Abusing Leaked Data and Vulnerable User Assets on Android
Show original YouTube description
Show transcript [en]
so since for addiction I'm Tomas and so today I will talk about Android based on the prototype project and system based on a lot of back emptying and amputee and so you may have seen me in the past years already talking about Android security technically speaking like Viet realization energy structure hooking and so today we will still talk about Android but contrary to previous talks which for many technical with systems that by basically not doing any technical things we can still do a lot of great things regarding Android security and the objective of this talk today is to review data management and Android so when I say data I mean user data and not application
data that we could assets and basically is to review a lot of bad practices that we still see nowaday and data management by application developers and to introduce how we can how they should feel that or so how can we use the fact that they don't use bad practices that they don't do good practices to basically hack application data and also I will make us a society apart a about like baboon tree hunting and Android and well what was the experience for couple of minutes about this kind of activity if once a what that expose were getting under is not a brand new topic I would say that yeah when we focus about data leaks and Android will mainly focus on
like the system leaks like basic core application leagues such as before we had how we can vertically retrieve the user identity based on the stock app miss configuration today the talk would be much more like about like any developed app with huge user base but practices and how basically by and studies is happily call or personal data confidential data and whatever and we will not talk about unsecure share the Tala Dean's which have basically a sidecar loading we will really focus on user data because for example like we don't really care that we leak the fact that we download the map of Hungary but we really care that anybody on your device can know where we
live where we work with our were preference location it would appear for example okay so just before talking like really inside the topic I will just make small guess and if someone who answers the question that we cool so the environment you just try to to have kind of general setups you have an app that is installed on the device with only Network permissions so that basically it can just send out data it's like a genuine I have no rootkit and whatever and basically your device is not fruity so like nobody should have a very good security and one bad stuff is that you have device has a lot of apps like really a lot and first of all you have
video streaming amps remote control and remote storage hub or like basically remote data storage hub which I dunno draw balls or whatever I mean one thing is that I say that we not disclose the name of the venerable application because of India that were Sund so the question is in general or in worst case among this kind of question I mean option sorry what can be done can we do like but basically asking not something we do file listing user identity disclosure user financial disclosure remote stored fight disclosure or remote control so the someone wants to may have a guess here so I would guess myself why basically we can do a lot of stuff we
cannot really do remote control we can just hack the user into giving us remote control but apart from this slice a part a we can do nearly all the other stuff I mean file listing is nearly an after P that we're not going to test but we can't hand this thing but we can definitely have user identity describes your result cleanest or disclosure and any file user fine you can disclose so the talk will be divided in four main topic which is basically the first one is explaining how that has to raise woo technically in security speaking and then well how can we use that all can we use bad practices to get leaked data and then obviously as
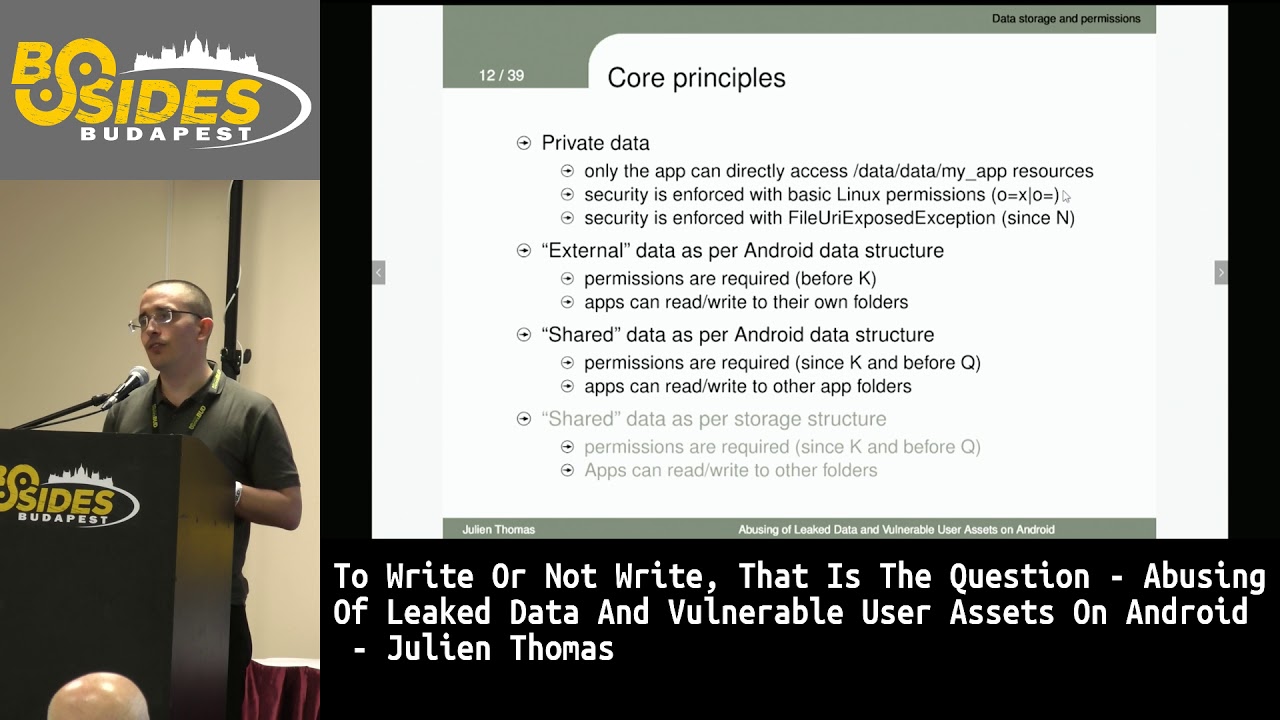
I said before what was the reaction of the vendors reckoning as a managed or like private abilities so that has to rage first a documentation because always good to read the documentation so I don't have put some bad words well just put Aram bits like read the manual so when we talk about external storage and Android we have nice goals given to us by the android framework and rigged system with a nice documentation such as you want to store you file on the external storage well you can use this function called get external files deer's which basically is described as follow is an absolute pass who application specific directories internal to the hub not typically
visible to user as major it so storage it is not always available well obviously external storage and no security is enforced with this file I mean like here when you're not a security expert you can see that here you have already two-sentence that seems conflicting like not typically visible to the user as made young and not sick no security is enforced I mean like unless you pay attention to the search fries would believe that that it could is not the zipper to the user while minute is and then if you look at the cat external storage directory which is another way to access the external storage well you will see that storage can use the definition
descriptions or in the documentation is like it can hold a relatively moment of data and each user has their own isolated shared storage well I mean here again when you say user is not an application because normally in Android every application is his user ID no when you say user here is user meaning the only guarantee you is that each user an Android like if you log in on the Android is as easily it is shared storage but not each application so that was one way to look at the documentation and then if you look another web documentation I mean I put through the reference below which is kind of the training describe little better what's the distinction between
