 o 67 and how nice that really was where you just kind of like do a buffer overflow and you get system level access that's what this is this is the new MSO 8 o 67 still exists we don't need creds anything like that to get system level access so it's a Metasploit module that we can kind of
just not really the easiest thing to see but we just kind of find out which host is gonna be vulnerable throw this Metasploit module at it gets us some meterpreter shell full system level access and now we can do all the kind of stuff that you saw earlier especially with like mini cats yep there we go we see our meterpreter how to patch that kind of thing have good patch management it's that simple as just patching for MS 1701 zero same thing with Kerberos if you've not heard about Kerberos it's again going to be a feature not a bug where this is just how it works once we get any kind of level of user creds in the system there are
lots of different tools that you can kind of use that says find all the SP NS inside of Kerberos and give us the Kerberos hashes that we can then crack offline again it's just how it works once we get a level of creds in order to be able to get in how do we fix this kind of thing just patch it no even Sir Paul knows that we just want to patch things up sorry yep so strong passwords so if we can't crack that Kerberos hash that we get then it's useless for us Thanks overall mitigations you know kind of get a slide for all the kind of stuff that we went through seems that we're recording so
you can kind of go through but we're also more than happy to share our slides with anybody that wants these kinds of things and you can contact us with these kinds of things it seems that we kind of used more than all of our time so and I am more than happy to take questions outside the room so we don't distract anything like that but we also want to McKenna I got my security girl here to throw the ball out to give if anybody wants to come to layer eight conference on June 8th and Provence all about social engineering OSINT gathering a whole conference all about that she's gonna turn her back and throw it if
anybody back up so if anybody wants to come if you if you catch the ball and you don't want to come just give it to somebody else who does and it gets you a free ticket come see me with it and we'll we'll get you in backup nobody wins it's okay a profit thank you very much thank you