internal storage which is basically the files have here are only accessible by the app itself that's what because the private data folder and when you have an instant were basically all of that is moved when you have an external storage is a word readable so here nobody back and like it's kind of obvious it is for readable is written however you have two nice features I will go back on this definition of features after is that it seems to behave like the internal fat because when you remove the app well the data is removed and the other very interesting stuff is that if you want to share your files with other application is written that it's the best place to
use however you should do before that is the best place if you don't require any access restriction and you want to share well I mean like you know like you have to repair the documentation because if you don't and you will have some kind of of misbelief okay so if we are developer not a security expert but we have a developer so now after we read the documentation well naturally some very general reading we seems to see that developers have a correct vision of what internal storage is because basically they will put on this folder core application data such as databases any private data and low volume data because basically if you want to load into store
a lot a huge amount of data you will lose the external storage at that documentation so as I said you will first open to cache databases and core files to do that to you therapist uses ton of code so like everything seems to be okay when we talk about the internal behavior and application however when you start to considered what is the vision of the purpose regarding non internal storage so the external storage which is you're gonna will go on the definition was we could buy external well the objective start to like it not be so much much of what we should expect from because basically this was a we stock data yeah when the booster share data okay
that's here against the definition then we started to store non core data meaning like any data that they processed I mean like you know like any data the new process some of the data are like internet - yeah because like is very sensitive and another stuff is as they will put their files that they want to share with author application because when you miss write the documentation you believe that this is the best or not to say the only way to share data is basically not to store on private because if it's private well it's private in cannot be shared so it's taught on what we could be / as decade folder however here we start well really
I mean like even on Google or Android agree that it was kind of a very bad name because SD card why it's not SD card and like it can be an SD card if you put an SD card but mainly NAND nowadays with the device that have a lot of storage embedded where is basically a storage inside the phone itself so it's not an external storage and if you look also as well photo renamed you have really similar structure as internal storage we strongly give the impression when you are a simple app dev a person without mainly security knowledge that you have the same practices at the same security because you stole you file and
your own app folder in the SD card so it's really the same so sure as the private photo and as I said also the documentation triggers won't expect it if you don't read it carefully so before about talking about the security implementation and why we should care about internal versus external let's talk about what we when I used to have an answer as kind of a feature of the external storage so the first one is that when he reads documentation you see that if you use some function call while we start fine on the device it is not removed after you earnest at the app so some people see that as a nice feature for returning
users meaning if you put files there the user Anastasi app and restart the app was data still here and walking obviously well is true which means that it's accessible and the second answer is that well we don't report SDK like I was talking with Windows that says look have an issue because you stole all you find on such as DeKalb where the answer was yes we know but we don't support external sdcard so that's not a problem for us well I mean now I mean like FD CAD is an Internet photos I said before however as I will so I also talked at the end of this talk is that even if these arguments are so obvious
to do so that they are wrong don't try to use that in baboon tease because like I said at hand they will never agree with that ok so now let's talk about security here again boss from a system point of view no an adaptive view so as I said probably data is private it means that all is he have can access to the files inside the private directories is protected by two levels by the Linux permission system and if we start to talk about no get by what we called an exception if you try to access files from an app that is not the app owning the private directory when we talk about the external data so the SD count folder
and if we stick to the Android function course we have permission required to access this folder so like before K before KitKat it was required this permission for any action and since a kid card we only require read external storage to access any folders that is not on external shared folder and if we access directly is not with the standard function called Android is still the same if we talk very quickly about how it works in terms of implementation so we have pure words that when we create a directory we are what we called a demon that is handling all the security on her behalf and when we want to access files it is on the external storage we have
what we call a control bay by the rapper as you see as a file system level so we had before fuse which is file system in user space and now we start to have sdcard FS which here again is misleading wall because it's not the file system of the sdcard but as the file system of the slash as the current folder which is not external and until Q that will believe that we start already up to the developer releases everything is owned by SD count so we don't have fine grade ownership on the SD card I mean that we change with Q and a lot of promises on them ok the other stuff is that content provider because that's
nice promote to talk when we want to talk about data we have a definition that these private data sheet option that will be a short story never be altered which means that normally that cannot be accessed however they can be made readable and editable by what we call a content provider we should be mandatory starting queue here again that is a question person for some people want to answer maybe like this general question who knows about content provider on Android yes very few I should have said concept inability an analyst to like this money you have a workshop about like using Rosa for example which is a way to analyze insecurity in content provider ok so content provider is first a
feature to expose data out of the box so basically by just using this framework and doing like this very small line of code you share your private data folders let's say in a secure way but it's also a framework to expose data as you wish magically you not only expose files which weeks can expose database you can expose queries you can expose a lot of things with the frame evasion of the content provider and so it's a very powerful framework however if not fully understood is better to stay away from it as a framework because you start to expose a lot I mean like you re vulnerable however is not a reason not to use a content provider as a feature
because by using it as in with the basic definition we were suppose you find in a secure way I mean like you just have to pay attention to how you name folders sorry like basically here like you just have to pay attention to this line which says which photo you share well I don't see that very complicated to do you want to be secure developer perspective what documentation is really complex and and we like you have a lot of documentation a lot of place to find it so the learning curve is not is kind of high and obviously we are very know that the documentation is not the sexiest thing on the planet private photo is a
constraint like if you talk with developers you will see that private folder is bad because like it's hard to debug it's hard to share data I mean like hard to share data when you have content provider here again it's much more that you don't know and you don't read the documentation until the hand external photo is great I mean like from a developer perspective it's easy to debug I mean like you just plug in the USB and have access to the to the SDK folder you have a lot of storage and persistence is possible and data sharing is believed to be easier here again well what's the difference between doing like a open file or sheriff I with content
provider like it's really 20 minute different consequences of this belief of developers probably photo is mostly used when strongly suggested I mean I I put mostly X percent we will see later what this X percent means basically it's me that you have a function call call get data base path well basically everybody every developer we use it so data base our muscles are not exposed however the external private folder is extensively used because as private and we still have some developers that care about security and protecting in code because basically is a care first trick where we put the file in the slash SD card instead of my data that way nobody will find it if you try
to find my data on my father second trick we make the for the name of the file I'm invisible by prefixing with dot you know like that's wearing Linux to hide files unless you do L but like if you do LS dash ace is their answer trick like if you stole major when best practice is to use what we call a media manager intend to say my data is here well one way to hide your file commit to developer is not to do this intent so nobody we know that files are on the SD card I mean like really I mean like here again that's very bad an old practices ok so now that we see is the developer
perspective what does it means when you have an Android phone like why really happen real life with real application ok so your initial objective was we report any non explicitly shared data that we see I didn't help well because most of times responds well well it's not critical expose data I mean like really you expose user data of corporate database not critical I mean ask you user no better option I mean I Hudgens so that yeah we know we expose the date of the user but we don't have any better option well yes you have content provider or the third answer was yeah we know that pair Deepak is insecure but user can change the storage location I
mean like really now you start to blame your own user for bad thirty-foot configuration so that wasn't that good and like after maybe one month two months of sending this kind of report like you start to be very depressing however you know like I was obvious in picture like I be back so where's the semi put is that we upgraded the objective to say to people like come on now like you can not say that it's not important like we show that we specifically target data that is paid definition not right to share that the only way to put these people like in front of the issue and they cannot say anything so basically we show that we
can expose user and notification application secret user password use a web activity copyright data and user sensitive data and nan da bollocks but still as we would see even if that's so obvious that this should not be shared it's still very complicated to make vendors agree with the statement so the candidate was that we don't forget any apps like we wanted to like here again target people that normally know their job and when we dis critical report agree with us so basically we we try to target this kind of issues so as I said use a PII image User Profile password bank information authentication token credential protocol a notification browsing I mean all the desktop we try
to see what we can do and this is interesting is that basically if most of the major app leaks this kind of data and when I say most of the major app like this is number of Donald official in the Play Store like you see that images are disclosed by app with 2,000 done load user profiles with 5.4 billion password in 100,000 bank information 6 million manic and I mean that like the worthless but basically we had an expectation to target still a good reasonable size of the user base to to say like you know like come on like your handlings data of million of users like you should really care okay so how do we
look for bugs so we first try to categorize the issue we want to target and we list is a relevant candidate for say target we detected the issue on one of the app so it's like a manual steps then we try to categorize issue and define a reproduction pattern when then the idea was to automate this analysis which obviously has not really possible so basically the only thing was automated is brain meaning we know how to do poor bug we know which back to look and radically Winstar we look we stop we look so we shall have some part of automation which is the brain pattern and then obviously after we did that we were start at one so it was really this
kind of game and that would present now ok so first one how to get user identity from logs logs I mean like everybody knows here log contain a lot of data really a lot read too much and developers particularly I have these nice stuff that when they put logs they basically want to be if they want to easily use them basically they put on these logs in data IDs everything that indentifies the user from the kind of view but it's also true for any attackers like if by looking at the log and that developer can know the user well any people works as the log can know the same thing for example here I just put here true to example of log
that we see we still the first ones that basically the user ID is disclosed and the email when we try to log in so basically just by looking the log below the user email address without any permission except read external storage another one was that basically we were leaking the account token and silicon token was a way to access user gender user email user first name last name phone number so just by looking as a log we we get very nice information so how we detected that we may discrete it basically every time we install an app or set of app look for by grab email address or people like Auto token and by only doing that we get like all this
information how to avoid that with very easy log you are clean you logs I mean like don't put user pin I on on the log the stupid and keep them private I mean like saying that we put the log on external storage because they are too big is kind of nonsense like you can you can zip them you can rotate them I mean like it's very bad better best practices regarding locking and like you already have framework to do log in correctly another way to extract user on your identity is based on naming convention which was another funny stuff which is like basically lot of haves nowadays handle me tea but I can't visit in the app so
our social networks data management application and they did a way to separate data sets meaning like I can't one icon curtain three there are different photos and the insecure approach that we often see is basically to use the user email address as a folder name or to use the user ID as a folder name well I just put here two lines so one is worth like when we do things you have my email that was discussed every time and when using author app offline cache where the social ID was disclosed and we don't pay intention over like this socialite is a very weird set of letters so when you look at that you don't understand why it
means and luckily for me well I know very well these social IDs when I look at this photo name I say like it ring the bell and basically it was the rule completes social ID social network ID of the user so by just looking at finance we know who you are without asking any relevant permission so the detection method is basically instead of grab while you find I like it's very very great for one and what's the best practices don't do that I mean like here again you can hash you can do like an internal mapping and private database that's here again but best practice is like don't put an email address as a folder I mean like this that makes no
sense you can hash that means the same Unisa t so user profiling what's in second issue we're trying to do meaning like let's assume that your identity is protected can we guess what's your preferences so basically we had the state methods to the IP address is not a sufficient SiC is too easy to get on Android like well while your protein on the web so we wanted to know exactly when what and where you are doing so one way to basically do user profiling on social network a social network application is basically to look at the cache because every time you visit a page where you get somehow some cache that is shared on external storage
so the first cache was that basically every header of the page you visit on this social app was cache as the header is unique to the page so we know exactly which page you are visiting when art is for the first time the second way is to get the user identity by looking at the picture cache is the user picture cache the first picture is your picture so basically here again we're not talking about an application with like 10,000 download we're talking with application with billions and yet the file the picture file can be easily Google reversed picture to know who you are in in matter of seconds another very interesting thing is web browsing so if
you lose some web apps they will they will catch the while because the webview is the external storage and by the case the webview cache is a word page so we know everything that you visit which page and sometimes we even get the credentials that you use within the page and here again how to avoid that is basically to assert behavior on the under link component you are using because most of the times this hub don't even know that that leaking this information because they use some kind of some a generation of the use here for this case a webview component that is not their own development okay so another one is playing with geolocation
and so when dealing with maps and GPS you often have a lot of data and the insecure approach is to consider that all GPS data or similar meaning you save everything in the same location and when I says anything is poison pearl well they use a database associated to the GPS map do it alone where you put them next to the maps I mean like it's kind of logically make sense when you're not the repels you put all the same or the logically linked data in the same location well I mean here for example like it was a map application that serialized the values of your preferences well means okay you get the SQL database you don't understand what
the format is while you just play some kind of guess and you see very quickly just serialize and you export everything and the way to detect that was basically to look at any exposed SQL SQL like database on Android on the external storage why here again just a basic crap about SQLite and two things here don't believe that read external storage is the same as access fine location like I said the value of the data that you're storing and the other thing is that don't believe that because you use a custom format users will not be able to I mean like attackers would be able to understand what's this format because they can just install the app on another
device whose the file and the device running the app so another way to play with GPS the location is regarding integrity here we have some SQLite database it is not even cellular that whole not encrypted here again same patent of detection and basically we can insert that information into GPS of the GPS app meaning we can insert fake route we can accept fake preferences towards the preferences and basically just describe a user experience for example okay extracting implicit configuration assets so documentation are often documents are often seven devices only for one reason you want to have offline support meaning like you cooperate and you have data well you want to save them on your device because you want to
access them locally and the insecure approach is to consider the documents when and not sensitive and the second stuff that this link is that basically as is not sensitive user don't need to know where we store them can see here was one mistake so the example is that body we users hard-code the storage location I don't say that to the user the second thing is that while you hide the capacity to change the storage directory and basically we only had to detect a file change which is super easy like we have file Observer that you can extend path file observer on Android and basically we are aware every time the file is asserted on the external storage
and here again the only mistake is that while I'm if I don't make that static on the external storage because like some people that use rehab may want to store confidential data and they want to know where is told what is to choose that and the second option is that I mean let the user decide what is going to store and make it by default secure like if the user want to have a lot of data just giving the option to put that in the external storage but don't assume by default that it's an external like it's not your data if you use the data when we extend about this configuration later we can talk about explicit confidential
data which is like encrypted documents and here again what sometimes you approach is exactly the same which is we don't tell you the way we store and another consideration is that as we are on Android system we don't give the encryption key like we keep that on the server like you know is top secret top important so we don't share that on the Android system which is here not a bad vision but the issue is that when you stop file in the a personal photo and you want to allow them to view while you have an issue because you don't have the encryption key so basically we have what people we just have the do sorry is
basically they will take the sensitive data encrypted data from the server they will put that on the external storage and two options first one is that we just put them and encrypted because we don't have the encryption key luckily we decrypt them on the fly and put them on the external storage which in the end is the same we have an encrypted confidential material on the external storage while detection method is really that is the same is like we just went over file change and like yeah I mean like just here again pay attention when you store fight just pay attention to what you store and how like like when I was talking about explicitly
confidential data it was even a feature and said AB that said we have we use this kind of vault or like secure vault or encrypted folder feature this is a paid feature but basically it's just like a folder on the external storage in x2z and secure folder ok extracting a special confidential data I will just sync the time still absent so when we want to extract impeach confidential data on the other stuff is that basically when you SMS no MMS most of the user would believe that way it's fine files can be stole like the files that you have put on the MMS he had so we put that on the shelf to read I mean like basically you expose any
date on send is an MMS to any application installed on the device even if you could then private and even if it's not an MMS app is just like a conversation have inside the banking application with your bank manager some people at the configuration consideration that as you share with someone while shared with everybody so the detection method here again was super easy just like instantly have play with it and see was disclosed and one way to do that better is just to assert how data I generated like if you action an MMS with the fact that is already stolen the SD card yeah it's fine to catch it on the SD card but if it's
taken from the camera for the PAL you take a nice picture of yourself and you want to send that to your partner well maybe you don't want that to be disclosed to any other app installed on the device okay next one injecting private data I was talking about how can we can access data that is told on the external storage another thing that is very nice is that basically you can do the same time of alteration basically every stud on the on the external folder like a remote like cooperate date on file Leticia stood on the NAM on server well if you're an app another app I mean you can just overwrite the file locally as the
next end user will open the data man it will have it will sing back to the server the modification that you made which is quite cool to upload any data that you want on the corporate server one of the see what's possible is that basically if you want to share file acknowledged you have the share feature like I want to share to the Bluetooth by bluetooth to another device I want to share by email most of these have what they do is that they wished oh the temporary file that is the action between sharing to the other half in the external folder and none as I say that is super great is a basically it will
even disclose the fact that they put that in the external folder so as an attacker just have to basically add this right on out of the data so that G genuine sender said the malicious file to the receiver and here again whether I talk about Mac application while magically the bad manager will trust your input because you believe it's use input Y it's not okay so I will just I think I'm running long time so this is exactly the same stuff so we'll just keep that one and I will talk about extracting shared private data you have to understand that I'm going to disclose the data you don't disclose data no like when this comes to data you don't
discuss to data well you disk use to data and the aggregation of site data and that has to be considered carefully be comfortable when you disclose action traces or interaction traces when you disclose the word price you don't disclose each line individually which means that attackers for example here when they see this kind of line repeating note that possible this heidi here is always so it was for remote control application was always disclose the but the case the controller ID was always this one with that name that one so basically we can start to know will connect to the device of the user by this disclosure of internal data that seems important and what is great with that is
particularly we can as an attacker fake remote connection by using the same I mean at the same ID badly the same name and the user we get a pop-up that someone with the same name as the one we have that user control device wants to connect worse and I will not disclose the exact repetition stats but basically we can just cancel sometime we can even cancel the genuine request and replace with Ron and the user would still believe that is a correct user because the name which is your information displayed is the same okay so extracting user secrets some date on some in update on are the facto sensitive like it's not equation and it's wrong to secure that every day does
at this process within the hub as is processed within the hub or is view within the hub can be disclosed and here present perm I'm talking about like when you connect with yet app connect to the remote server and there is a failure and you want to log this site failure basically don't hurt him that the failure is caused by the user wrong inputs because when you do that where basically you put on the log email first name last name and password which sometimes if it's a server-side mistake Israel is a password so basically on the lock you put the user email and password weathers great same thing when someone is viewing content and rehab I'm like he
said because I'm doing that on the app that you can disclose the bank account some Bank apps when you look at the bank account within do you have just cash that because the PDF they need to be rendered sweetened to bestow luckily but it's temporary so we just put that on on the shared folder and it's just not right okay so evolution of this 2d I mean I'm so seeking evolution of this of the study so I know this process was a really time consuming stuff right like we spend months because it was manually installed manually start which app because we had to sign up most of the time we had permanent retraction meaning we
found Berg we generalize the generalization is not good so it was like a permanent stuff and the standardization is very hard because more time the Berg is different is follow the same logic of incorrect disclosure by the way discourse is never the same so after menses we started to have general pattern which was not a straightforward stuff and it happened relied on on on the combo in stand-up find potentially vulnerable fine grab for disclosure I mean like this really like you have to target the wrap-up category very quickly otherwise thought to be very emplace and that up to days of in standing apps you find no bug I mean like when you find the right
category all of them are vulnerable but unless you find that is really like a not nice so classification of the issues we have a lot of type of data disclosed we have a private data we have user private data we have device protected assets to charge the location and and the reason for this exposure is really limited means the first one is up most of time at the proprietors failed to read the documentation they then try to define like is even even not asserting is defining the security policy now if you don't design defined your security policy and when you consider as public and not public well I mean like is stupid because like everything is
discussing way you don't even control and the third type of failure is like not to perform any security test because it's very easy when when you are the other purpose to just check where you'll find as Todd in life scenario most of the issue were here discovered because it was no security assertion at all so classification of the vendors so we have food for people we do bad Monty I think they know that already virus vendor profile so we have the really responsive vendor like the top one that respond very quickly a couple of days mostly time is managed by big multi-platforms but not always diagonally the issues pay or give one your subscription to the software as you
can reap refers you see payment option then you have non-responsive vendors which people that basically see your issue let's say I AB is out of stop because you know like when you do back when T of scope even if this is bad where you can still say is out of copy see if it's out of scope also we say won't fix one piece for maybe two reason why is because the product is a end-of-life so what we see a lot with device manufacturer oh it's too much work to fix so it's a question of benefits versus cost and then you have a third type of vendor which is majority of them which is a correspondence you
send them image sensor my second email says a majority made no reply of the couple of months but for the third one type of vendors I will say that's not the right approach because basically we're talking with Google but like why can we do I mean like when we are talking about ATS applause vendors that disclose million of user assets I mean obviously for how the next step that was escalated to Google Play team and has just woken to progress classification of the vendors after can apply than the we try to understand what the vision of them and the first issue we had is like Korea how to explain the issue to them is really complicated we have to explain
to them was disclosing user email address or Israel entity is bad I mean like knowledge that their own business they should know well that we have to disclose also to illustrate how sensitive the data is disclosed I mean like when you disclose user business which has cooperate data encrypted cooperate data normally we don't have to explain why it's bad for cotton provider that I mentioned before we even had something to explain what does passed on dress up in your ability means I mean like it's a very well known security issue very bad for the war operating system but most of the time vendors just says you have to specifically tell me why personal discipline variability is bad I mean
like you just have to type these keywords on Google to find ways bad and the reason most of time is because you should pay attention you when you talk to to vendor you have to business in part you have the vendor business involved and you have the users of the vendor application business and when you start to go against the vendor objective to protect the user business sometimes start to be very conflicting the other issue that sometimes master time it doesn't even watch the effort when you have no reply when you get a one-year subscription or when you get a t-shirt I mean like it's cool yeah but when takes when text how was to find the bug and
more how was to explain the bug I mean a t-shirt is not really enough and the last part is that even if you show everything written the issue even in that case changing the vision vendor is very hard okay so conclusion even if I say it was very complicated and time-consuming to do this kind of survey I mean like it's very interesting to do what else we can say like similar to dumpster diving on Android because basically you're looking for a needle in a haystack except that you don't even know what you needle is I'm also Tom you don't even know where the F stack is so it's very challenging generalizes others say it was partially automated on the
pattern side but on the other side most of the time manual access it is often reproducible which is running fun one well you can be sure that if one developer made this mistake a lot of gear and still a lot of work is possible this kind of study and I hope that some people will be interesting to do this kind of study too we can read a real automate ation too many like really like to the founders conferences the minus sign we can extend the type of disclosure analysis and the candidate because basically as I said with target is huge user base which normally means that developers are already very aware of what they do what
happen when you have an app that had 100,000 download I mean like what no but already 100,000 users so potential is disclosure of 100,000 user data we didn't look at this because we just like at the higher expectation term abuse base and another potential walk is basically to use this disclosure to get even more explosion exposure sorry first but when we get talking ID going back to like understand how this ID using them of API as we did for one study can discuss even far more data that the one that lives on the device because if you disclose you notification token of an API where you can get all the user profile even if it's not on the user
device however one small stuff here is that we will walk of that again but two things here pretty much this kind of fishes is only depend and the vendors like if you again doubt you find and don't fix it will never be fixed and the cigar stinks is that if they still behave the same way as discarding most of the time these kind of issues well the label wars for security researcher to do this kind of fool because like it's a lot of time for basically nothing okay so thank you for your attention you have any question [Applause]